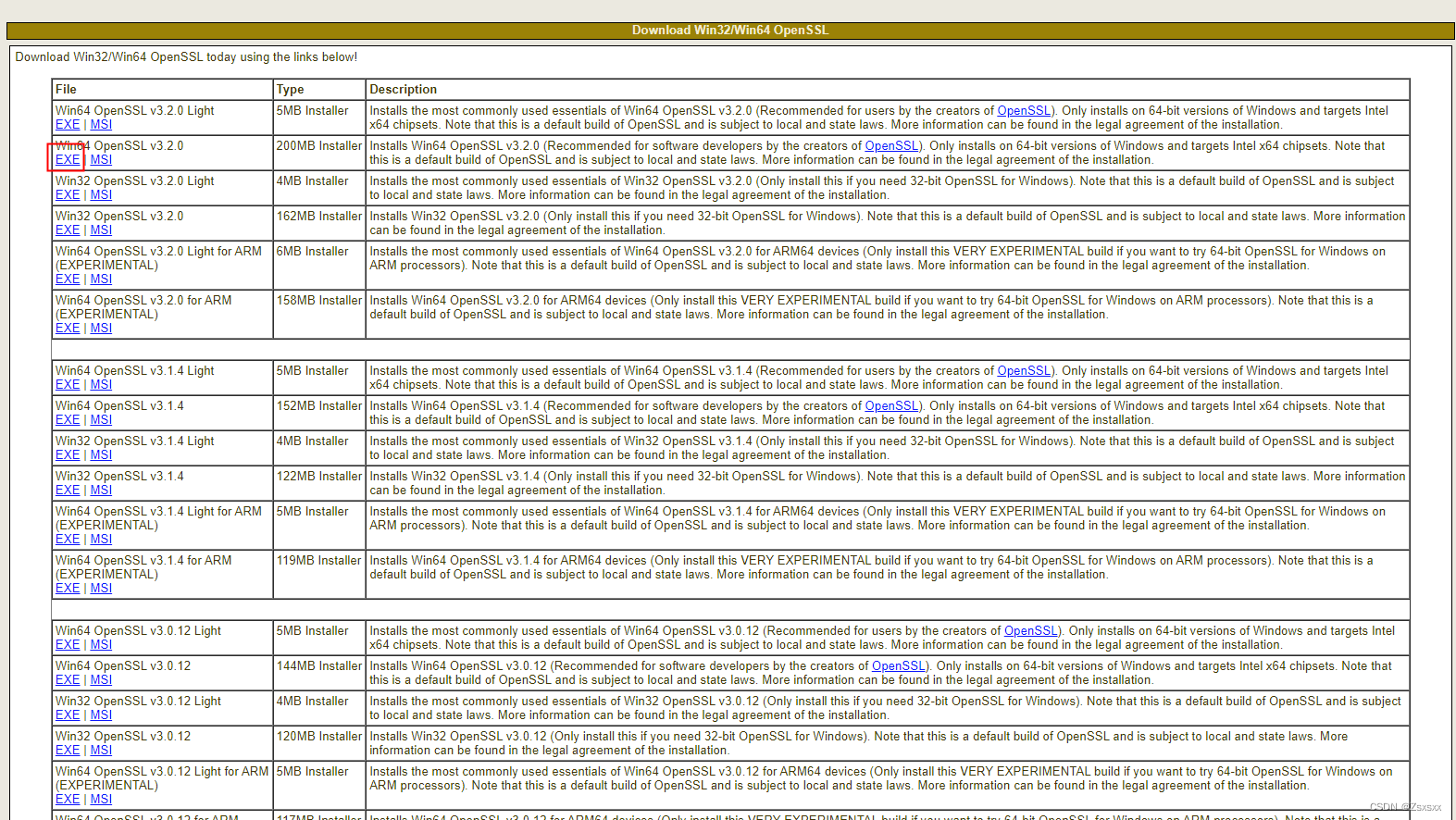
1、使用openssl进行自签证书的创建(以下为下载链接)
https://slproweb.com/products/Win32OpenSSL.html
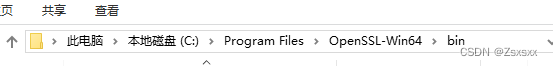
2、下载完成后进入如下界面,使用cmd进入
![]()
3、执行命令生成自签名ca证书、创建服务器密钥及证书、客户端密钥及证书:
3.1、创建自签名ca证书
openssl genrsa -out ca.key 2048
openssl req -x509 -new -nodes -key ca.key -sha256 -days 3650 -out ca.pem
3.2、创建服务器密钥及证书
openssl genrsa -out emqx.key







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章

















 1万+
1万+

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








