easyCSharp
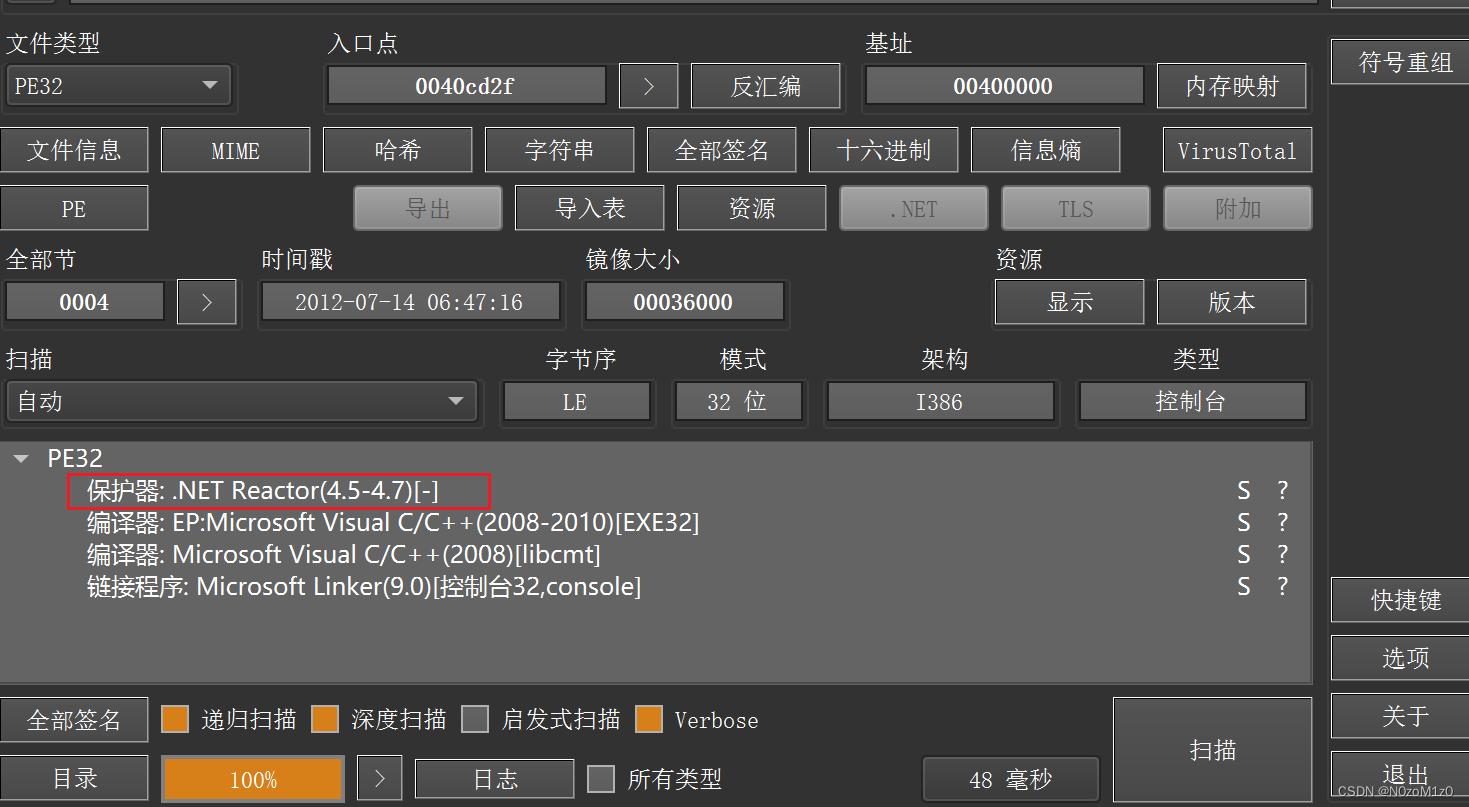
die检查发现有壳
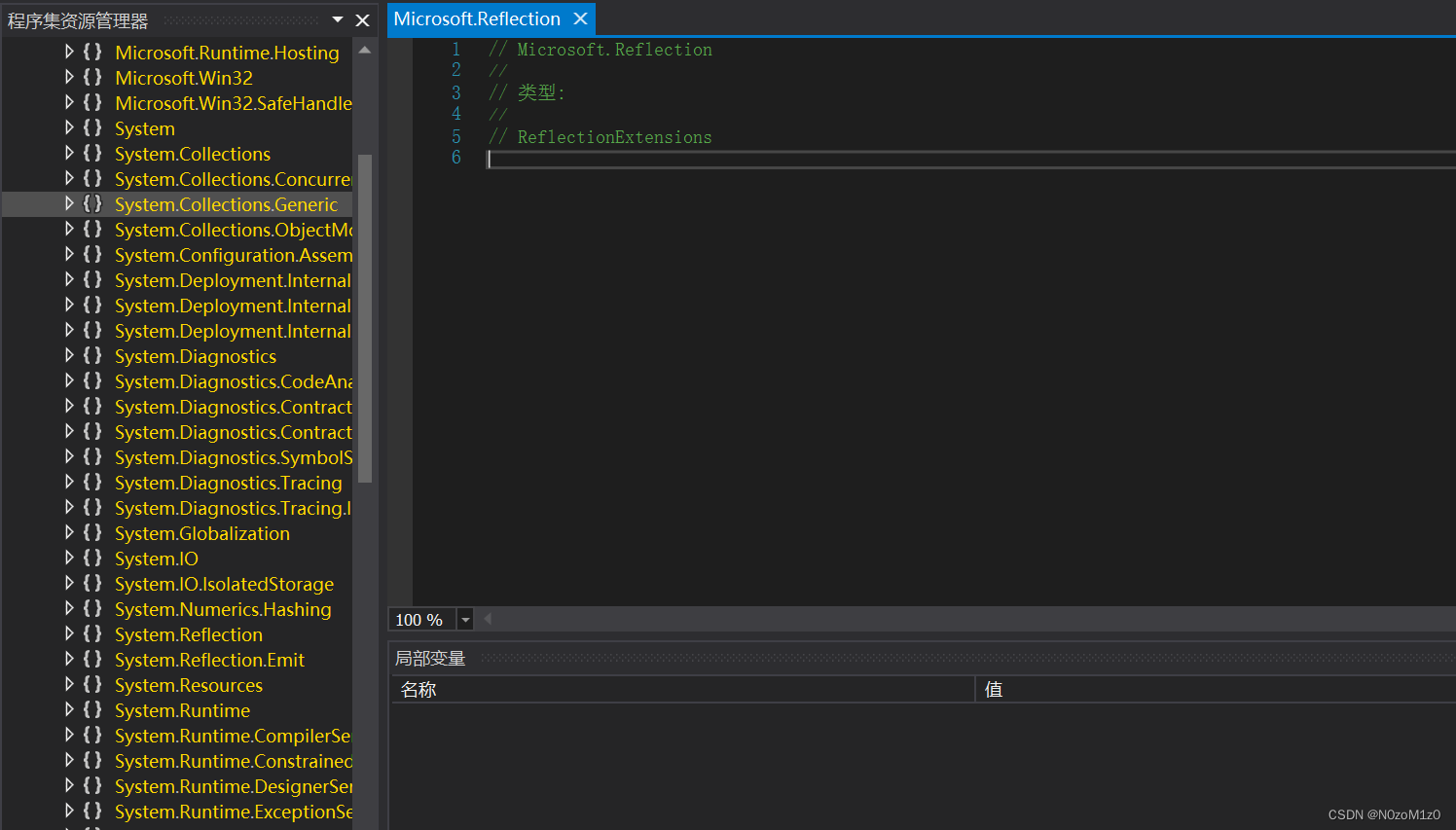
用de4dot把壳脱掉 拖进dnspy发现啥也没有
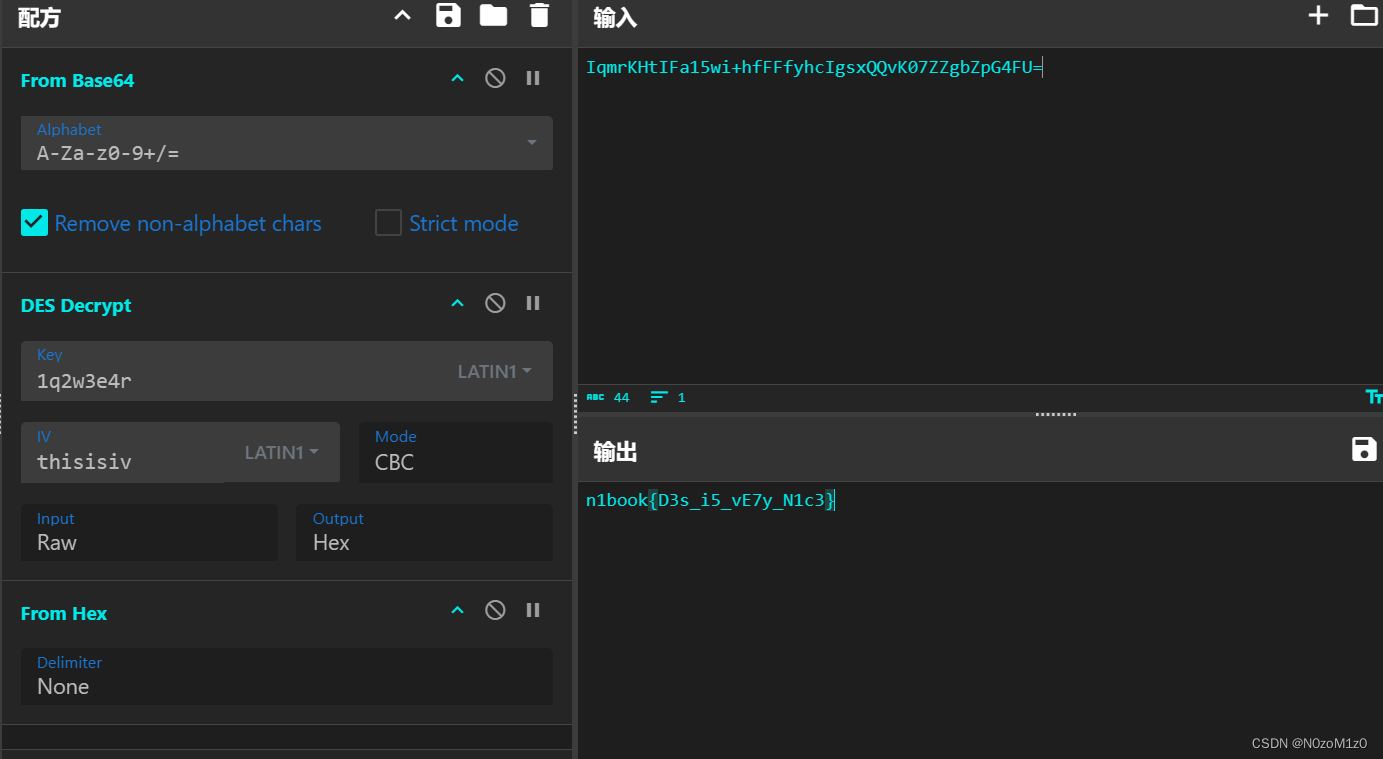
用IDA看能看到这种代码:
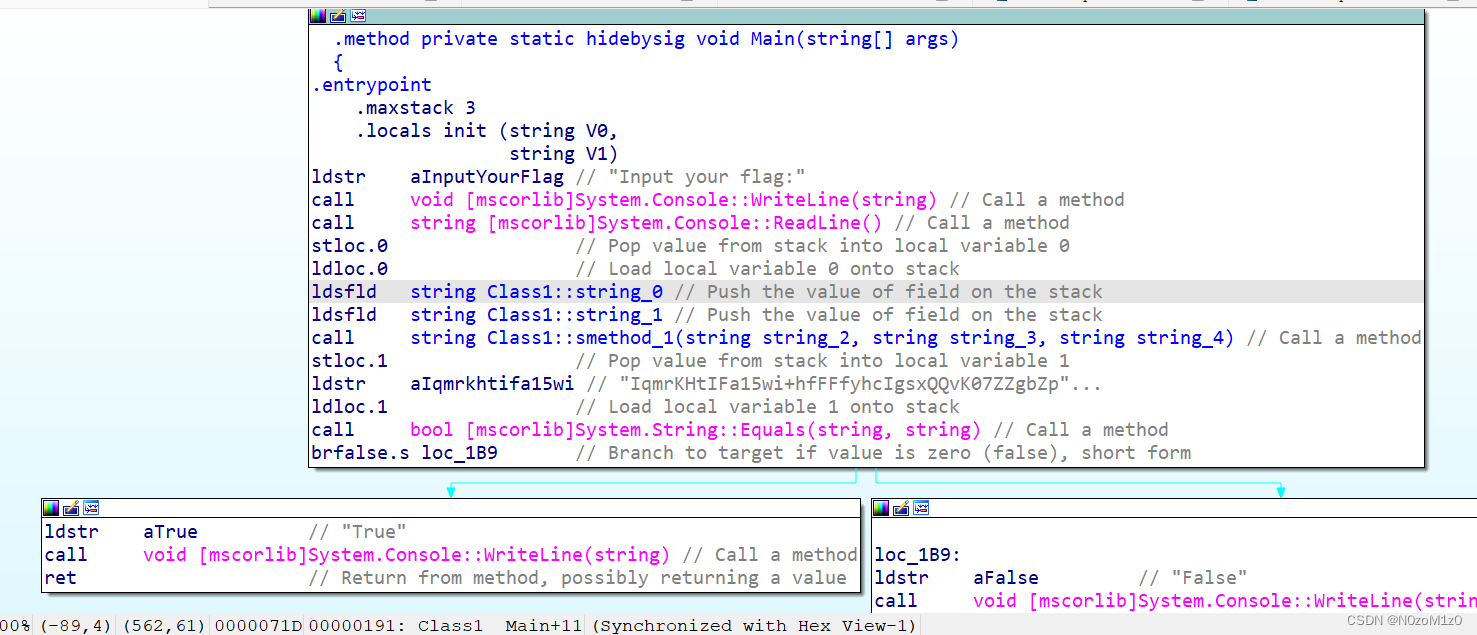
跟着逆就行
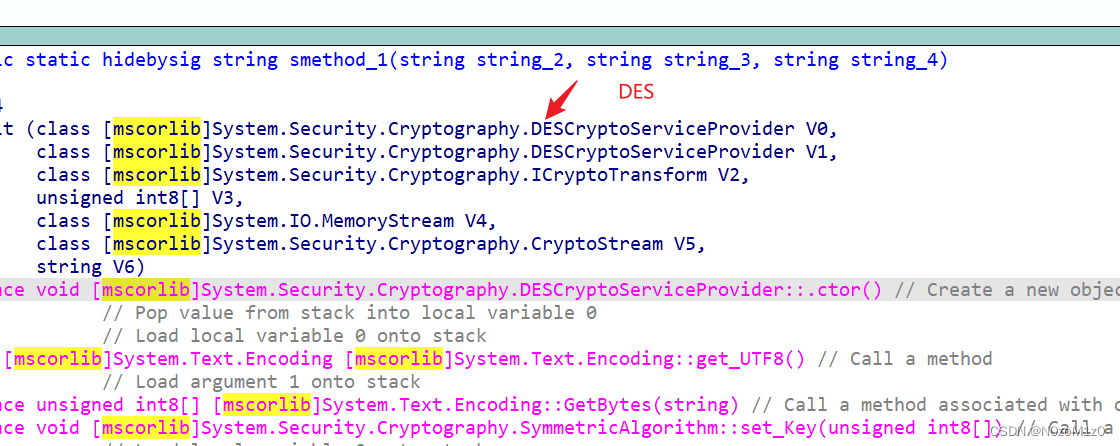
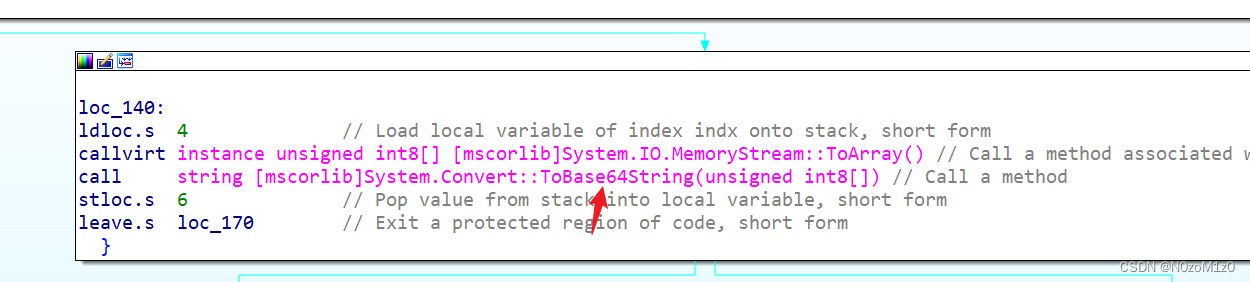
密文: IqmrKHtIFa15wi+hfFFfyhcIgsxQQvK07ZZgbZpG4FU=
easy_rust
由于rust代码冗长 所以我们可以通过string搜索关键字符串 比如搜索flag
找到输入点 发现在一个base64encode里
再在函数列表搜索main 进入main
核心逻辑就这两句:
BASE64ENCODE((__int64)v14, (__int64)(&v11.private_2 + 1));
if ( (_$LT$alloc..string..String$u20$as$u20$core..cmp..PartialEq$GT$::eq::h785456d93284be99(v14, &v11) & 1) != 0 )
这是base64和check
发现check的两个值都在base64encode的参数里
进入base64encode 可以发现这样一句
core::panicking::panic::hb5daa85c7c72fc62(
"attempt to add with overflowxkPmey0LoJt4u5A9MznQhZEH6VSUvRX=Y13fi8srlaTdwGB2+q7cg/bKjpNCFIODInput your flag:\n"
"Ufy3UbIdXc82u0z=Sfk3=MlWFailed to read lineTrue!\n"
"False!\n",
28LL,
&off_23FE58);
结合语言特性 这种就是把函数用上的参数/字符串 都写进去了
很容易猜出overflow后面的是base64变表 flag后面的是密文
变表base64解就行了
n1book{9o0d_j0b}
easy_go
函数列表搜索main 进入main_main
查找发现没有main_init 所以放心分析main_main即可
代码很短
check len and format:
if ( p_string->len == 21
&& (*(_DWORD *)ptr != 1868706158 || *((_WORD *)ptr + 2) != 27503 ? (v1 = 0) : (v1 = ptr[6] == 123),
v1 && ptr[20] == 125) )
Final_Check:
for ( i = 0LL; i < 13; ++i )
{
if ( i >= v4 )
runtime_panicIndex();
if ( byte_561538[i] + byte_561518[i] * *(_BYTE *)(i + v3) != byte_561528[i] )
goto LABEL_12;
}
找到对应值 爆破即可
enc = [0xB7, 0x9C, 0x79, 0x43, 0x9B, 0xAF, 0x94, 0xE4, 0x94, 0x71, 0xEC, 0xEA, 0x8E, 0x00, 0x00, 0x00]
key1 = [0xD3, 0x75, 0x9B, 0xF9, 0xA3, 0x87, 0xED, 0x93, 0x8D, 0xDD, 0x77, 0xED, 0x67, 0x00, 0x00, 0x00]
key2 = [0xDB, 0x9E, 0xB7, 0x9A, 0x91, 0xCA, 0xA1, 0x6B, 0x97, 0xC1, 0x74, 0xB3, 0x90, 0x00, 0x00, 0x00]
flag = "n1book{"
for i in range(13):
for x in range(32,128):
check = (key2[i]+key1[i]*x)&0xff
if check==enc[i]:
flag += chr(x)
break
print(flag)
flag += "}"
print(flag)
n1book{4Ff1n3_C1pH3R}
easy_mfc
这题打开还是不好找到逻辑
WinMain里面貌似没有进行check操作
还好函数很少 挨个翻
翻到有个check
v7[0] = 0x928C9DBC;
v7[1] = 0x21864740;
v7[2] = 0xFD8FACF5;
v3 = *(_DWORD *)(a2 - 12) == 26; // len=26
v7[3] = 0x3AE9E468;
v7[4] = 0x64B366C0;
v7[5] = 0x22D3797E;
v8 = 0xF831;
v5[0] = 0xFDEEACD2;
v5[1] = 0x79FD2C2F;
v5[2] = 0x85D0DEC5;
v5[3] = 0xBB6B658;
v5[4] = 0x54C039F5;
v5[5] = 0x54E21F21;
v6 = 0x8502;
if ( v3 )
{
v4 = 0; // CHECK!
while ( (*((unsigned __int8 *)v7 + v4) ^ (unsigned __int16)ATL::CSimpleStringT<wchar_t,1>::GetAt(&a2, v4)) == *((unsigned __int8 *)v5 + v4) )
{
if ( ++v4 >= *(_DWORD *)(a2 - 12) )
{
CWnd::SetDlgItemTextW(this, -1, L"OK");
goto LABEL_7;
}
}
}
CWnd::SetDlgItemTextW(this, -1, L"Error");
这里提取出两个数组 xor回去即可
enc1 = "BC9D8C9240478621F5AC8FFD68E4E93AC066B3647E79D32231F8"
enc2 = "D2ACEEFD2F2CFD79C5DED08558B6B60BF539C054211FE2540285"
enc1 = [int(enc1[i*2:i*2+2],16) for i in range(len(enc1)//2)]
enc2 = [int(enc2[i*2:i*2+2],16) for i in range(len(enc2)//2)]
for i in range(len(enc1)):
print(chr(enc1[i]^enc2[i]),end='')
n1book{X0r_x0R_15_s0_f1v3}





















 969
969

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








