openssh和ssh
In working on getting Remote debugging with VS Code on Windows to a Raspberry Pi using .NET Core on ARM in my last post, I was looking for optimizations and realized that I was using plink/putty for my SSH tunnel. Putty is one of those tools that we (as developers) often take for granted, but ideally I could do stuff like this without installing yet another tool. Being able to use out of the box tools has a lot of value.
在上一篇文章中,通过使用ARM上的.NET Core在Windows上使用VS Code进行远程调试到Raspberry Pi上的过程中,我在寻找优化并意识到我在SSH隧道中使用了plink / putty。 腻子是我们(作为开发人员)经常认为理所当然的那些工具之一,但是理想情况下,我可以在不安装其他工具的情况下做类似的事情。 能够使用现成的工具具有很多价值。
A friend pointed out this part where I'm using plink.exe to ssh into the remote Linux machine to launch the VS Debugger:
一位朋友指出了这部分,其中我正在使用plink.exe SSH到远程Linux计算机中以启动VS调试器:
"pipeTransport": {
"pipeCwd": "${workspaceFolder}",
"pipeProgram": "${env:ChocolateyInstall}\\bin\\PLINK.EXE",
"pipeArgs": [
"-pw",
"raspberry",
"root@crowpi.lan"
],
"debuggerPath": "/home/pi/vsdbg/vsdbg"
}
I could use Linux/bash that's built into Windows 10 for years now. As you may know, Windows 10 can run many Linuxes out of the box. If I have a Linux distro configured, I can call Linux commands locally from CMD or PowerShell. For example, here you see I have three Linuxes and one is the default. I can call "wsl" and any command line is passed in.
多年来,我都可以使用Windows 10中内置Linux / bash。 您可能知道, Windows 10可以开箱即用地运行许多Linux 。 如果配置了Linux发行版,则可以从CMD或PowerShell本地调用Linux命令。 例如,在这里您看到我有三个Linux,其中一个是默认的。 我可以调用“ wsl”,并传入任何命令行。
C:\Users\scott> wslconfig /l
Windows Subsystem for Linux Distributions:
Ubuntu-18.04 (Default)
WLinux
Debian
C:\Users\scott> wsl ls ~/
forablog forablog.2 forablog.2.save forablog.pub myopenaps notreal notreal.pub test.txt
So theoretically I could "wsl ssh" and use that Linux's ssh, but again, requires setup and it's a little silly. Windows 10 now supports OpenSSL already!
因此,从理论上讲,我可以“使用wsl ssh”并使用该Linux的ssh,但是同样,它需要设置,而且有点愚蠢。 Windows 10现在已经支持OpenSSL!
Open an admin PowerShell to see if you have it installed. Here I have the client software installed but not the server.
打开管理PowerShell,以查看是否已安装。 在这里,我安装了客户端软件,但没有安装服务器。
PS> Get-WindowsCapability -Online | ? Name -like 'OpenSSH*'
Name : OpenSSH.Client~~~~0.0.1.0
State : Installed
Name : OpenSSH.Server~~~~0.0.1.0
State : NotPresent
You can then add the client (or server) with this one-time command:
然后,您可以使用此一次性命令添加客户端(或服务器):
Add-WindowsCapability -Online -Name OpenSSH.Client~~~~0.0.1.0
You'll get all the standard OpenSSH stuff that one would want.
您将获得想要的所有标准OpenSSH东西。
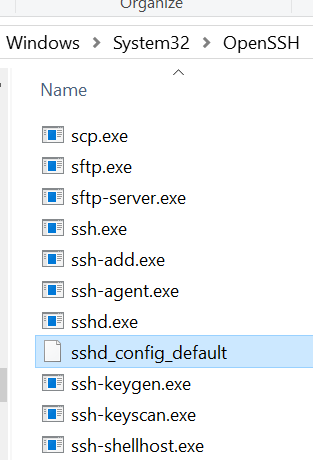
Let's say now that I want to be able to ssh (shoosh!) into a remote Linux machine using PGP keys rather than with a password. It's much more convenient and secure. I'll be ssh'ing with my Windows SSH into a remote Linux machine. You can see where ssh is installed:
现在让我们说,我希望能够使用PGP密钥而不是使用密码ssh(嘘!)到远程Linux计算机中。 它更加方便和安全。 我将使用Windows SSH将其SSH到远程Linux计算机中。 您可以看到ssh的安装位置:
C:\Users\scott>where ssh
C:\Windows\System32\OpenSSH\ssh.exe
Level set - What are we doing and what are we trying to accomplish?
设定水平-我们在做什么以及我们想要完成什么?
I want to be able to type "ssh pi@crowpi" from my Windows machine and automatically be logged in.
我希望能够从Windows计算机上键入“ ssh pi @ crowpi”并自动登录。
I will
我会
- Make a key on my Window machine. The FROM. I want to ssh FROM here TO the Linux machine. 在我的Window机器上做一个钥匙。 FROM。 我想从这里切换到Linux机器。
- Tell the Linux machine (by transferring it over) about the public piece of my key and add it to a specific user's allowed_keys. 告诉Linux机器(通过转让)有关我的密钥的公开部分,并将其添加到特定用户的allowed_keys中。
- PROFIT 利润
Here's what I did. Note you can do this is several ways. You can gen the key on the Linux side and scp it over, you can use a custom key and give it a filename, you can use a password as you like. Just get the essence right.
这就是我所做的。 请注意,您可以通过多种方式执行此操作。 您可以在Linux端生成密钥,然后将其加密,可以使用自定义密钥并为其提供文件名,也可以根据需要使用密码。 只是正确的本质。
Below, note that when the command line is C:\ I'm on Windows and when it's $ I'm on the remote Linux machine/Raspberry Pi.
在下面,请注意,当命令行为C:\时,我在Windows上,当它是$时,我在远程Linux机器/ Raspberry Pi上。
- gen the key on Windows with ssh-keygen 在Windows上使用ssh-keygen生成密钥
- I ssh'ed over to Linux and note I'm prompted for a password, as expected.我切换到Linux并注意,按预期,系统提示我输入密码。
- I "ls" to see that I have a .ssh/ folder. Cool. You can see authorized_keys is in there, you may or may no have this file or folder. Make the ~/.ssh folder if you don't. 我“ ls”看到我有一个.ssh /文件夹。 凉。 您可以看到authorized_keys在其中,您可能有也可能没有此文件或文件夹。 如果不创建〜/ .ssh文件夹。
- Exit out. I'm in Windows now. 退出。 我现在在Windows中。
- Look closely here. I'm "scott" on Windows so my public key is in c:\users\scott\.ssh\id_rsa.pub. Yours could be in a file you named earlier, be conscious. 在这里仔细看。 我在Windows上是“斯科特”,所以我的公钥在c:\ users \ scott \ .ssh \ id_rsa.pub中。 请注意,您的文件可能位于您之前命名的文件中。
- I'm type'ing (cat on Linux is type on Windows) that text file out and piping it into SSH where I login that remote machine with the user pi and I then cat (on the Linux side now) and append >> that text to the .ssh/authorized_keys folder. The ~ folder is implied but could be added if you like. 我正在键入文本文件(Linux上的猫在Windows上是键入),并将其通过管道传输到SSH中,然后我用pi用户登录该远程计算机,然后我用cat(现在在Linux端)并附加>>那文本到.ssh / authorized_keys文件夹。 隐含〜文件夹,但可以根据需要添加。
- Now when I ssh pi@crowpi I should NOT be prompted for a password. 现在,当我ssh pi @ crowpi时,不应该提示我输入密码。
Here's the whole thing.
这就是全部。
C:\Users\scott\Desktop> ssh-keygen
Generating public/private rsa key pair.
Enter file in which to save the key (C:\Users\scott/.ssh/id_rsa):
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in C:\Users\scott/.ssh/id_rsa.
Your public key has been saved in C:\Users\scott/.ssh/id_rsa.pub.
The key fingerprint is:
SHA256:x2vJHHXwosSSzLHQWziyx4II+scott@IRONHEART
The key's randomart image is:
+---[RSA 2048]----+
| . .... . |
|..+. .=+=. o |
| .. |
+----[SHA256]-----+
C:\Users\scott\Desktop> ssh pi@crowpi
pi@crowpi's password:
Linux crowpi 2018 armv7l
pi@crowpi:~ $ ls .ssh/
authorized_keys id_rsa id_rsa.pub known_hosts
pi@crowpi:~ $ exit
logout
Connection to crowpi closed.
C:\Users\scott\Desktop> type C:\Users\scott\.ssh\id_rsa.pub | ssh pi@crowpi 'cat >> .ssh/authorized_keys'
pi@crowpi's password:
C:\Users\scott\Desktop> ssh pi@crowpi
pi@crowpi: ~ $
Fab. At this point I could go BACK to my Windows' Visual Studio Code launch.json and simplify it to NOT use Plink/Putty and just use ssh and the ssh key management that's included with Windows.
晶圆厂此时,我可以返回到Windows的Visual Studio Code launch.json,并将其简化为不使用Plink / Putty,而仅使用Windows附带的ssh和ssh密钥管理。
"pipeTransport": {
"pipeCwd": "${workspaceFolder}",
"pipeProgram": "ssh",
"pipeArgs": [
"pi@crowpi.lan"
],
"debuggerPath": "/home/pi/vsdbg/vsdbg"
}
Cool!
凉!
NOTE: In my previous blog post some folks noted I am logging in as "root." That's an artifact of the way that .NET Core is accessing the GPIO pins. That won't be like that forever.
注意:在我以前的博客文章中,有些人指出我以“ root”身份登录。 这是.NET Core访问GPIO引脚的方式的产物。 那不会永远如此。
Thoughts? I hope this helps someone.
有什么想法吗? 我希望这可以帮助别人。
openssh和ssh





















 665
665











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








