

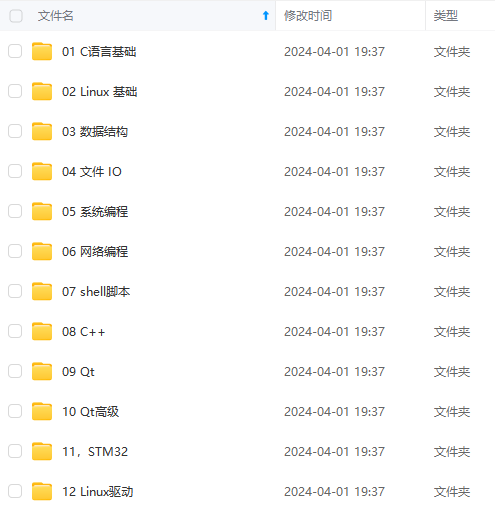
既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,涵盖了95%以上物联网嵌入式知识点,真正体系化!
由于文件比较多,这里只是将部分目录截图出来,全套包含大厂面经、学习笔记、源码讲义、实战项目、大纲路线、电子书籍、讲解视频,并且后续会持续更新
需要这些体系化资料的朋友,可以加我V获取:vip1024c (备注嵌入式)
- \State E _ n = E _ n + c _ i E\_n=E\_n+c\_i E_n=E_n+c_i;
- \EndWhile
- \label{code:recentEnd}
- \end{algorithmic}
- \end{algorithm}
example 3
代码:
[plain]
view plain
copy
- \begin{algorithm}[h]
- \caption{Conjugate Gradient Algorithm with Dynamic Step-Size Control}
- \label{alg::conjugateGradient}
- \begin{algorithmic}[1]
- \Require
- f ( x ) f(x) f(x): objective funtion;
- x _ 0 x\_0 x_0: initial solution;
- s s s: step size;
- \Ensure
- optimal KaTeX parse error: Undefined control sequence: \* at position 4: x^{\̲*̲}
- \State initial g _ 0 = 0 g\_0=0 g_0=0 and d _ 0 = 0 d\_0=0 d_0=0;
- \Repeat
- \State compute gradient directions g _ k = ▽ f ( x _ k ) g\_k=\bigtriangledown f(x\_k) g_k=▽ f(x_k);
- \State compute Polak-Ribiere parameter β _ k = g _ k T ( g _ k − g _ k − 1 ) ∥ g _ k − 1 ∥ 2 \beta\_k=\frac{g\_k^{T}(g\_k-g\_{k-1})}{\parallel g\_{k-1} \parallel^{2}} β_k=∥ g_k−1 ∥2g_kT(g_k−g_k−1);
- \State compute the conjugate directions d _ k = − g _ k + β _ k d _ k − 1 d\_k=-g\_k+\beta\_k d\_{k-1} d_k=−g_k+β_k d_k−1;
- \State compute the step size α _ k = s / ∥ d _ k ∥ _ 2 \alpha\_k=s/\parallel d\_k \parallel\_{2} α_k=s/∥ d_k ∥_2;
- \Until{( f ( x _ k ) > f ( x _ k − 1 ) f(x\_k)>f(x\_{k-1}) f(x_k)>f(x_k−1))}
- \end{algorithmic}
- \end{algorithm}
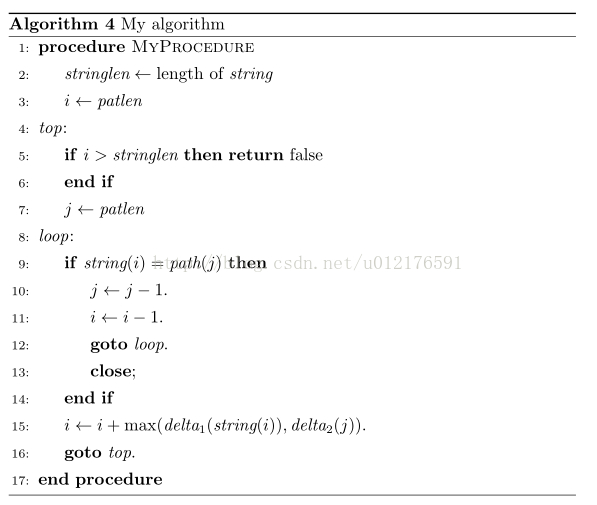
example 4
代码:
[plain]
view plain
copy
- \makeatletter
- \def\BState{\State\hskip-\ALG@thistlm}
- \makeatother
- \begin{algorithm}
- \caption{My algorithm}\label{euclid}
- \begin{algorithmic}[1]
- \Procedure{MyProcedure}{}
- \State stringlen ← length of string \textit{stringlen} \gets \text{length of }\textit{string} stringlen ← length of string
- \State i ← patlen i \gets \textit{patlen} i ← patlen
- \BState \emph{top}:
- \If { i > stringlen i > \textit{stringlen} i > stringlen} \Return false
- \EndIf
- \State j ← patlen j \gets \textit{patlen} j ← patlen
- \BState \emph{loop}:
- \If { string ( i ) = path ( j ) \textit{string}(i) = \textit{path}(j) string(i) = path(j)}
- \State j ← j − 1 j \gets j-1 j ← j−1.
- \State i ← i − 1 i \gets i-1 i ← i−1.
- \State \textbf{goto} \emph{loop}.
- \State \textbf{close};
- \EndIf
- \State i ← i + max ( delta _ 1 ( string ( i ) ) , delta _ 2 ( j ) ) i \gets i+\max(\textit{delta}\_1(\textit{string}(i)),\textit{delta}\_2(j)) i ← i+max(delta_1(string(i)),delta_2(j)).
- \State \textbf{goto} \emph{top}.
- \EndProcedure
- \end{algorithmic}
- \end{algorithm}
algorithm2e例子
algorithm2e包可能会与其它包产生冲突,一个常见的错误提示是“Too many }'…”。为了解决这个问题,要在引入algorithm2e包之前加入下面的命令:
[plain]
view plain
copy
- \makeatletter
- \newif\if@restonecol
- \makeatother
- \let\algorithm\relax
- \let\endalgorithm\relax
所以前期准备:
[plain]
view plain
copy
- \makeatletter
- \newif\if@restonecol
- \makeatother
- \let\algorithm\relax
- \let\endalgorithm\relax
- \usepackage[linesnumbered,ruled,vlined]{algorithm2e}%[ruled,vlined]{
- \usepackage{algpseudocode}
- \usepackage{amsmath}
- \renewcommand{\algorithmicrequire}{\textbf{Input:}} % Use Input in the format of Algorithm
- \renewcommand{\algorithmicensure}{\textbf{Output:}} % Use Output in the format of Algorithm
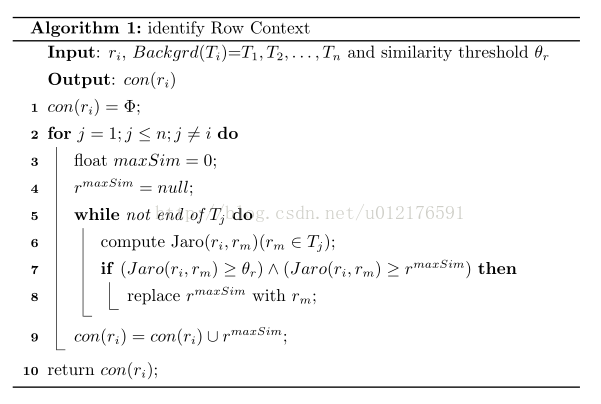
example 1
代码:
[plain]
view plain
copy
- \begin{algorithm}
- \caption{identify Row Context}
- \KwIn{ r _ i r\_i r_i, B a c k g r d ( T _ i ) Backgrd(T\_i) Backgrd(T_i)= T _ 1 , T _ 2 , … , T _ n {T\_1,T\_2,\ldots ,T\_n} T_1,T_2,… ,T_n and similarity threshold θ _ r \theta\_r θ_r}
- \KwOut{ c o n ( r _ i ) con(r\_i) con(r_i)}
- c o n ( r _ i ) = Φ con(r\_i)= \Phi con(r_i)= Φ;
- \For{ j = 1 ; j ≤ n ; j ≠ i j=1;j \le n;j \ne i j=1;j ≤ n;j = i}
- {
- float m a x S i m = 0 maxSim=0 maxSim=0;
- r m a x S i m = n u l l r^{maxSim}=null rmaxSim=null;
- \While{not end of T _ j T\_j T_j}
- {
- compute Jaro( r _ i , r _ m r\_i,r\_m r_i,r_m)( r _ m ∈ T _ j r\_m\in T\_j r_m∈ T_j);
- \If{ ( J a r o ( r _ i , r _ m ) ≥ θ _ r ) ∧ ( J a r o ( r _ i , r _ m ) ≥ r m a x S i m ) (Jaro(r\_i,r\_m) \ge \theta\_r)\wedge (Jaro(r\_i,r\_m)\ge r^{maxSim}) (Jaro(r_i,r_m) ≥ θ_r)∧ (Jaro(r_i,r_m)≥ rmaxSim)}
- {
- replace r m a x S i m r^{maxSim} rmaxSim with r _ m r\_m r_m;
- }
- }
- c o n ( r _ i ) = c o n ( r _ i ) ∪ r m a x S i m con(r\_i)=con(r\_i)\cup {r^{maxSim}} con(r_i)=con(r_i)∪ rmaxSim;
- }
- return c o n ( r _ i ) con(r\_i) con(r_i);
- \end{algorithm}
example 2
代码:
[plain]
view plain
copy
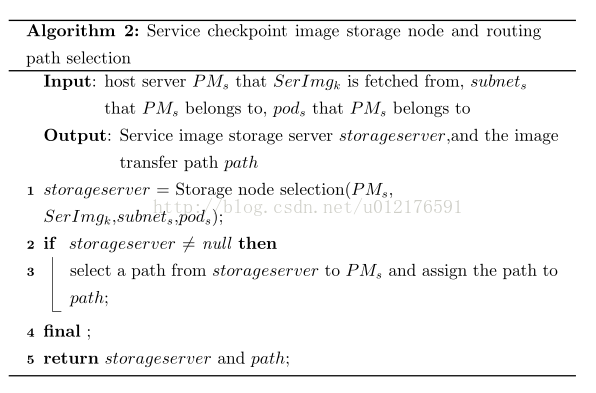
- \begin{algorithm}
- \caption{Service checkpoint image storage node and routing path selection}
- \LinesNumbered
- \KwIn{host server P M _ s PM\_s PM_s that S e r I m g _ k SerImg\_k SerImg_k is fetched from, s u b n e t _ s subnet\_s subnet_s that P M _ s PM\_s PM_s belongs to, p o d _ s pod\_s pod_s that P M _ s PM\_s PM_s belongs to}
- \KwOut{Service image storage server s t o r a g e s e r v e r storageserver storageserver,and the image transfer path p a t h path path}
- s t o r a g e s e r v e r storageserver storageserver = Storage node selection( P M _ s PM\_s PM_s, S e r I m g _ k SerImg\_k SerImg_k, s u b n e t _ s subnet\_s subnet_s, p o d _ s pod\_s pod_s);
- \If{ s t o r a g e s e r v e r storageserver storageserver ≠ \neq = null}
- {
- select a path from s t o r a g e s e r v e r storageserver storageserver to P M _ s PM\_s PM_s and assign the path to p a t h path path;
- }
- \textbf{final} ;
- \textbf{return} s t o r a g e s e r v e r storageserver storageserver and p a t h path path;
- \end{algorithm}
example 3
代码:
[plain]
view plain
copy
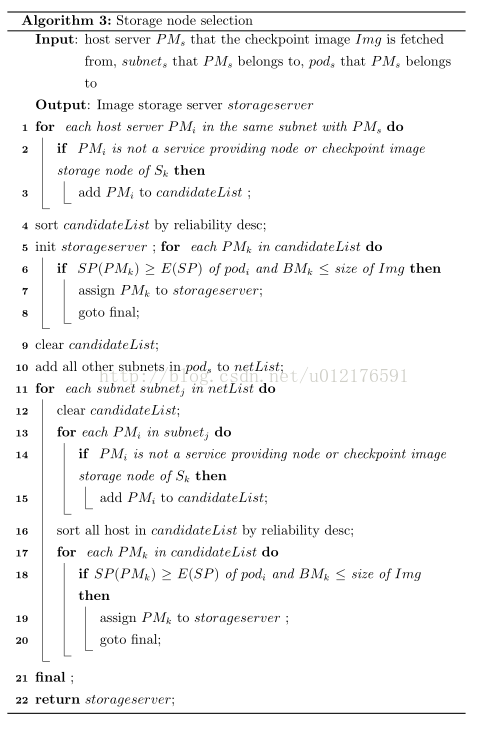
- \begin{algorithm}
- \caption{Storage node selection}
- \LinesNumbered
- \KwIn{host server P M _ s PM\_s PM_s that the checkpoint image I m g Img Img is fetched from, s u b n e t _ s subnet\_s subnet_s that P M _ s PM\_s PM_s belongs to, p o d _ s pod\_s pod_s that P M _ s PM\_s PM_s belongs to}
- \KwOut{Image storage server s t o r a g e s e r v e r storageserver storageserver}
- \For{ each host server P M _ i PM\_i PM_i in the same subnet with P M _ s PM\_s PM_s }
- {
- \If{ P M _ i PM\_i PM_i is not a service providing node or checkpoint image storage node of S _ k S\_k S_k }
- {
- add P M _ i PM\_i PM_i to c a n d i d a t e L i s t candidateList candidateList ;
- }
- }
- sort c a n d i d a t e L i s t candidateList candidateList by reliability desc;
- init s t o r a g e s e r v e r storageserver storageserver ;
- \For{ each P M _ k PM\_k PM_k in c a n d i d a t e L i s t candidateList candidateList}
- {
- \If{ S P ( P M _ k ) SP(PM\_k) SP(PM_k) ≥ \geq ≥ E ( S P ) E(SP) E(SP) of p o d _ i pod\_i pod_i and B M _ k BM\_k BM_k ≤ \le ≤ size of I m g Img Img }
- {
- assign P M _ k PM\_k PM_k to s t o r a g e s e r v e r storageserver storageserver;
- goto final;
- }
- }
- clear c a n d i d a t e L i s t candidateList candidateList;
- add all other subnets in p o d _ s pod\_s pod_s to n e t L i s t netList netList;
- \For{ each subnet s u b n e t _ j subnet\_j subnet_j in n e t L i s t netList netList}
- {
- clear c a n d i d a t e L i s t candidateList candidateList;
- \For {each P M _ i PM\_i PM_i in s u b n e t _ j subnet\_j subnet_j }
- {
- \If{ P M _ i PM\_i PM_i is not a service providing node or checkpoint image storage node of S _ k S\_k S_k }
- {
- add P M _ i PM\_i PM_i to c a n d i d a t e L i s t candidateList candidateList;
- }
- }
- sort all host in c a n d i d a t e L i s t candidateList candidateList by reliability desc;
- \For{ each P M _ k PM\_k PM_k in c a n d i d a t e L i s t candidateList candidateList}
- {
- \If{ S P ( P M _ k ) SP(PM\_k) SP(PM_k) ≥ \geq ≥ E ( S P ) E(SP) E(SP) of p o d _ i pod\_i pod_i and B M _ k BM\_k BM_k ≤ \le ≤ size of I m g Img Img}
- {
- assign P M _ k PM\_k PM_k to s t o r a g e s e r v e r storageserver storageserver ;
- goto final;
- }
- }
- }
- \textbf{final} ;
- \textbf{return} s t o r a g e s e r v e r storageserver storageserver;
- \end{algorithm}
example 4
代码:
[plain]
view plain
copy
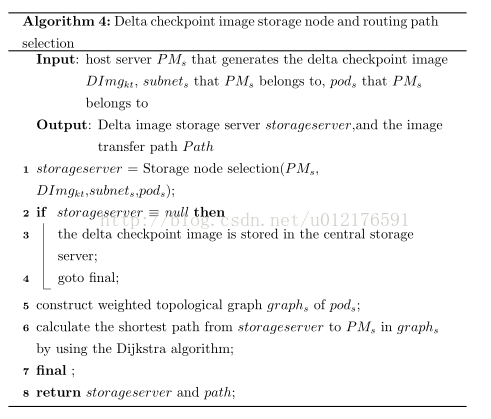
- \begin{algorithm}
- \caption{Delta checkpoint image storage node and routing path selection}
- \LinesNumbered
- \KwIn{host server P M _ s PM\_s PM_s that generates the delta checkpoint image D I m g _ k t DImg\_{kt} DImg_kt, s u b n e t _ s subnet\_s subnet_s that P M _ s PM\_s PM_s belongs to, p o d _ s pod\_s pod_s that P M _ s PM\_s PM_s belongs to}
- \KwOut{Delta image storage server s t o r a g e s e r v e r storageserver storageserver,and the image transfer path P a t h Path Path}
- s t o r a g e s e r v e r storageserver storageserver = Storage node selection( P M _ s PM\_s PM_s, D I m g _ k t DImg\_{kt} DImg_kt, s u b n e t _ s subnet\_s subnet_s, p o d _ s pod\_s pod_s);
- \If{ s t o r a g e s e r v e r storageserver storageserver ≡ \equiv ≡ null}
- {
- the delta checkpoint image is stored in the central storage server;
- goto final;
- }
- construct weighted topological graph g r a p h _ s graph\_s graph_s of p o d _ s pod\_s pod_s;
- calculate the shortest path from s t o r a g e s e r v e r storageserver storageserver to P M _ s PM\_s PM_s in g r a p h _ s graph\_s graph_s by using the Dijkstra algorithm;
- \textbf{final} ;
- \textbf{return} s t o r a g e s e r v e r storageserver storageserver and p a t h path path;
- \end{algorithm}
example 5
[plain]
view plain
copy
- \documentclass[8pt,twocolumn]{ctexart}
- \usepackage{amssymb}
- \usepackage{bm}
- \usepackage{textcomp} %命令\textacutedbl的包,二阶导符号
- % Page length commands go here in the preamble
- \setlength{\oddsidemargin}{-0.25in} % Left margin of 1 in + 0 in = 1 in
- \setlength{\textwidth}{9in} % 纸张宽度Right margin of 8.5 in - 1 in - 6.5 in = 1 in
- \setlength{\topmargin}{-.75in} % Top margin of 2 in -0.75 in = 1 in
- \setlength{\textheight}{9.2in} % Lower margin of 11 in - 9 in - 1 in = 1 in
- \setlength{\parindent}{0in}
- \makeatletter
- \newif\if@restonecol
- \makeatother
- \let\algorithm\relax
- \let\endalgorithm\relax
- \usepackage[linesnumbered,ruled,vlined]{algorithm2e}%[ruled,vlined]{
- \usepackage{algpseudocode}
- \renewcommand{\algorithmicrequire}{\textbf{Input:}}
- \renewcommand{\algorithmicensure}{\textbf{Output:}}
- \begin{document}
- \begin{algorithm}
- \caption{component matrices computing}
- \LinesNumbered
- \KwIn{ X ∈ R l _ 1 × l _ 2 × ⋯ × l _ N , ε , λ , δ , R \mathcal{X}\in\mathbb{R}^{l\_1\times l\_2\times\cdots\times l\_N},\varepsilon,\lambda,\delta,R X∈Rl_1× l_2×⋯× l_N,ε,λ,δ,R}
- \KwOut{ A ( j ) s A^{(j)}s A(j)s for j = 1 j=1 j=1 to N N N}
- \textbf{Initialize} all A ( j ) s A^{(j)}s A(j)s //which can be seen as the 0 t h 0^{th} 0th round iterations;
- { l l l\hspace*{-1pt}\textacutedbl} = L =L =L //if we need to judge whether ( 11 ) (11) (11) is true then { l l l\hspace*{-1pt}\textacutedbl} denotes L ∣ _ t − 1 L|\_{t-1} L∣_t−1;
- \For{ each A _ i _ j r j ( 1 ≤ j ≤ N , 1 ≤ i _ j ≤ I _ j , 1 ≤ r ≤ R ) A\_{i\_jr}^{{j}}(1\le j\le N,1\le i\_j\le I\_j,1\le r\le R) A_i_jrj(1≤ j≤ N,1≤ i_j≤ I_j,1≤ r≤ R) }
- {// 1 s t 1^{st} 1st round iterations;
- g _ i _ j r ( j ) ′ = g _ i _ j r ( j ) g\_{i\_jr}^{(j)'}=g\_{i\_jr}^{(j)} g_i_jr(j)′=g_i_jr(j);
- A _ i _ j r ( j ) ′ = A _ i _ j r ( j ) A\_{i\_jr}^{(j)'}=A\_{i\_jr}^{(j)} A_i_jr(j)′=A_i_jr(j)//if the rollback shown as ( 12 ) (12) (12) is needed, A _ i _ j r ( j ) ′ A\_{i\_jr}^{(j)'} A_i_jr(j)′ denotes A _ i _ j r ( j ) ∣ _ t − 1 A\_{i\_jr}^{(j)}|\_{t-1} A_i_jr(j)∣_t−1;
- A _ i _ j r ( j ) = A _ i _ j r ( j ) − s i g n ( g _ i _ j r ( j ) ) ⋅ δ _ i _ j r ( j ) A\_{i\_jr}^{(j)}=A\_{i\_jr}^{(j)}-\mathrm{{\bf sign}}\left(g\_{i\_jr}^{(j)}\right)\cdot\delta\_{i\_jr}^{(j)} A_i_jr(j)=A_i_jr(j)− sign(g_i_jr(j))⋅δ_i_jr(j);
- }
- \Repeat(//other rounds of iterations for computing component matrices){ L ≤ ε \bm{L\le \varepsilon} L≤ ε or maximum iterations exhausted}
- {
- l ′ = L l'=L l′=L //if we need to judge whether ( 11 ) (11) (11) is true then l ′ l' l′ denotes L ∣ _ t L|\_t L∣_t;
- \For{ each A _ i _ j r j ( 1 ≤ j ≤ N , 1 ≤ i _ j ≤ I _ j , 1 ≤ r ≤ R ) A\_{i\_jr}^{{j}}(1\le j\le N,1\le i\_j\le I\_j,1\le r\le R) A_i_jrj(1≤ j≤ N,1≤ i_j≤ I_j,1≤ r≤ R)}
- {
- \If{ g _ i _ j r ( j ) ⋅ g _ i _ j r ( j ) ′ > 0 g\_{i\_jr}^{(j)}\cdot g\_{i\_jr}^{(j)'}>0 g_i_jr(j)⋅ g_i_jr(j)′>0}
- {
- A _ i _ j r ( j ) ′ = A _ i _ j r ( j ) A\_{i\_jr}^{(j)'}=A\_{i\_jr}^{(j)} A_i_jr(j)′=A_i_jr(j) ;
- g _ i _ j r ( j ) ′ = g _ i _ j r ( j ) g\_{i\_jr}^{(j)'}=g\_{i\_jr}^{(j)} g_i_jr(j)′=g_i_jr(j) ;
- δ _ i _ j r ( j ) = min ( δ _ i _ j r ( j ) ⋅ η + , M a x S t e p S i z e ) \delta\_{i\_jr}^{(j)}=\bm{\min}\left(\delta\_{i\_jr}^{(j)}\cdot\eta^{+},Max\\_Step\\_Size\right) δ_i_jr(j)=min(δ_i_jr(j)⋅η+,MaxStepSize);
收集整理了一份《2024年最新物联网嵌入式全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升的朋友。

需要这些体系化资料的朋友,可以加我V获取:vip1024c (备注嵌入式)
一个人可以走的很快,但一群人才能走的更远!不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人
都欢迎加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!
- g _ i _ j r ( j ) ′ = g _ i _ j r ( j ) g\_{i\_jr}^{(j)'}=g\_{i\_jr}^{(j)} g_i_jr(j)′=g_i_jr(j) ;
- δ _ i _ j r ( j ) = min ( δ _ i _ j r ( j ) ⋅ η + , M a x S t e p S i z e ) \delta\_{i\_jr}^{(j)}=\bm{\min}\left(\delta\_{i\_jr}^{(j)}\cdot\eta^{+},Max\\_Step\\_Size\right) δ_i_jr(j)=min(δ_i_jr(j)⋅η+,MaxStepSize);
收集整理了一份《2024年最新物联网嵌入式全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升的朋友。
[外链图片转存中…(img-ccKBkcCQ-1715886474566)]
[外链图片转存中…(img-fGAWDL4L-1715886474566)]
需要这些体系化资料的朋友,可以加我V获取:vip1024c (备注嵌入式)
一个人可以走的很快,但一群人才能走的更远!不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人
都欢迎加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!


































 9574
9574











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








