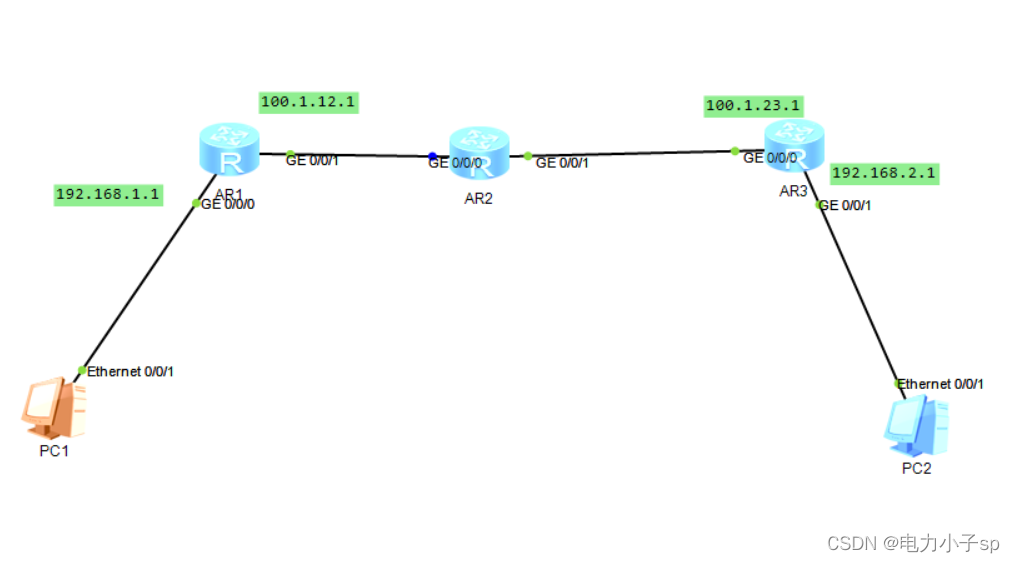
配置结果:
PC1与PC2之间流量加密
配置步骤:
1.略
各个接口配置Ip地址
2.R1配置
1.配置名为bx的提议,使用加密算法aes-cbc-128
[Huawei]sys R1
[R1]ike proposal 1
[R1-ike-proposal-1]encryption-algorithm aes-cbc-1282.认证算法sha1(sm开头为国密系列)
[R1-ike-proposal-1]authentication-algorithm sha13.dh group2----非对称加密
[R1-ike-proposal-1]dh group2 4.认证方式---域共享----pre-share
[R1-ike-proposal-1]authentication-method pre-share
[R1-ike-proposal-1]q时间为默认,不配置,大部分都有默认值。
5.域共享名为bx,v1,密钥为123,模式为主模式
[R1]ike peer
[R1]ike peer bx v1
[R1-ike-peer-bx]pre-shared-key cipher key123
[R1-ike-peer-bx]exchange-mode main v1可以选主模式或野蛮模式
6.对方地址100.1.23.1(R3)
[R1-ike-peer-bx]remote-address 100.1.23.17.配置ipsec ty1,tunnel隧道,aes-128加密算法,sha1认证
[R1]ipsec proposal ty1
[R1-ipsec-proposal-ty1]encapsulation-mode tunnel
[R1-ipsec-proposal-ty1]esp encryption-algorithm aes-128
[R1-ipsec-proposal-ty1]esp authentication-algorithm sha1
[R1-ipsec-proposal-ty1]q8.创建acl3000(高级acl),源IP-目标IP
[R1]acl 3000
[R1-acl-adv-3000]rule permit ip source 192.168.1.0 0.0.0.255 destination 192.168
.2.0 0.0.0.2559.写名为cl的IPSEC的策略,动态协商,将ty1,acl3000,ike-peer bx写入
[R1]ipsec policy cl 1 isakmp
[R1-ipsec-policy-isakmp-cl-1]proposal ty1
[R1-ipsec-policy-isakmp-cl-1]ike-peer bx
[R1-ipsec-policy-isakmp-cl-1]security acl 300010.完美向前法--下次换的密钥与上次的密钥完全没有关系,安全度高
[R1-ipsec-policy-isakmp-cl-1]pfs dh-group2
[R1-ipsec-policy-isakmp-cl-1]dis th
11.将cl调用在接口下
[R1]int g0/0/1
[R1-GigabitEthernet0/0/1]ipsec policy cl
[R1-GigabitEthernet0/0/1]q3.R3同上
最后使用PC1pingPC2时,在中间公网路由抓包可以看到,流量已被加密。


























 2083
2083











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










