题目:https://ctf.bugku.com/challenges/detail/id/116.html
IDA打开无壳
1.SHIFT+F12打开string窗口
2.ALT+T查找flag

3.双击查看该字符串的内存地址
变量位于只读数据区(rdata)
![]()
4.按X键定位变量的交叉引用地址
F5查看伪代码(关键部分)
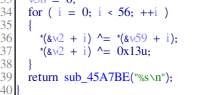
分析后是两步异或的过程
5.用C语言对数据处理得到flag
#include <stdio.h>
#include <stdlib.h>
int main()
{
FILE *fp=fopen("flag","w");
int a[56]= {123,32,18,98,119,108,65,41,124,80,125,38,124,111,74,49,83,108,94,108,84,6,96,83,44,121,104,110,32,95,117,101,99,123,127,119,96,48,107,71,92,29,81,107,90,85,64,12,43,76,86,13,114,1,117,126};
int b[56]= {18,64,98,5,2,4,6,3,6,48,49,65,32,12,48,65,31,78,62,32,49,32,1,57,96,3,21,9,4,62,3,5,4,1,2,3,44,65,78,32,16,97,54,16,44,52,32,64,89,45,32,65,15,34,18,16};
for(int i=0; i<56; i++)
{
a[i]=a[i]^b[i]^0x13u;
fprintf(fp,"%c",a[i]);
}
fclose(fp);
}
6.查看输出文件得到flag:zsctf{T9is_tOpic_1s_v5ry_int7resting_b6t_others_are_n0t}



























 495
495











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










