[2019红帽杯]easyRE
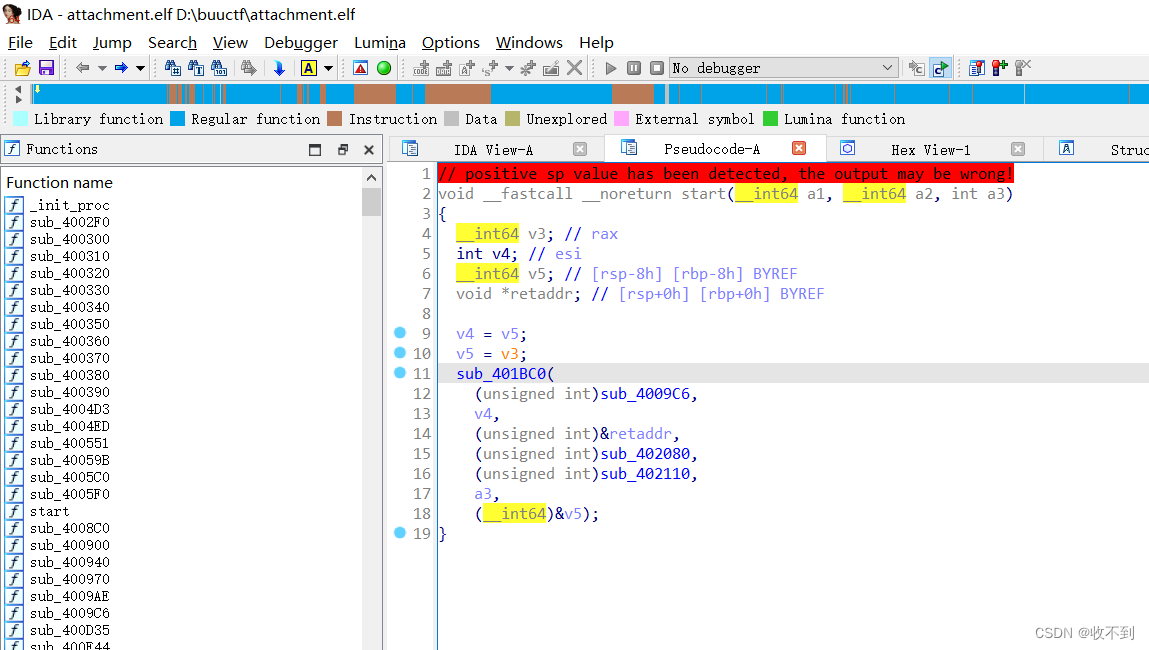
.elf文件64位
ida打开好奇怪啊
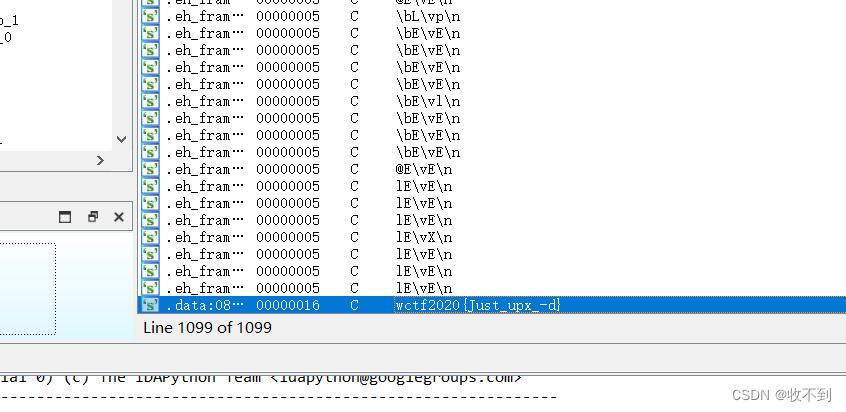
shift +12
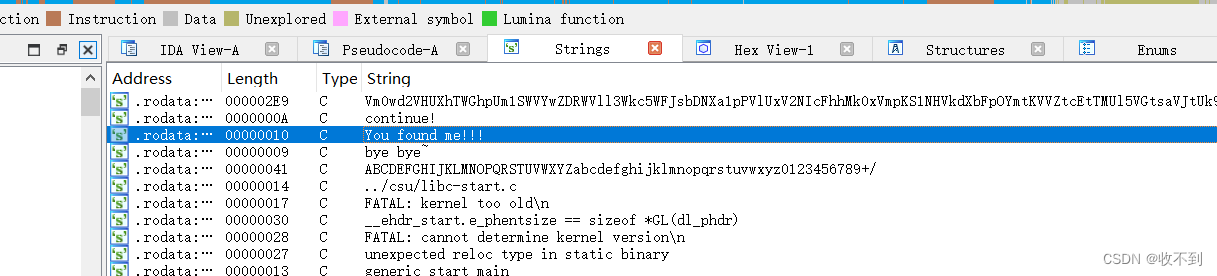
那个you found me交叉引用Ctl X(反编译不了好怪啊)
进入4009C6
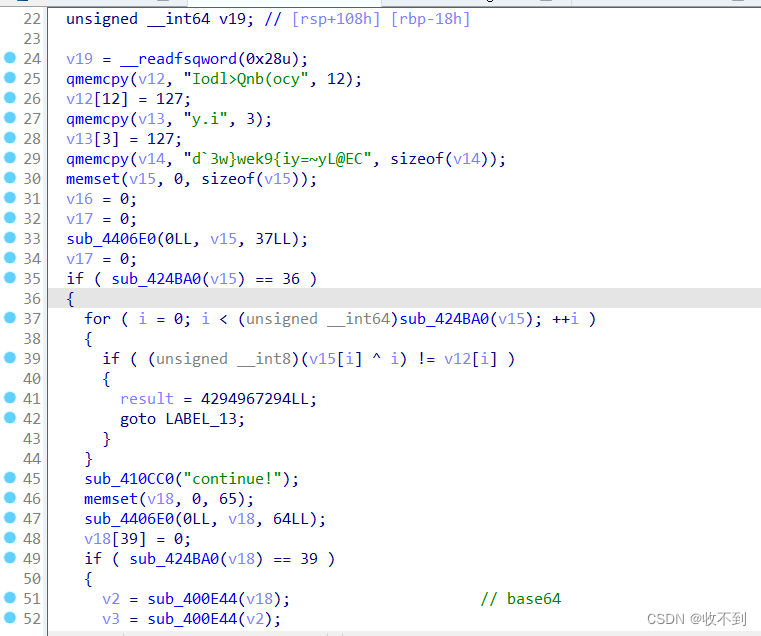
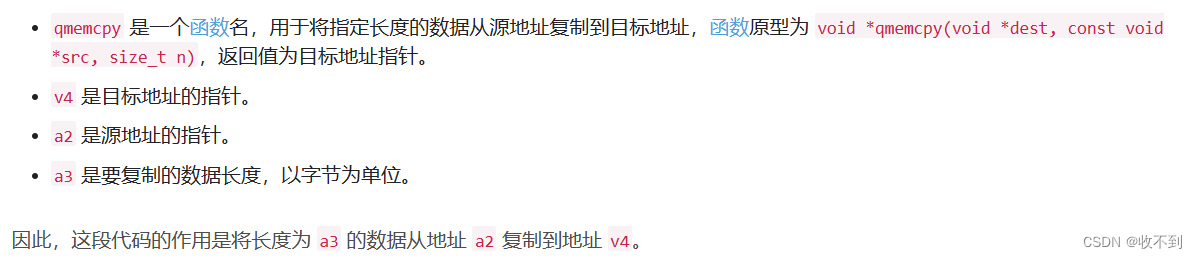
qmemcpy函数名
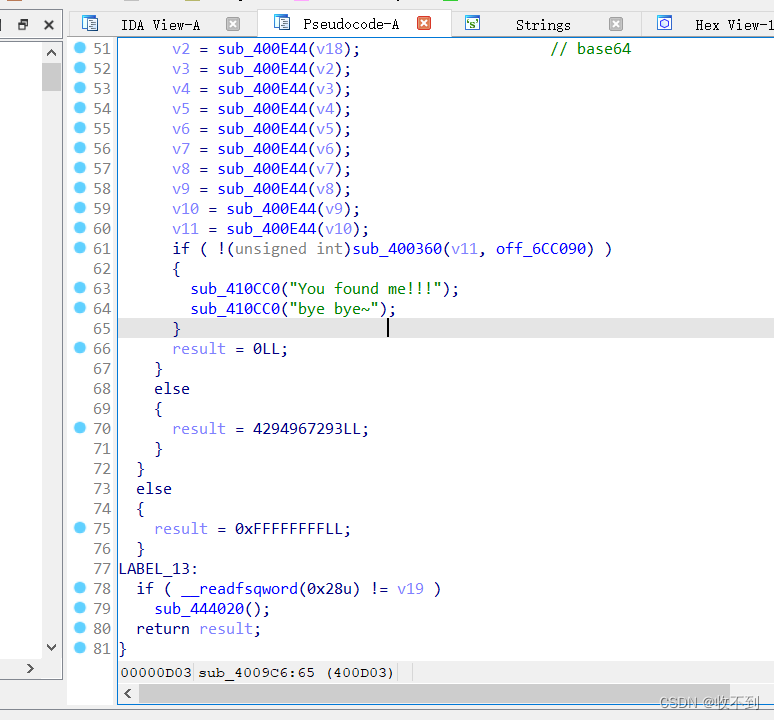
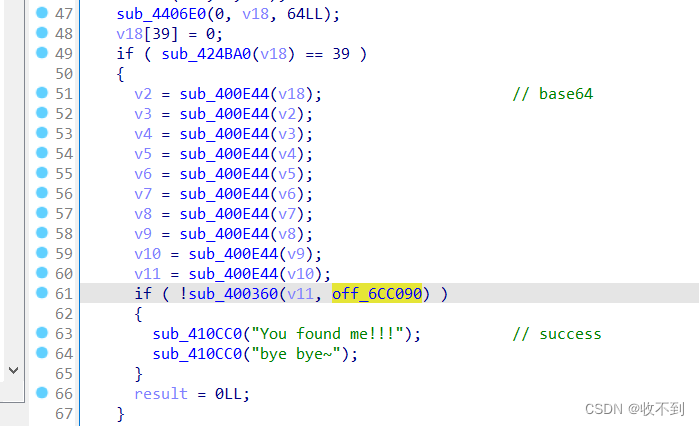
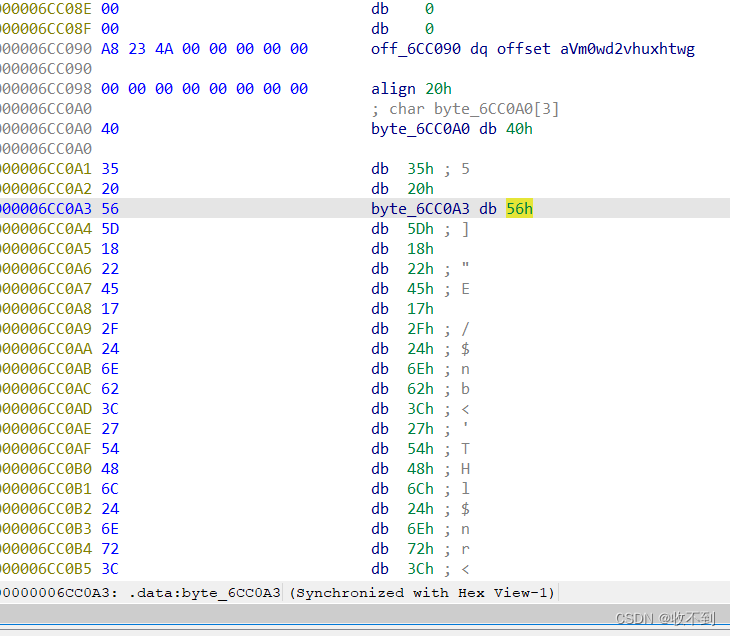
观察分析得到10次base64得到那个off6cc090进去发现·很长一串数,提取数据base64解密
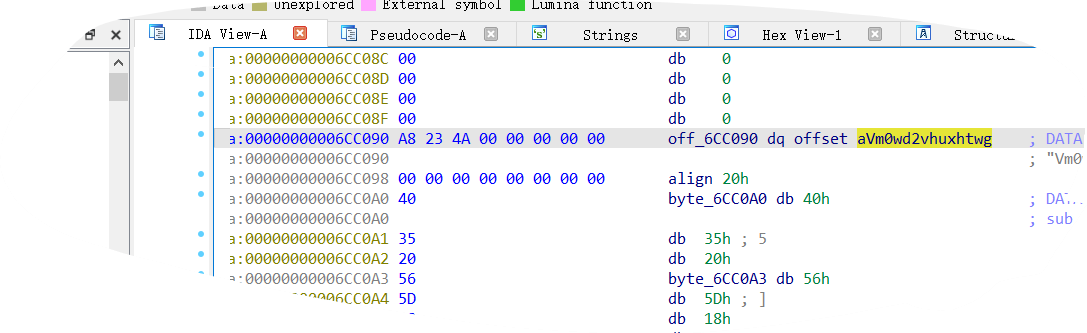
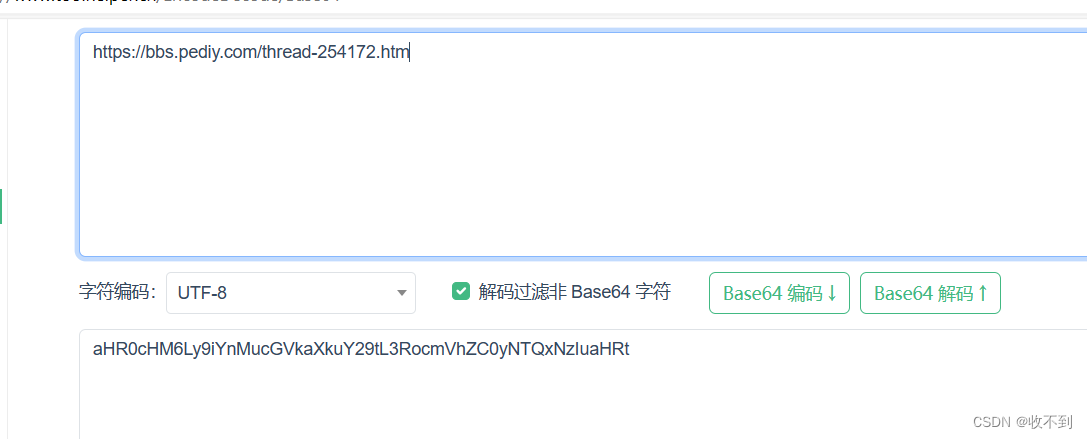
经多次base64解码(怀疑ing)得到一个网址emmm没啥作用
啊欺骗感情吗这不是
然后那个下面
有一些数据交叉引用
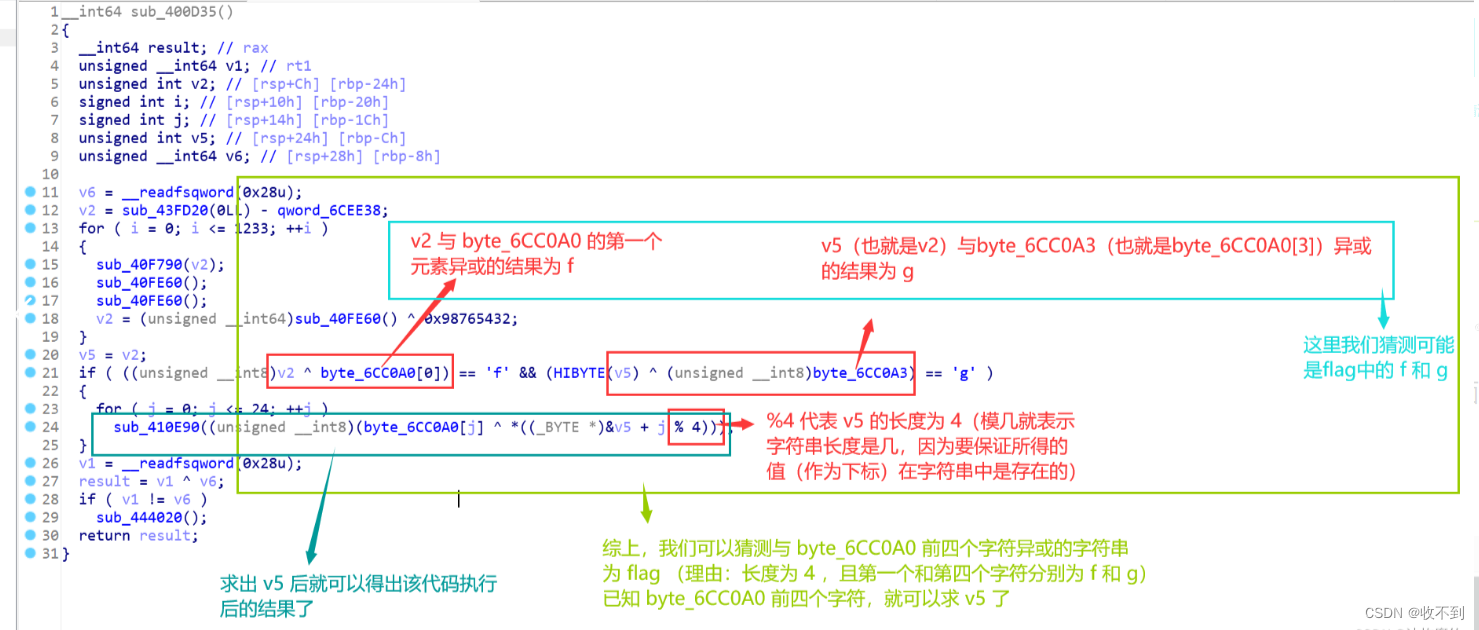
反编译,观察
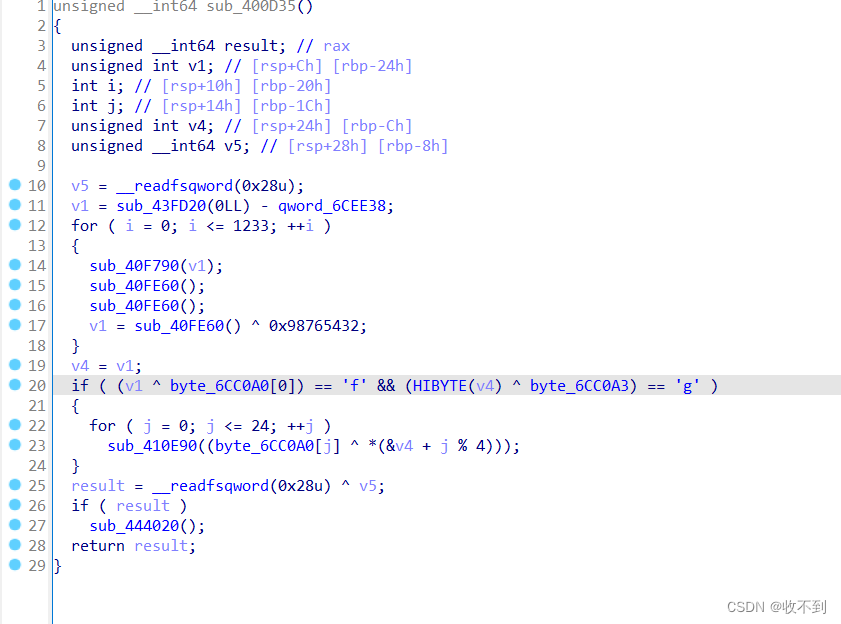
(⊙o⊙)…学习ing
分析
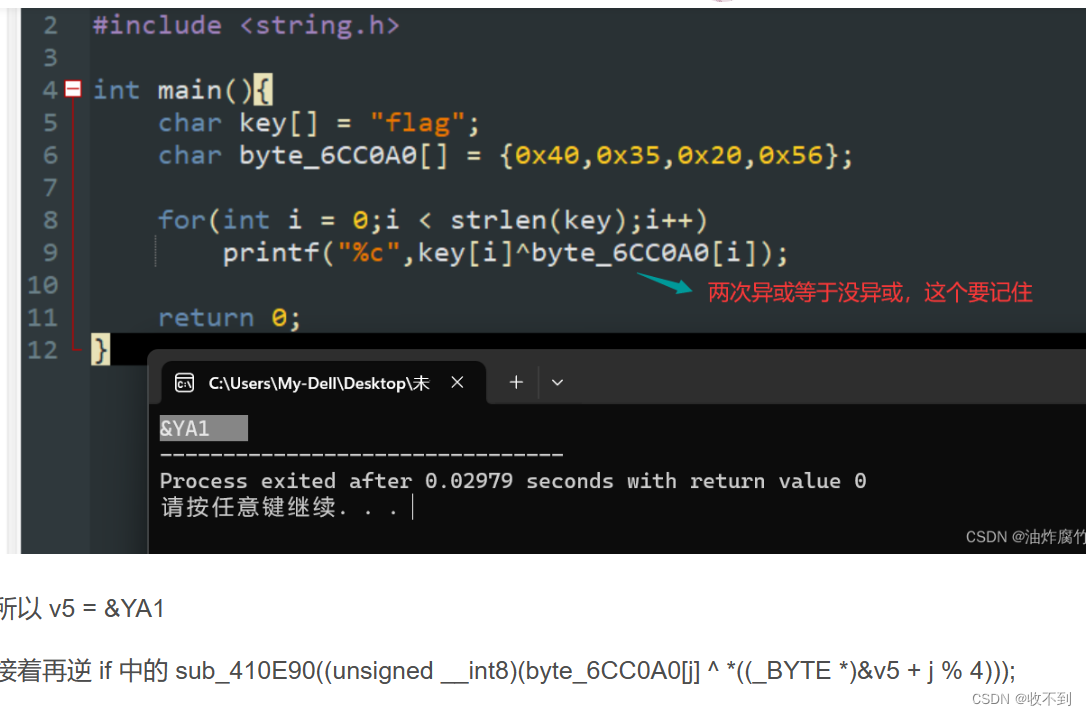
#include <stdio.h>
#include <string.h>
int main(){
char s[] = {0x40,0x35,0x20,0x56,0x5D,0x18,0x22,0x45,0x17,0x2F,0x24,0x6E,0x62,0x3C,0x27,0x54,0x48,0x6C,0x24,0x6E,0x72,0x3C,0x32,0x45,0x5B};
char cc[] = "&YA1";
for(int i = 0;i<strlen(s);i++){
printf("%c",s[i]^cc[i%4]);
}
}[MRCTF2020]Transform
open
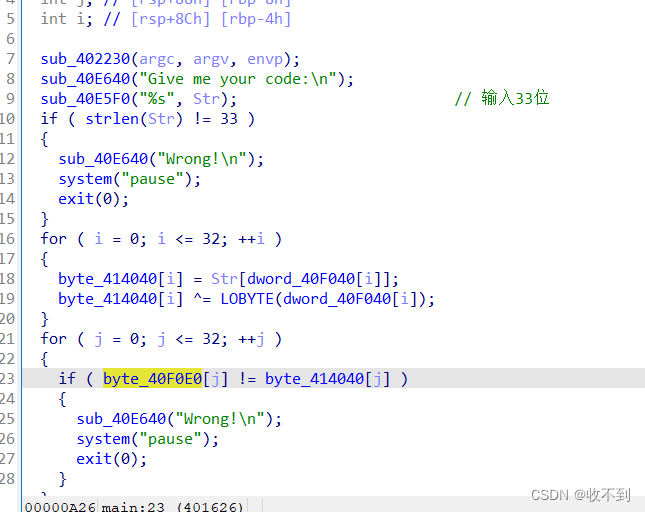
可以导出两个数组的数据
比较简单的逆向
写脚本逆回去
#include<stdio.h>
int main()
{
int i,j,k;
char c[33];
int a[40] =
{9,10,15,23,7,24,12,6,1,16,3,17,32,29,11,30,27,22,4,13,19,20,
21,2,25,5,31,8,18,26,28,14 };
int b[33] ={103,121,123,127,117,43,60,82,83,
121,87,94,93,66,123,45,42,102,66,126,76,
87,121,65,107,126,101,60,92,69,111,98,77};
for ( i = 0; i <= 32; ++i )
{
b[i] ^= a[i];//LOBYTE:取16位数的低8位
}
for(i=0;i<=32;i++)
{
k=a[i];
c[k]=(char)b[i];
}
puts(c);
return 0;
}
[WUSTCTF2020]level2
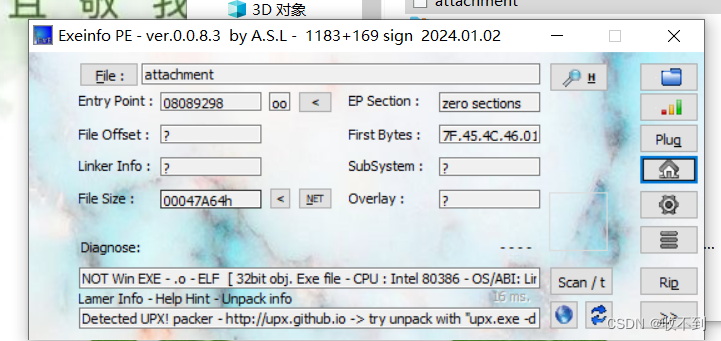
upx壳
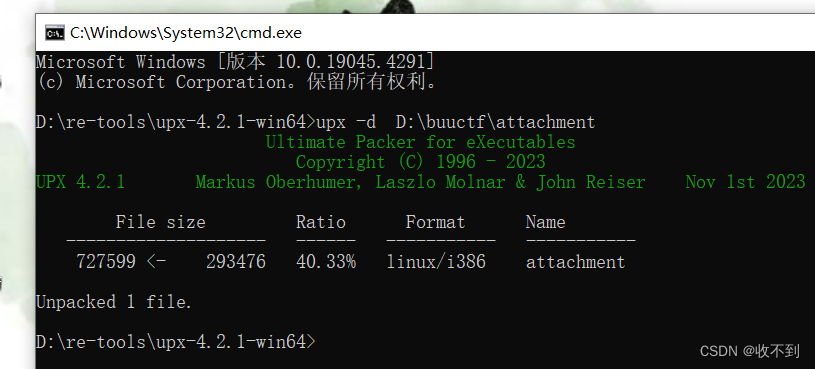
32位
打开
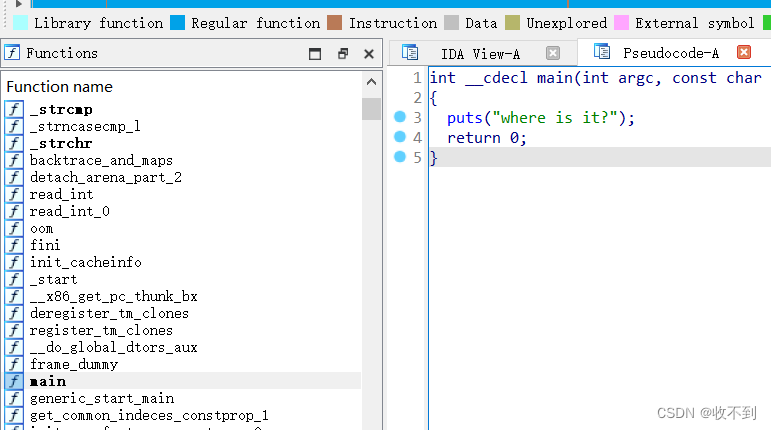
啥也不是
shift +12查找拖到底
[SUCTF2019]SignIn
有蚊子咬我emmm但无壳
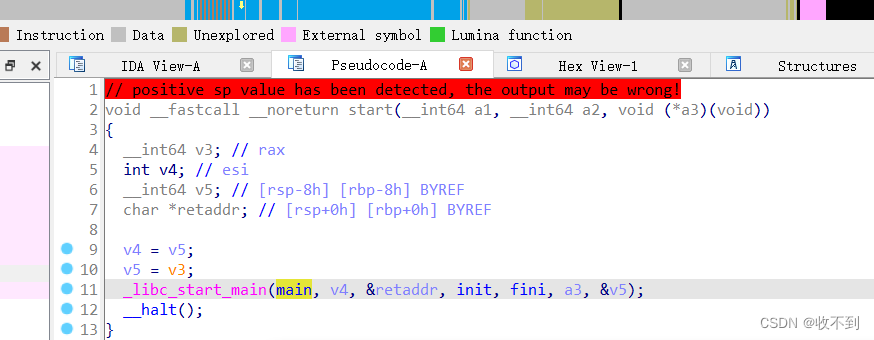
进入主函数

下面插播几个函数
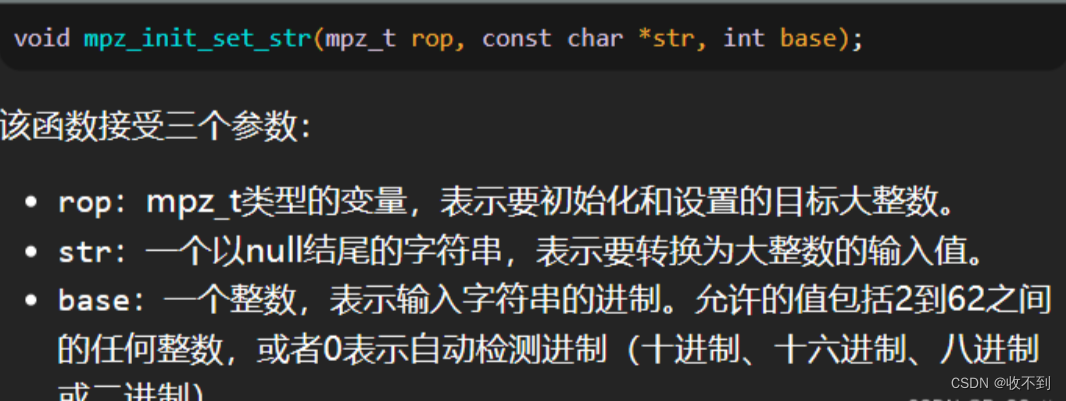
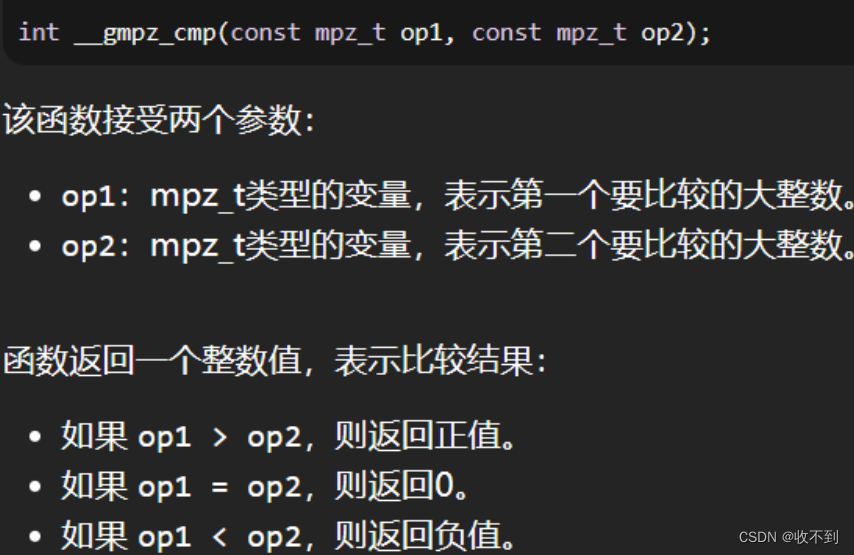
看那个gmpz就想到前天rsa下载gmpy的那个找了半天没找到
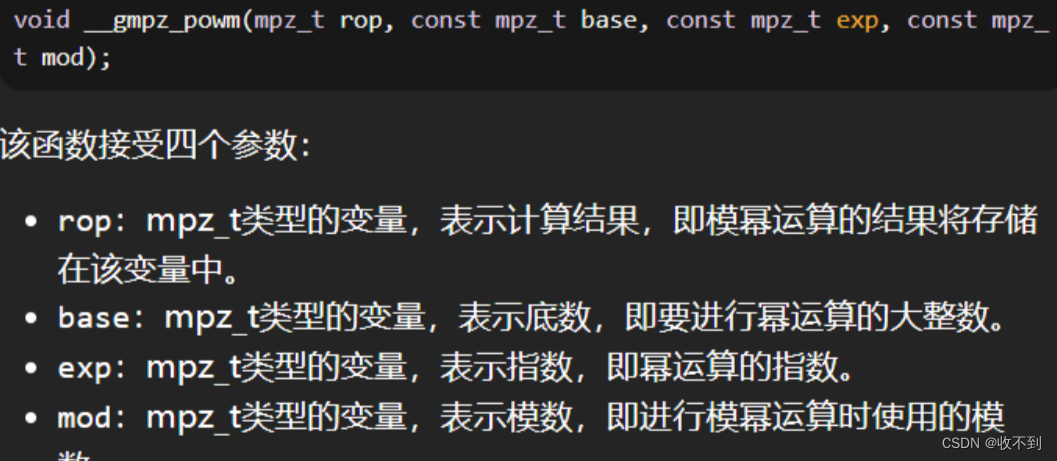
加上那个pow函数(第二个)底数指数模推测rsa
n=103461035900816914121390101299049044413950405173712170434161686539878160984549
p= 282164587459512124844245113950593348271
q=366669102002966856876605669837014229419
e=65537
c = 0xad939ff59f6e70bcbfad406f2494993757eee98b91bc244184a377520d06fc35
v6 = m = c的e次方mod N
下载gmpy
import gmpy2
p = 282164587459512124844245113950593348271
q = 366669102002966856876605669837014229419
c = 0xad939ff59f6e70bcbfad406f2494993757eee98b91bc244184a377520d06fc35
E = 65537
N = p * q
T = (p - 1) * (q - 1)
D = int(gmpy2.invert(E, T))
m = gmpy2.powmod(c, D, N)
hex_m = str(hex(m)[2:]) # 去掉'0x'
byte_value = bytes.fromhex(hex_m)
flag = byte_value.decode('utf-8')
print(flag) # suctf{Pwn_@_hundred_years}





















 1197
1197











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








