-
组网需求
如图1所示,实现IPv4 Host与IPv6 Host间的互访;(由于eNSP模拟器的路由器不支持NAT64实现,因此使用USG6000V)USG6000V为双协议栈,连接IPv6网络以及IPv4网络;
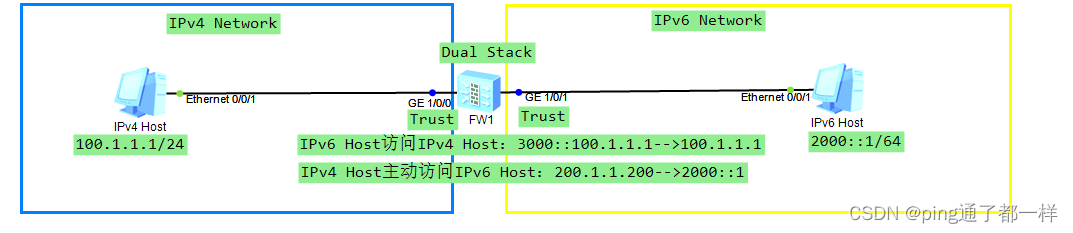 图1 动态/静态NAT64组网图
图1 动态/静态NAT64组网图
-
操作步骤
1、防火墙的接口划入trust区域,配置接口IP地址,并放行ping包
略
2、防火墙上开启NAT64功能,并配置NAT64前缀
nat64 enable
nat64 prefix 3000:: 96说明:此处NAT64前缀以3000:: 96为例,如果不配置,则默认为知名前缀64:FF9b::/96
3、配置地址池,给NAT64进行IP协议转换的时候使用
nat address-group 1 0
mode pat
section 0 200.1.1.1 200.1.1.1004、配置防火墙的NAT策略
nat-policy
rule name 1
nat-type nat64
action source-nat address-group 15、如果是IPv4主动访问IPv6,那么需要配置静态的NAT64映射
nat64 static 2000::1 200.1.1.200







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章

















 4596
4596

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








