WP-guicheng
虽然说注定拿不到奖,但还是第一次认真参与一场ctf,学到了不少新的知识,因此写下这份wp纪念一下。
[pwn]babyida_pwn
解题思路
反编译代码,看到当输入为2222时拿到shell,ls,看到flag文件
[misc]温柔点
解题思路
zip文件被加密,给出了dic密码本,用py的zipfile暴力破解
# -*- coding: utf-8 -*-
import zipfile
import os
def Test(line):
try:
with zipfile.ZipFile("H://QAQ//QAQ.zip","r") as f:
f.extractall("H://QAQ//",pwd=line.encode("utf-8")) #利用密码字典中的密码解压缩
except Exception as e:
return e
finally:
f.close()
def main():
try:
with open("H://QAQ//dic") as file:
lines=file.readlines()
for line in lines:
line=line.strip("\n")
e=Test(line)
if e:
# print(line)
pass
else:
print("************压缩文件的密码是:%s"%line)
return line
except Exception as e:
print("异常对象的类型是:%s"%type(e))
print("异常对象的内容是:%s"%e)
finally:
file.close()
if __name__=='__main__':
re=main()
if re:
pass
else:
print("对不起,密码字典中未匹配到密码!")
得到密码1q2w3e4r5tyuiop,解压后看到图片flag
[crypto]babyflower
解题思路
找到文本加密为花朵符号的网站 解密得到HFHXGU{S3ool_XIBKG0~}
由于我们已知格式为SUSCTF{},因此做一个简单代换,得到倒序字母表,解出真正flag
[crypto]justRSA
题目
from Crypto.Util.number import *
from flag import flag
p=getPrime(150)
q=getPrime(150)
n=p*q
e=65537
m=bytes_to_long(flag)
c=pow(m,e,n)
print(n)
print(c)
'''
1478515719392936710044850615656034941194767475153371243813090897713762117025516403232117859
635346483268607041765081653692316846690674938281834040872188948517632743897309531894345982
'''
解题思路
已知n,可以直接在线分解,得到p,q,已知e,用扩欧得到d,直接解码密文;
[crypto]ezpy
题目
import random
from Crypto.Util.number import *
from Crypto.Cipher import AES
from binascii import b2a_hex, a2b_hex
flag1 = "*********"
key = 'llggwwcryptoyyds'
mode = AES.MODE_OFB
cryptor = AES.new(key.encode('utf-8'), mode, b'0000000000000000')
length = 16
count = len(flag1)
if count % length != 0:
add = length - (count % length)
else:
add = 0
message = flag1 + ('\0' * add)
ciphertext = cryptor.encrypt(message.encode('utf-8'))
result = b2a_hex(ciphertext)
print(result.decode('utf-8'))
# b6e4122d658a39d8fa3da7369e1f6dc2
flag2 = b'*********'
n = 2 ** 256
flaglong = bytes_to_long(flag2)
m = random.randint(2, n-1) | 1
c = pow(m, flaglong, n)
print('m = ' + str(m))
print('c = ' + str(c))
# m = 83862941474000352622736856571533270468192196205332529383208031858169966457039
# c = 93540468044159507877580535912312883151967317672005767396221829672116391895425
解题思路
可以看到flag分为前后两部分,前一部分加密使用自带的AES库,已知密钥和模式,只需调用解密函数,参数设为相同的key和mode,即可得到flag1,需要注意不可以在主函数调用encrypt函数后直接decrypt,可以另写一个decypt函数;
第二部分是离散对数问题,可以调用discrete_log()函数直接解出flag2;
将flag1和flag2拼接即得答案
import libnum
import sagemath
#import Crypto
from Crypto.Cipher import AES
import binascii
from Crypto.Util.number import long_to_bytes
from binascii import b2a_hex, a2b_hex
m = 83862941474000352622736856571533270468192196205332529383208031858169966457039
c = 93540468044159507877580535912312883151967317672005767396221829672116391895425
n = 2 ** 256
#d=discrete_log(c,mod(m,n))
#print (d)
d=450624660454257828385864
print (libnum.n2s(d))
def de(content):
key = 'llggwwcryptoyyds'
mode = AES.MODE_OFB
cryptor = AES.new(key.encode('utf-8'), mode, b'0000000000000000')
k = a2b_hex(content)
b=cryptor.decrypt(k)
print(b)
re='b6e4122d658a39d8fa3da7369e1f6dc2'
de(re)
#print (libnum.n2s(b))
[crypto]ezcipher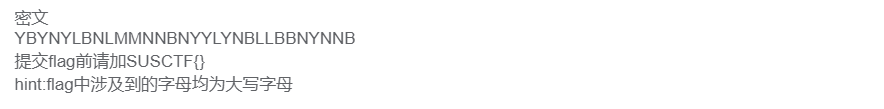
解题思路
观察到密文中一共只有5个字符,使用棋盘密码,暴力跑出所有可能性,筛选出有意义的字符串
#include<iostream>
#include<cstring>
#include<cstdio>
using namespace std;
char C[5][5]={'B','T','A','L','P','D','H','O','Z','K','Q','F','V','S','N','G','I','C','U','X','M','R','E','W','Y'};
char D[5][5]={'a','b','c','d','e','f','g','h','i','k','l','m','n','o','p','q','r','s','t','u','v','w','x','y','z'};
string A="010203123442212003021331120221";
//char P[5]={Y,B,N,M,L};
bool f[5];
string S;
int main()
{
freopen("1.txt","w",stdout);
for(int i1=0;i1<5;i1++)
{
f[i1]=1;
for(int i2=0;i2<5;i2++)
{
if(f[i2]==1)continue;
f[i2]=1;
for(int i3=0;i3<5;i3++)
{
if(f[i3]==1)continue;
f[i3]=1;
for(int i4=0;i4<5;i4++)
{
if(f[i4]==1)continue;
f[i4]=1;
for(int i5=0;i5<5;i5++)
{
if(f[i5]==1)continue;
for(int j=0;j<30;j+=2)
{
int p,q;
if(A[j]-'0'==i1)p=0;
else if(A[j]-'0'==i2)p=1;
else if(A[j]-'0'==i3)p=2;
else if(A[j]-'0'==i4)p=3;
else p=4;
if(A[j+1]-'0'==i1)q=0;
else if(A[j+1]-'0'==i2)q=1;
else if(A[j+1]-'0'==i3)q=2;
else if(A[j+1]-'0'==i4)q=3;
else q=4;
S+=D[p][q];
}
//cout<<"SUSCTF{"<<S<<"}"<<endl;
cout<<S<<endl;
S="";
}
f[i4]=0;
}
f[i3]=0;
}
f[i2]=0;
}
f[i1]=0;
}
}

[reverse]babyre
解题思路:
xor问题,观察反编译程序

可以看到原始字符串处理后结果要等于aa_tql
先对aa_tql进行异或解密

a= [0x73, 0x06, 0x75, 0x16, 0x62, 0x04,
0x7F, 0x1C, 0x74, 0x21, 0x7E, 0x0A,
0x3B, 0x64, 0x2C, 0x6D, 0x5D, 0x02,
0x6E, 0x5D, 0x14, 0x4B, 0x2A, 0x57]
s=''
s=''
for i in range(1,len(a)):
s+=chr(a[i]^a[i-1])
print(s)
#susctf{chU_t1_HA0_l3I_a}
#SUSCTF{CHu_T1_ha0_L3i_A}
由于之前代码中进行了大小写转换,因此再转换回来即可得flag
[web]justeval
解题思路
eval()可以将内容作为php代码来执行
/?a=echo ` base64 flag.php`;
得到密文后用base64解码即可得flag
[web]easy_sql
解题思路
无过滤注入

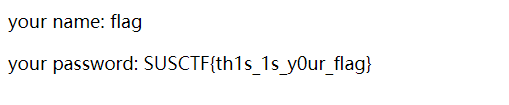
[web]EasyRobot
解题思路
查看robots.txt即得flag
ps: 其它一些有意思的加解密网站
与佛论禅

新与佛论禅得到部分密码,zip的解密直接枚举问号处字符,构造密码本解密;





















 7898
7898











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








