ettercap 安装
zypper addrepo https://download.opensuse.org/repositories/home:bastianfriedrich/openSUSE_Leap_15.3/home:bastianfriedrich.repo
zypper refresh
zypper install ettercap
wireshark 安装
zypper install wireshark
#运行
Couldn’t run /usr/sbin/dumpcap in child process: Permission denied Are you a member of the ‘wireshark’ group? Try running ‘usermod -a -G wireshark your_username’ as root.
...
usermod -a -G wireshark tom #执行后注销wireshark就可以用
用于嗅探实验的主机为 suse leap15.3,ip:192.168.31.170
tom@tonixtom:~> ip addr | grep link/
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
link/ether 00:0c:29:34:88:c1 brd ff:ff:ff:ff:ff:ff
我这里可能共用同一样网卡,是一台电脑上的三个主机,均为虚拟机。被嗅探的2个主机为两个xp虚拟机,ip分别192.168.31.132和192.168.31.138。下面演示在主机192.168.31.132访问对方提供的http服务。.

开启arp欺骗

tom@tonixtom:~> ip addr | grep link/
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
link/ether 00:0c:29:34:88:c1 brd ff:ff:ff:ff:ff:ff

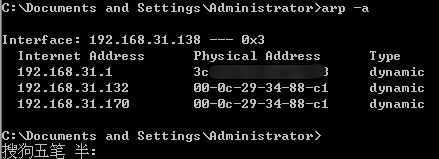
可以看到在leap上,俩个xp系统的通信的目标地址均变成了本机。























 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








