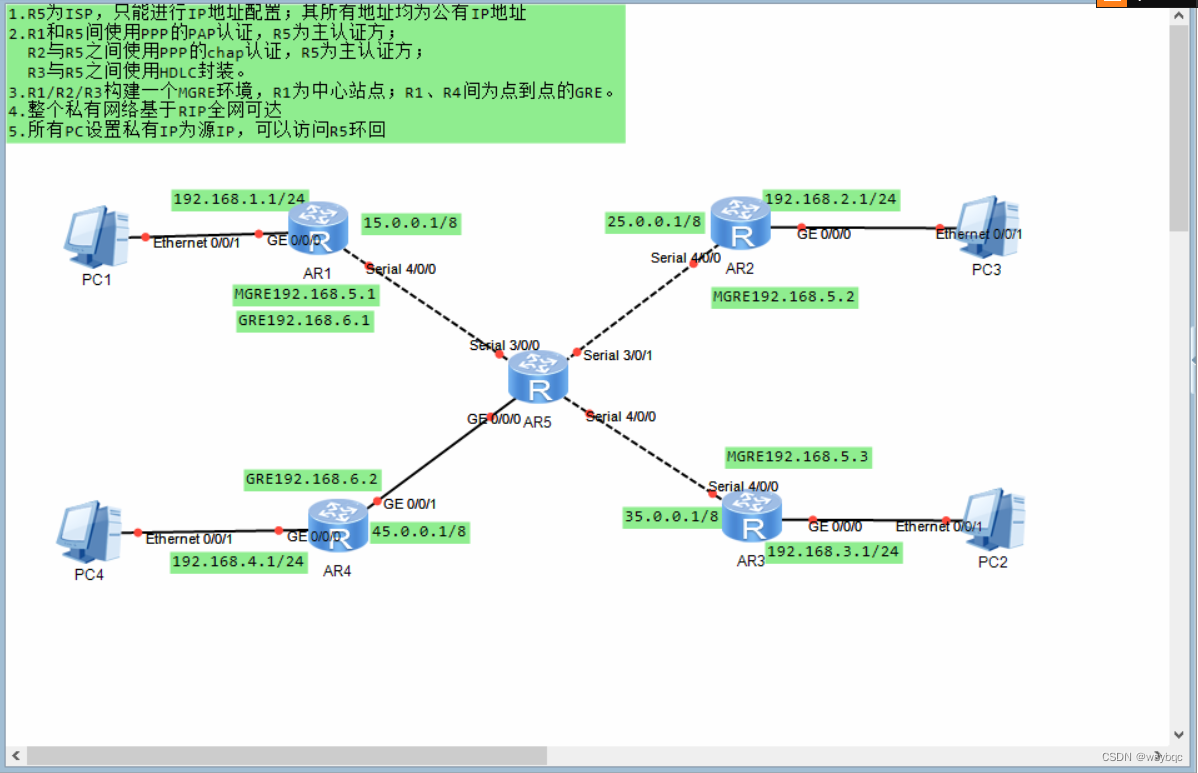
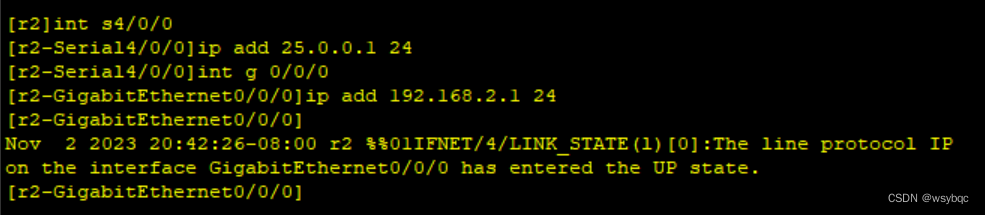
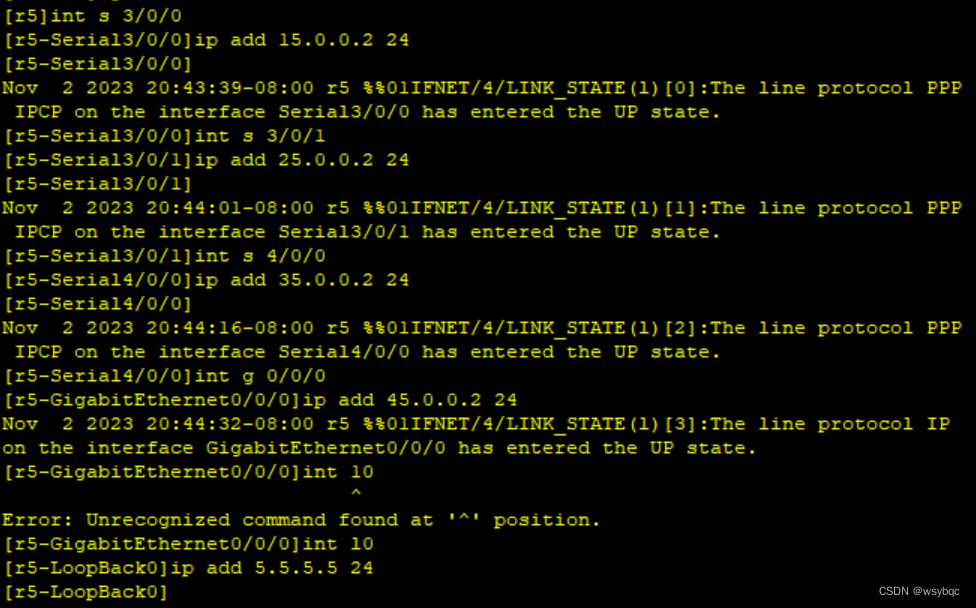
首先配置路由各个接口并配置r5环回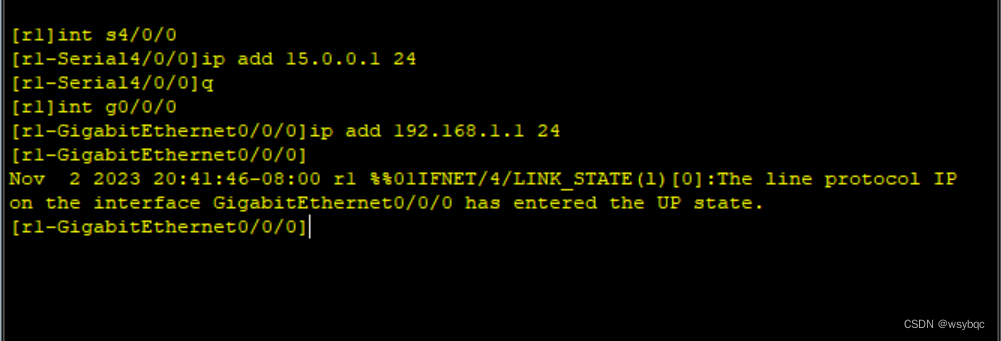

接着在私网边界路由器配一条缺省指向isp
[r1]ip route-static 0.0.0.0 0 15.0.0.2 [r2]ip route-static 0.0.0.0 0 25.0.0.2
[r3]ip route-static 0.0.0.0 0 35.0.0.2 [r4]ip route-static 0.0.0.0 0 45.0.0.2
然后配置r1与r5之间的pap认证,r5为主认证方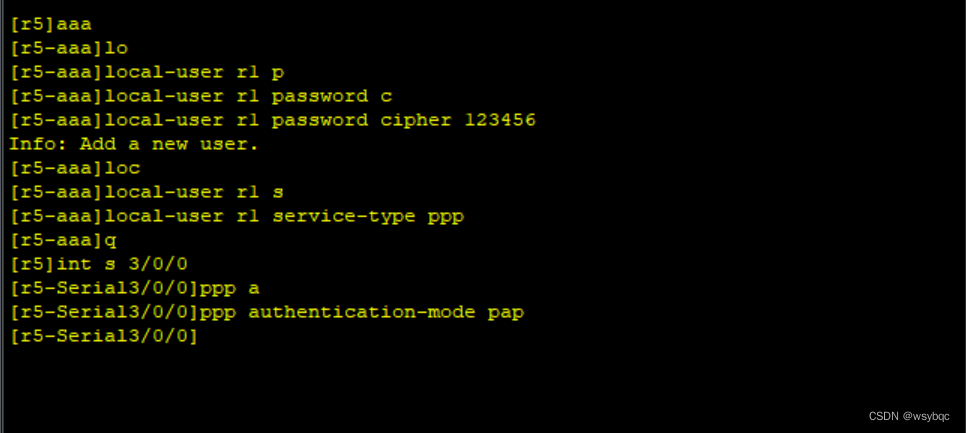

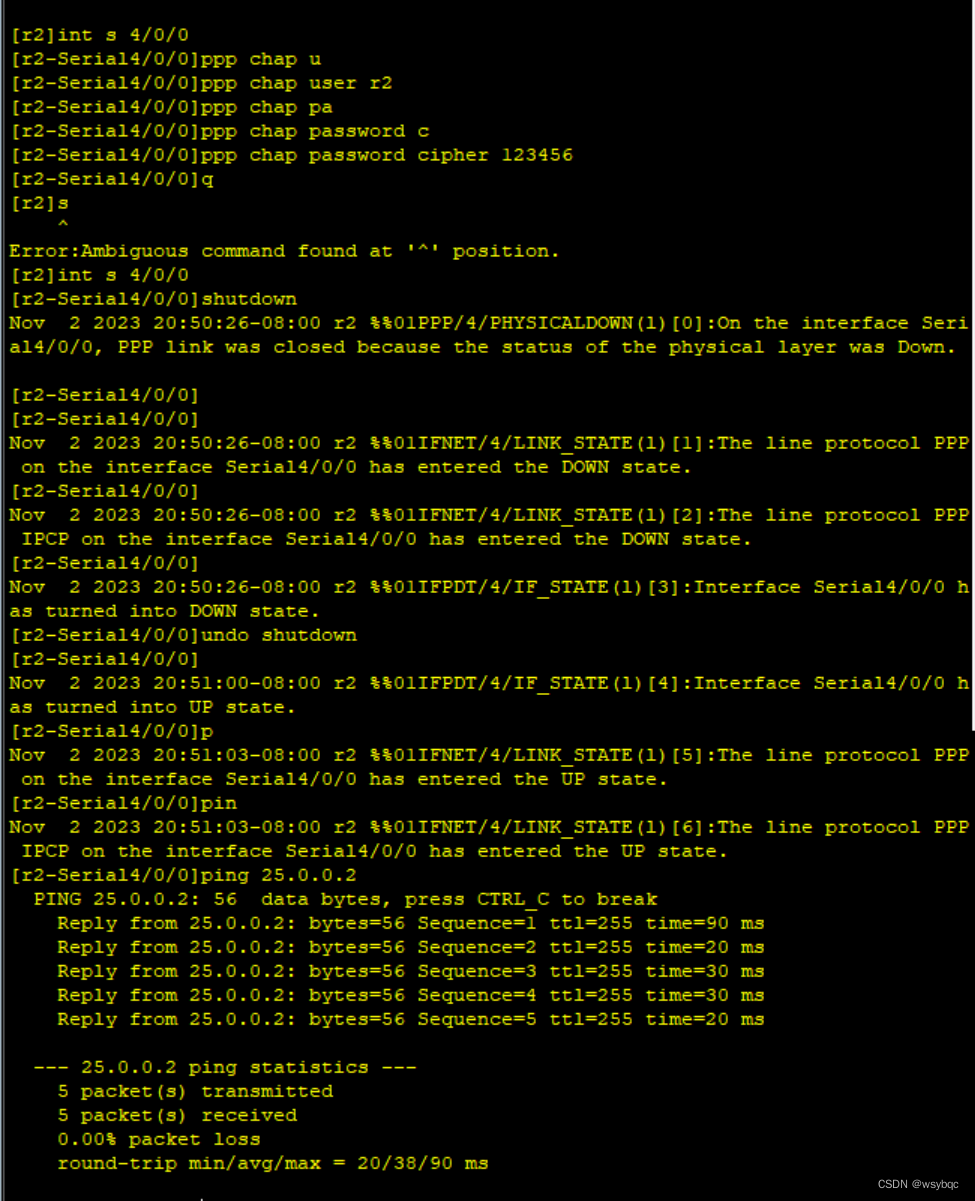
再接着配置r2与r5之间的chap认证,仍然r5为主认证方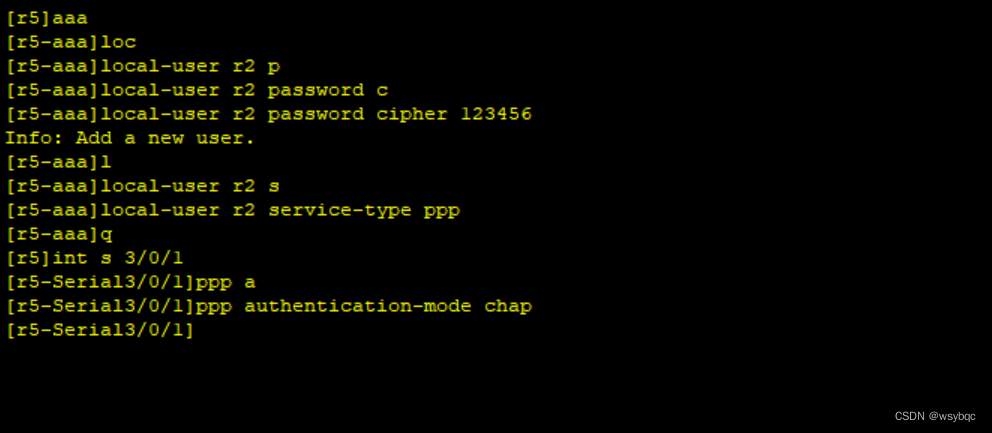
第五:r3和r5之间使用HDLC封装
[r5]int s4/0/0
[r5-Serial4/0/0]link-protocol hdlc
Warning: The encapsulation protocol of the link will be changed. Continue? [Y/N]
:y
[r3]int s4/0/0
[r3-Serial4/0/0]link-protocol hdlc
Warning: The encapsulation protocol of the link will be changed. Continue? [Y/N]
:y
在r3上ping 35.0.0.2,ping成功代表配置完成
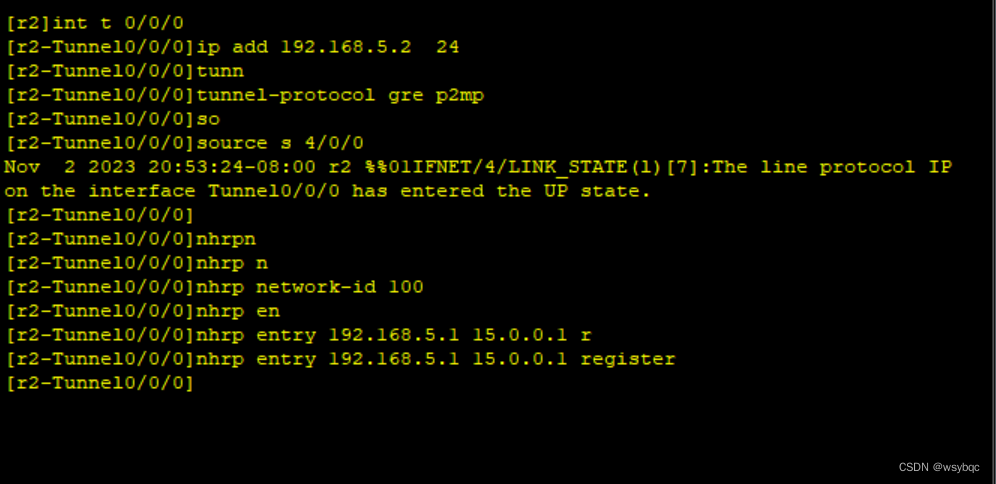
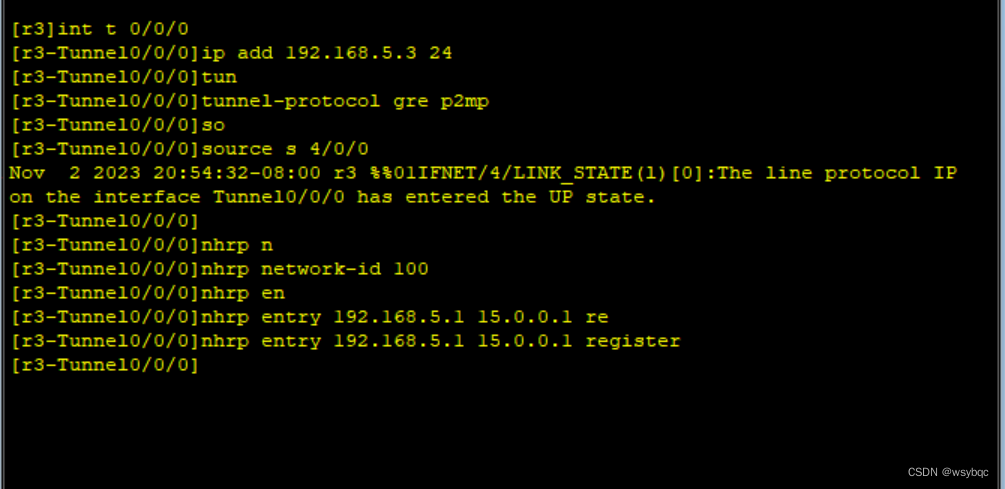
第六:r1,r2,r3构建MGRE环境,r1为中心站点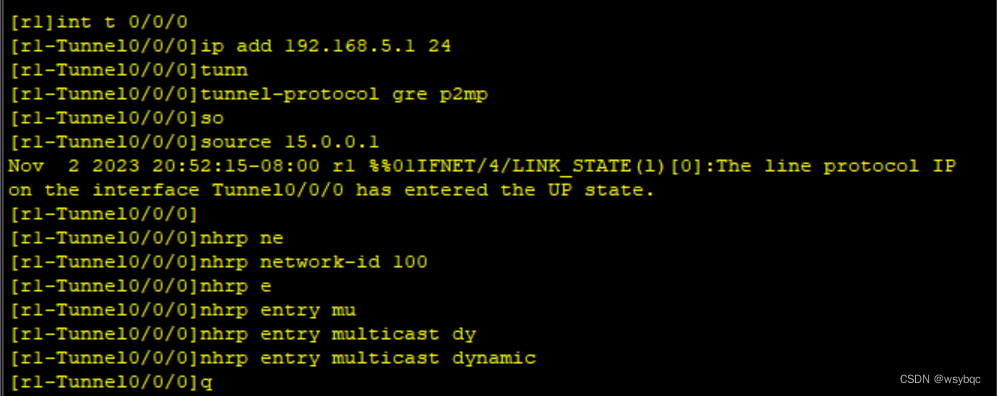
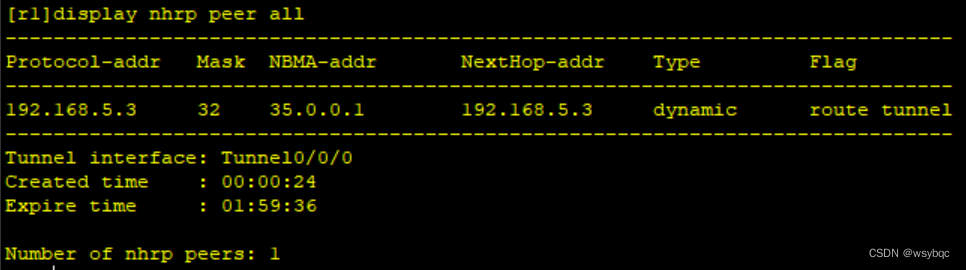
可以在r1上用display nhrp peer all这个命令查看是否配置成功
第七:r1、r4间为点到点的GRE
[r1]int t0/0/1
[r1-Tunnel0/0/1]ip add 192.168.6.1 24
[r1-Tunnel0/0/1]tunnel-protocol gre
[r1-Tunnel0/0/1]source 15.0.0.1
[r1-Tunnel0/0/1]description 45.0.0.1
[r4]int t0/0/0
[r4-Tunnel0/0/0]ip add 192.168.6.2 24
[r4-Tunnel0/0/0]tunnel-protocol gre
[r4-Tunnel0/0/0]source 45.0.0.1
[r4-Tunnel0/0/0]description 15.0.0.1
第八步:整个私有网络基于RIP全网可达
[r1]rip
[r1-rip-1]version 2
[r1-rip-1]network 192.168.1.0
[r1-rip-1]network 192.168.5.0
[r1-rip-1]network 192.168.6.0
r2.r3.r4也同理
[r2-rip-1]network 192.168.2.0
[r2-rip-1]network 192.168.5.0
[r3-rip-1]network 192.168.5.0
[r3-rip-1]network 192.168.3.0
[r4-rip-1]network 192.168.4.0
[r4-rip-1]network 192.168.6.0
第九步:给所有pc手动配置IP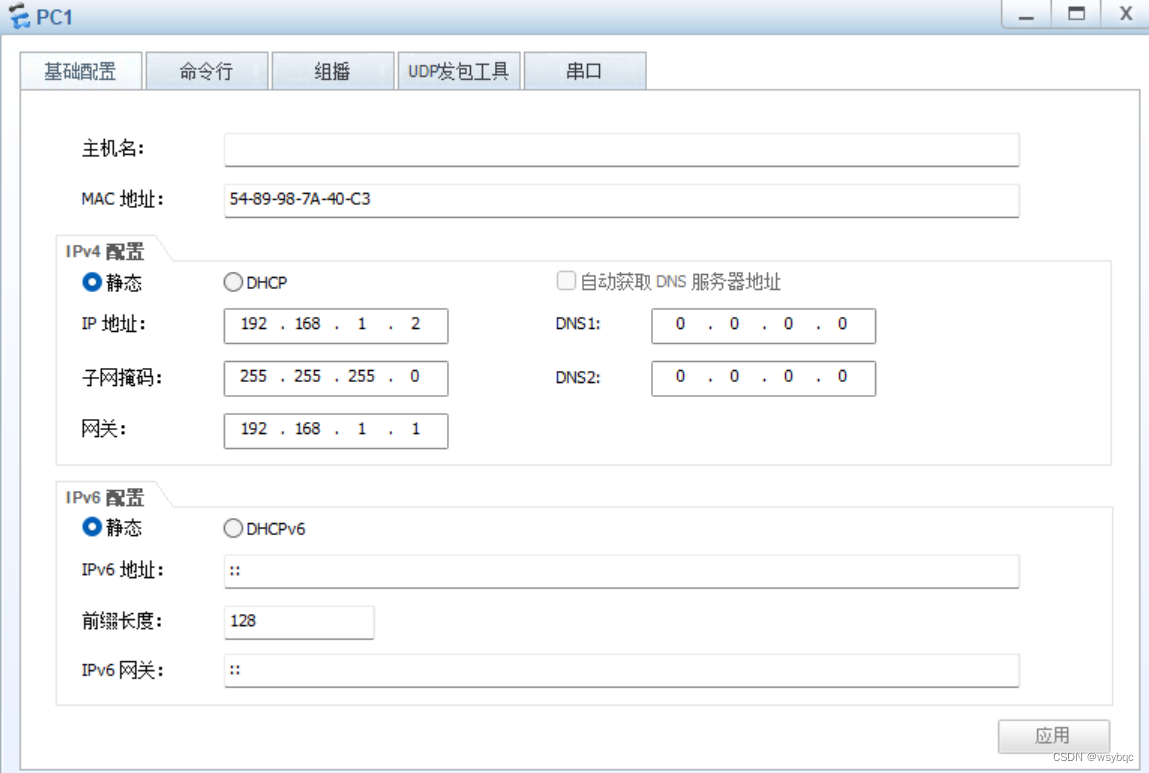



第十步:在边界路由上配置低级ACL,使pc可以访问R5(ISP)环回
[r1]acl 2000
[r1-acl-basic-2000]rule permit source 192.168.1.0 0.0.0.255
[r1-acl-basic-2000]q
[r1]int s4/0/0
[r1-Serial4/0/0]nat outbound 2000
[r2]acl 2000
[r2-acl-basic-2000]rule permit source 192.168.2.0 0.0.0.255
[r2-acl-basic-2000]q
[r2]int s4/0/0
[r2-Serial4/0/0]nat outbound 2000
[r3]acl 2000
[r3-acl-basic-2000]rule permit source 192.168.3.0 0.0.0.255
[r3-acl-basic-2000]q
[r3]int s4/0/0
[r3-Serial4/0/0]nat outbound 2000
[r4]acl 2000
[r4-acl-basic-2000]rule permit source 192.168.4.0 0.0.0.255
[r4-acl-basic-2000]q
[r4]int g0/0/1
[r4-GigabitEthernet0/0/1]nat outbound 2000
配置完成后所有pc都可以ping通R5环回





















 902
902











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








