shiro
- Apache Shiro是一个Java的安全(权限)框架。
- Shiro可以非常容易的开发出足够好的应用,其不仅可以用在JavaSE环境,也可以用在JavaEE环境。
- Shiro可以完成,认证,授权,加密,会话管理, Web集成,缓存等。
- 下载地址: http://shiro.apache.org/
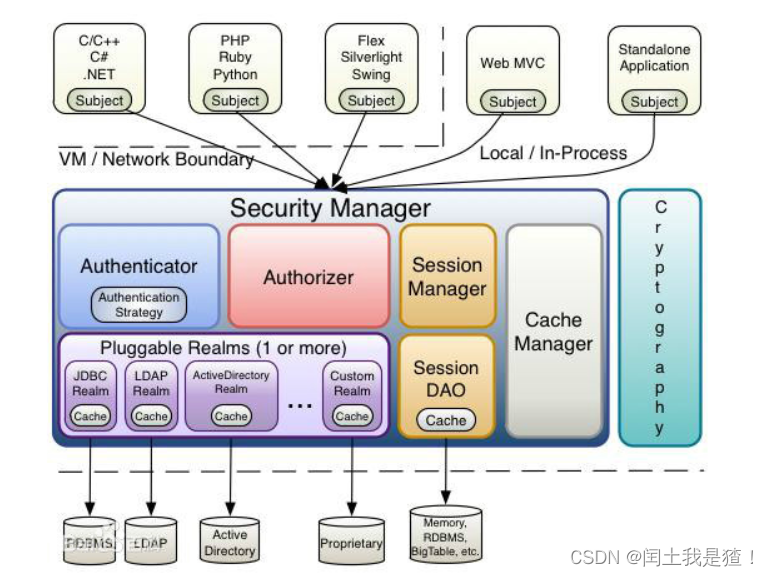
三个核心组件:Subject, SecurityManager 和 Realms.
Subject:即“当前操作用户”。但是,在Shiro中,Subject这一概念并不仅仅指人,也可以是第三方进程、后台帐户(Daemon Account)或其他类似事物。它仅仅意味着“当前跟软件交互的东西”。
-
Subject代表了当前用户的安全操作,SecurityManager则管理所有用户的安全操作。
-
SecurityManager:它是Shiro框架的核心,典型的Facade模式,Shiro通过SecurityManager来管理内部组件实例,并通过它来提供安全管理的各种服务。
-
Realm: Realm充当了Shiro与应用安全数据间的“桥梁”或者“连接器”。也就是说,当对用户执行认证(登录)和授权(访问控制)验证时,Shiro会从应用配置的Realm中查找用户及其权限信息。
-
<!-- Subject 用户 SecurityManager 管理所有用户 Realm 连接数据 -->
从这个意义上讲,Realm实质上是一个安全相关的DAO:它封装了数据源的连接细节,并在需要时将相关数据提供给Shiro。当配置Shiro时,你必须至少指定一个Realm,用于认证和(或)授权。配置多个Realm是可以的,但是至少需要一个。
Shiro内置了可以连接大量安全数据源(又名目录)的Realm,如LDAP、关系数据库(JDBC)、类似INI的文本配置资源以及属性文件等。如果系统默认的Realm不能满足需求,你还可以插入代表自定义数据源的自己的Realm实现。

1、pom.xml
<dependency>
<groupId>org.apache.shiro</groupId>
<artifactId>shiro-core</artifactId>
<version>1.4.0</version>
</dependency>
<!-- 日志 -->
<dependency>
<groupId>org.slf4j</groupId>
<artifactId>jcl-over-slf4j</artifactId>
<version>1.7.21</version>
</dependency>
<dependency>
<groupId>org.slf4j</groupId>
<artifactId>slf4j-log4j12</artifactId>
<version>1.7.21</version>
</dependency>
<dependency>
<groupId>log4j</groupId>
<artifactId>log4j</artifactId>
<version>1.2.17</version>
</dependency>
<dependency>
<groupId>commons-logging</groupId>
<artifactId>commons-logging</artifactId>
<version>1.2</version>
</dependency>
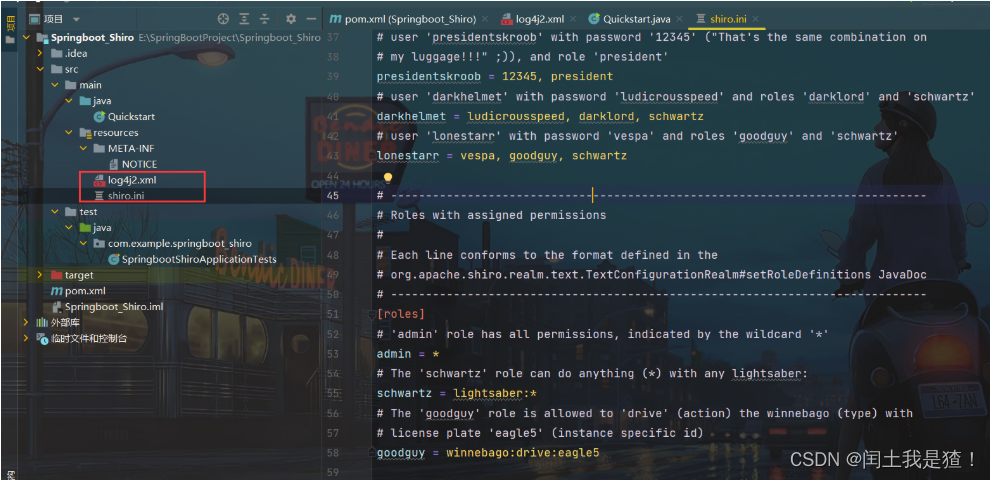
2、配置文件
[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-6UpLAwx4-1677722901370)(assets/1672307711485.png)]
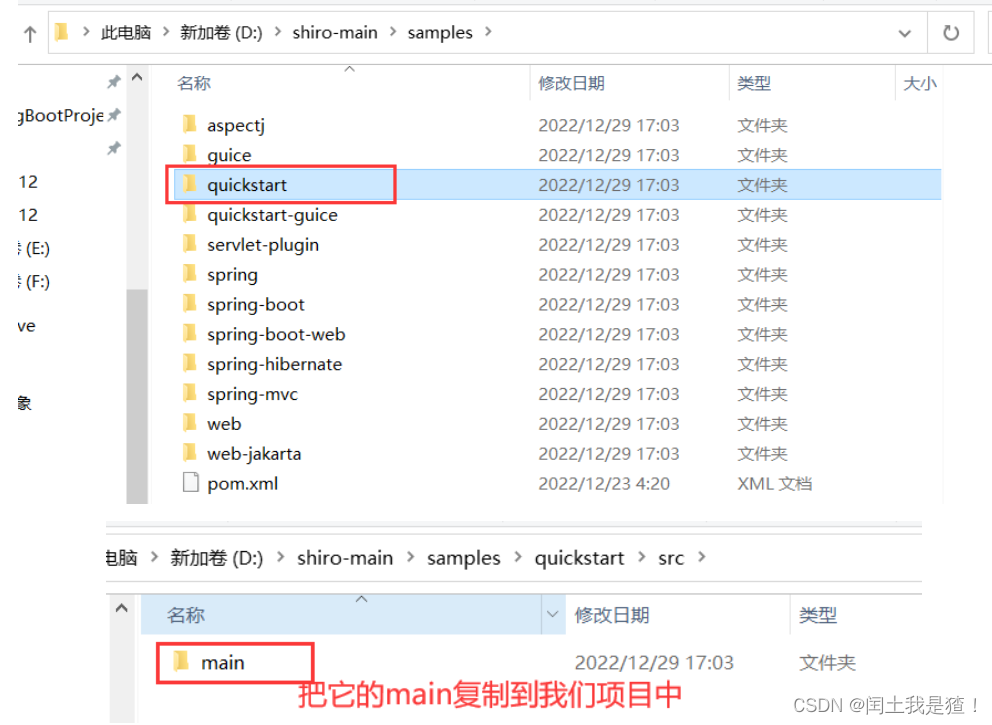
3、快速开始
修改它的导包和配置
//import org.apache.shiro.ini.IniSecurityManagerFactory;
import org.apache.shiro.mgt.DefaultSecurityManager;
import org.apache.shiro.realm.text.IniRealm;
//import org.apache.shiro.lang.util.Factory;
import org.apache.shiro.util.Factory;
public static void main(String[] args) {
DefaultSecurityManager securityManager = new DefaultSecurityManager();
IniRealm iniRealm = new IniRealm("classpath:shiro.ini");
securityManager.setRealm(iniRealm);
}
SpringBoot整合Shiro
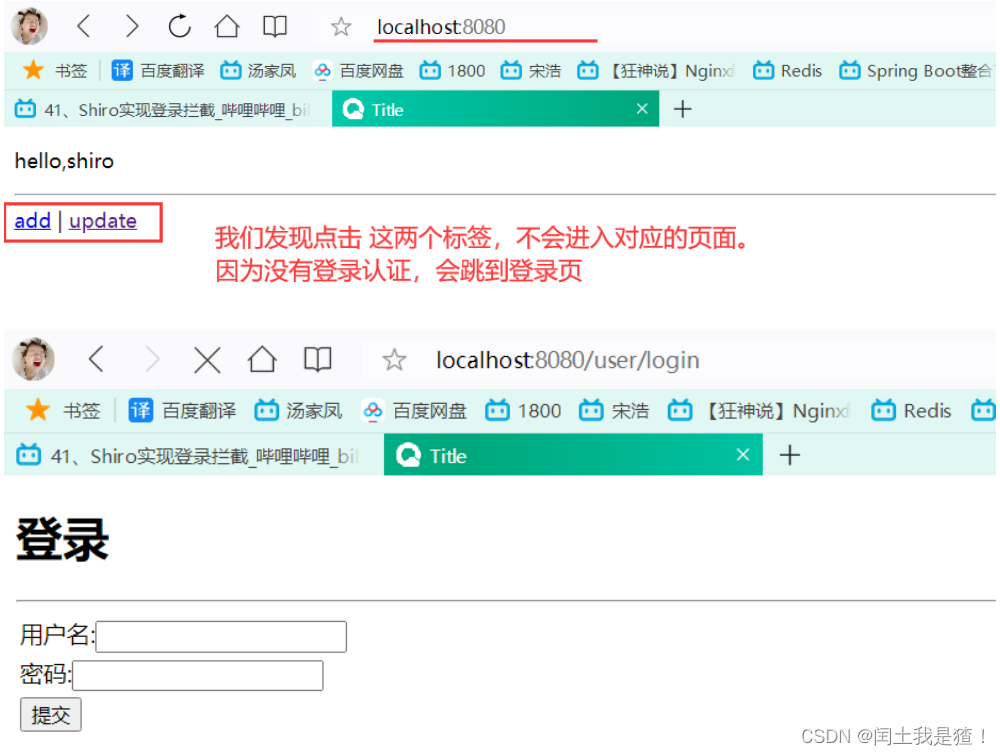
登录拦截
<!--引入shiro-->
<dependency>
<groupId>org.apache.shiro</groupId>
<artifactId>shiro-spring-boot-starter</artifactId>
<version>1.5.3</version>
</dependency>
环境搭建
<!--
Subject 用户
SecurityManager 管理所有用户
Realm 连接数据
-->
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-devtools</artifactId>
<scope>runtime</scope>
<optional>true</optional>
</dependency>
<!--引入shiro-->
<dependency>
<groupId>org.apache.shiro</groupId>
<artifactId>shiro-spring-boot-starter</artifactId>
<version>1.5.3</version>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-thymeleaf</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-web</artifactId>
</dependency>
config
ShiroConfig
package com.example.springboot_shiro.config;
import org.apache.shiro.spring.web.ShiroFilterFactoryBean;
import org.apache.shiro.web.mgt.DefaultWebSecurityManager;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.Configuration;
import java.util.LinkedHashMap;
import java.util.Map;
@Configuration
public class ShiroConfig {
//ShiroFilterBean , 第三步
@Bean
public ShiroFilterFactoryBean getShiroFilterFactoryBean() {
ShiroFilterFactoryBean bean = new ShiroFilterFactoryBean();
//关联安全管理器
bean.setSecurityManager(getDefaultWebSecurityManager());
//添加shiro的内置过滤器
/**
* anno:无需认证就可以访问
* authc : 必须认证了才可以访问
* user: 必须拥有 记住我功能才能用
* perms: 拥有对某个资源
* role:拥有某个角色权限才能访问
*/
Map<String, String> filterMap = new LinkedHashMap<>();
filterMap.put("/user/add", "authc");
filterMap.put("/user/update", "authc");
//也可以写成/* , 所有的
//filterMap.put("/user/*", "authc");
bean.setFilterChainDefinitionMap(filterMap);
//设置登录请求
bean.setLoginUrl("/user/login");
return bean;
}
//DefaultWebSecurityManager : 第二步
@Bean
public DefaultWebSecurityManager getDefaultWebSecurityManager() {
DefaultWebSecurityManager securityManager = new DefaultWebSecurityManager();
//关联
securityManager.setRealm(userRealm());
return securityManager;
}
//relam 对象 , 需要自定义类 : 第一步
@Bean
public UserRealm userRealm() {
return new UserRealm();
}
}
UserRealm
public class UserRealm extends AuthorizingRealm{
//授权
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
System.out.println("执行了==>授权 doGetAuthorizationInfo");
return null;
}
//认证
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken authenticationToken) throws AuthenticationException {
System.out.println("执行了==>认证 doGetAuthenticationInfo");
return null;
}
}
Controller
@Controller
public class MyController {
@RequestMapping(value = {"/", "/index"})
public String toIndex(Model model) {
model.addAttribute("msg", "hello,shiro");
return "index";
}
@RequestMapping("/user/add")
public String add() {
return "user/add";
}
@RequestMapping("/user/update")
public String update() {
return "user/update";
}
@RequestMapping("/user/login")
public String toLogin() {
return "user/login";
}
}
index.html
<body>
<p th:text="${msg}"></p>
<hr/>
<a th:href="@{user/add}">add</a> | <a th:href="@{user/update}">update</a>
</body>

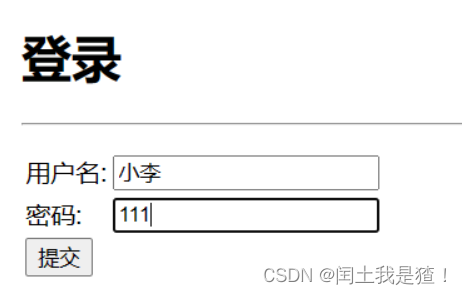
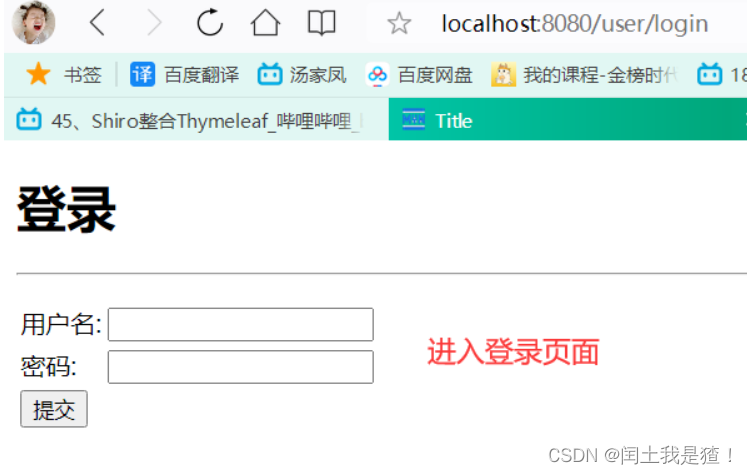
login页面
<body>
<h1>登录</h1>
<hr>
<form action="" method="post">
<table>
<tr>
<td>
用户名:
</td>
<td>
<input type="text" name="username">
</td>
</tr>
<tr>
<td>
密码:
</td>
<td>
<input type="text" name="password">
</td>
</tr>
<tr>
<td>
<input type="submit" value="提交">
</td>
</tr>
</table>
</form>
</body>
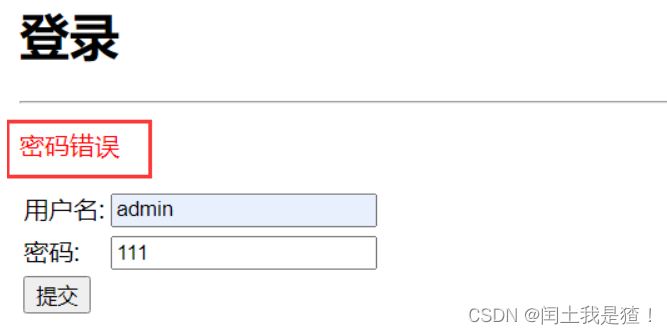
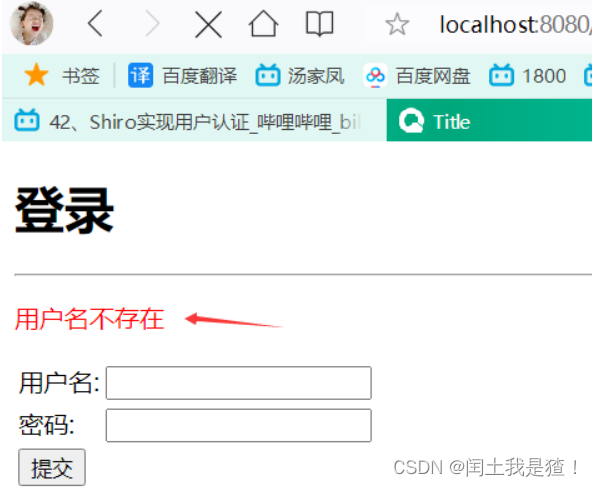
用户认证
controller
@RequestMapping("/login")
public String login(String username, String password, Model model) {
//获取当前用户
Subject subject = SecurityUtils.getSubject();
//封装用户的登录数据
UsernamePasswordToken token = new UsernamePasswordToken(username, password);
//执行登录方法,如果没异常就ok
try {
subject.login(token);
} catch (UnknownAccountException e) { //用户名不存在
model.addAttribute("msg", "用户名不存在");
return "/user/login";
} catch (IncorrectCredentialsException e) {//密码不存在
model.addAttribute("msg", "密码错误");
return "/user/login";
}
return "index";
}
UserRealm
public class UserRealm extends AuthorizingRealm {
//授权
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
System.out.println("执行了==>授权 doGetAuthorizationInfo");
return null;
}
//认证
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken authenticationToken) throws AuthenticationException {
System.out.println("执行了==>认证 doGetAuthenticationInfo");
//用户名,密码 应该在数据库中取。
String username = "admin";
String password = "123123";
UsernamePasswordToken userToken = (UsernamePasswordToken) authenticationToken;
//如果输入的用户名 不等于 username的值(admin) 应该在数据库中获得
if (!userToken.getUsername().equals(username)) {
return null; //抛出异常 UnknownAccountException
}
//密码认证,shiro做
return new SimpleAuthenticationInfo("", password, "");
}
}


Shiro整合Mybatis
pom.xml
<dependency>
<groupId>mysql</groupId>
<artifactId>mysql-connector-java</artifactId>
</dependency>
<dependency>
<groupId>log4j</groupId>
<artifactId>log4j</artifactId>
<version>1.2.17</version>
</dependency>
<dependency>
<groupId>com.alibaba</groupId>
<artifactId>druid</artifactId>
<version>1.2.15</version>
</dependency>
yml
spring:
datasource:
username: root
password: 160554
#?serverTimezone=UTC解决时区的报错
url: jdbc:mysql://localhost:3306/mybatis?serverTimezone=UTC&useUnicode=true&characterEncoding=utf-8
driver-class-name: com.mysql.cj.jdbc.Driver
type: com.alibaba.druid.pool.DruidDataSource
#Spring Boot 默认是不注入这些属性值的,需要自己绑定
#druid 数据源专有配置
initialSize: 5
minIdle: 5
maxActive: 20
maxWait: 60000
timeBetweenEvictionRunsMillis: 60000
minEvictableIdleTimeMillis: 300000
validationQuery: SELECT 1 FROM DUAL
testWhileIdle: true
testOnBorrow: false
testOnReturn: false
poolPreparedStatements: true
#配置监控统计拦截的filters,stat:监控统计、log4j:日志记录、wall:防御sql注入
#如果允许时报错 java.lang.ClassNotFoundException: org.apache.log4j.Priority
#则导入 log4j 依赖即可,Maven 地址:https://mvnrepository.com/artifact/log4j/log4j
filters: stat,wall,log4j
maxPoolPreparedStatementPerConnectionSize: 20
useGlobalDataSourceStat: true
connectionProperties: druid.stat.mergeSql=true;druid.stat.slowSqlMillis=500
mybatis:
type-aliases-package:
com.example.springboot_shiro.pojo
mapper-locations:
classpath:mapper/*.xml
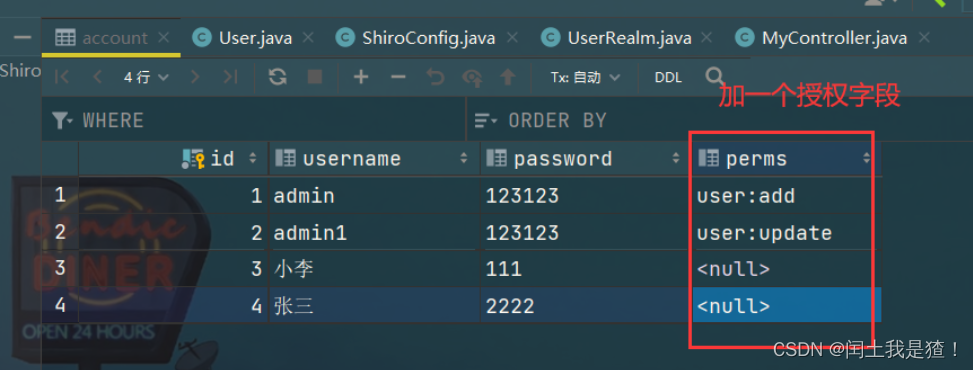
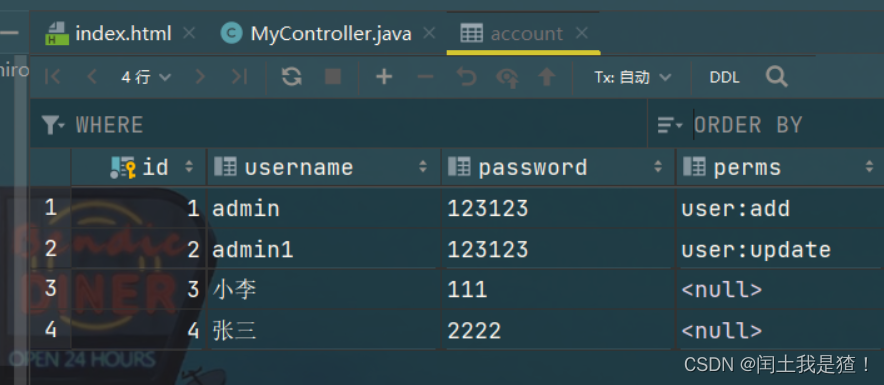
数据库
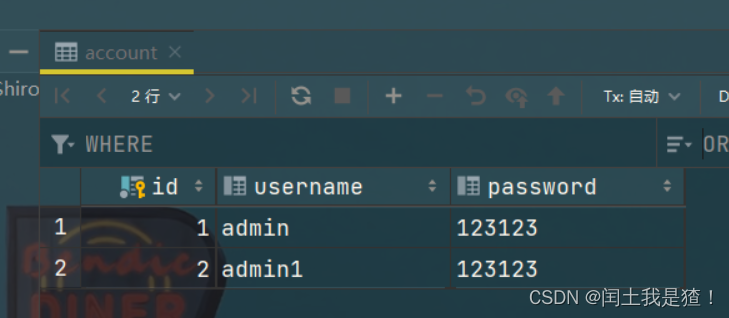
pojo
@Data
@AllArgsConstructor
@NoArgsConstructor
public class User {
private int id;
private String username;
private String password;
}
mapper
@Mapper
@Repository
public interface UserMapper {
public User findByUsername(String username);
}
<?xml version="1.0" encoding="UTF-8" ?>
<!DOCTYPE mapper PUBLIC "-//mybatis.org//DTD Mapper 3.0//EN"
"http://mybatis.org/dtd/mybatis-3-mapper.dtd">
<mapper namespace="com.example.springboot_shiro.mapper.UserMapper">
<select id="findByUsername" parameterType="String" resultType="com.example.springboot_shiro.pojo.User">
select *
from mybatis.account
where username = #{username}
</select>
</mapper>
@Service
public class UserService {
@Autowired
private UserMapper userMapper;
public User findByUsername(String username) {
return userMapper.findByUsername(username);
}
}
controller
@RequestMapping("/login")
public String login(String username, String password, Model model) {
//获取当前用户
Subject subject = SecurityUtils.getSubject();
//封装用户的登录数据
UsernamePasswordToken token = new UsernamePasswordToken(username, password);
//执行登录方法,如果没异常就ok
try {
subject.login(token);
} catch (UnknownAccountException e) { //用户名不存在
model.addAttribute("msg", "用户名不存在");
return "/user/login";
} catch (IncorrectCredentialsException e) {//密码不存在
model.addAttribute("msg", "密码错误");
return "/user/login";
}
return "index";
}
UserRealm
public class UserRealm extends AuthorizingRealm {
@Autowired
private UserService userService;
//授权
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
System.out.println("执行了==>授权 doGetAuthorizationInfo");
return null;
}
//认证
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken authenticationToken) throws AuthenticationException {
System.out.println("执行了==>认证 doGetAuthenticationInfo");
//用户名,密码 应该在数据库中取。
// String username = "admin";
// String password = "123123";
UsernamePasswordToken userToken = (UsernamePasswordToken) authenticationToken;
//连接真实数据库 , 参数传入 输入的 用户名
User user = userService.findByUsername(userToken.getUsername());
if (user==null){ //根据用户名查不到。没有这个人
return null; //抛出异常 UnknownAccountException
}
// 如果输入的用户名 不等于 username的值(admin) 。 应该在数据库中获得
// if (!userToken.getUsername().equals(username)) {
// }
// 可以加密 MD5:a1s2d4a827CCB0EE 。MD5盐值加密 827CCB0EEusername
//加密加盐 查询用户时,除了查到加密密码外,还能查到盐值。 把输入密码+盐值加密和数据库存放密码比对就OK
//密码认证,shiro做 ,加密了
return new SimpleAuthenticationInfo("", user.getPassword(), "");
}
}
[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-guKsFsDX-1677722901384)(assets/1672577812953.png)]
[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-5KYWgwny-1677722901385)(assets/1672577821258.png)]
[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-fNS2VzRz-1677722901386)(assets/1672577831994.png)]
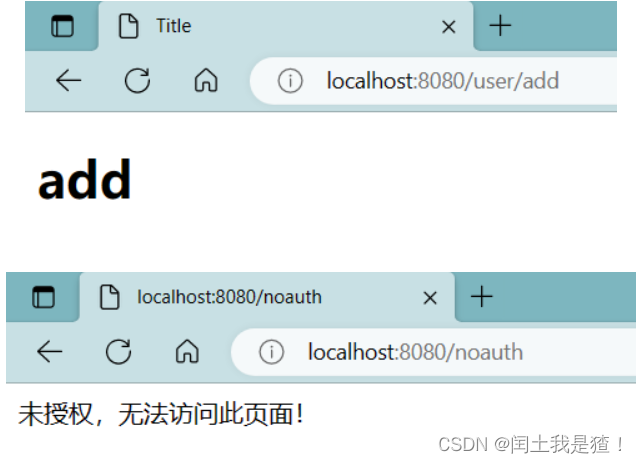
请求授权
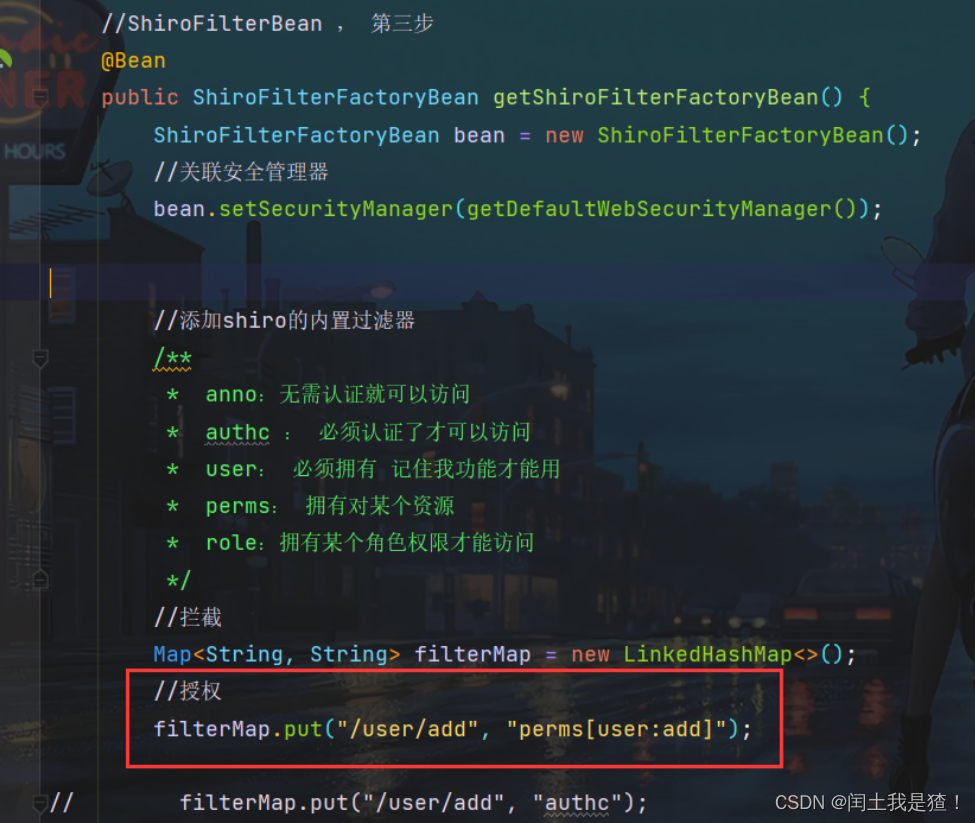
↑ 有 user:add 这个字符串才会授权*
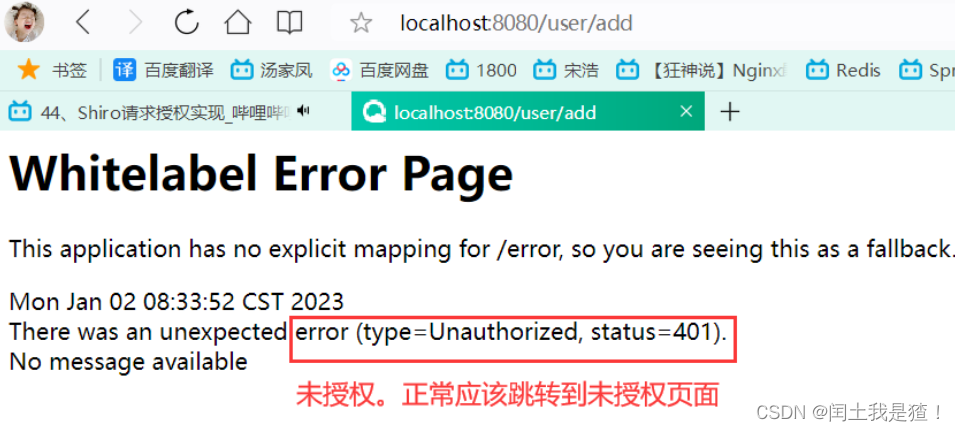
为了不让它显示报错信息,我们让他跳到指定页面
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-iTErKIFi-1677722901389)(assets/1672619939516.png)]](https://img-blog.csdnimg.cn/23e2d283de3245d5bae089cffe570b75.png)
@RequestMapping("/noauth")
@ResponseBody
public String noauth(){
return "未授权,无法访问此页面!";
}
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-sRrwvOvo-1677722901391)(assets/1672625674566.png)]](https://img-blog.csdnimg.cn/21bf33e8b6f447c2a210cbaed3c389bd.png)
ShiroConfig
//ShiroFilterBean , 第三步
@Bean
public ShiroFilterFactoryBean getShiroFilterFactoryBean() {
ShiroFilterFactoryBean bean = new ShiroFilterFactoryBean();
//关联安全管理器
bean.setSecurityManager(getDefaultWebSecurityManager());
//添加shiro的内置过滤器
/**
* anno:无需认证就可以访问
* authc : 必须认证了才可以访问
* user: 必须拥有 记住我功能才能用
* perms: 拥有对某个资源
* role:拥有某个角色权限才能访问
*/
//拦截
Map<String, String> filterMap = new LinkedHashMap<>();
//授权 ,有 user:add 这个字符串才会授权
filterMap.put("/user/add", "perms[user:add]");
filterMap.put("/user/update", "perms[user:update]");
// filterMap.put("/user/add", "authc");
// filterMap.put("/user/update", "authc");
//也可以写成/* , 所有的
filterMap.put("/user/*", "authc");
bean.setFilterChainDefinitionMap(filterMap);
//设置登录请求,没认证跳转到这里
bean.setLoginUrl("/user/login");
//设置未授权页面
bean.setUnauthorizedUrl("/noauth");
return bean;
}
UserRealm
public class UserRealm extends AuthorizingRealm {
@Autowired
private UserService userService;
//授权
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
System.out.println("执行了==>授权 doGetAuthorizationInfo");
//这些授权应该在数据库里取
SimpleAuthorizationInfo info = new SimpleAuthorizationInfo();
// info.addStringPermission("user:add");
//拿到当前用户
Subject subject = SecurityUtils.getSubject();
//拿到user对象
User currentUser = (User) subject.getPrincipal();
//设置当前用户的权限,数据库里取
info.addStringPermission(currentUser.getPerms());
return info;
}
}
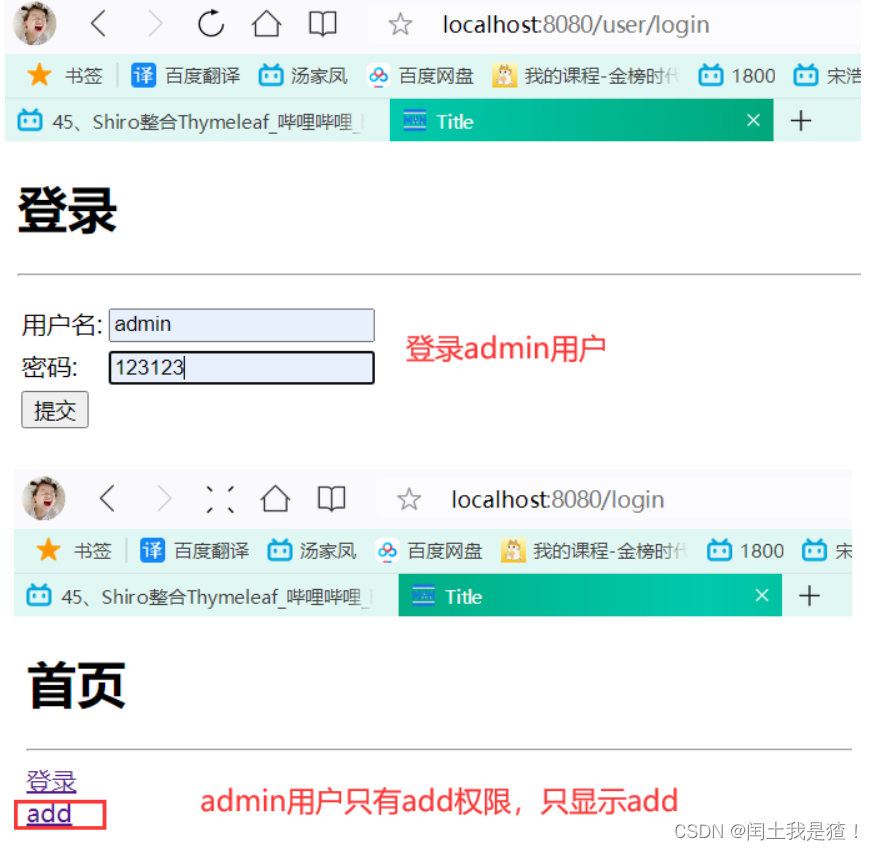
测试一下
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-XoYbOMc3-1677722901392)(assets/1672625829869.png)]](https://img-blog.csdnimg.cn/7d0b09b56f784f15b37b7448ceceb4fc.png)
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-soY4BW7L-1677722901394)(assets/1672625857293.png)]](https://img-blog.csdnimg.cn/eb0891dc254744e5bfade9d606d74f92.png)
都不能访问
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-ZokaahkY-1677722901395)(assets/1672625847829.png)]](https://img-blog.csdnimg.cn/b1a19d12dfef4360bddb39e32e7d885d.png)
我们再登录有user:add权限的admin
可以发现add有权限进入,update不能进
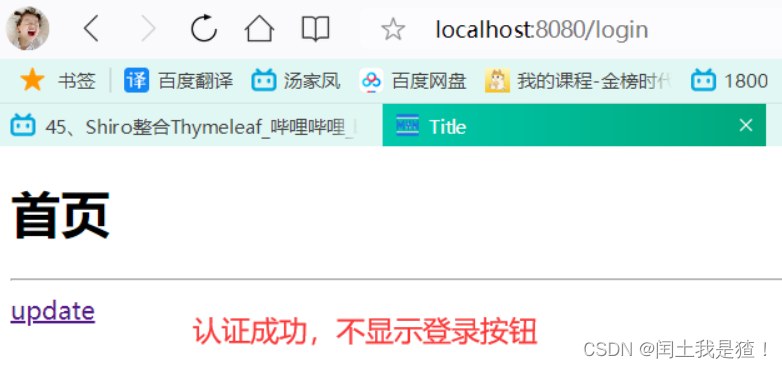
Shiro整合Thymeleaf
pom.xml
<!-- shiro整合thymeleaf -->
<dependency>
<groupId>com.github.theborakompanioni</groupId>
<artifactId>thymeleaf-extras-shiro</artifactId>
<version>2.0.0</version>
</dependency>
ShiroConfig
//整合ShiroDialect:用来整合shiro thymeleaf
@Bean
public ShiroDialect getShiroDialect(){
return new ShiroDialect();
}
index.html
<!DOCTYPE html>
<html lang="en"
xmlns:th="http://www.thymeleaf.org"
xmlns:shiro="http://www.thymeleaf.org/thymeleaf-extras-shiro">
<head>
<meta charset="UTF-8">
<title>Title</title>
</head>
<body>
<h1>首页</h1>
<p th:text="${msg}"></p>
<hr/>
<a th:href="@{/user/login}">登录</a>
<!-- 如果有user:add这个权限就显示下面的内容 -->
<div shiro:hasPermission="user:add">
<a th:href="@{user/add}">add</a>
</div>
<!-- 如果有user:update这个权限就显示下面的内容 -->
<div shiro:hasPermission="user:update">
<a th:href="@{user/update}">update</a>
</div>
</body>
</html>



<!--没有认证 才显示 ,认证成功不显示(登录)-->
<div shiro:notAuthenticated>
<a th:href="@{/login}">登录</a>
</div>
注销
ShiroConfig
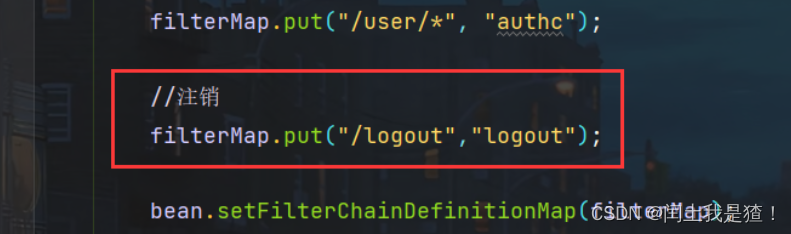
//注销
filterMap.put("/logout","logout");
Controller
@RequestMapping("/logout")
public String logout(){
return "redirect:/user/login";
}
index.html
<!-- 认证成功才显示 -->
<div shiro:authenticated>
<a th:href="@{/logout}">注销</a>
</div>























 1797
1797











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








