版本:Grey Hack v0.7.3618 - Alpha
脚本源码
if params.len != 2 or params[0] == "-h" or params[0] == "--help" then exit("<b>Usage: "+program_path.split("/")[-1]+" [ip_address] [LAN_address]</b>")
metaxploit = include_lib("/lib/metaxploit.so")
if not metaxploit then
metaxploit = include_lib(current_path + "/metaxploit.so")
end if
if not metaxploit then exit("Error: Can't find metaxploit library in the /lib path or the current folder")
address = params[0]
net_session = metaxploit.net_use( address )
if not net_session then exit("Error: can't connect to net session")
libKernel = net_session.dump_lib
print("Founded " + libKernel.lib_name + " "+ libKernel.version)
if not libKernel then exit("Error: " + libName + " not found.")
lanIp = params[1]
resultMem = ""
resultKey = ""
kernel_router_exploits = metaxploit.scan(libKernel)
for kernel_router_exploit in kernel_router_exploits
print(kernel_router_exploit)
result_lists = metaxploit.scan_address(libKernel, kernel_router_exploit).split("Unsafe check: ")[1:]
for result_list in result_lists
target_str = result_list.split(".")[0]
target_key = target_str.split(" ")[-1]
result = libKernel.overflow(kernel_router_exploit, target_key[3:-4], lanIp)
print(target_key + ": " + typeof(result))
if typeof(result) == "shell" then
root_file = result.host_computer.File("/root")
if root_file.has_permission("w") then
result.start_terminal
else if root_file.has_permission("r") then
resultMem = kernel_router_exploit
resultKey = target_key[3:-4]
else
if resultMem == "" then resultMem = kernel_router_exploit
if resultKey == "" then resultKey = target_key[3:-4]
end if
end if
end for
end for
result = libKernel.overflow(resultMem, resultKey, lanIp)
if typeof(result) == "shell" then
result.start_terminal
end if
exit("Fail...")
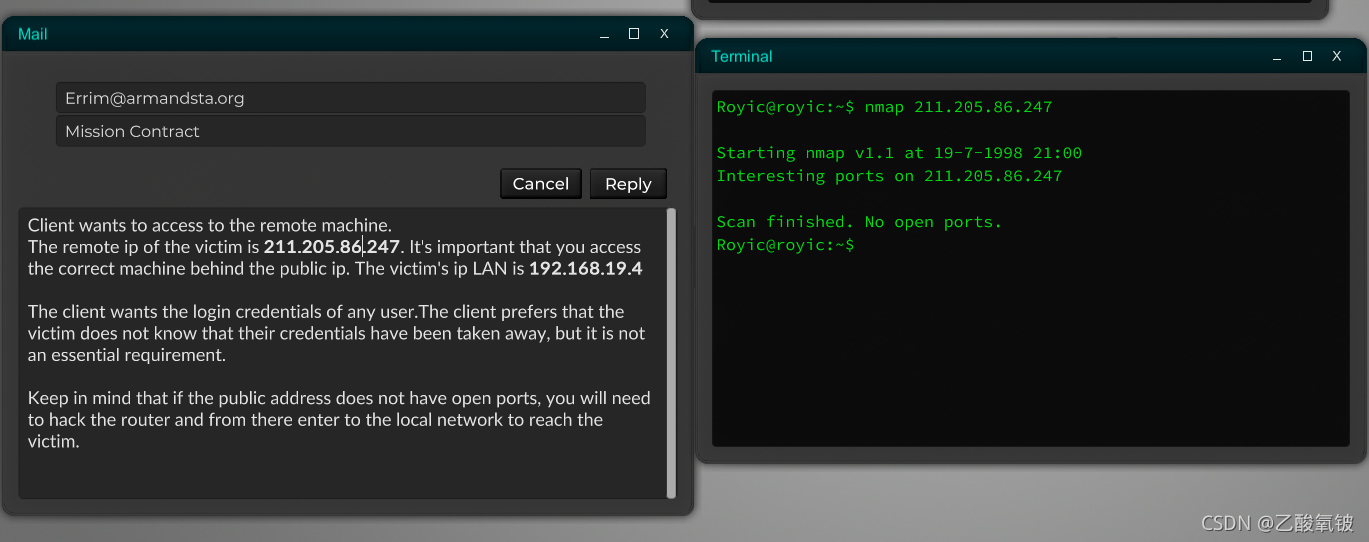
用法
【脚本名】 【公网IP】 【局域网IP】
效果及示例
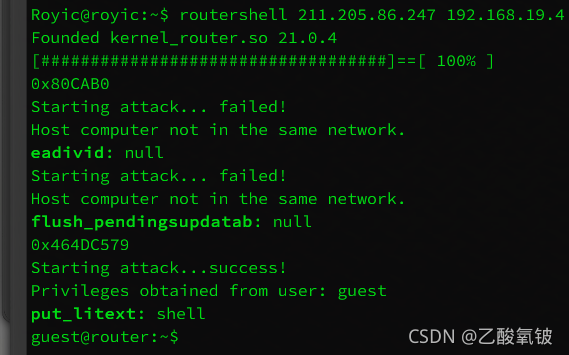
先检测目标端口库版本
再尝试遍历攻破漏洞以获取shell
视情况不同,可能得到游客或root权限
如图,本案例中目标IP尚未开放常见端口
得到了路由器游客权限的shell























 781
781











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










