一、官方文档
为保证安装成功,安装顺序尽可能和官方文档保持一致,如果没有在文档中体现,往往是因为不需要具体操作步骤。在没有特别说明的情况下,操作步骤需要在每个节点执行。
使用kubeadm安装kubernetes主要分两个大的步骤:
第一步:所有节点安装kubeadm
第二步:使用kubeadm引导kubernetes部署,包括在主节点初始化kubernetes集群,其他节点接入kubernetes集群。
本文主要说明第一步:安装kubeadm。
二、环境准备
2.1 虚机信息
- vmware workstation pro 16.5.2
- ubuntu-22.04.4-live-server-amd64.iso
- 部署3台虚机
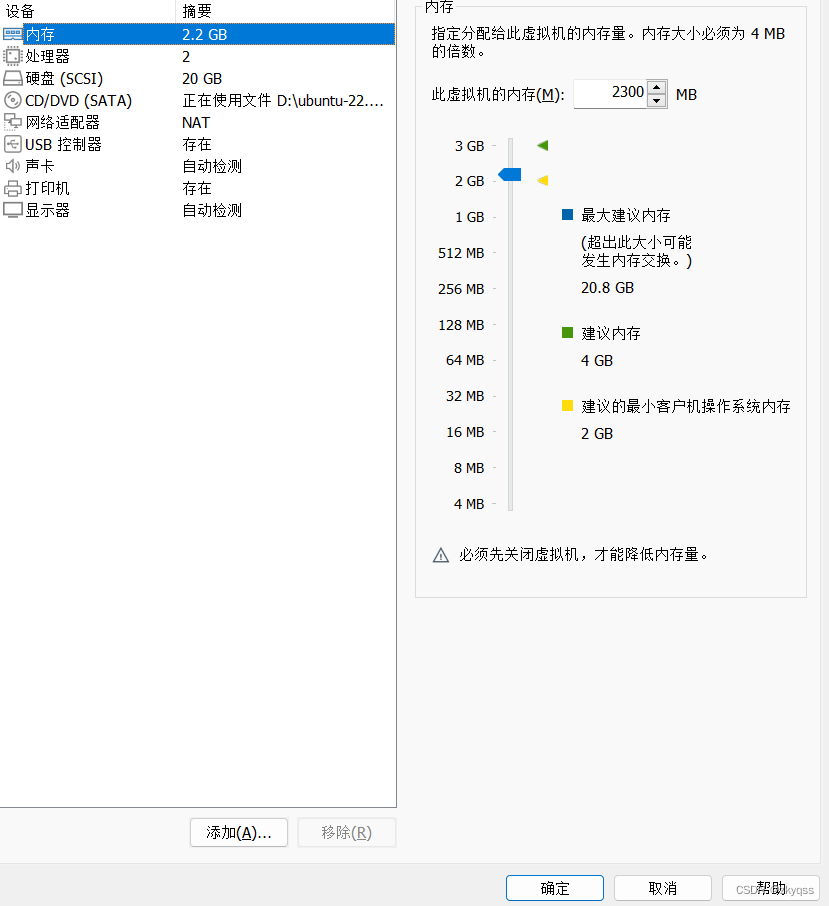
- 内存:2.2 G
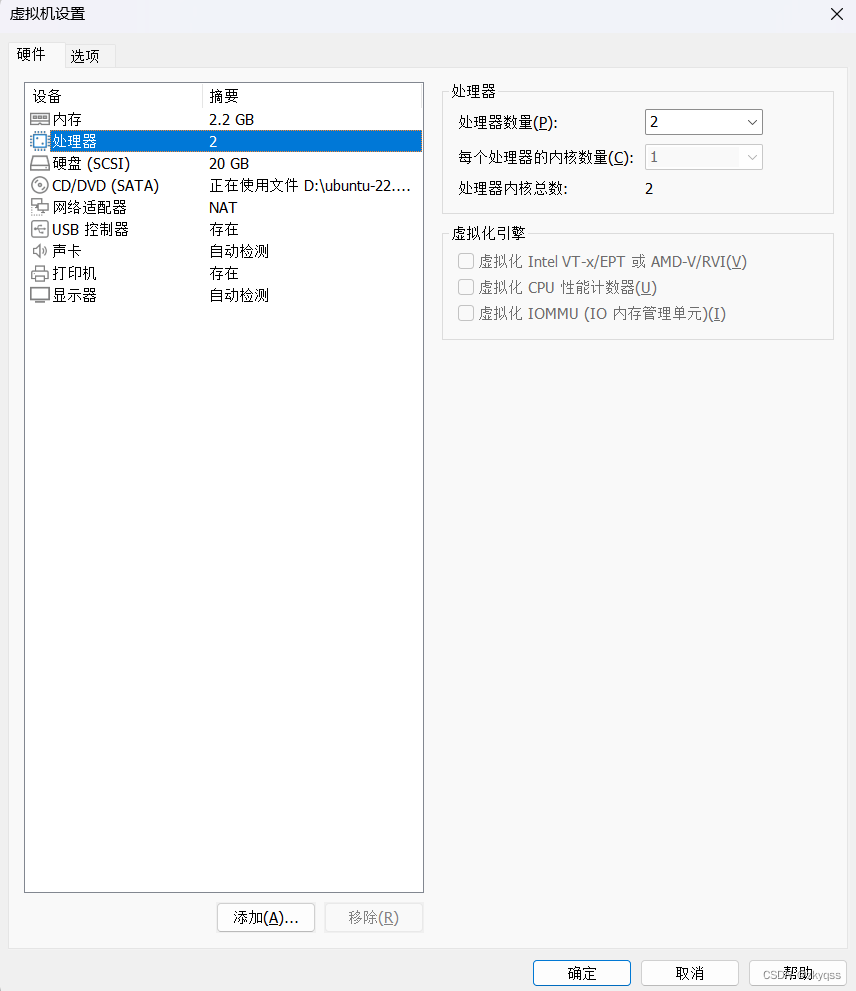
- CPU: 2
- 网卡
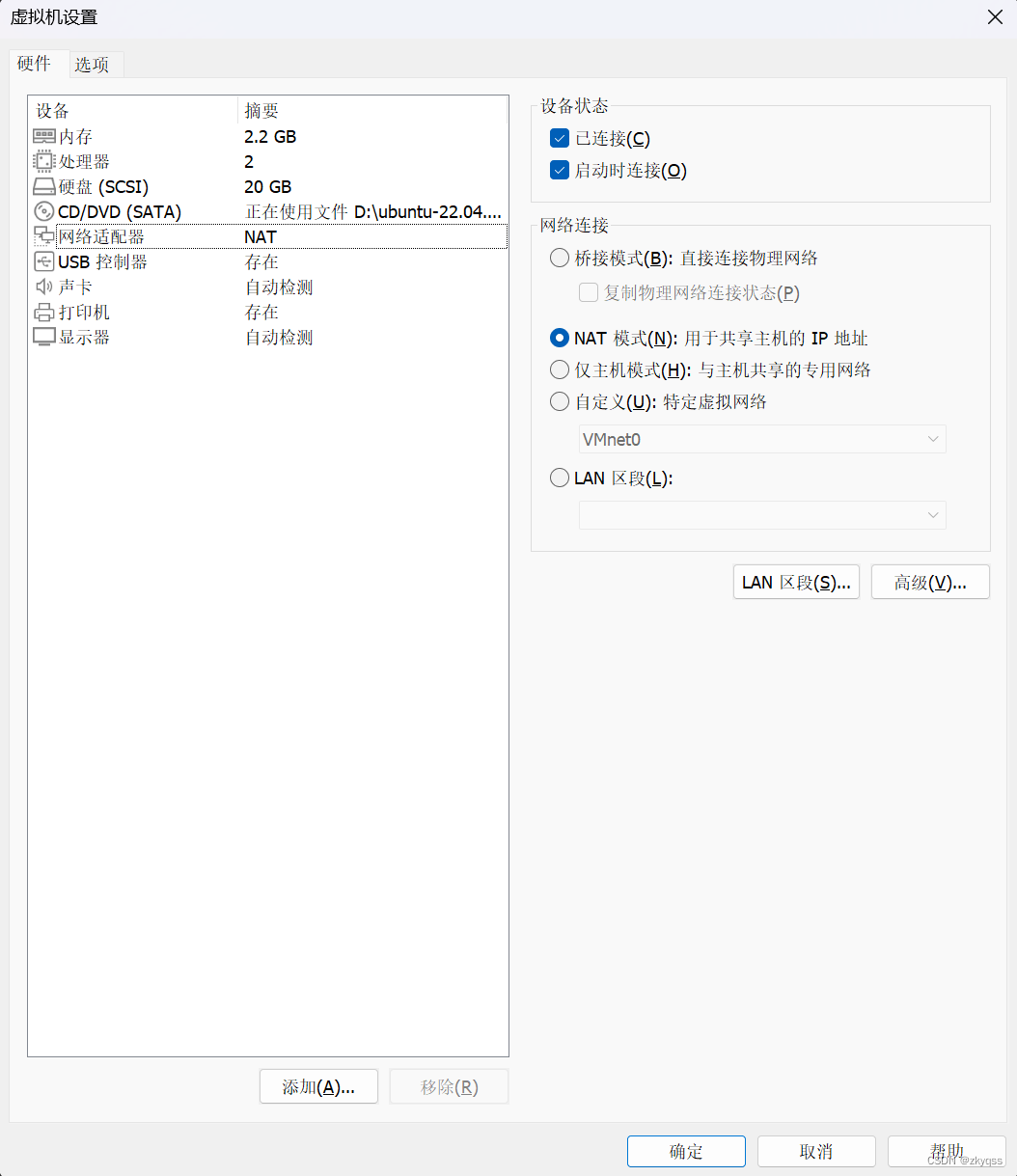
三台虚机各配置1块网卡,静态设置IP地址,三台虚机IP地址分别为:11.0.1.21/24,11.0.1.22/24,11.0.1.23/24。IP地址可以在安装ubuntu的时侯设置,也可以安装完成后修改网卡配置文件:
lxhub@k8s-1:~$ sudo cat /etc/netplan/00-installer-config.yaml
[sudo] password for lxhub:
# This is the network config written by 'subiquity'
network:
ethernets:
ens33:
addresses:
- 11.0.1.21/24
nameservers:
addresses:
- 11.0.1.2
search: []
routes:
- to: default
via: 11.0.1.2
version: 2
lxhub@k8s-1:~$ 2.2 Disable swap
1、sudo swapoff -a
2、编辑/etc/fstab,注释含有swap的语句
3、删除/swap.img
运行实例:
lxhub@k8s-1:~$ sudo swapoff -a
[sudo] password for lxhub:
lxhub@k8s-1:~$
lxhub@k8s-1:~$ cat /etc/fstab
# /etc/fstab: static file system information.
#
# Use 'blkid' to print the universally unique identifier for a
# device; this may be used with UUID= as a more robust way to name devices
# that works even if disks are added and removed. See fstab(5).
#
# <file system> <mount point> <type> <options> <dump> <pass>
# / was on /dev/ubuntu-vg/ubuntu-lv during curtin installation
/dev/disk/by-id/dm-uuid-LVM-pevVPMemSMXfdUNOJelGQodHMOMCVebvlfGn00He3Ng3cYecBS22jMkc882iZRnm / ext4 defaults 0 1
# /boot was on /dev/sda2 during curtin installation
/dev/disk/by-uuid/0aeab3a7-ed4b-43e8-9049-f761f861a0d2 /boot ext4 defaults 0 1
/swap.img none swap sw 0 0
lxhub@k8s-1:~$ sudo vi /etc/fstab
lxhub@k8s-1:~$ cat /etc/fstab
# /etc/fstab: static file system information.
#
# Use 'blkid' to print the universally unique identifier for a
# device; this may be used with UUID= as a more robust way to name devices
# that works even if disks are added and removed. See fstab(5).
#
# <file system> <mount point> <type> <options> <dump> <pass>
# / was on /dev/ubuntu-vg/ubuntu-lv during curtin installation
/dev/disk/by-id/dm-uuid-LVM-pevVPMemSMXfdUNOJelGQodHMOMCVebvlfGn00He3Ng3cYecBS22jMkc882iZRnm / ext4 defaults 0 1
# /boot was on /dev/sda2 during curtin installation
/dev/disk/by-uuid/0aeab3a7-ed4b-43e8-9049-f761f861a0d2 /boot ext4 defaults 0 1
# /swap.img none swap sw 0 0
lxhub@k8s-1:~$
lxhub@k8s-1:/$ sudo rm /swap.img
检查命令:
lxhub@k8s-1:~$ systemctl list-units --type=swap
UNIT LOAD ACTIVE SUB DESCRIPTION
0 loaded units listed. Pass --all to see loaded but inactive units, too.
To show all installed unit files use 'systemctl list-unit-files'.
lxhub@k8s-1:~$ free -m
total used free shared buff/cache available
Mem: 2173 296 1117 1 759 1711
Swap: 0 0 0
lxhub@k8s-1:~$三、安装container runtime
为了在Pod中运行容器,Kubernetes使用容器运行时。
默认情况下,Kubernetes使用容器运行时接口(Container Runtime Interface,CRI)与选择的容器运行时进行接口交互。
3.1 Container Runtimes
打开Container Runtimes网页,根据网页内容进行安装。
Kubernetes 1.29要求使用符合容器运行时接口(Container Runtime Interface,CRI)的运行时。
本文选择containerd容器运行时进行安装。
3.1.1 启用IPv4转发和让iptables能够看到桥接流量
执行命令:
cat <<EOF | sudo tee /etc/modules-load.d/k8s.conf
overlay
br_netfilter
EOF
sudo modprobe overlay
sudo modprobe br_netfilter
# sysctl params required by setup, params persist across reboots
cat <<EOF | sudo tee /etc/sysctl.d/k8s.conf
net.bridge.bridge-nf-call-iptables = 1
net.bridge.bridge-nf-call-ip6tables = 1
net.ipv4.ip_forward = 1
EOF
# Apply sysctl params without reboot
sudo sysctl --system验证br_netfilter和overlay模块是否已加载,如果输出中包含这些模块的名称,则表示它们已成功加载到内核中。
lsmod | grep br_netfilter
lsmod | grep overlay
运行实例:
lxhub@k8s-1:~$ lsmod | grep br_netfilter
br_netfilter 32768 0
bridge 307200 1 br_netfilter
lxhub@k8s-1:~$ lsmod | grep overlay
overlay 151552 0验证net.bridge.bridge-nf-call-iptables,net.bridge.bridge-nf-call-ip6tables和net.ipv4.ip_forward系统变量是否设置为1,运行以下命令:
sysctl net.bridge.bridge-nf-call-iptables net.bridge.bridge-nf-call-ip6tables net.ipv4.ip_forward
运行实例:
lxhub@k8s-1:~$ sysctl net.bridge.bridge-nf-call-iptables net.bridge.bridge-nf-call-ip6tables net.ipv4.ip_forward
net.bridge.bridge-nf-call-iptables = 1
net.bridge.bridge-nf-call-ip6tables = 1
net.ipv4.ip_forward = 13.1.2 cgroup drivers选择
在Linux系统中,控制组(Control Groups,通常简称为cgroups)是一种内核特性,用于限制和管理系统中各个进程组(或任务组)可以使用的资源。这种资源可以包括CPU、内存、磁盘I/O、网络带宽等。
kubelet和底层的容器运行时都需要与控制组(cgroups)进行交互,以实施对Pod和容器的资源管理,并设置资源请求和限制,如CPU和内存。
1、kubelet
- kubelet是在每个Kubernetes节点上运行的主要代理程序,负责管理节点上的Pod生命周期。它通过与容器运行时(如Docker、containerd等)交互来创建、销毁和监控容器。
- 当kubelet接收到要调度的Pod的规范时,它会检查Pod的资源请求和限制,并将这些信息传递给容器运行时,以便容器运行时能够在创建容器时设置正确的cgroup限制。
- 通过与cgroups进行交互,kubelet可以监视和限制Pod使用的资源,确保它们不会超出预期的限制。
2、容器运行时
- 底层的容器运行时(如Docker、containerd等)负责实际创建和管理容器。
- 当容器运行时收到kubelet发送的要求创建容器的请求时,它会根据kubelet提供的Pod规范中定义的资源请求和限制,将这些信息传递给cgroups,并在创建容器时设置相应的资源限制。
- 通过与cgroups进行交互,容器运行时可以确保创建的容器不会超出指定的CPU和内存限制,从而有效地管理资源,并保证容器间的资源隔离和公平共享。
综上所述,kubelet和容器运行时通过与cgroups进行交互,有效地实现了对Pod和容器的资源管理,包括设置资源请求和限制,并确保集群中的工作负载能够得到适当的资源分配和限制。
为了与控制组(cgroups)进行交互,kubelet和容器运行时需要使用cgroup驱动程序。cgroup驱动程序负责与Linux内核中的cgroups子系统通信,并执行相应的操作,如设置资源限制、监视资源使用等。
两个主要cgroup驱动程序是cgroupfs和systemd。
1、cgroupfs:cgroup 文件系统是 Linux 内核中早期引入的一种 cgroup 实现方式。它通过挂载 cgroup 文件系统来管理控制组,并提供了一组文件和目录,用于配置和监视控制组。cgroupfs 驱动程序通常在不使用 systemd 作为 init 系统的 Linux 发行版上使用。
2、systemd:systemd 是一个系统和服务管理器,也是一种 init 系统。它集成了对控制组的支持,并提供了一种称为 systemd-cgroups-agent 的功能,用于与 cgroup 控制器通信。systemd 驱动程序通常在使用 systemd 作为 init 系统的 Linux 发行版上使用,如最新版本的 Ubuntu、Fedora 等。
在 Kubernetes 环境中,kubelet 和容器运行时必须使用相同的 cgroup 驱动程序,以确保资源管理的一致性和可靠性。
在使用 systemd 作为 init 系统时,将 systemd 作为 Kubelet 和容器运行时(如 Docker、containerd)的 cgroup 驱动是一种推荐的配置方式。
3.1.3 kubelet设置systemd cgroup driver
从 Kubernetes v1.22 版本开始,当使用 kubeadm 创建集群时,如果用户没有在 KubeletConfiguration 中设置 cgroupDriver 字段,kubeadm 会默认将其设置为 systemd。这意味着在大多数情况下,用户无需手动配置 Kubelet 的 cgroup 驱动,kubeadm 会自动进行适当的配置。
containerd设置systemd cgroup driver必须在安装containerd后完成。所以首先要进行containerd的安装。所有这一步会在containerd中说明。
3.2 containerd的安装
3.2.1 选择安装方式
打开Getting started with containerd网页,根据网页内容进行安装。
安装containerd的方式有多种,这里使用 apt-get 来安装 containerd.io 包。
containerd.io 包含 runc,但不包含 CNI 插件。在安装和配置 containerd.io 之后,如果需要 CNI 插件(通常用于 Kubernetes 网络配置),需要单独安装它们。
3.2.2 在 Ubuntu 上安装containerd
打开Install Docker Engine on Ubuntu网页,根据网页内容进行安装。
1、设置 Docker 的 apt 仓库
# Add Docker's official GPG key:
sudo apt-get update
sudo apt-get install ca-certificates curl
sudo install -m 0755 -d /etc/apt/keyrings
sudo curl -fsSL https://download.docker.com/linux/ubuntu/gpg -o /etc/apt/keyrings/docker.asc
sudo chmod a+r /etc/apt/keyrings/docker.asc
# Add the repository to Apt sources:
echo \
"deb [arch=$(dpkg --print-architecture) signed-by=/etc/apt/keyrings/docker.asc] https://download.docker.com/linux/ubuntu \
$(. /etc/os-release && echo "$VERSION_CODENAME") stable" | \
sudo tee /etc/apt/sources.list.d/docker.list > /dev/null
sudo apt-get update
验证:
lxhub@k8s-1:/$ cat /etc/apt/sources.list.d/docker.list
deb [arch=amd64 signed-by=/etc/apt/keyrings/docker.asc] https://download.docker.com/linux/ubuntu jammy stable
2、安装conterd.io(注意,只安装containerd.io,不按照docker)
sudo apt-get install containerd.io
运行实例:
lxhub@k8s-1:~$ sudo apt-get install containerd.io
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
The following NEW packages will be installed:
containerd.io
0 upgraded, 1 newly installed, 0 to remove and 18 not upgraded.
Need to get 29.8 MB of archives.
After this operation, 118 MB of additional disk space will be used.
Get:1 https://download.docker.com/linux/ubuntu jammy/stable amd64 containerd.io amd64 1.6.31-1 [29.8 MB]
Fetched 29.8 MB in 3s (9,582 kB/s)
Selecting previously unselected package containerd.io.
(Reading database ... 74545 files and directories currently installed.)
Preparing to unpack .../containerd.io_1.6.31-1_amd64.deb ...
Unpacking containerd.io (1.6.31-1) ...
Setting up containerd.io (1.6.31-1) ...
Created symlink /etc/systemd/system/multi-user.target.wants/containerd.service → /lib/systemd/system/containerd.service.
Processing triggers for man-db (2.10.2-1) ...
Scanning processes...
Scanning linux images...
Running kernel seems to be up-to-date.
No services need to be restarted.
No containers need to be restarted.
No user sessions are running outdated binaries.
No VM guests are running outdated hypervisor (qemu) binaries on this host.
lxhub@k8s-1:~$
验证命令:
lxhub@k8s-1:~$ containerd --version
containerd containerd.io 1.6.31 e377cd56a71523140ca6ae87e30244719194a521
lxhub@k8s-1:~$
lxhub@k8s-1:~$ sudo systemctl status containerd
● containerd.service - containerd container runtime
Loaded: loaded (/lib/systemd/system/containerd.service; enabled; vendor preset: enabled)
Active: active (running) since Fri 2024-05-17 23:16:03 UTC; 12min ago
Docs: https://containerd.io
Process: 2202 ExecStartPre=/sbin/modprobe overlay (code=exited, status=0/SUCCESS)
Main PID: 2203 (containerd)
Tasks: 8
Memory: 11.9M
CPU: 3.153s
CGroup: /system.slice/containerd.service
└─2203 /usr/bin/containerd
...
3.2.3 containerd设置systemd cgroup driver
1、reset config.toml
lxhub@k8s-1:~$ sudo -i
root@k8s-1:~# containerd config default > /etc/containerd/config.toml 2、编辑config.toml
设置:SystemdCgroup = true
root@k8s-1:~# vi /etc/containerd/config.toml
...
[plugins."io.containerd.grpc.v1.cri".containerd.runtimes.runc.options]
SystemdCgroup = true
...3、重启containerd
root@k8s-1:~# systemctl restart containerd
root@k8s-1:~# systemctl enable containerd四、安装kubeadm, kubelet和kubectl
kubeadm: 用于集群引导和配置的工具。kubelet: 运行在每个节点上,负责管理节点上的容器和 Pod。kubectl: 用于与 Kubernetes 集群通信和管理的命令行工具。
1、更新 apt 包索引并安装使用 Kubernetes apt 仓库所需的软件包
sudo apt-get update
# apt-transport-https may be a dummy package; if so, you can skip that package
sudo apt-get install -y apt-transport-https ca-certificates curl gpg2、Download the public signing key for the Kubernetes package repositories. 下载 Kubernetes 包仓库的公共签名密钥
# If the directory `/etc/apt/keyrings` does not exist, it should be created before the curl command, read the note below.
# sudo mkdir -p -m 755 /etc/apt/keyrings
curl -fsSL https://pkgs.k8s.io/core:/stable:/v1.29/deb/Release.key | sudo gpg --dearmor -o /etc/apt/keyrings/kubernetes-apt-keyring.gpg
操作实例:
lxhub@k8s-1:/etc/apt/keyrings$ ls
docker.asc <--之前安装containerd.io步骤是添加的
lxhub@k8s-1:/etc/apt/keyrings$ curl -fsSL https://pkgs.k8s.io/core:/stable:/v1.29/deb/Release.key | sudo gpg --dearmor -o /etc/apt/keyrings/kubernetes-apt-keyring.gpg
lxhub@k8s-1:/etc/apt/keyrings$ ls
docker.asc kubernetes-apt-keyring.gpg <-- Kubernetes软件包仓库公共签名密钥
3、Add the appropriate Kubernetes apt repository.注意版本号是1.29.
# This overwrites any existing configuration in /etc/apt/sources.list.d/kubernetes.list
echo 'deb [signed-by=/etc/apt/keyrings/kubernetes-apt-keyring.gpg] https://pkgs.k8s.io/core:/stable:/v1.29/deb/ /' | sudo tee /etc/apt/sources.list.d/kubernetes.list
操作实例:
lxhub@k8s-1:/etc/apt/sources.list.d$ cat kubernetes.list
deb [signed-by=/etc/apt/keyrings/kubernetes-apt-keyring.gpg] https://pkgs.k8s.io/core:/stable:/v1.29/deb/ /4、Update the apt package index, install kubelet, kubeadm and kubectl, and pin their version:
sudo apt-get update
sudo apt-get install -y kubelet kubeadm kubectl
sudo apt-mark hold kubelet kubeadm kubectl
版本:
lxhub@k8s-1:/$ kubeadm version
kubeadm version: &version.Info{Major:"1", Minor:"29", GitVersion:"v1.29.5", GitCommit:"59755ff595fa4526236b0cc03aa2242d941a5171", GitTreeState:"clean", BuildDate:"2024-05-14T10:44:51Z", GoVersion:"go1.21.9", Compiler:"gc", Platform:"linux/amd64"}
lxhub@k8s-1:/$ kubectl version
Client Version: v1.29.5
Kustomize Version: v5.0.4-0.20230601165947-6ce0bf390ce3
The connection to the server localhost:8080 was refused - did you specify the right host or port?
lxhub@k8s-1:/$ kubelet --version
Kubernetes v1.29.5
lxhub@k8s-1:/$以上步骤需要在所有节点执行!!!
接下来使用kubeadm引导安装kubernetes集群。








 https://v1-29.docs.kubernetes.io/docs/setup/production-environment/tools/kubeadm/install-kubeadm/
https://v1-29.docs.kubernetes.io/docs/setup/production-environment/tools/kubeadm/install-kubeadm/















 762
762

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








