一、题目:(来自于攻防世界)
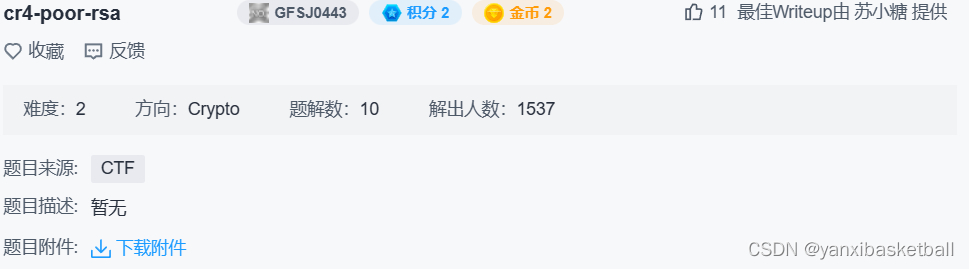
附件:
需要更改后缀名,才能打开,我这里先加上 .txt和加上 .tar试试
加上 .txt后打开得到如下:
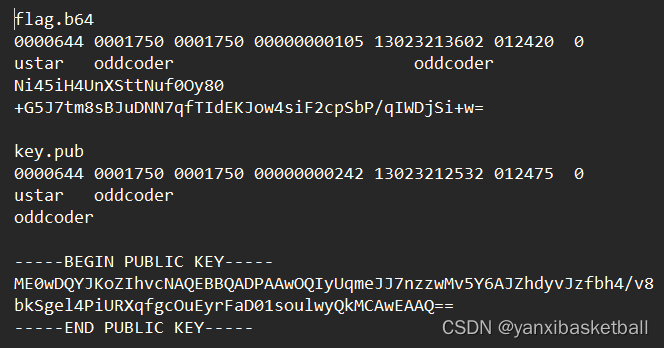
而加上 .tar,解压后得到如下:
二、解答过程
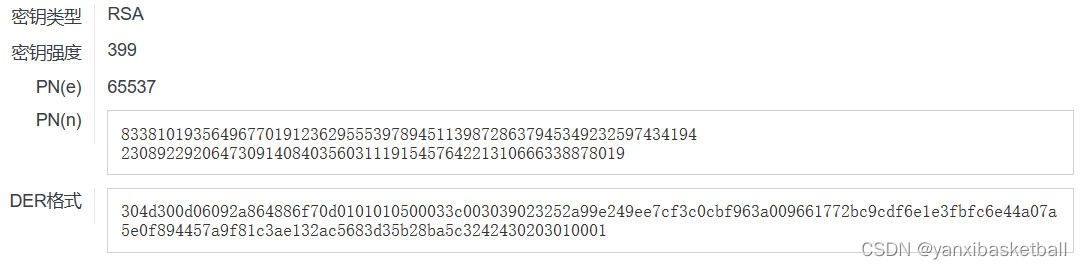
(1)从key.pub中获取公钥信息
方式一:利用在线网站,SSL在线工具-公钥解析 (hiencode.com)
方式二:利用Crypto.PublicKey的RSA模块从key.pub中获取公钥信息
from Crypto.Util.number import *
from Crypto.PublicKey import RSA
import gmpy2,binascii
from base64 import b64decode
import rsa
# 从公钥里面提取n 和 e
with open('D:\\桌面\\bf930316910b451c94c41ce8a9d851a8\\bf930316910b451c94c41ce8a9d851a8\\key.pub','r') as f:
key = RSA.import_key(f.read())
e = key.e
n = key.n
print('e = %d\nn = %d'%(e,n))(2)获取到n后,尝试分解n
使用yufa,分解出的质数太多
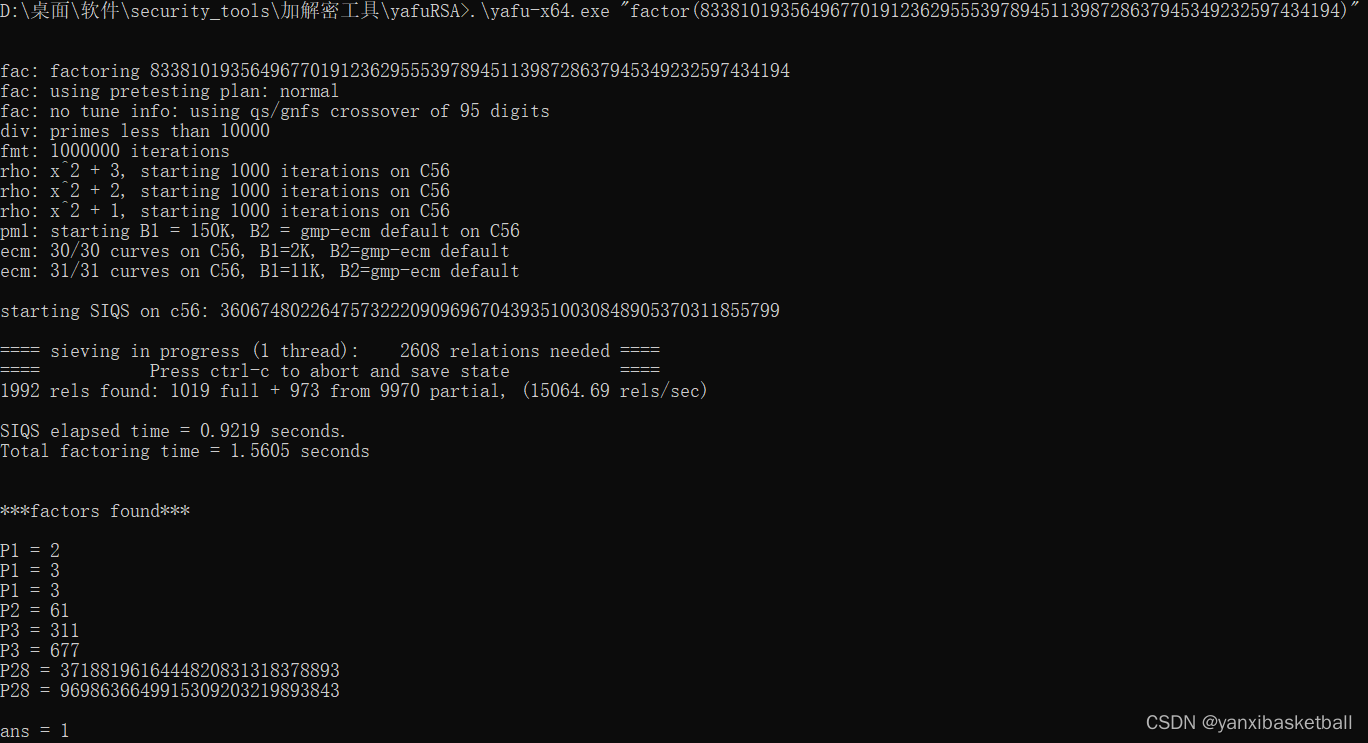
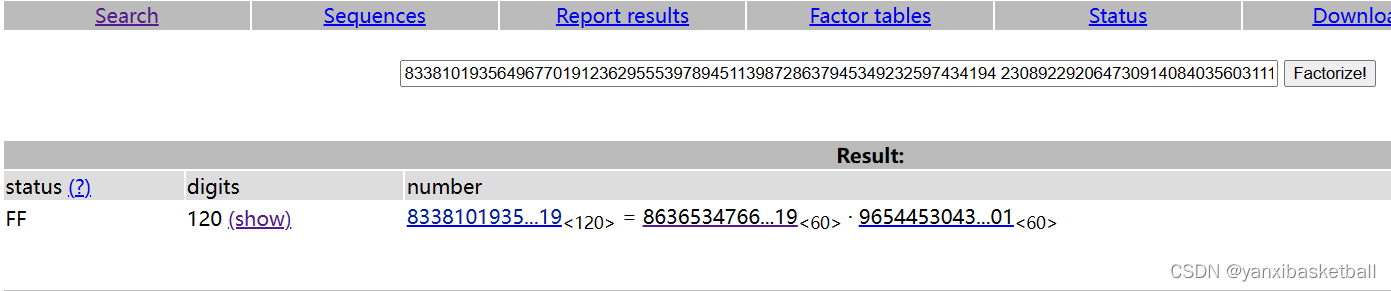
尝试其他分解网站 factordb.com,成功分解出了两个数
(3)得到p,q后变成计算私钥解密,其中flag还要进行base64解码
from Crypto.Util.number import *
from Crypto.PublicKey import RSA
import gmpy2,binascii
from base64 import b64decode
import rsa
# 从公钥里面提取n 和 e
with open('D:\\桌面\\bf930316910b451c94c41ce8a9d851a8\\bf930316910b451c94c41ce8a9d851a8\\key.pub','r') as f:
key = RSA.import_key(f.read())
e = key.e
n = key.n
p = 863653476616376575308866344984576466644942572246900013156919
q = 965445304326998194798282228842484732438457170595999523426901
d = int(inverse(e, (p-1)*(q-1)))
key = rsa.PrivateKey(n,e,d,p,q)
f = "Ni45iH4UnXSttNuf0Oy80+G5J7tm8sBJuDNN7qfTIdEKJow4siF2cpSbP/qIWDjSi+w="
c = b64decode(f)
flag = rsa.decrypt(c,key)
print(flag)






















 756
756

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








