0x00 open-source
#include <stdio.h>
#include <string.h>
int main(int argc, char *argv[]) {
if (argc != 4) {
printf("what?\n");
exit(1);
}
unsigned int first = atoi(argv[1]);
if (first != 0xcafe) {
printf("you are wrong, sorry.\n");
exit(2);
}
unsigned int second = atoi(argv[2]);
if (second % 5 == 3 || second % 17 != 8) {
printf("ha, you won't get it!\n");
exit(3);
}
if (strcmp("h4cky0u", argv[3])) {
printf("so close, dude!\n");
exit(4);
}
printf("Brr wrrr grr\n");
unsigned int hash = first * 31337 + (second % 17) * 11 + strlen(argv[3]) - 1615810207;
printf("Get your key: ");
printf("%x\n", hash);
return 0;
}
第一题附件为.c文件,直接放进ide中查看,代码最后输出的hash即为本题flag,而hash的计算用到了三个参数,自己写入参数后运行得到flag
#include <stdio.h>
#include <string.h>
int main()
{
int a=0xcafe;
int b=25;
int c=7;
unsigned int hash = a * 31337 + (b % 17) * 11 + c - 1615810207;
printf("Get your key: ");
printf("%x\n", hash);
return 0;
}
Get your key: c0ffee
0x01 simple-unpack
将题目附件直接拖入ida中分析,发现函数非常少,判断可能加了壳

把附件拿到exeinfope里查壳发现是upx

用工具进行脱壳

直接在字符串窗口中找到flag

0x02 logmein
直接拖入ida中查看反汇编代码

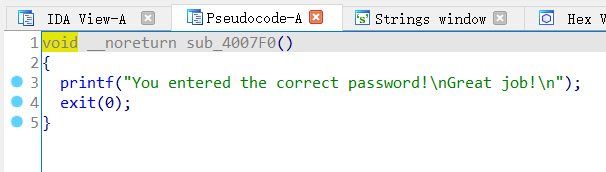
根据提示我们需要输入一个字符串存储在s中,如果s的长度大于v8则会调用sub_4007C0()函数,双击可以查看该函数
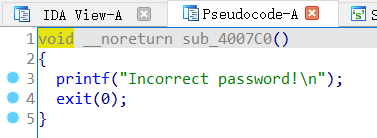
for循环中对s的每一个字符进行判断,如果和flag一致就会跳出循环,最后调用sub_4007F0()函数
可以利用反汇编代码中的变量值计算出flag
v7 = 'harambe'
v6 = 7
v8 = ":\"AL_RT^L*.?+6/46"
for i in range(len(v8)):
print(chr(ord(v7[i%v6])^ord(v8[i])),end='')
RC3-2016-XORISGUD
0x03 insanity
直接拖入ida中打开,在字符串中找到flag

0x04 python-trade
附件为一个pyc文件,找到在线pyc反编译得到源码
#!/usr/bin/env python
# visit https://tool.lu/pyc/ for more information
import base64
def encode(message):
s = ''
for i in message:
x = ord(i) ^ 32
x = x + 16
s += chr(x)
return base64.b64encode(s)
correct = 'XlNkVmtUI1MgXWBZXCFeKY+AaXNt'
flag = ''
print 'Input flag:'
flag = raw_input()
if encode(flag) == correct:
print 'correct'
else:
print 'wrong'
解题脚本如下
import base64
correct = 'XlNkVmtUI1MgXWBZXCFeKY+AaXNt'
p = base64.b64decode(correct)
print(p)
flag=''
for c in p:
x = ord(chr(c))-16
x = x^32
flag+=chr(x)
print(flag)
'''
b'^SdVkT#S ]`Y\\!^)\x8f\x80ism'
nctf{d3c0mpil1n9_PyC}
'''
0x05 re1
放入ida中查看源代码

程序将v5和用户输入的v7进行了比较,我们查看v5
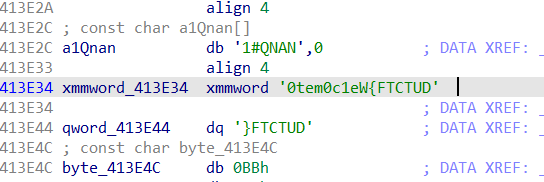
将xmmword_413E34解码后可以得到flag,由于存储字符串是采用小端存储,倒过来就是正确flag
DUTCTF{We1c0met0DUTCTF}
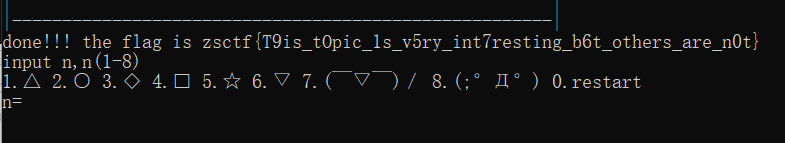
0x06 game

一个点灯游戏,规则很容易看懂,按顺序输入12345678即可通过
0x07 Hello, CTF
将exe附件放入ida中

将可疑的串进行16进制解析





















 652
652











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








