mkdir /usr/local/etc/janus- 上传janus配置文件至/usr/local/etc/janus目录下(参考来源)
设置好的参考配置文件链接: https://pan.baidu.com/s/1rifqq1GVpCm5T_rEwsLJEg?pwd=4j9y 提取码: 4j9y
注意:https的SSL证书需提前生成;无域名的情况,证书生成参考教程
配置文件中需要修改的地方有:
janus.jcfg:
general: {
configs_folder = "/usr/local/etc/janus" # Configuration files folder
plugins_folder = "/usr/local/lib/janus/plugins" # Plugins folder
transports_folder = "/usr/local/lib/janus/transports" # Transports folder
events_folder = "/usr/local/lib/janus/events" # Event handlers folder
loggers_folder = "/usr/local/lib/janus/loggers" # External loggers folder
}
nat: {
stun_server = "47.104.30.235" #stun服务器外网地址
#stun_port = 3478
nice_debug = false
#full_trickle = true
#ice_nomination = "regular"
#ice_keepalive_conncheck = true
#ice_lite = true
#ice_tcp = true
# By default Janus tries to resolve mDNS (.local) candidates: even
# though this is now done asynchronously and shouldn't keep the API
# busy, even in case mDNS resolution takes a long time to timeout,
# you can choose to drop all .local candidates instead, which is
# helpful in case you know clients will never be in the same private
# network as the one the Janus instance is running from. Notice that
# this will cause ICE to fail if mDNS is the only way to connect!
#ignore_mdns = true
# In case you're deploying Janus on a server which is configured with
# a 1:1 NAT (e.g., Amazon EC2), you might want to also specify the public
# address of the machine using the setting below. This will result in
# all host candidates (which normally have a private IP address) to
# be rewritten with the public address provided in the settings. As
# such, use the option with caution and only if you know what you're doing.
# Make sure you keep ICE Lite disabled, though, as it's not strictly
# speaking a publicly reachable server, and a NAT is still involved.
# If you'd rather keep the private IP address in place, rather than
# replacing it (and so have both of them as advertised candidates),
# then set the 'keep_private_host' property to true.
# Multiple public IP addresses can be specified as a comma separated list
# if the Janus is deployed in a DMZ between two 1-1 NAT for internal and
# external users.
#nat_1_1_mapping = "1.2.3.4"
#keep_private_host = true
# You can configure a TURN server in two different ways: specifying a
# statically configured TURN server, and thus provide the address of the
# TURN server, the transport (udp/tcp/tls) to use, and a set of valid
# credentials to authenticate. Notice that you should NEVER configure
# a TURN server for Janus unless it's really what you want! If you want
# *users* to use TURN, then you need to configure that on the client
# side, and NOT in Janus. The following TURN configuration should ONLY
# be enabled when Janus itself is sitting behind a restrictive firewall
# (e.g., it's part of a service installed on a box in a private home).
turn_server = "47.104.30.235"
turn_port = 3478
turn_type = "udp"
turn_user = "admin"
turn_pwd = "123456"
# You can also make use of the TURN REST API to get info on one or more
# TURN services dynamically. This makes use of the proposed standard of
# such an API (https://tools.ietf.org/html/draft-uberti-behave-turn-rest-00)
# which is currently available in both rfc5766-turn-server and coturn.
# You enable this by specifying the address of your TURN REST API backend,
# the HTTP method to use (GET or POST) and, if required, the API key Janus
# must provide. The timeout can be configured in seconds, with a default of
# 10 seconds and a minimum of 1 second. Notice that the 'opaque_id' provided
# via Janus API will be used as the username for a specific PeerConnection
# by default; if that one is missing, the 'session_id' will be used as the
# username instead.
#turn_rest_api = "http://yourbackend.com/path/to/api"
#turn_rest_api_key = "anyapikeyyoumayhaveset"
#turn_rest_api_method = "GET"
#turn_rest_api_timeout = 10
# In case a TURN server is provided, you can allow applications to force
# Janus to use TURN (https://github.com/meetecho/janus-gateway/pull/2774).
# This is NOT allowed by default: only enable it if you know what you're doing.
#allow_force_relay = true
# You can also choose which interfaces should be explicitly used by the
# gateway for the purpose of ICE candidates gathering, thus excluding
# others that may be available. To do so, use the 'ice_enforce_list'
# setting and pass it a comma-separated list of interfaces or IP addresses
# to enforce. This is especially useful if the server hosting the gateway
# has several interfaces, and you only want a subset to be used. Any of
# the following examples are valid:
# ice_enforce_list = "eth0"
# ice_enforce_list = "eth0,eth1"
# ice_enforce_list = "eth0,192.168."
# ice_enforce_list = "eth0,192.168.0.1"
# By default, no interface is enforced, meaning Janus will try to use them all.
#ice_enforce_list = "eth0"
# In case you don't want to specify specific interfaces to use, but would
# rather tell Janus to use all the available interfaces except some that
# you don't want to involve, you can also choose which interfaces or IP
# addresses should be excluded and ignored by the gateway for the purpose
# of ICE candidates gathering. To do so, use the 'ice_ignore_list' setting
# and pass it a comma-separated list of interfaces or IP addresses to
# ignore. This is especially useful if the server hosting the gateway
# has several interfaces you already know will not be used or will simply
# always slow down ICE (e.g., virtual interfaces created by VMware).
# Partial strings are supported, which means that any of the following
# examples are valid:
# ice_ignore_list = "vmnet8,192.168.0.1,10.0.0.1"
# ice_ignore_list = "vmnet,192.168."
# Just beware that the ICE ignore list is not used if an enforce list
# has been configured. By default, Janus ignores all interfaces whose
# name starts with 'vmnet', to skip VMware interfaces:
ice_ignore_list = "vmnet"
# In case you want to allow Janus to start even if the configured STUN or TURN
# server is unreachable, you can set 'ignore_unreachable_ice_server' to true.
# WARNING: We do not recommend to ignore reachability problems, particularly
# if you run Janus in the cloud. Before enabling this flag, make sure your
# system is correctly configured and Janus starts after the network layer of
# your machine is ready. Note that Linux distributions offer such directives.
# You could use the following directive in systemd: 'After=network-online.target'
# https://www.freedesktop.org/software/systemd/man/systemd.unit.html#Before=
#ignore_unreachable_ice_server = true
}janus.transport.http.jcfg:
general: {
#events = true # Whether to notify event handlers about transport events (default=true)
json = "indented" # Whether the JSON messages should be indented (default),
# plain (no indentation) or compact (no indentation and no spaces)
base_path = "/janus" # Base path to bind to in the web server (plain HTTP only)
http = true # Whether to enable the plain HTTP interface
port = 8088 # Web server HTTP port
#interface = "eth0" # Whether we should bind this server to a specific interface only
#ip = "192.168.0.1" # Whether we should bind this server to a specific IP address (v4 or v6) only
https = true # Whether to enable HTTPS (default=false)
secure_port = 8089 # Web server HTTPS port, if enabled
#secure_interface = "eth0" # Whether we should bind this server to a specific interface only
#secure_ip = "192.168.0.1" # Whether we should bind this server to a specific IP address (v4 or v6) only
#acl = "127.,192.168.0." # Only allow requests coming from this comma separated list of addresses
#mhd_connection_limit = 1020 # Open connections limit in libmicrohttpd (default=1020)
#mhd_debug = false # Ask libmicrohttpd to write warning and error messages to stderr (default=false)
}
certificates: {
cert_pem = "/usr/cert/server.crt" #ssl证书地址
cert_key = "/usr/cert/server.key" #ssl证书地址
#cert_pwd = "secretpassphrase"
#ciphers = "PFS:-VERS-TLS1.0:-VERS-TLS1.1:-3DES-CBC:-ARCFOUR-128"
}janus.transport.websockets.jcfg:
general: {
#events = true # Whether to notify event handlers about transport events (default=true)
json = "indented" # Whether the JSON messages should be indented (default),
# plain (no indentation) or compact (no indentation and no spaces)
#pingpong_trigger = 30 # After how many seconds of idle, a PING should be sent
#pingpong_timeout = 10 # After how many seconds of not getting a PONG, a timeout should be detected
ws = true # Whether to enable the WebSockets API
ws_port = 8188 # WebSockets server port
#ws_interface = "eth0" # Whether we should bind this server to a specific interface only
#ws_ip = "192.168.0.1" # Whether we should bind this server to a specific IP address only
#ws_unix = "/run/ws.sock" # Use WebSocket server over UNIX socket instead of TCP
wss = true # Whether to enable secure WebSockets
wss_port = 8989 # WebSockets server secure port, if enabled
#wss_interface = "eth0" # Whether we should bind this server to a specific interface only
#wss_ip = "192.168.0.1" # Whether we should bind this server to a specific IP address only
#wss_unix = "/run/wss.sock" # Use WebSocket server over UNIX socket instead of TCP
#ws_logging = "err,warn" # libwebsockets debugging level as a comma separated list of things
# to debug, supported values: err, warn, notice, info, debug, parser,
# header, ext, client, latency, user, count (plus 'none' and 'all')
#ws_acl = "127.,192.168.0." # Only allow requests coming from this comma separated list of addresses
}
certificates: {
cert_pem = "/usr/cert/server.crt"
cert_key = "/usr/cert/server.key"
#cert_pwd = "secretpassphrase"
#ciphers = "ECDHE-RSA-AES256-GCM-SHA384:ECDHE-RSA-AES128-GCM-SHA256"
}
其他文件配置根据实际需要配置
- 上传docker-compose.yaml至/usr/local/下
配置好的参考文件链接: 链接:https://pan.baidu.com/s/1jTjI11oq2vIX9s9aNi3ypA?pwd=lv1m
提取码:lv1m
注意:外面配置的所有的文件路径需要做映射,包括SSL证书路径
version: '3.8'
services:
#
# janus-gateway
#
janus-gateway:
image: 'canyan/janus-gateway:latest'
command: ["/usr/local/bin/janus", "-F", "/usr/local/etc/janus"]
container_name: janus
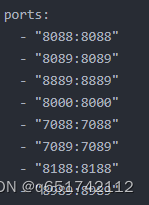
ports:
- "8088:8088"
- "8089:8089"
- "8889:8889"
- "8000:8000"
- "7088:7088"
- "7089:7089"
- "8188:8188"
- "8989:8989"
volumes:
- "./etc/janus/janus.jcfg:/usr/local/etc/janus/janus.jcfg"
- "./etc/janus/janus.eventhandler.sampleevh.jcfg:/usr/local/etc/janus/janus.eventhandler.sampleevh.jcfg"
- "./etc/janus/janus.transport.http.jcfg:/usr/local/etc/janus/janus.transport.http.jcfg"
- "./etc/janus/janus.eventhandler.gelfevh.jcfg:/usr/local/etc/janus/janus.eventhandler.gelfevh.jcfg"
- "./etc/janus/janus.eventhandler.mqttevh.jcfg:/usr/local/etc/janus/janus.eventhandler.mqttevh.jcfg"
- "./etc/janus/janus.eventhandler.nanomsgevh.jcfg:/usr/local/etc/janus/janus.eventhandler.nanomsgevh.jcfg"
- "./etc/janus/janus.eventhandler.rabbitmqevh.jcfg:/usr/local/etc/janus/janus.eventhandler.rabbitmqevh.jcfg"
- "./etc/janus/janus.eventhandler.wsevh.jcfg:/usr/local/etc/janus/janus.eventhandler.wsevh.jcfg"
- "./etc/janus/janus.logger.jsonlog.jcfg:/usr/local/etc/janus/janus.logger.jsonlog.jcfg"
- "./etc/janus/janus.plugin.audiobridge.jcfg:/usr/local/etc/janus/janus.plugin.audiobridge.jcfg"
- "./etc/janus/janus.plugin.duktape.jcfg:/usr/local/etc/janus/janus.plugin.duktape.jcfg"
- "./etc/janus/janus.plugin.echotest.jcfg:/usr/local/etc/janus/janus.plugin.echotest.jcfg"
- "./etc/janus/janus.plugin.lua.jcfg:/usr/local/etc/janus/janus.plugin.lua.jcfg"
- "./etc/janus/janus.plugin.nosip.jcfg:/usr/local/etc/janus/janus.plugin.nosip.jcfg"
- "./etc/janus/janus.plugin.recordplay.jcfg:/usr/local/etc/janus/janus.plugin.recordplay.jcfg"
- "./etc/janus/janus.plugin.sip.jcfg:/usr/local/etc/janus/janus.plugin.sip.jcfg"
- "./etc/janus/janus.plugin.streaming.jcfg:/usr/local/etc/janus/janus.plugin.streaming.jcfg"
- "./etc/janus/janus.plugin.textroom.jcfg:/usr/local/etc/janus/janus.plugin.textroom.jcfg"
- "./etc/janus/janus.plugin.videocall.jcfg:/usr/local/etc/janus/janus.plugin.videocall.jcfg"
- "./etc/janus/janus.plugin.videoroom.jcfg:/usr/local/etc/janus/janus.plugin.videoroom.jcfg"
- "./etc/janus/janus.plugin.voicemail.jcfg:/usr/local/etc/janus/janus.plugin.voicemail.jcfg"
- "./etc/janus/janus.transport.mqtt.jcfg:/usr/local/etc/janus/janus.transport.mqtt.jcfg"
- "./etc/janus/janus.transport.nanomsg.jcfg:/usr/local/etc/janus/janus.transport.nanomsg.jcfg"
- "./etc/janus/janus.transport.pfunix.jcfg:/usr/local/etc/janus/janus.transport.pfunix.jcfg"
- "./etc/janus/janus.transport.rabbitmq.jcfg:/usr/local/etc/janus/janus.transport.rabbitmq.jcfg"
- "./etc/janus/janus.transport.websockets.jcfg:/usr/local/etc/janus/janus.transport.websockets.jcfg"
- "/usr/cert/server.crt:/usr/cert/server.crt"
- "/usr/cert/server.key:/usr/cert/server.key"
restart: always
- 开放相关的外网端口,包括trun(udp-3478,30000-60000)的。
- 进入/usr/local/目录,启动镜像
cd /usr/local/
docker-compose up -d- 安装nginx (参考教程)
2、安装与常用命令
rpm -Uvh http://nginx.org/packages/centos/7/noarch/RPMS/nginx-release-centos-7-0.el7.ngx.noarch.rpm
yum install -y nginx
sudo systemctl start nginx
sudo systemctl enable nginx
systemctl restart nginx
3、open() “/usr/local/var/run/nginx.pid” failed (13: Permission denied)
sudo chmod -R 777 /usr/local/var/run
- 上传janus网站到服务器
链接:https://pan.baidu.com/s/1ZtsJS2ZUO1GcwtPNVhMiQw?pwd=hdui
提取码:hdui
参考原文:janus快速搭建docker版本centos7.9_weixin_37849325的博客-CSDN博客_docker安装janus
























 1793
1793

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








