哥们太垃圾了,看着人家嘎嘎拿分。。。
robots协议
访问/robots.txt
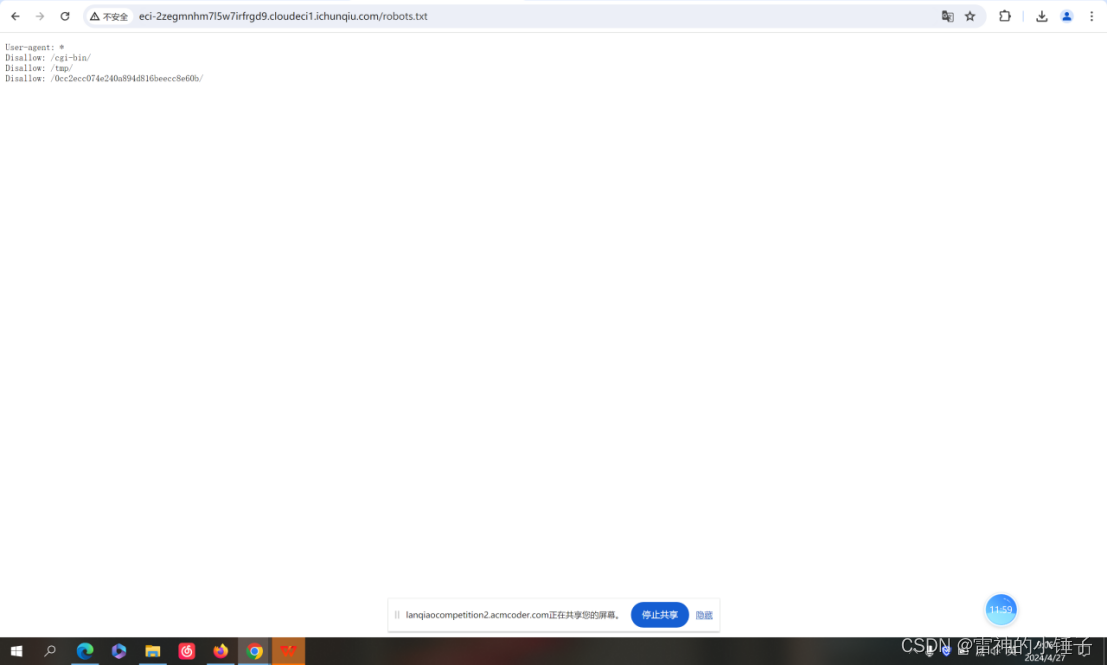
再拼接访问:
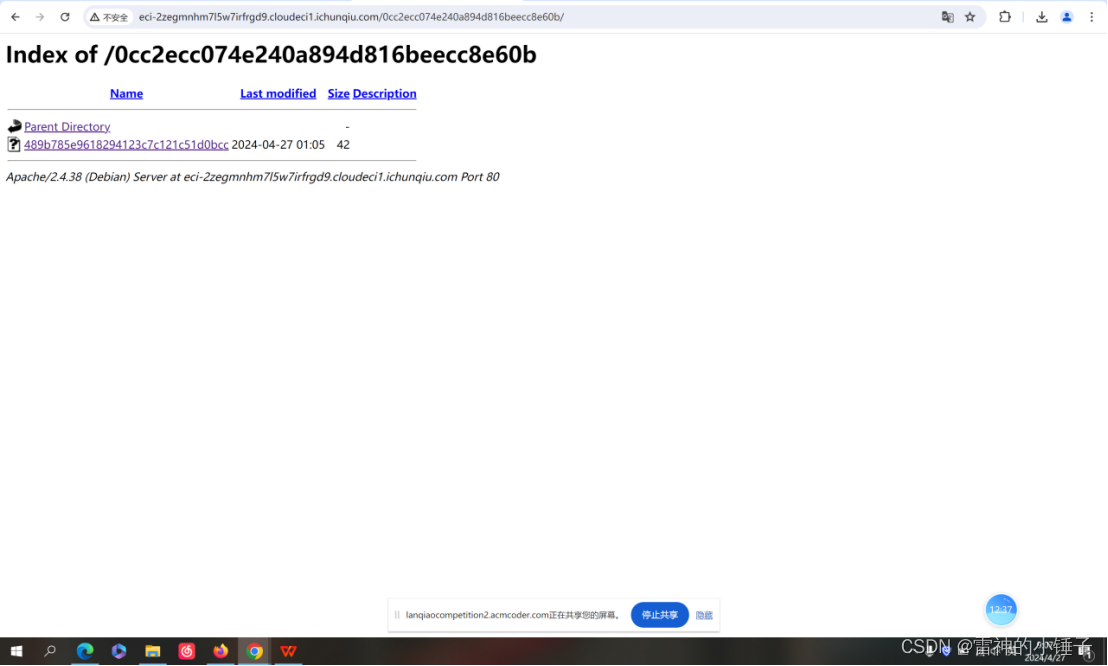
点击
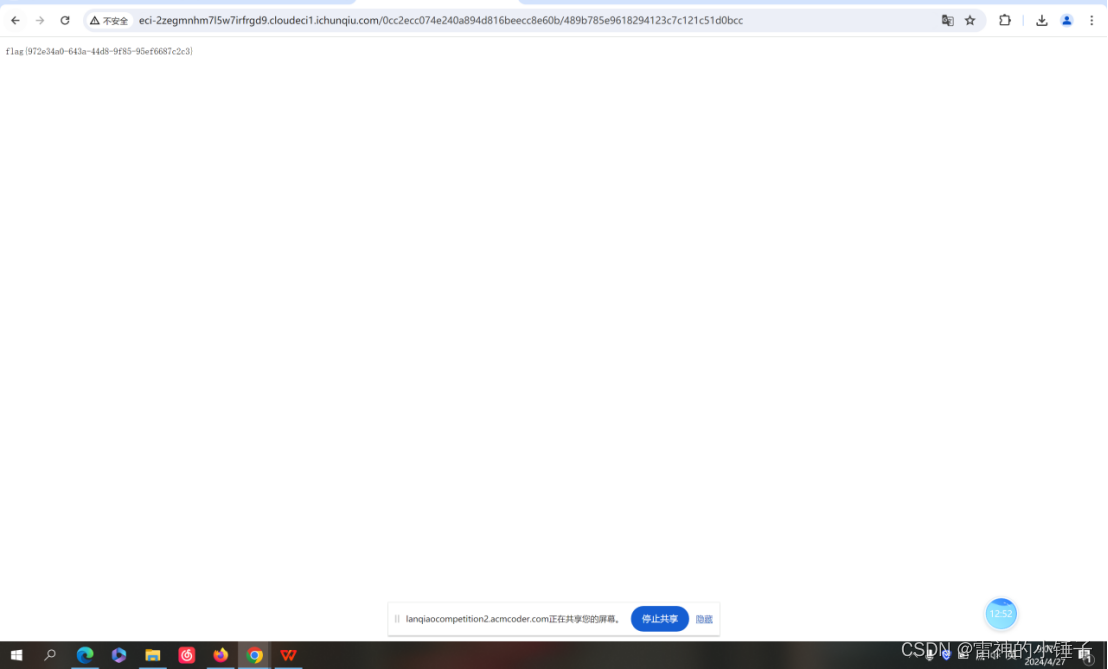
得到flag
Packet
拿到数据包,放入wireshark分析
查找flag字样数据:
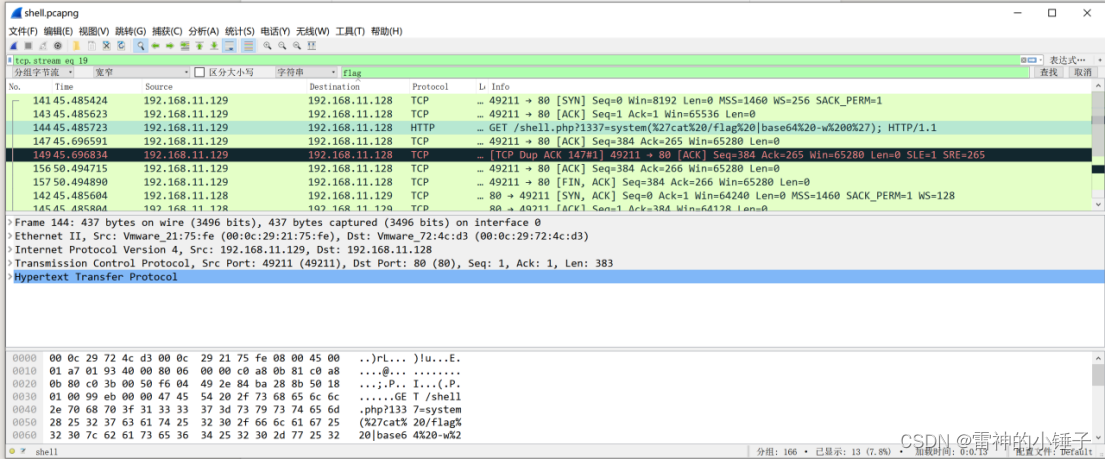
得到可疑:
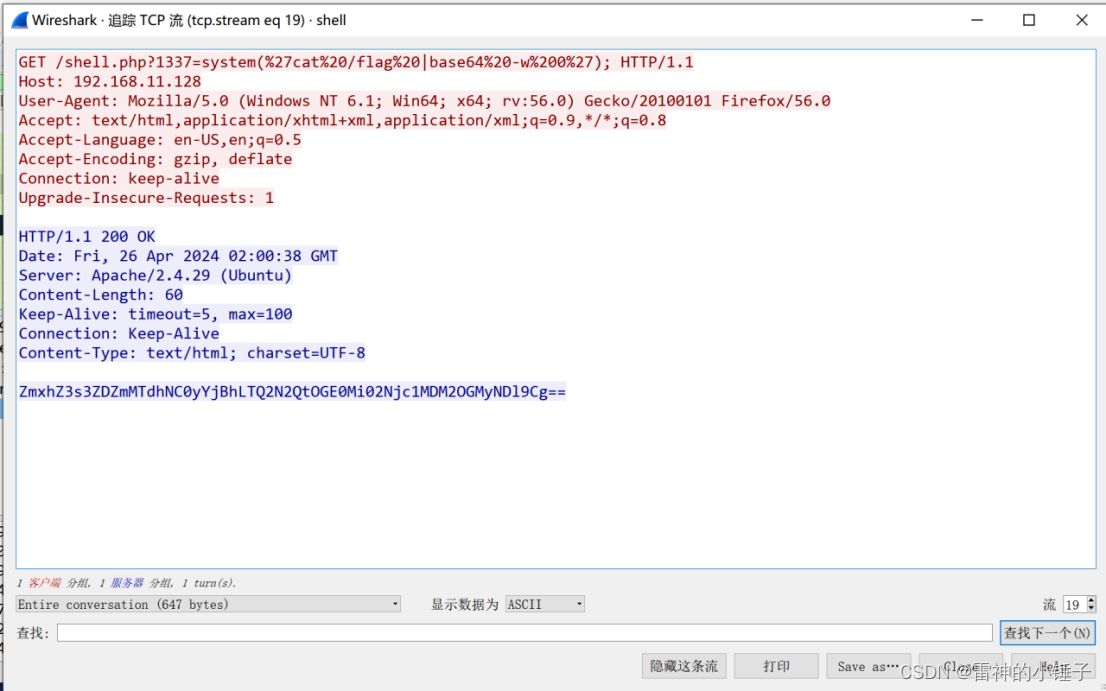
Base64解密:
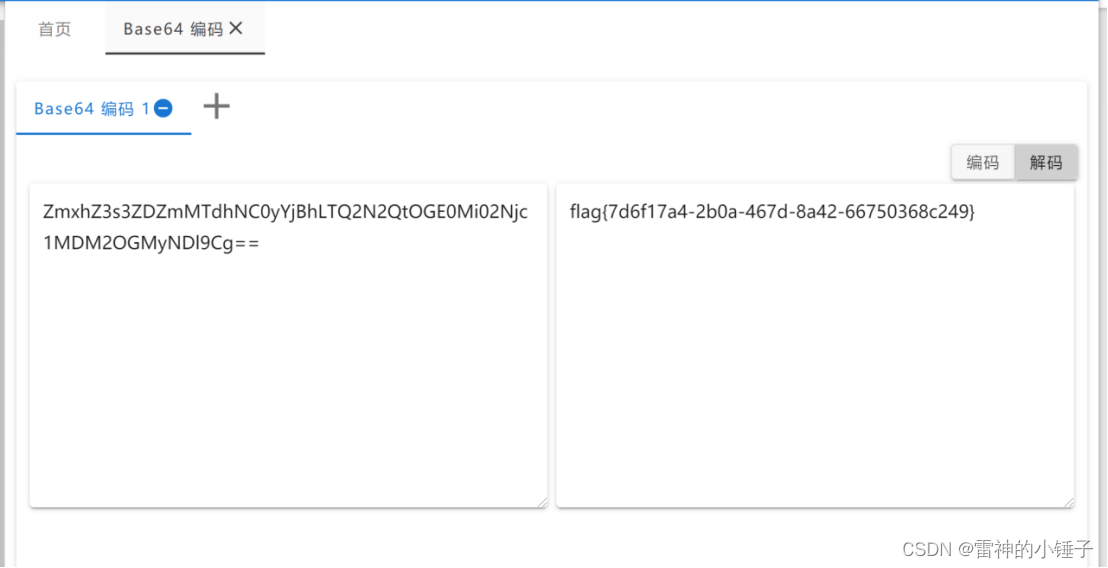
得到flag
Cc:
打开得到加密流程后:
使用离线版解密:

得到flag
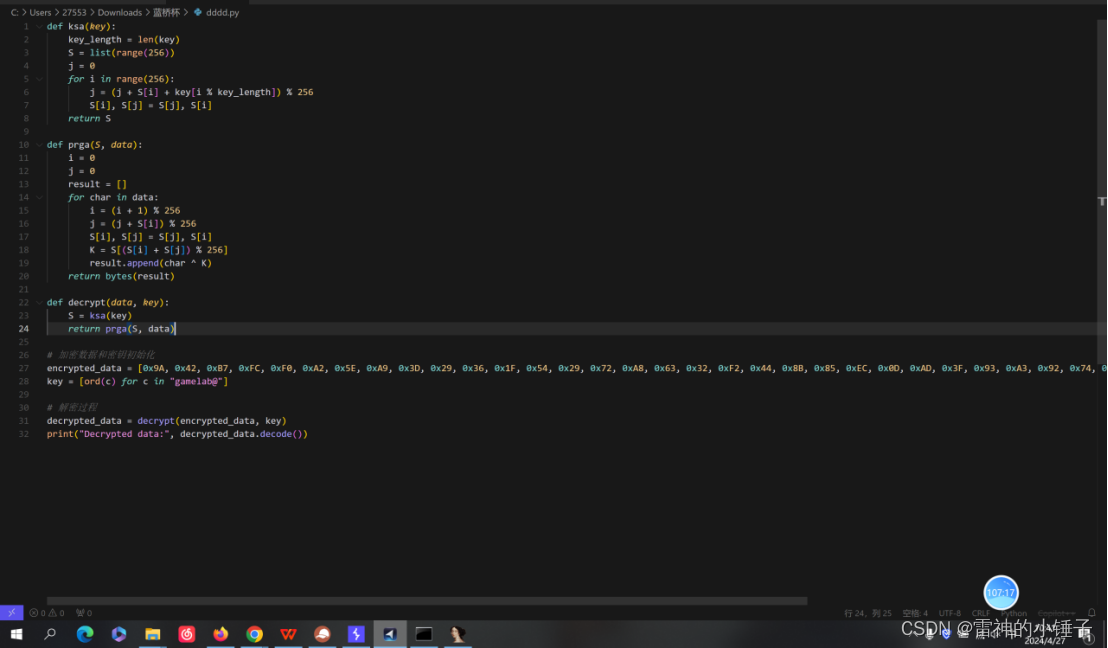
Rc4:
def ksa(key):
key_length = len(key)
S = list(range(256))
j = 0
for i in range(256):
j = (j + S[i] + key[i % key_length]) % 256
S[i], S[j] = S[j], S[i]
return S
def prga(S, data):
i = 0
j = 0
result = []
for char in data:
i = (i + 1) % 256
j = (j + S[i]) % 256
S[i], S[j] = S[j], S[i]
K = S[(S[i] + S[j]) % 256]
result.append(char ^ K)
return bytes(result)
def decrypt(data, key):
S = ksa(key)
return prga(S, data)
# 加密数据和密钥初始化
encrypted_data = [0x9A, 0x42, 0xB7, 0xFC, 0xF0, 0xA2, 0x5E, 0xA9, 0x3D, 0x29, 0x36, 0x1F, 0x54, 0x29, 0x72, 0xA8, 0x63, 0x32, 0xF2, 0x44, 0x8B, 0x85, 0xEC, 0x0D, 0xAD, 0x3F, 0x93, 0xA3, 0x92, 0x74, 0x81, 0x65, 0x69, 0xEC, 0xE4, 0x39, 0x85, 0xA9, 0xCA, 0xAF, 0xB2, 0xC6]
key = [ord(c) for c in "gamelab@"]
# 解密过程
decrypted_data = decrypt(encrypted_data, key)
print("Decrypted data:", decrypted_data.decode())
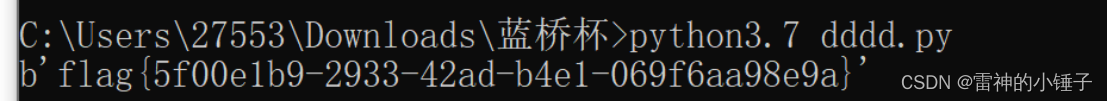
运行解密脚本得到flag
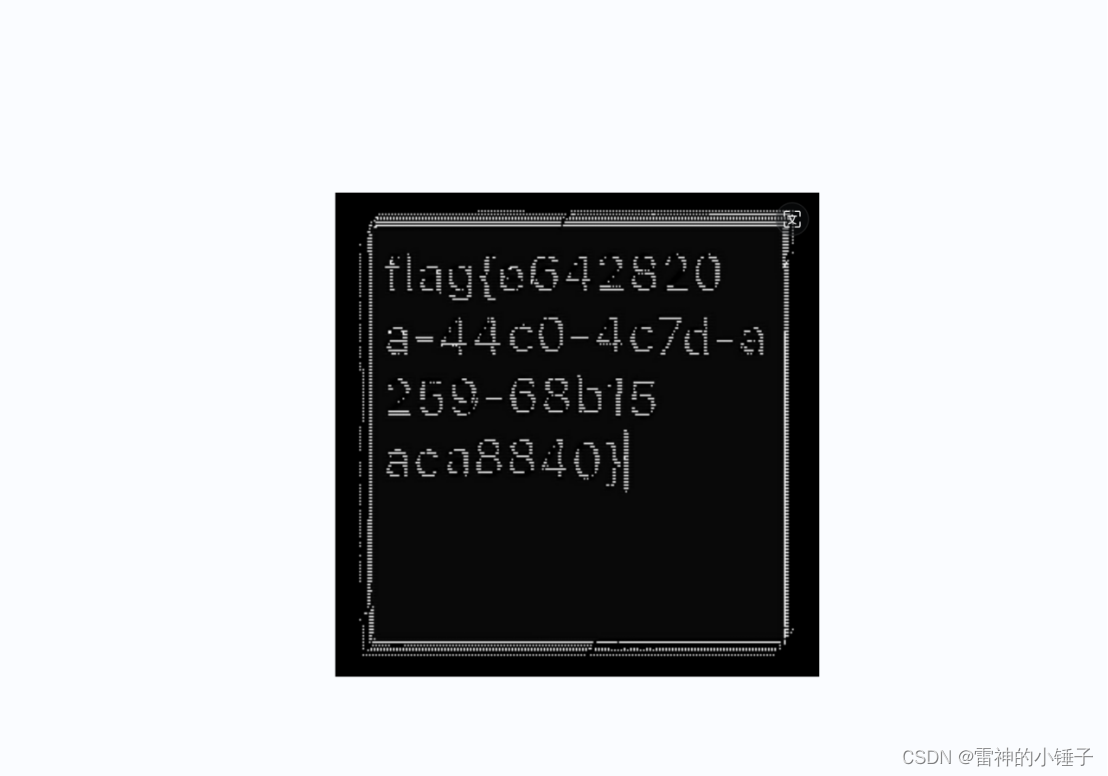
缺失的数据:
分析脚本,发现脚本有错误,未定义,缩进等问题:
修改后:
import cv2
import numpy as np
import pywt
class WaterMarkDWT:
def __init__(self, origin: str, watermark: str, key: int, weight: list):
self.key = key
self.img = cv2.imread(origin)
self.mark = cv2.imread(watermark)
self.coef = weight
def arnold(self, img):
r, c = img.shape
p = np.zeros((r, c), np.uint8)
a, b = 1, 1
for k in range(self.key):
for i in range(r):
for j in range(c):
x = (i + b * j) % r
y = (a * i + (a * b + 1) * j) % c
p[x, y] = img[i, j]
return p
def deArnold(self, img):
r, c = img.shape
p = np.zeros((r, c), np.uint8)
a, b = 1, 1
for k in range(self.key):
for i in range(r):
for j in range(c):
x = ((a * b + 1) * i - b * j) % r
y = (-a * i + j) % c
p[x, y] = img[i, j]
return p
def get(self, size: tuple = (1200, 1200), flag: int = None):
img = cv2.resize(self.img, size)
img1 = cv2.cvtColor(img, cv2.COLOR_RGB2GRAY)
img2 = cv2.cvtColor(self.mark, cv2.COLOR_RGB2GRAY)
c = pywt.wavedec2(img2, 'db2', level=3)
[cl, (cH3, cV3, cD3), (cH2, cV2, cD2), (cH1, cV1, cD1)] = c
d = pywt.wavedec2(img1, 'db2', level=3)
[dl, (dH3, dV3, dD3), (dH2, dV2, dD2), (dH1, dV1, dD1)] = d
a1, a2, a3, a4 = self.coef
ca1 = (cl - dl) * a1
ch1 = (cH3 - dH3) * a2
cv1 = (cV3 - dV3) * a3
cd1 = (cD3 - dD3) * a4
waterImg = pywt.waverec2([ca1, (ch1, cv1, cd1)], 'db2')
waterImg = np.array(waterImg, np.uint8)
waterImg = self.deArnold(waterImg)
kernel = np.ones((3, 3), np.uint8)
if flag == 0:
waterImg = cv2.erode(waterImg, kernel)
elif flag == 1:
waterImg = cv2.dilate(waterImg, kernel)
cv2.imwrite('水印.png', waterImg)
return waterImg
if __name__ == '__main__':
origin_img = 'a.png'
watermark_img = 'newImg.png'
k = 20
xs = [0.2, 0.2, 0.5, 0.4]
W1 = WaterMarkDWT(origin_img, watermark_img, k, xs)
watermarked_image = W1.get()
print("Watermarking completed.")
运行脚本:得到flag
Theorem:
首先使用本地脚本分离出p,q(n比较小可以直接分离)
from Crypto.Util.number import *
from gmpy2 import *
# 已知的RSA参数和密文
n = 94581028682900113123648734937784634645486813867065294159875516514520556881461611966096883566806571691879115766917833117123695776131443081658364855087575006641022211136751071900710589699171982563753011439999297865781908255529833932820965169382130385236359802696280004495552191520878864368741633686036192501791
e = 65537
c = 36423517465893675519815622861961872192784685202298519340922692662559402449554596309518386263035128551037586034375613936036935256444185038640625700728791201299960866688949056632874866621825012134973285965672502404517179243752689740766636653543223559495428281042737266438408338914031484466542505299050233075829
# 从n分解得到的p和q
p = 9725277820345294029015692786209306694836079927617586357442724339468673996231042839233529246844794558371350733017150605931603344334330882328076640690156717
q = 9725277820345294029015692786209306694836079927617586357442724339468673996231042839233529246844794558371350733017150605931603344334330882328076640690156923
# 计算phi(n)
phi = (p - 1) * (q - 1)
# 计算d
d = invert(e, phi)
# 使用CRT进行解密
m1 = powmod(c, d % (p - 1), p)
m2 = powmod(c, d % (q - 1), q)
h = invert(p, q)
m = (m1 + p * ((m2 - m1) * h % q)) % n
# 将解密后的数字转换回字节串
flag = long_to_bytes(m)
print(flag)
运行脚本得到flag





















 2248
2248

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








